
Hassan Ud-Deen |Friday, 1 May 2026 2026-5-1 06:52:0 Author: portswigger.net(查看原文) 阅读量:30 收藏
Hassan Ud-Deen | Friday, 1 May 2026 at 06:52 UTC
Senior pentesters have a deeply refined intuition about what is vulnerable in an environment. The problem? That expertise is often siloed with an individual and trapped in their notes or Python scripts.
When seniors are at capacity, coverage gaps open up precisely where your environment relies on specialist knowledge.
Custom scan checks in Burp Suite help encode that hard-won knowledge into repeatable tests, so expertise can scale across the teams, applications, and workflows that need it.
Even with thousands of applications and APIs to test, and expertise split between multiple testers, custom scan checks help you:
- React faster to critical threats.
- Tailor testing to individual tech stacks and domain-specific business logic.
.png)
1. Rapid response to zero-days and CVEs
The moment a critical CVE is disclosed, the clock starts. It is only a matter of hours before it is actively exploited in the wild. Even after security teams develop a reliable probe for the vulnerability, checking thousands of target apps and APIs manually leaves your estate exposed.
Turning a manual proof of concept into a custom scan check lets you scale testing for specific signatures across your entire portfolio. This helps identify, validate, and remediate the exposure before an exploit hits your perimeter.
Instead of relying on a pentester to manually probe app by app, you encode that understanding into every scan that Burp Suite DAST runs in your environment. With detection logic defined by your own researchers, you move from “understanding the issue” to “knowing where to act” across thousands of applications in a fraction of the time it would take to wait for a vendor-supplied update.
When React2Shell was publicly disclosed, for example, PortSwigger Research immediately developed and released a custom scan check using our powerful extensibility API. This got the check into the hands of potentially vulnerable users without them waiting for a new product release.
We then worked with a major MSSP that was using it in live emergency engagements, feeding back what they were seeing as they went. Once the test case had been refined through manual testing, they were able to quickly roll it out at scale in Burp Suite DAST.
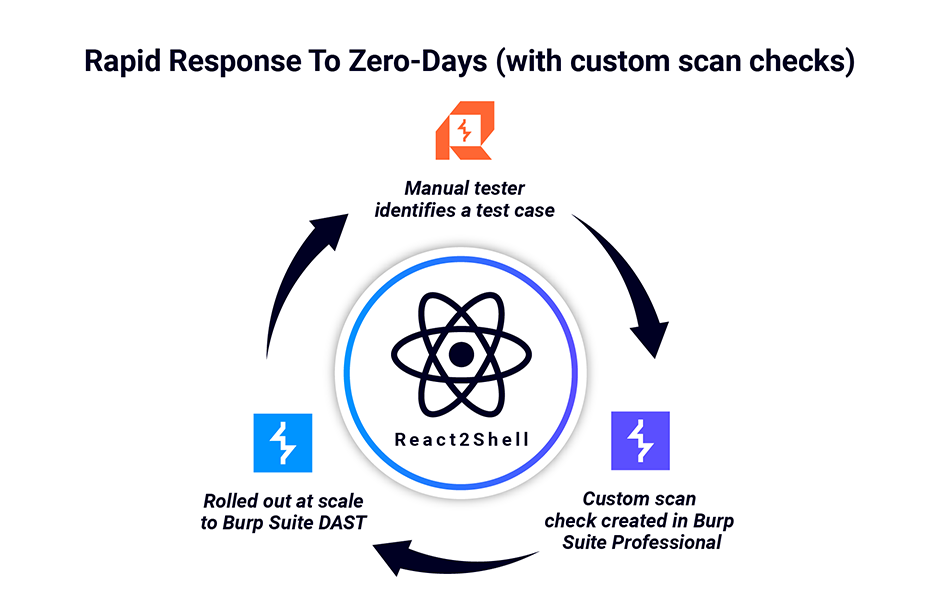
Burp Suite empowered them to find a critical vulnerability once, and then test for it everywhere.
But rapid threat identification and response at scale is just one of the many use cases for custom scan checks.
Across the 18,000+ security teams that trust Burp Suite, we often see teams encode testing logic as a reusable, high-value security asset for effective coverage.
Quick tip: Burp Suite DAST shares the same scan engine as Burp Suite Professional. So a custom scan check can export from a pentester’s workbench to your entire automated fleet in minutes. This allows you to hunt for critical vulnerabilities at scale using the exact logic your team trusts.
2. Turn expert logic into repeatable coverage
Effective AppSec teams treat their testing logic as a reusable security asset rather than a one-off task. Over time, this creates a compounding effect. The system gets smarter with every engagement, ensuring that expertise does not reset every time a person moves between teams.
- Institutional memory: A custom scan check written to find a unique WAF bypass or an exposed
.envfile outlives the engagement it was created for, becoming a permanent part of your testing standard. - Junior-senior leverage: Senior testers can package their “gut instincts” into custom scan checks, allowing junior members of the team to benefit from high-level logic they might not yet be able to reproduce manually.
- Automating bespoke workflows: You can reuse existing scan configurations and powerful extensions developed in-house to find vulnerabilities that default scans miss entirely.
- Defensible standards: By codifying your testing standards, you ensure coverage is no longer dependent on who happens to pick up the work. The same expert-level logic is applied consistently across every application in the portfolio.
The real opportunity with custom scan checks is building a bi-directional ecosystem where manual and automated testing reinforce each other.
For example, another pattern we see across teams is using custom scan checks to detect secrets and sensitive data embedded in HTTP responses. This includes:
- API keys hidden in JavaScript bundles.
- AWS credentials sitting in frontend code.
- Exposed
.js.mapsource map files that hand attackers your original source code.
These are the kinds of findings that make headlines, and they are notoriously hard to catch at scale without automation.
3. Encode environment-specific testing standards
Missing CSP headers or CORS misconfigurations can have severe consequences, but they are easy to miss, especially when the risky behavior depends on how your applications and services are configured. Custom scan checks let you turn those, and many other environment-specific testing expectations, into repeatable tests that run at scale.
For example, if your microservices rely on X-Tenant-ID headers to enforce tenant separation, you can codify checks that look for places where tenant context is missing, inconsistent, or handled in a way that could expose cross-tenant data.
This shift ensures that testing quality is no longer a roll of the dice based on which tester picked up the ticket.
By making these standards explicit and automatable, you ensure that the “scent” of a vulnerability — something a senior tester might find by instinct — becomes a permanent, repeatable part of your security baseline.
Practitioner knowledge is consistently applied across more applications without forcing every tester to rediscover the same issue by hand.
Quick tip: You can use Burp Collaborator in active custom scan checks to detect vulnerabilities that require out-of-band interaction testing. This enables you to build checks that detect out-of-band issues, and define how Burp handles and reports them.
Scale coverage of high-impact vulnerabilities
If your team already relies on Burp Suite Professional day to day, custom scan checks are one of the most practical ways to start making that expertise more reusable now.
They let you take the checks your testers already trust and apply them more consistently across the work you are already doing to identify high-impact threats. Whether that is checking for newly disclosed CVEs, recurring business-logic weaknesses, or environment-specific standards.
A good next step is to start small:
- Identify one high-value check your team repeats manually.
- Turn it into a custom scan check.
- Make it part of your regular testing approach.
From there, a more strategic question naturally follows: if this logic is valuable in Burp Suite Professional, how far can it scale across the rest of your application estate?
For many AppSec teams, that means reducing the gap between the manual testing workflows they already depend on in Burp Suite Professional and the broader automated coverage they need elsewhere.
That is where pairing Burp Suite Professional with Burp Suite DAST becomes interesting: it gives teams a way to extend the same testing logic, expertise, and workflows they already trust into more consistent coverage at scale.
如有侵权请联系:admin#unsafe.sh