The post Cyber Resilience as Capital Planning: Quantifying Risk appeared first on CyberSaint Blog.
For decades, the cybersecurity budgethas been treated as part of Operational Expenditure (OpEx), a necessary “tax” on doing business, much like insurance or electricity. Security leaders have traditionally fought for budgets based on fear, uncertainty, and doubt, often struggling to justify the return on investment for tools that ideally result in “no change”.
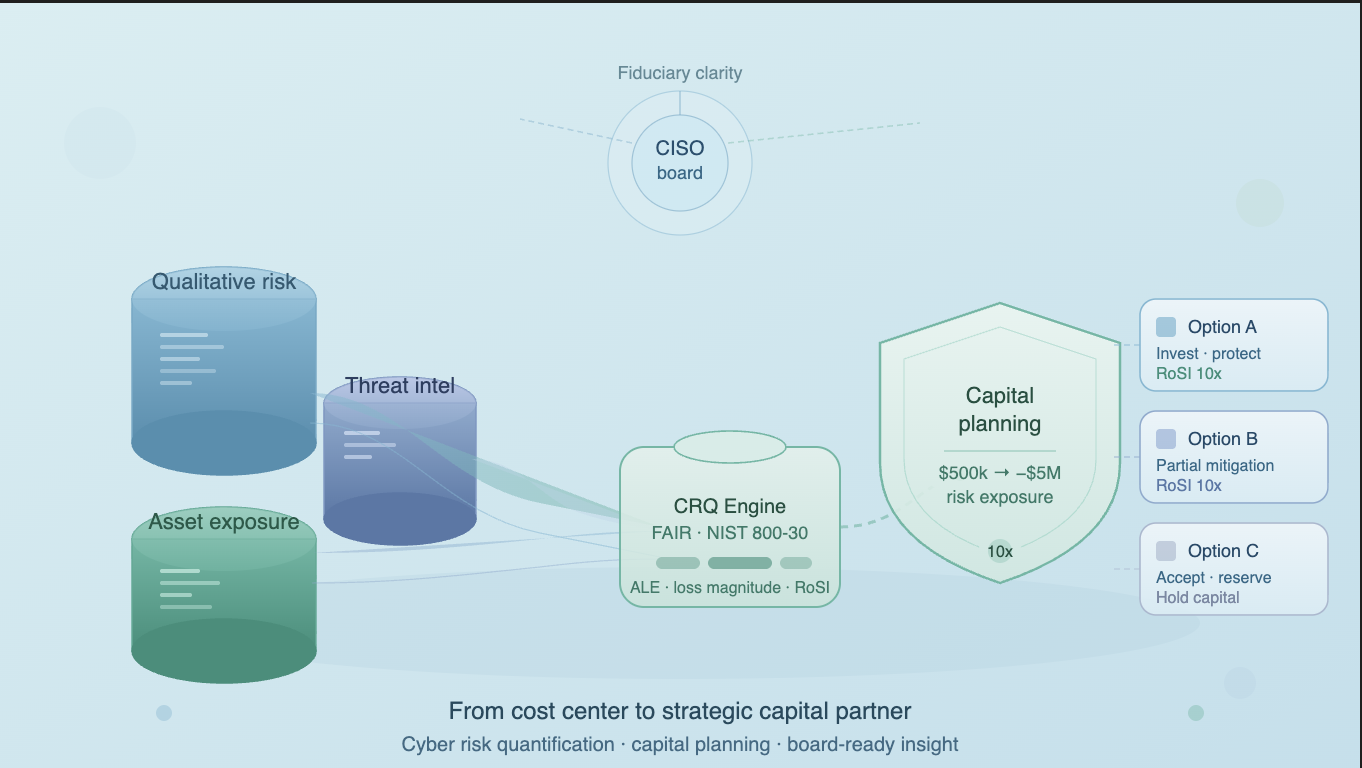
![]()
*** This is a Security Bloggers Network syndicated blog from CyberSaint Blog authored by Padraic O'Reilly. Read the original post at: https://www.cybersaint.io/blog/cyber-resilience-as-capital-planning-quantifying-risk