
Key FindingsConsolidation after peak fragmentation: The top 10 ransomware groups accoun 2026-5-11 09:59:14 Author: research.checkpoint.com(查看原文) 阅读量:12 收藏
Key Findings
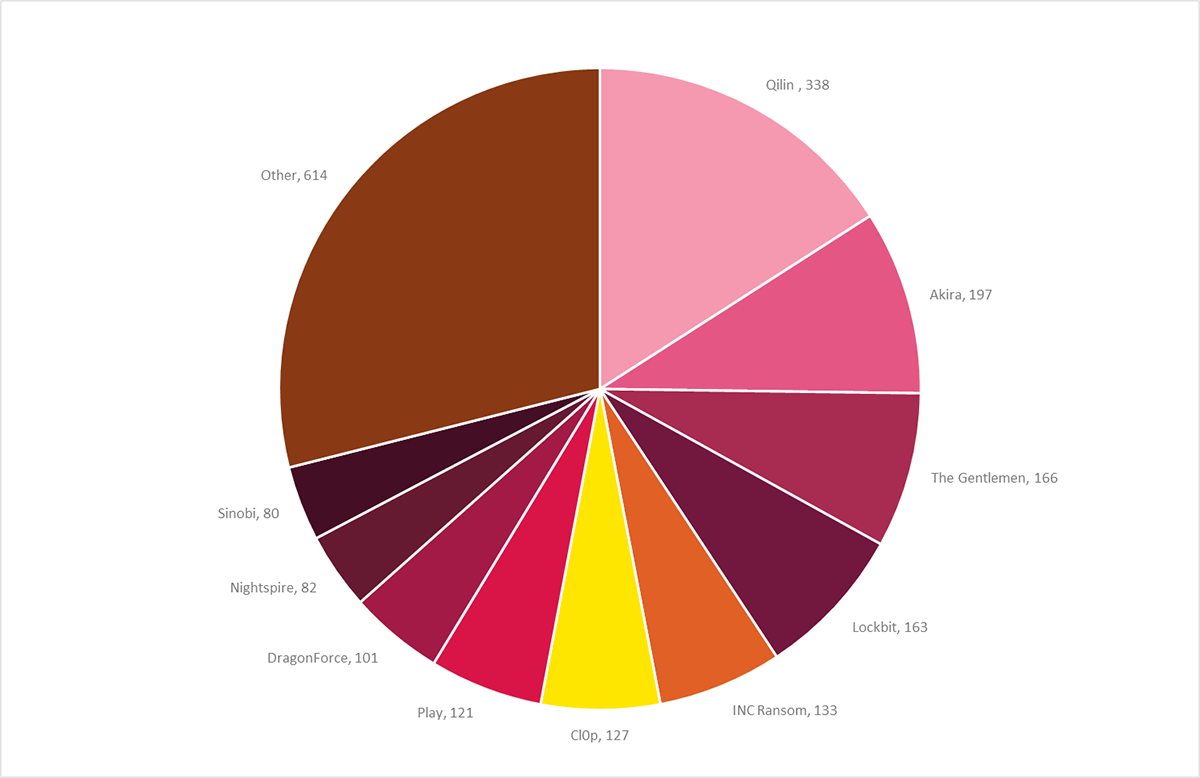
- Consolidation after peak fragmentation: The top 10 ransomware groups accounted for 71% of all Q1 2026 victims, a sharp reversal from the fragmentation seen in Q3 2025. The ransomware ecosystem is once again consolidating around fewer, more dominant operators.
- Volume stabilization at historically high levels: There were 2,122 victims posted on data leak sites (DLS), making this period the second-highest Q1 on record. The long growth trend is stabilizing.
- Qilin’s sustained dominance: Qilin maintained its position as the most prominent ransomware operation for the third consecutive quarter, posting 338 victims.
- The Gentlemen is the breakout story of Q1 2026 reaching the third place on the global ransomware list, increasing their victim count from 40 victims in Q4 2025 to 166 in Q1 2026.
- LockBit 5.0 comeback confirmed: LockBit posted 163 victims in Q1 2026, climbing to fourth place.
Ransomware in Q1 2026: Consolidation at Scale
During the first quarter of 2026, we monitored more than 70 active data leak sites (DLS) that collectively listed 2,122 new victims. This figure represents a 12.2% decline from the Q4 2025 all-time record of 2,416 victims but remains the second-highest Q1 on record at 117% above Q1 2024 (977 victims) and is keeping in line with the elevated baseline established through 2025.
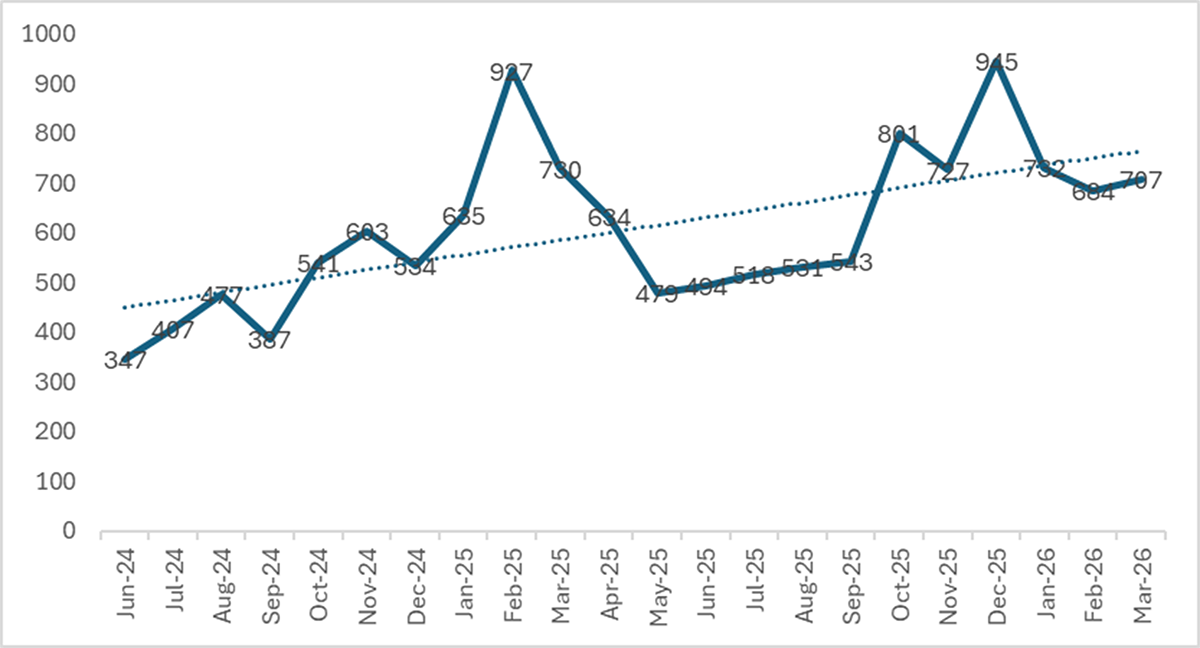
Monthly volumes within Q1 were consistently stable: in January there were 732 recorded victims, 684 in February, and 706 in March. This reflects a sustained operating rate of an average of 707 victims per month in Q1 2026.
The headline year-over-year (YoY) comparison shows a 7.1% decline from the 2,285 victims in Q1 2025. However, this comparison is misleading as the Q1 2025 numbers were heavily inflated by Cl0p’s Cleo mass-exploitation campaign which contributed approximately 390 victims in a single burst. If we exclude Cl0p from both periods, there were 1,894 victims in Q1 2025 versus 1,995 in Q1 2026, an actual YoY increase of 5.3%. The underlying growth trend in ransomware operations persists, even as the most dramatic spikes subside.
From fragmentation to consolidation
The most significant structural development seen in Q1 2026 is not the volume of attacks but the consolidation of the different operators conducting them. After two years of steady fragmentation, during which the number of active groups grew from 51 in Q1 2024 to a peak of 85 in Q3 2025 and the Top-10 share of victims fell from 68% to 57%, the ecosystem has decisively reversed course.
In Q1 2026, the top 10 groups accounted for 71.1% of all DLS-posted victims, which is the highest concentration since Q1 2024 when the ecosystem was far smaller. The number of active groups shrank from 85 to 71. Fourteen groups that were active in Q4 2025 disappeared entirely, while 21 new names appeared. However, most of the newcomers posted fewer than 10 victims, failing to take advantage of the disappearance of established mid-tier operators.
This is a common pattern repeated throughout the ecosystem’s history: law enforcement actions disrupt the ransomware market, affiliates scatter, and survivors who avoid disruption absorb the displaced talent pool and grow. Groups such as Qilin, Akira, The Gentlemen, and LockBit, who together claimed 41% of all victims in Q1, capitalized on the instability of their competitors. In Q1 2026, Qilin alone posted more victims than the combined output of the bottom 50 groups.
This dynamic carries implications beyond statistics. The consolidation of the ecosystem around fewer, more dominant operators changes its character. Larger RaaS brands invest in operational consistency, including functional decryption tools, because their business model depends on the perception that victim payment results in data recovery. In contrast, the ransomware fragmentation we saw in 2025 introduced dozens of transient operators with no such incentive to invest any effort in decryption. An example is Obscura, whose encryption bug renders files over 1 GB permanently unrecoverable regardless of payment. For defenders and incident responders, consolidation means facing fewer but more capable adversaries.
Notable surges and declines
Comparing the data between Q4 2025 and Q1 2026 reveals which groups are absorbing the affiliate talent pool, and which are failing to take advantage of it.
Surges:
- The Gentlemen grew by 315%, going from 40 claimed victims to 166, making them the biggest story of Q1 2026, covered in detail below.
- LockBit 5.0 activity increased by 106%, from 79 victims to 163.
- Nightspire, a closed-group operation with OneDrive cloud encryption capability, expanded by 183% from 29 victims to 82, sustaining growth across two consecutive quarters.
- Play posted a 64% increase, going from 74 victims to 121.
Declines:
- SafePay fell by 77%, going from 97 victims to 22. SafePay is a centralized, non-RaaS operation whose DLS was marked inactive from mid-March 2026 through early April for unknown reasons.
- Devman declined by 70%, from 82 victims to 25. The ransomware’s operator “Tramp”, a former Conti and Black Basta affiliate, was added to Interpol’s wanted list in January 2026. All three DLS sites went offline by early February.
- Sinobi dropped by 42%, from 139 victims to 80. After a strong January (56 victims), activity collapsed to just 7 victims in March. As of the time of this publication, no postings were recorded in April.

Actor Spotlight: The Gentlemen – The Breakout Story of Q1 2026
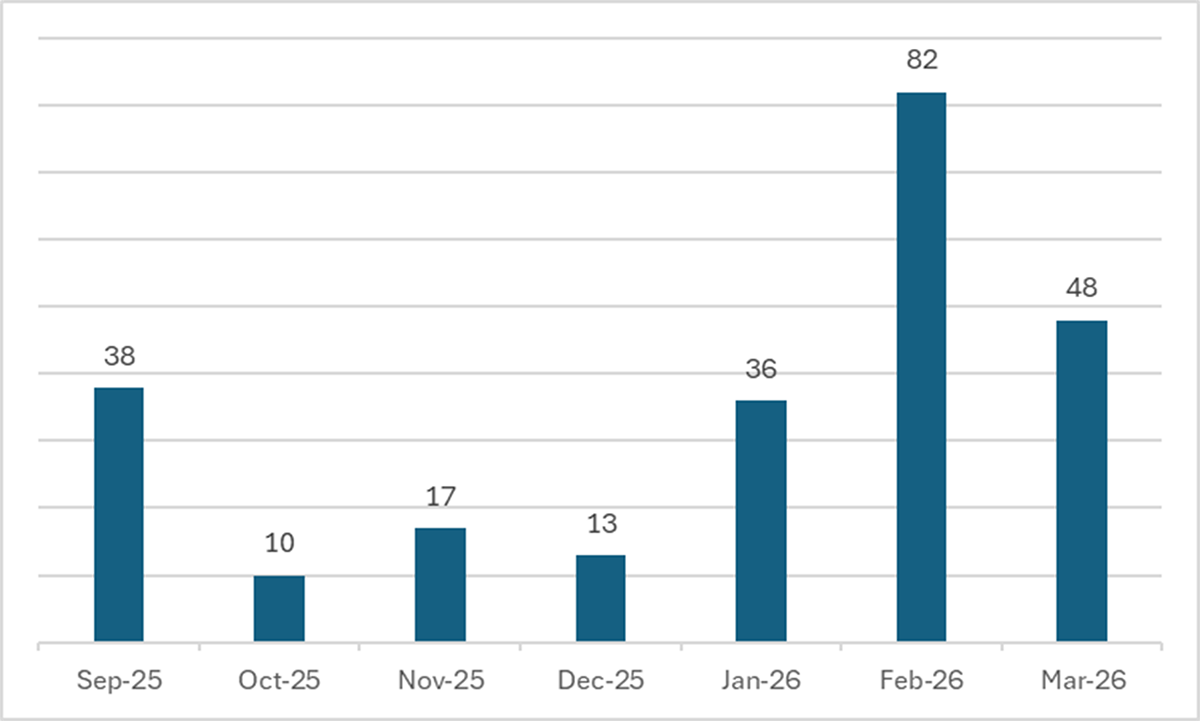
The Gentlemen is the most significant new ransomware operation to emerge in recent months. Going from zero victims in August 2025 to 166 in Q1 2026, the group achieved third place globally through a combination of pre-existing access stockpiles, aggressive geographic diversification, and a deliberate rejection of the traditional US-centric targeting model.
Origins: A Qilin defection
The Gentlemen was founded by a threat actor known as Hastalamuerte – an experienced Qilin affiliate, who left the Qilin RaaS program following a dispute over an unpaid commission of approximately $48,000. This explains both its rapid operational capability and its sophistication: the operators started with established tradecraft, tooling, and, crucially, a stockpile of pre-compromised access.
The FortiGate stockpile
The group’s most distinctive asset is a cache of approximately 14,700 pre-exploited FortiGate devices, exploited primarily via CVE-2024-55591 (a critical authentication bypass in FortiOS/FortiProxy). In addition to the exploited devices, the operators maintain 969 validated brute-forced FortiGate VPN credentials ready for attack. This stockpile provides The Gentlemen with a supply of ready-to-use initial access tools far exceeding what typical RaaS affiliates acquire through real-time exploitation or access broker purchases.
How was this stockpile acquired? According to this report, Hastalamuerte was an experienced affiliate who had previously worked with Embargo, LockBit, and Medusa before joining Qilin. Before creating their own RaaS platform, The Gentlemen’s operators “experimented with various affiliate models used by other prominent ransomware groups.” The 14,700-device inventory likely predates the group’s September 2025 launch. Publishing 38 victims within weeks of beginning operation strongly suggests pre-existing access in the form of a massive number of compromised devices rather than real-time exploitation.
A non-Western targeting model
The Gentlemen’s geographic distribution is a striking outlier. Only 13.3% of its victims are based in the United States, compared to the ecosystem average of 49.6%. Thailand (10.8%), Brazil (6.0%), and India (4.2%) all feature prominently on their victim list.
This may reflect the geographic distribution of exploitable FortiGate devices; the group attacks where it has pre-positioned access, and that access happens to be concentrated in APAC and Latin American networks. This is an infrastructure-driven pattern rather than a deliberate targeting strategy: the operators did not choose Thailand or Brazil based on strategic preference but are exploiting access they already have.
However, we cannot exclude a secondary factor: deliberate avoidance of US targets to reduce law enforcement risk. The Gentlemen is a Russian-speaking operation founded by an affiliate who already experienced the consequences of ransomware ecosystem disputes. The decision to exploit a globally distributed stockpile while bypassing US devices – if that is what is occurring – would represent rational risk management given the heightened US law enforcement posture.
LockBit 5.0: Making a Comeback
LockBit posted 163 victims in Q1 2026 (an increase of 106% compared to Q4 2025), climbing from outside the top 10 to fourth place globally. After an initial surge of 85 victims in January (likely to reflect the accumulation of access during the pre-launch period), activity dipped to just 33 victims in February before climbing back to 45 in March. This dip-and-recovery trajectory is characteristic of a program rebuilding its affiliate base instead of exhausting a one-time stockpile, assuming these are genuine reports and not recycled or fictional reports.
Until its takedown in early 2024, LockBit was the most dominant RaaS operation globally, responsible for 20–30% of all data-leak site victim postings. Following Operation Cronos, several arrests and data seizures disrupted the group’s infrastructure.
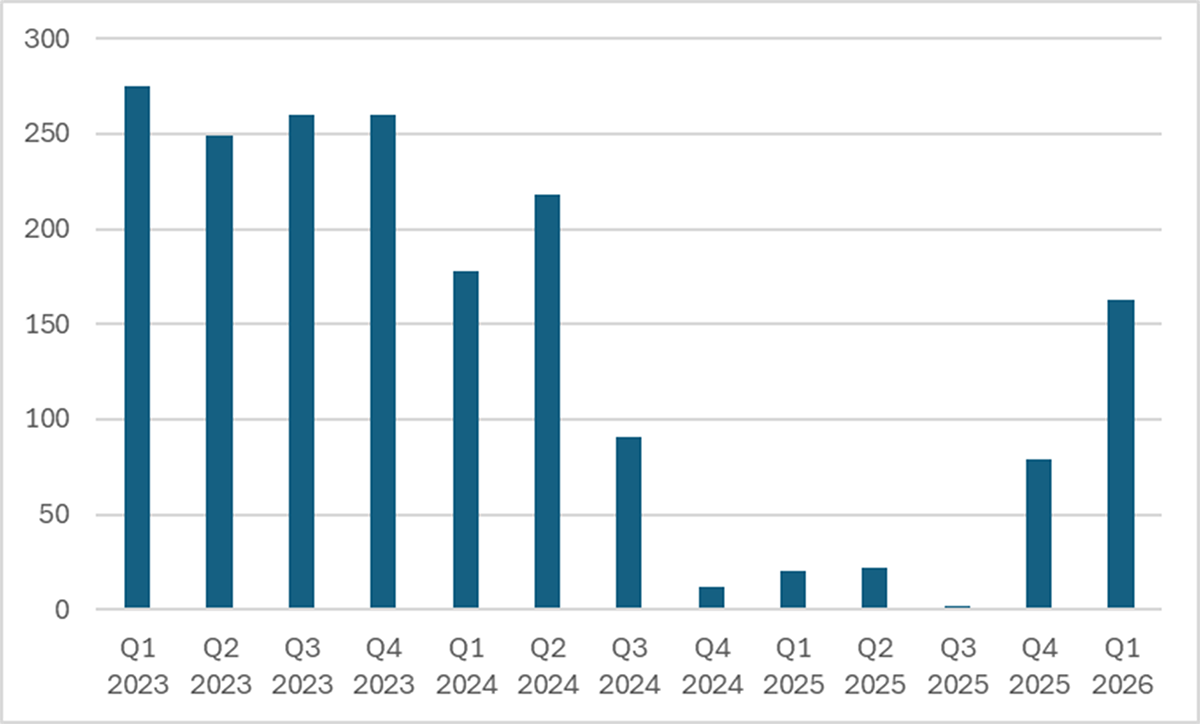
The new LockBit 5.0 was officially launched on the RAMP underground forum in September 2025, coinciding with the sixth anniversary of the operation. The new version introduced multi-platform support (Windows, Linux, ESXi), enhanced evasion and anti-analysis mechanisms, faster encryption routines, and randomized 16-character file extensions to disrupt signature-based detection. New affiliates were required to provide a Bitcoin deposit of approximately $500.
Geographic diversification: from US dominance to global spread
LockBit’s geographic targeting has undergone a dramatic and measurable shift since its last appearance. Historically, the United States accounted for over 50% of LockBit’s victims – consistent with the ecosystem-wide baseline. In Q1 2026, US victims represented just 21.2% of LockBit’s total, with Italy (8.6%), Brazil (8.6%), and Turkey (5.1%) picking up the slack.
The shift away from US victims is new. Despite no documented forum announcements, the circumstantial evidence is strong: the direction is specifically toward non-US and European nations or countries with less aggressive behavior toward ransomware operators such as Italy, Brazil, and Turkey. The result is a nearly 30-percentage-point (pp) drop in US-based victims, despite an overall 106% increase in victims compared to Q4 2025.
The reaction to law enforcement actions may not result in a lower overall attack volume, but operators such as LockBitSUpp appear to be trying to redirect their activity away from the enforcing jurisdictions. Whether this represents a deliberate strategic decision or an emergent consequence of attracting affiliates from different geographic backgrounds remains an open question.
DragonForce: The Cartel Model Under Pressure
DragonForce posted 101 victims in Q1 2026 (an increase of 29% compared to Q4 2025), with a steep climb from 10 victims in January to 35 in February and 56 in March. This trajectory suggests an operation gaining momentum rather than depleting stockpiled access.
DragonForce continues to distinguish itself through its public relations strategy and “cartel” branding, positioning itself as an umbrella organization for multiple sub-brands. However, our investigation indicates that the cartel model is smaller than advertised:
- Devman, which split from DragonForce in July 2025, saw their victim totals collapse from 82 (Q4 2025) to 25 (Q1 2026). Twenty-four of those victims were posted in January.
- Coinbase Cartel, initially reported as a DragonForce sub-brand, has been independently linked to the ShinyHunters operation by Bitdefender.
- Obscura, cited as a potential cartel member, posted only around 20 victims in total.
DragonForce’s technical capabilities remain genuine with multi-platform support and the group actively recruits affiliates. Its data audit service, which analyzes stolen datasets exceeding 300 GB to identify the most valuable information for extortion leverage, represents genuine innovation in the extortion model. However, the broader cartel narrative appears to be more marketing than substance.
Geographic Distribution of Victims – Q1 2026
The geographic distribution of ransomware victims in Q1 2026 maintains the fundamental pattern established over previous quarters: the United States accounts for just under half of all reported cases (49.6%), with Western developed economies making up the clear majority of targets.
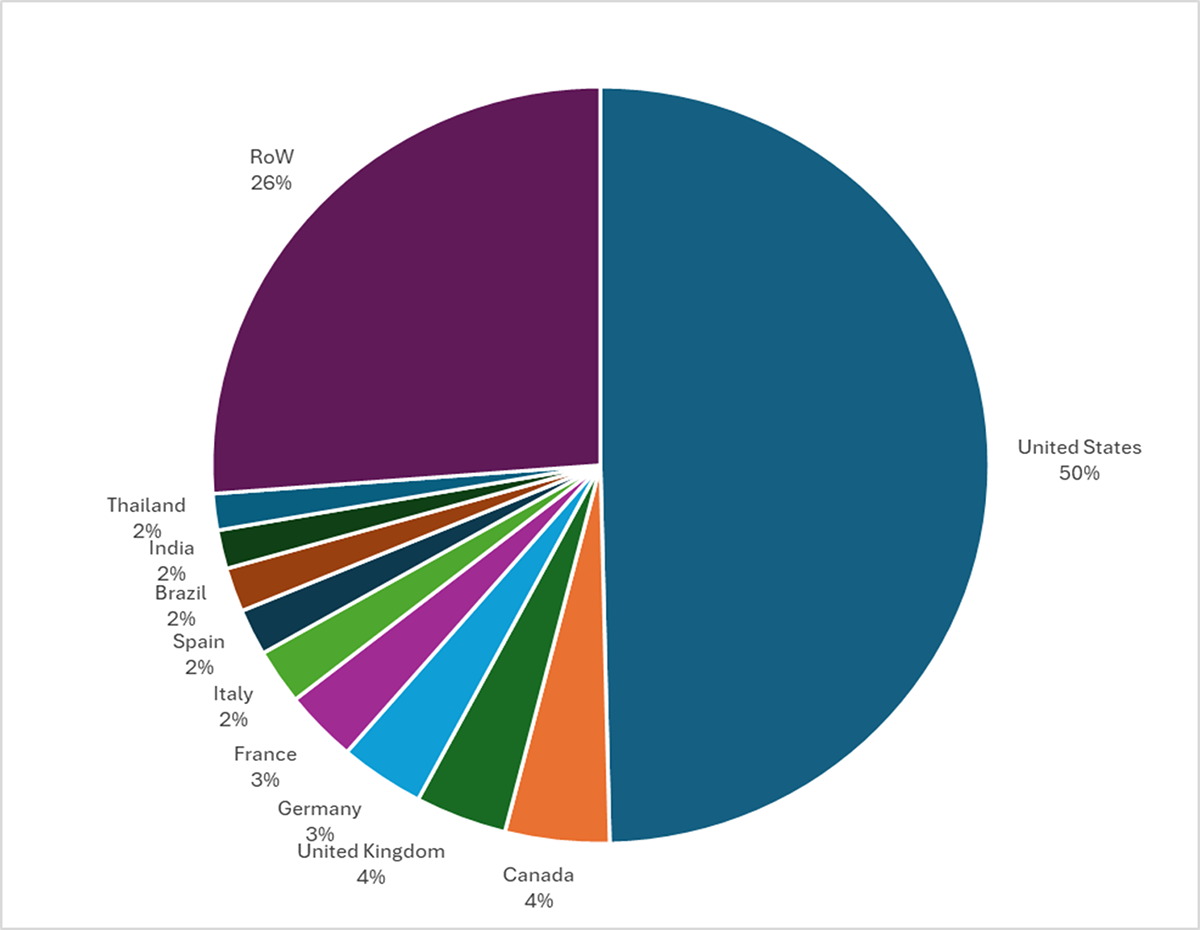
The most notable development is Thailand’s entry into the top 10 for the first time, driven almost entirely by The Gentlemen, for whom Thai organizations constitute 10.8% of total victims. Taiwan also rose sharply (from 8 victims to 26), while South Korea dropped out entirely. This confirms that Qilin’s Q3 2025 financial sector campaign targeting 30 South Korean organizations was a one-off event rather than a sustained targeting shift.
Per-Actor Geographic Targeting: Distinct Patterns
A per-actor analysis of the top 20 groups’ country distributions reveals that the ecosystem-level averages mask dramatically different targeting strategies. We identified six distinct geographic patterns by measuring each actor’s deviation from the 49.6% US baseline.
Pattern 1 – Extreme US focus (>75% US). These actors target the United States at rates far exceeding the ecosystem average:
- Play (85.1% US) operates as a closed group with a Russia-nexus lineage and centralized target selection that consistently prefers US organizations.
- Sinobi (76.2% US) explicitly targets US mid-market manufacturing and construction.
- Genesis (93.1% US) whose near-exclusive US focus (27 of 29 confirmed victims) and emphasis on the Healthcare sector (20.7%) is striking for an emerging actor with no documented affiliate program.
Pattern 2 – Deliberate US avoidance (<25% US). These actors are going in the opposite direction:
- Tengu (11.4% US) is the most geographically diversified actor in the top 20, with victims spread across Indonesia (8.6%), Mexico (8.6%), India (6.9%), and Italy (5.8%).
- LockBit (21.5% US) represents deliberate post-disruption diversification, as discussed above.
Pattern 3 – Vulnerability related distribution:
- Cl0p’s geographic anomalies (18.1% Canada and 8.7% Australia). Cl0p’s traditional mass exploitation campaigns produce victim distributions that mirror the installed base of the exploited software, in this case EBS campaign (CVE-2025-61882).
- The Gentlemen (13.3% US) reflects the geographic distribution of its approximately 14,700-device FortiGate access stockpile, which is concentrated in Thailand (10.8%), Brazil (6%), and India (4.2%).
Country-Level Actor Dominance: When One Group Shapes a Nation’s Threat Profile
Flipping the analysis from “which countries does an actor target” to “which actors dominate each country” reveals an even more striking picture. Several countries’ entire ransomware threat profiles are defined by a single actor’s operational choices.
Single-actor-shaped countries:
| Country | Dominant actor | Share |
|---|---|---|
| Thailand | The Gentlemen | 53% |
| Argentina | Qilin | 39% |
| Mexico | LockBit | 37% |
| Australia | Cl0p | 34% |
| Switzerland | Akira | 31% |
| Brazil | LockBit | 31% |
Thailand’s case is the most extreme: more than half of all Thai ransomware victims are claimed by The Gentlemen. Without this single group, Thailand would not even appear in the top-10 most-attacked countries. Similarly, without Cl0p’s Oracle EBS campaign, Australia and Canada would show substantially lower victim counts. These findings underscore that country-level ransomware statistics are frequently shaped by one actor’s specific access inventory, software exploitation campaign, or strategic redirection – not by broad shifts in the threat landscape.
Multi-actor convergence countries. Two countries stand out for having three or more actors independently converging to create unusually diverse threat environments:
- Turkey (23 victims): LockBit (6 victims) + DragonForce (5 victims) + The Gentlemen (5 victims), 70% of Turkey’s victim totals are due to the activity of just three actors.
- Japan (21 victims): The Gentlemen (6 victims) + Everest (4 victims) + Nightspire (3 victims). = 62% of the victims are due to three distinct actors. Both The Gentlemen and Nightspire exploit the same FortiGate vulnerability (CVE-2024-55591).
Ransomware Attacks by Industry – Q1 2026
The industry distribution of ransomware victims in Q1 2026 shows continued cross-sector impact, with a few notable concentrations.
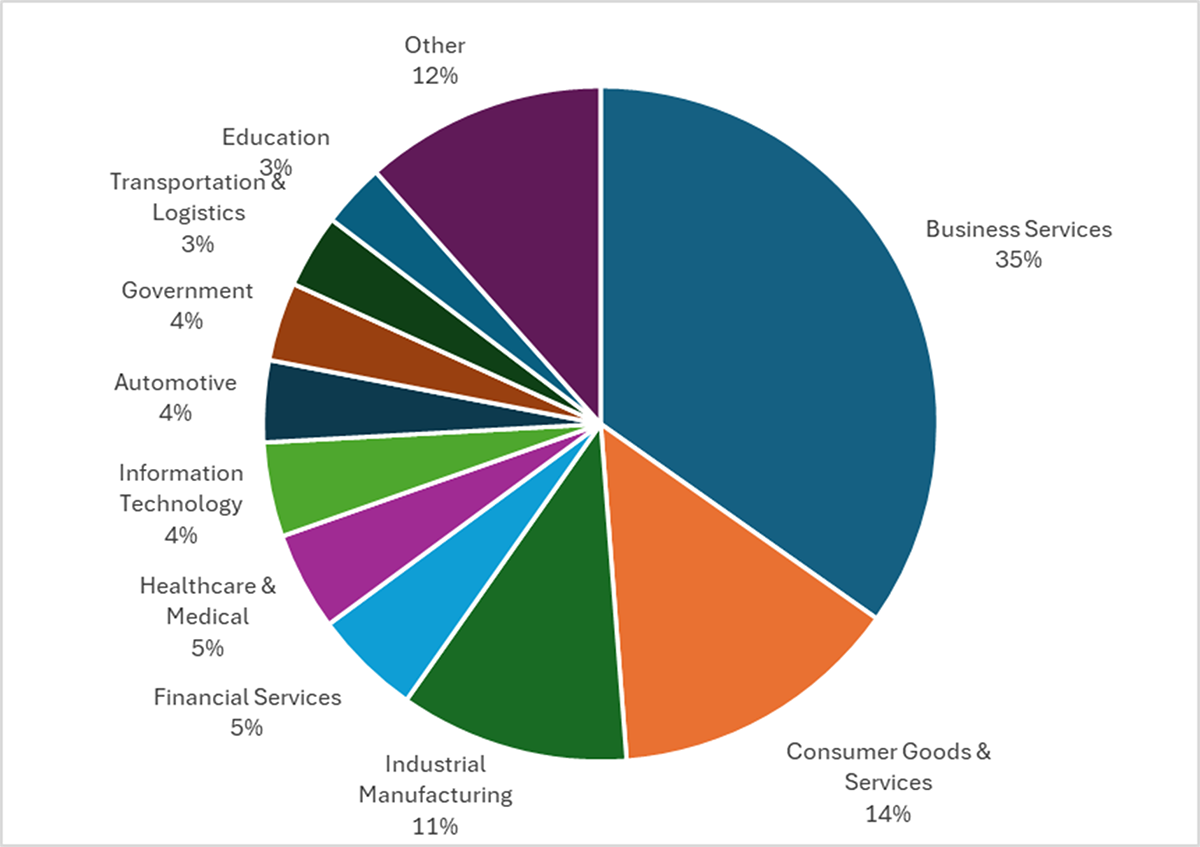
As with geographic patterns, ecosystem-level industry averages mask fundamentally different targeting strategies at the actor level. A per-actor analysis of the top 20 groups reveals that sector selection is driven by at least three distinct observations.
Software footprint targeting. Cl0p’s 53.5% Business Services concentration (+18.6 percentage points above baseline) does not reflect a preference for professional services firms. It reflects the user base of Oracle EBS, the enterprise application exploited in the Q1 2026 campaign. Mass exploitation campaigns produce industry distributions that mirror the deployment pattern of the exploited software. This is the same dynamic observed in Cl0p’s geographic analysis, where Canada and Australia were over-represented because of Oracle EBS adoption.
Operational disruption maximization. Akira’s targeting of Consumer Goods (23.9%, +9.8 percentage points above baseline) and Industrial Manufacturing (17.8%, +6.7 percentage points above baseline), a combined 41.7% versus the 25.1% baseline, is consistent with an economically optimized model. These sectors share high downtime costs (production lines, supply chain dependencies) and complex IT/OT environments that make recovery without decryption keys extremely difficult. With $244 million in total proceeds and a 34% share of IR engagements, Akira’s sector selection reflects deliberate targeting of firms where the pressure to pay is greatest. This is not opportunistic; it’s the Conti lineage playbook applied to the sectors where it generates the highest return per incident.
Anubis stands apart from all other top-20 actors in its willingness to target healthcare (13.0%, +8.3 percentage points above baseline) and critical infrastructure (8.7%, +7.7 percentage points above baseline).
Conclusion
In Q1 2026, the ransomware ecosystem entered a new phase. After two years of steady fragmentation, the market is reconsolidating around a smaller number of dominant operators. Qilin, Akira, The Gentlemen, and LockBit together account for 41% of all victims. Domination by the top-10 actors has returned to levels not seen since early 2024.
This consolidation is not a return to the previous state. The emerging dominant groups are more technically capable, more geographically diversified, and more resilient to disruption than their predecessors. At the same time, the economic foundations of ransomware are showing signs of stress. Payment rates have fallen to historic lows. Mass data-theft campaigns are generating diminishing returns. The gap between the growing number of DLS-posted victims (2,122 in Q1 2026) and the declining monetization per victim may accelerate the current consolidation squeezing out operators who cannot achieve sufficient scale or sophistication to remain profitable.
如有侵权请联系:admin#unsafe.sh