2026-5-11 00:0:0 Author: zeltser.com(查看原文) 阅读量:0 收藏
The AI Defense Matrix maps eight AI asset classes to NIST CSF functions, giving security leaders one grid to assign ownership, find gaps, and select controls. Sounil Yu and I co-authored it as the security-for-AI companion to his Cyber Defense Matrix.
The AI Defense Matrix helps security leaders find gaps, assign ownership, and select controls to defend AI systems. It also helps vendors explain their value and plan a product strategy. I co-authored it with Sounil Yu.
The cybersecurity community is racing to reshape our programs to secure the AI transformation era. We’re under pressure to support AI adoption while meeting our risk management responsibilities and calibrating acceptable insecurity.
Existing AI security frameworks each cover one slice of the work. NIST IR 8596 names AI components to protect, OWASP LLM Top 10 ranks application risks, and ISO 42001 specifies AI management controls. Practitioners need to combine those slices into a single view of safeguarding each AI asset class. Sounil’s Cyber Defense Matrix gave that single view for cybersecurity; the AI Defense Matrix extends it to AI-specific assets.
The resulting grid is a “security for AI” companion to the Cyber Defense Matrix, which covers “AI for security.” The AI Defense Matrix website has the details.
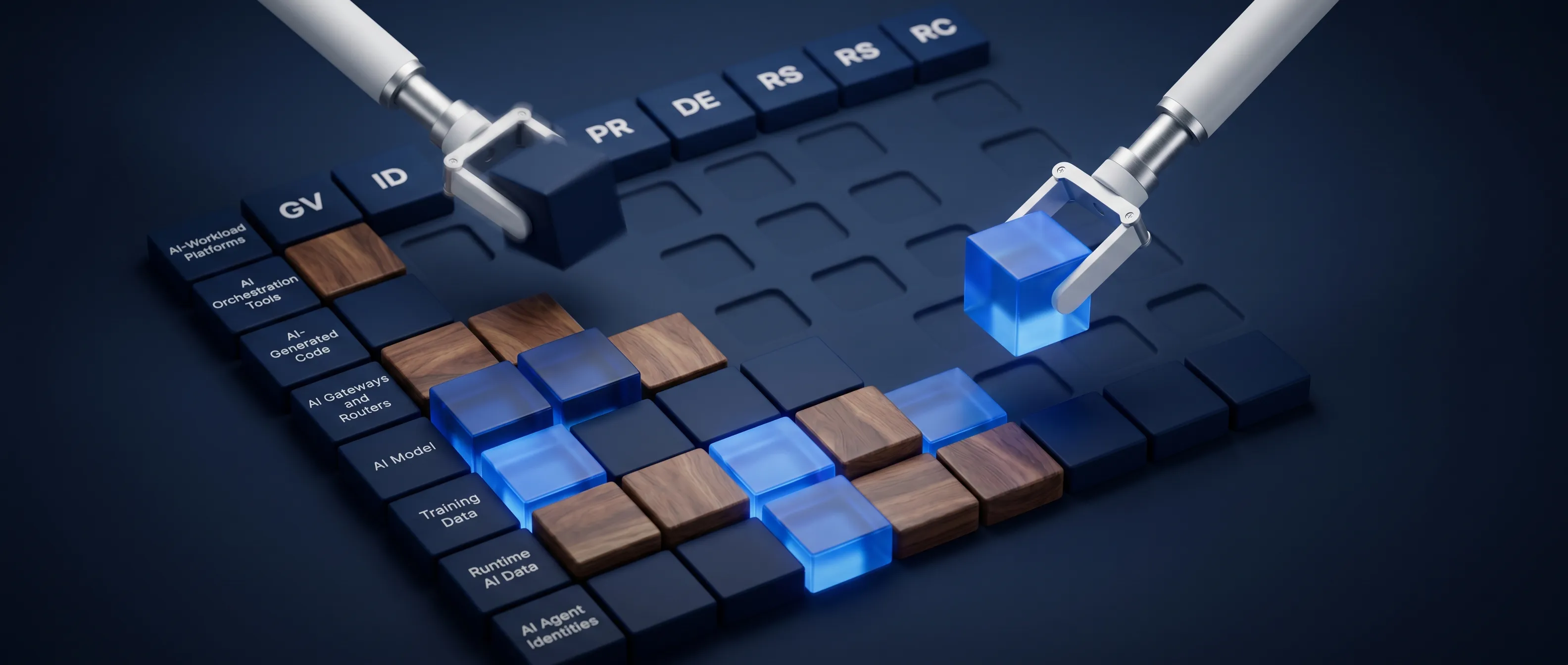
The matrix organizes AI defense activities.
The framework’s eight rows are AI asset classes that enterprises need to safeguard. It uses NIST CSF 2.0 functions as columns to classify the defensive activities. Each cell captures a process or technology for defending each AI asset class:
| Asset Class | Govern | Identify | Protect | Detect | Respond | Recover |
|---|---|---|---|---|---|---|
| AI-Workload Platforms | ||||||
| AI Orchestration Tools | ||||||
| AI-Generated Code | ||||||
| AI Gateways and Routers | ||||||
| AI Model | ||||||
| Training Data | ||||||
| Runtime AI Data | ||||||
| AI Agent Identities |
Practitioners and vendors use the matrix differently.
Practitioners: Review each cell and ask whether any processes or technologies in your program exist at that intersection. Start with Govern to anchor on ownership, risk appetite, and policy. Create a gap inventory and use it alongside your understanding of the business context to build an AI defense roadmap.
Vendors: Identify the cells that your product addresses and map your capabilities there rather than claim broad coverage. Treat thinly covered cells as opportunities to differentiate, sharpen the roadmap, or shape the sales narrative. Use these insights to inform your product strategy.
Your AI assistant can navigate the matrix.
You can use your AI assistant to work through the AI Defense Matrix interactively. My public MCP server now exposes the matrix as a set of tools your AI can use. It can explain the latest matrix contents or look up cross-mappings to other AI security frameworks. It can also run an evaluation playbook against your AI security program, or cross-map your product capabilities to find gaps.
Add my MCP server to you AI assistant (https://website-mcp.zeltser.com/mcp) to start using these tools. The same server also helps your AI evaluate security product strategies, write incident reports, and more.
Eight asset classes need AI-specific defenses.
Here’s how the AI Defense Matrix groups different types of AI assets:
- AI-Workload Platforms: Inference servers, training platforms, vector DB platforms, and the model-loading supply chain.
- AI Orchestration Tools: Agentic orchestration tools, plus their plugins, skills, hooks, system prompts, scaffolding, harnesses, configuration settings, and MCP clients on user devices.
- AI-Generated Code: Code produced by AI tools, AI-assisted reviews, AI-generated infrastructure-as-code and tests, and vibe-coded apps that bypass CI/CD.
- AI Gateways and Routers: MCP proxies and gateways, LLM routers, outbound AI-service traffic, shadow AI egress, and model-registry traffic.
- AI Model: Model weights, fine-tuning checkpoints, model cards, registries, AIBOM, and the third-party LLMs your enterprise consumes.
- Training Data: Datasets used for training, fine-tuning, and continued learning.
- Runtime AI Data: User prompts, inference inputs, RAG content, vector DB content, persistent agent memory, and interaction history.
- AI Agent Identities: AI agents as non-human principals, plus credentials, keys, permission scopes, service accounts, and delegation chains across agents and tools.
A row earns its place when the asset needs AI-specific defense beyond what traditional cybersecurity handles. When two AI assets share the same defender team and tool category, they are combined into a single row.
Use the matrix to anchor your AI defense work as the field evolves. Let the gaps you find shape your priorities.
如有侵权请联系:admin#unsafe.sh