Executive SummaryThis article examines new obfuscation techniques the Gremlin stea 2026-5-15 10:0:52 Author: unit42.paloaltonetworks.com(查看原文) 阅读量:29 收藏
Executive Summary
This article examines new obfuscation techniques the Gremlin stealer malware uses to conceal malicious payloads within embedded resources. We analyze a variant protected by a sophisticated commercial packing utility that employs instruction virtualization, transforming the original code into a custom, non-standard bytecode executed by a private virtual machine.
Gremlin stealer siphons sensitive information from compromised systems and exfiltrates it to attacker‑controlled servers for potential publication or sale. It targets web browsers, system clipboard and local storage to exfiltrate sensitive information like:
- Payment card details
- Browser cookies
- Session tokens
- Cryptocurrency wallet data
- FTP and VPN credentials
This threat has rapidly evolved, incorporating new anti-analysis safeguards into recent builds.
Palo Alto Networks customers are better protected from Gremlin Stealer through our Network Security solutions and Cortex line of products, including:
- Cortex XDR and XSIAM
- Advanced WildFire
- Advanced Threat Prevention
- Advanced URL Filtering and Advanced DNS Security
If you think you might have been compromised or have an urgent matter, contact the Unit 42 Incident Response team.
New Gremlin Site for Publishing Data
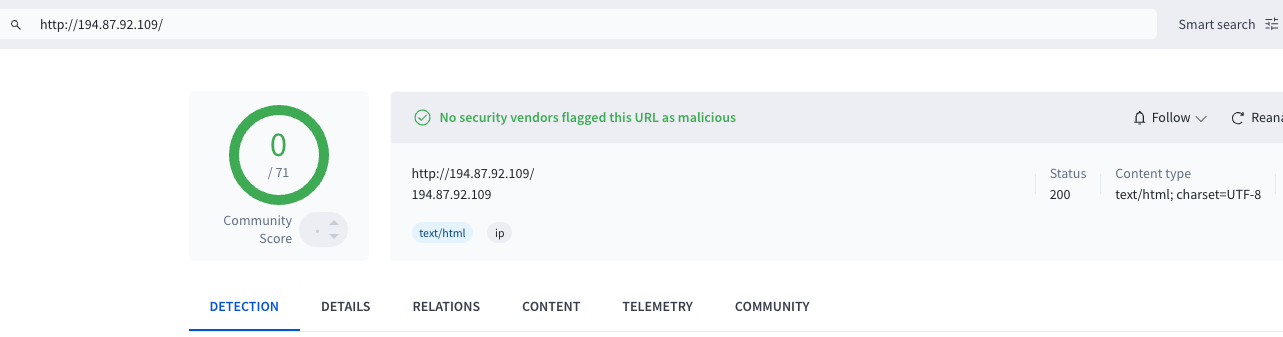
Using data from our internal threat intelligence, we identified a new Gremlin stealer variant. This variant exfiltrates stolen data to a newly deployed site at hxxp[:]194.87.92[.]109 as shown in Figure 1.
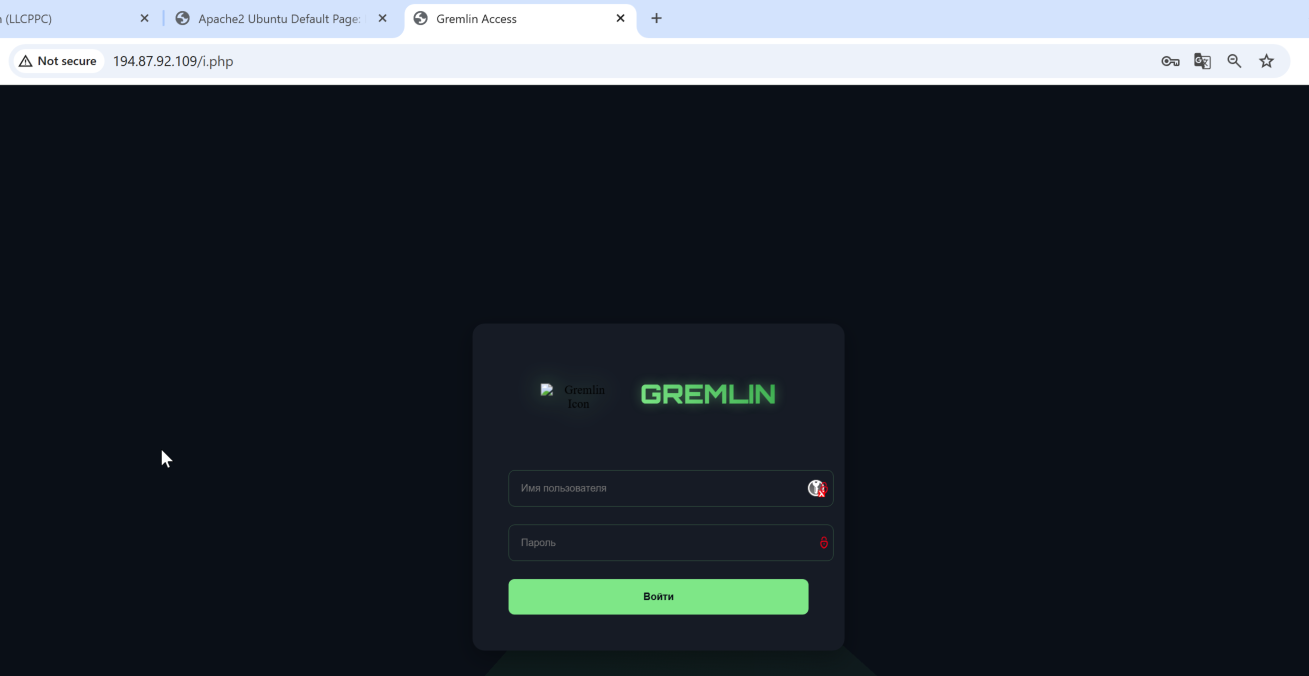
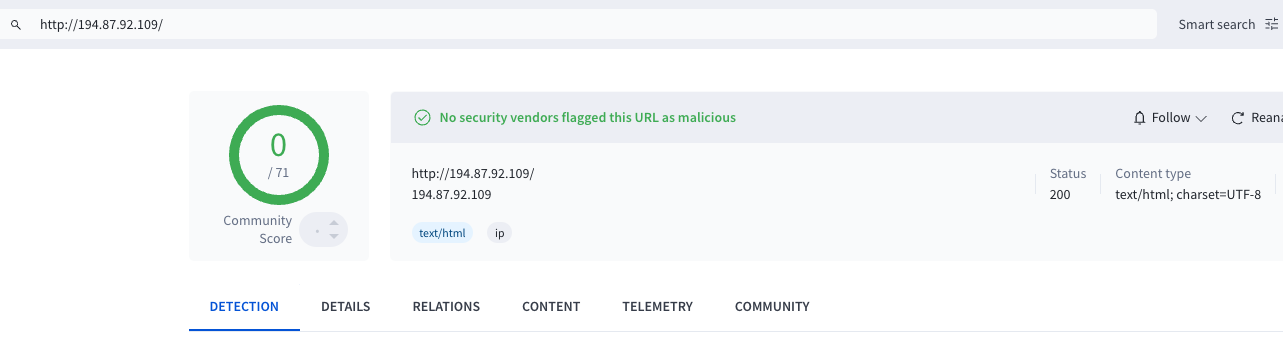
At the time of discovery, VirusTotal showed zero detection for this new Gremlin site hxxp[:]194.87.92[.]109, its associated URLs or any retrieved artifacts. There were no block list entries, community reports or malicious categorizations as shown in Figure 2.
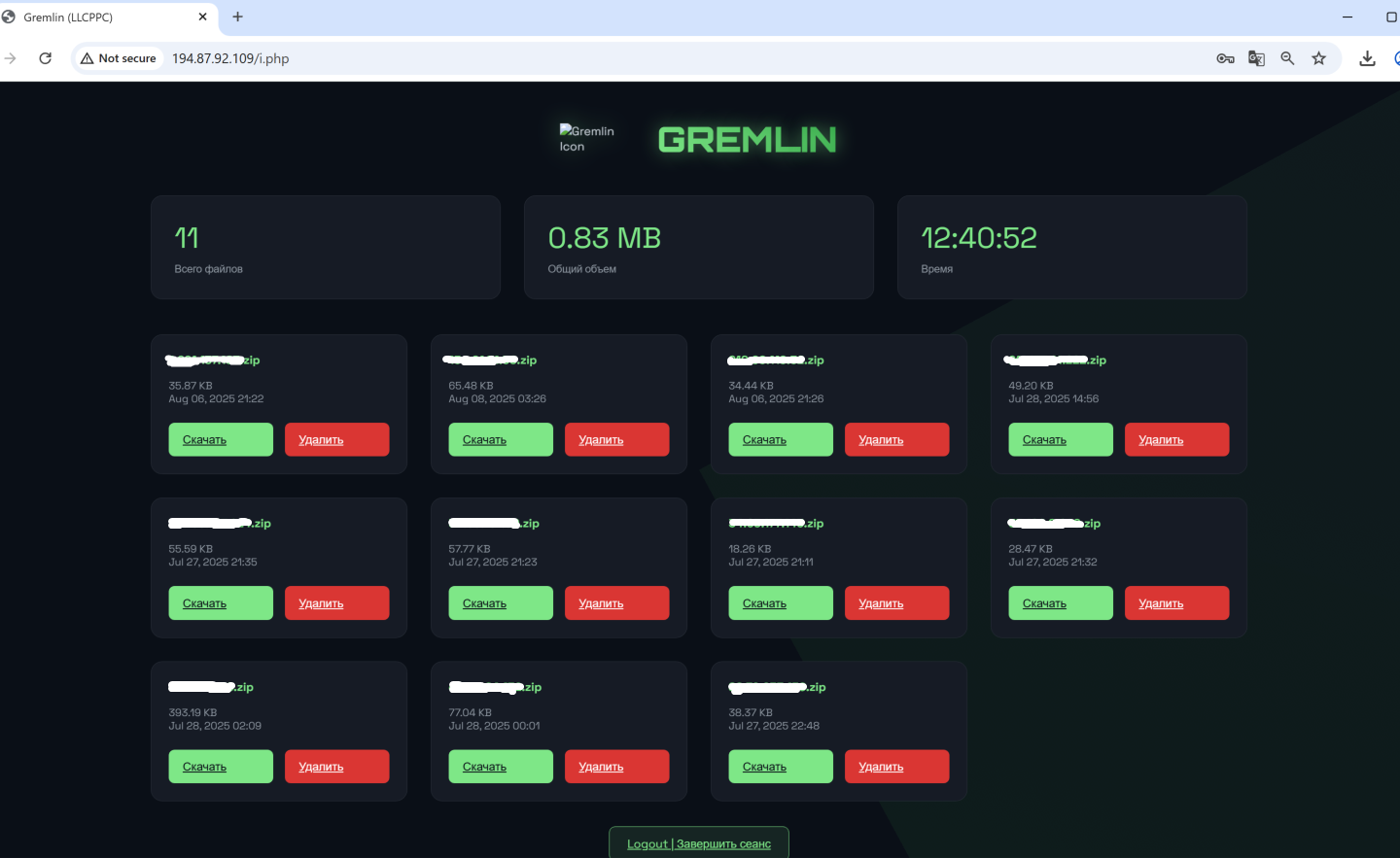
After data theft, the malware bundles harvested artifacts into a ZIP archive, including:
- Browser cookies
- Session tokens
- Clipboard contents
- Cryptocurrency wallet data
- FTP and VPN credentials
The malware names the file using the victim’s public IP address to identify the source, and then uploads it to the attacker-controlled site, as shown in Figure 3.
Technical Analysis
In this section, we present a comparative analysis of older and newer Gremlin stealer variants, highlighting the key changes and describing our process for extracting the final-stage payloads.
Hiding Payload in Resource
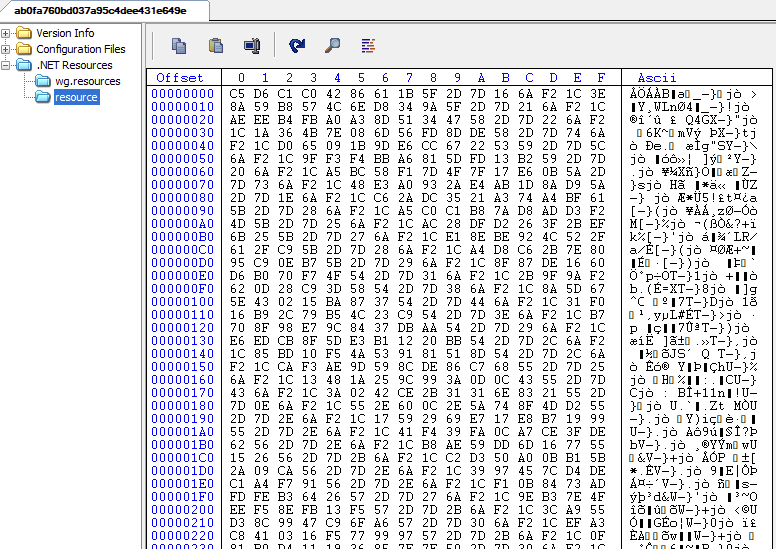
The latest iteration of the Gremlin stealer has an increased focus on stealth, specifically designed to evade static analysis tools. In this version, the malware authors have shifted the malicious payload into the .NET Resource section, masking it with XOR encoding to bypass signature-based detection and heuristic scanning.
Figure 4 shows how the resource section appears as an opaque block of data, hiding strings and API calls that would otherwise trigger alerts.
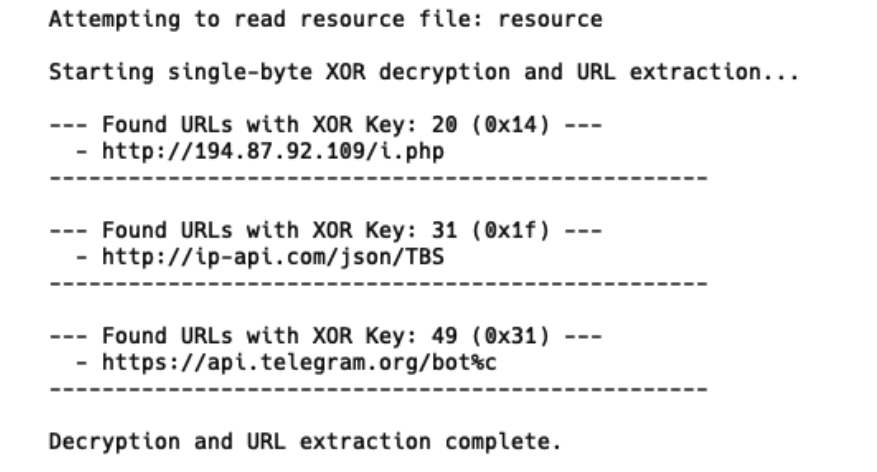
By applying a single-byte XOR decryption routine, we recovered the plain-text configuration. Figure 5 shows that this reveals the hard-coded command-and-control (C2) URLs and exfiltration paths.
Gremlin stealer uses the resource section to mirror the tactics of several high-profile malware families that frequently use this area for payload obfuscation, including:
Comparison with Older Version
Comparing past and present versions reveals a clear evolution in Gremlin stealer’s anti-analysis techniques. Legacy samples (shown in Figure 6) lacked obfuscation, leaving function exports and internal symbols intact.
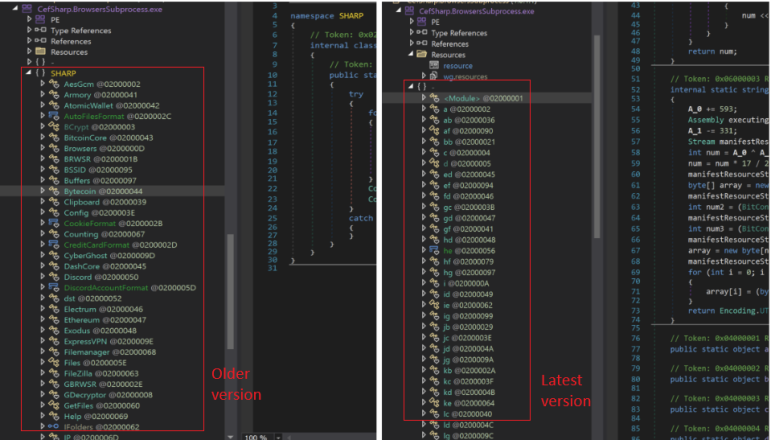
The current iteration implements a staged loading mechanism. Each critical function is decrypted and mapped into memory from the .NET resource section only when needed. This method forces analysts to perform dynamic debugging to observe any meaningful program behavior.
Key Enhancements in the Latest Variant
Gremlin stealer’s evolution from a basic credential harvester to a modular toolkit is evident in several key architectural upgrades:
- Expanded target scope: Gremlin stealer includes a dedicated Discord token extraction module, which signifies a pivot toward targeting digital identity and social engineering.
- Active financial fraud: The latest variant shifts from passive data theft to active financial interference. This crypto clipper functionality continuously monitors the system clipboard for strings matching cryptocurrency wallet patterns. When it detects a match, the malware replaces the victim's address with the attacker’s wallet in real time, diverting funds during transactions.
- Advanced persistence: The WebSocket-based session hijacking module represents its most significant technical upgrade. This allows Gremlin stealer to hijack active, live browser sessions and bypass modern cookie protections by requesting the data directly from the running browser process.
Sample Packed Using a Complex Commercial Packing Utility
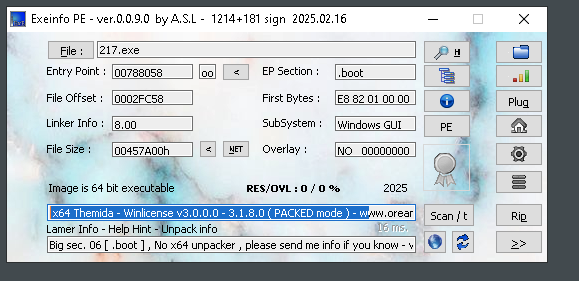
We uncovered an iteration of Gremlin stealer (SHA256 2172dae9a5a695e00e0e4609e7db0207d8566d225f7e815fada246ae995c0f9b) packed using a packing utility, as shown in Figure 7 below.
Let’s discuss the obfuscation and anti-analysis techniques this variant uses.
Code Obfuscation and Anti Analysis
Identifier Renaming (The “No-Labels” Technique)
Imagine trying to cook in a kitchen where every can, box and spice jar has its label replaced with a random, short name like a, b, c, hf or ze. The malware authors applied this technique to the variant’s code.
- What it is: They replaced every meaningful name for a class, method or variable with a meaningless one.
- Why it's effective: It removes all context. A method originally named StealPasswordsFromChrome might become a(). A variable named decryptionKey might become b. This forces an analyst to manually trace every single function call to figure out its purpose, which is incredibly time-consuming.
- Example: In the file hf.cs, the main orchestrator class is named hf, and its primary methods are a, b and c. In bb.cs, the class for stealing browser data is BrowserCredentialStealer, but in the original obfuscated code, it was just bb.
String Encryption (The “Secret Decoder Ring” Technique)
In this technique, malware authors made readable strings appear as gibberish. Instead of writing a word like password or a URL like hxxps://api[.]telegram[.]org directly in the code, the malware stores them encrypted.
- What it is: All important strings are hidden. The code only contains numbers that act as a key to a secret decoder function. When the program needs a string, it passes these numbers to the decoder, which then returns the real string.
- The decoder ring function: The secret decoder is the method _003CModule_003E.c(int, int, int).
- It takes three integers as input
- It uses these numbers to calculate an offset and a length
- It opens an embedded resource file (named resource in the .csproj file) which contains all the encrypted strings
- It seeks the calculated offset, reads the specified number of encrypted bytes and uses the third integer as a key to decrypt them
- It returns the final, readable string
- Why it's effective: It completely hides the malware's intentions from static analysis. Analysts cannot simply search the code for suspicious keywords like Telegram, wallet.dat or api.ipify[.]org because they don't exist in plain text. Instead, analysts must either run the program in a debugger to see what strings are produced or reverse-engineer the decoder function.
- Example: A line like this from the original code:
csharp
// This is what the obfuscated code looks like
string url = global::_003CModule_003E.c(18829, 2178, 23);
When executed, the c() function would run its decoding operation, and the URL variable would then contain: csharp
// This is the real value at runtime
string url = "http://api.ipify.org/?format=json";
Control-Flow Obfuscation (The “Maze of Useless Roads” Technique)
This technique makes the code's logic intentionally confusing, like turning a straight road into a maze of dead ends and pointless loops that all eventually lead to the same place.
- What it is: The decompiler output is filled with complex and nonsensical if-else statements, goto jumps and mathematical operations that don't actually affect the outcome. These are designed to confuse both human analysts and automated analysis tools.
- Why it's effective: It breaks the logical flow that a person would expect to see. It makes it hard to determine which path the code will actually take, even though in many cases, there's only one real path. This significantly increases the time and effort required for reverse engineering.
- Example: There are many switch statements and goto labels (e.g., IL_00c8, IL_0138) that create a tangled web of execution, even though the underlying logic is a simple sequence of await Task.Run(...).
Conclusion
While the core architecture and exfiltration methods via private web panels or the Telegram Bot API remain consistent, this latest variant of Gremlin stealer represents an evolution into a more complex threat. By transitioning from a simple data exfiltration tool to a more advanced modular stealer, Gremlin now targets Chromium-based browsers. It uses memory-resident techniques to hijack active session tokens and sensitive data directly from running processes, rather than relying solely on static database files.
This threat’s scope has broadened, as evidenced by a dedicated Discord token stealer. This module scans multiple paths and uses regex validation to compromise modern communication platforms.
The malware’s author has also added a clipboard hijacker. This new monetization feature enables persistent financial fraud. It continuously monitors the clipboard, replacing cryptocurrency wallet addresses with attacker-controlled ones.
Palo Alto Networks Protection and Mitigation
Palo Alto Networks customers are better protected from the threats discussed above through the following products:
- The Advanced WildFire machine-learning models and analysis techniques have been reviewed and updated in light of the IoCs shared in this research.
- Advanced URL Filtering and Advanced DNS Security identify known domains and URLs associated with this activity as malicious.
- Advanced Threat Prevention has an inbuilt machine learning-based detection that can detect exploits in real time.
- Cortex XDR and XSIAM are designed to:
- Prevent the execution of known malicious malware, and also prevent the execution of unknown malware using Behavioral Threat Protection and machine learning based on the Local Analysis module.
- Protect against credential gathering tools and techniques using the new Credential Gathering Protection available from Cortex XDR 3.4.
- Detect post-exploit activity, including credential-based attacks, with behavioral analytics, through Cortex XDR Pro.
If you think you may have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America: Toll Free: +1 (866) 486-4842 (866.4.UNIT42)
- UK: +44.20.3743.3660
- Europe and Middle East: +31.20.299.3130
- Asia: +65.6983.8730
- Japan: +81.50.1790.0200
- Australia: +61.2.4062.7950
- India: 00080005045107
Indicators of Compromise
SHA256 hashes of the Gremlin stealer samples analyzed for this article:
- 2172dae9a5a695e00e0e4609e7db0207d8566d225f7e815fada246ae995c0f9b
- 9aab30a3190301016c79f8a7f8edf45ec088ceecad39926cfcf3418145f3d614
- 971198ff86aeb42739ba9381923d0bc6f847a91553ec57ea6bae5becf80f8759
- ab0fa760bd037a95c4dee431e649e0db860f7cdad6428895b9a399b6991bf3cd
- f76ba1a4650d8cafb6d3ff071688c5db6fd37e165050f03cece693826f51d346
- a9f529a5cbc1f3ee80f785b22e0c472953e6cb226952218aecc7ab07ca328abd
- 691896c7be87e47f3e9ae914d76caaf026aaad0a1034e9f396c2354245215dc3
- 281b970f281dbea3c0e8cfc68b2e9939b253e5d3de52265b454d8f0f578768a2
- 9fda1ddb1acf8dd3685ec31b0b07110855832e3bed28a0f3b81c57fe7fe3ac20
- d11938f14499de03d6a02b5e158782afd903460576e9227e0a15d960a2e9c02c
- 1bd0a200528c82c6488b4f48dd6dbc818d48782a2e25ccd22781c5718c3f62f5
URLs
- hxxp[:]194.87.92[.]109/i.php
Additional Resources
- Gremlin Stealer: New Stealer on Sale in Underground Forum — Unit 42, Palo Alto Networks
如有侵权请联系:admin#unsafe.sh