International espionage isn’t always about sophisticated malware and zero-day bugs. Sometimes it’s as simple as pretending to be someone else asking for a favor.
For four years, a Chinese aerospace engineer did just that. Dozens of researchers at NASA, the US military, and major universities handed him exactly what he asked for, and possibly violated US laws in the process.
His name is Song Wu. He’s been on the FBI’s wanted list since September 2024, charged with 14 counts of wire fraud and 14 counts of aggravated identity theft, and he’s still at large.
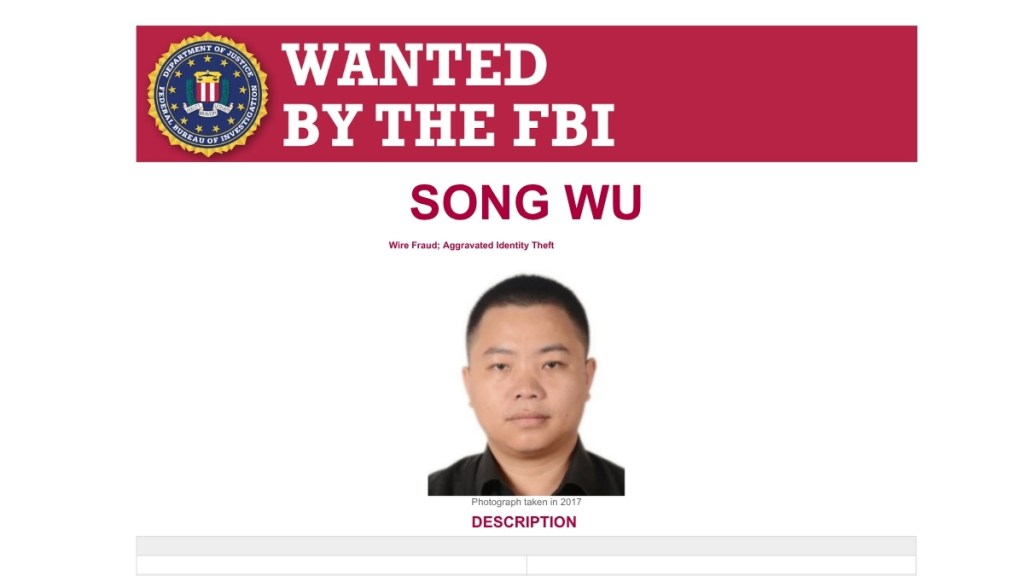
Wu’s day job was as an engineer at the Aviation Industry Corporation of China (AVIC), a Beijing-headquartered state-owned aerospace and defense conglomerate with over 400,000 employees. The US has AVIC and several subsidiaries on a sanctions list.
His side hustle was simpler. From January 2017 through December 2021, Wu set up email accounts impersonating real US researchers and engineers, then emailed their colleagues asking for source code and proprietary software. He targeted employees at NASA, the Air Force, Navy, Army, and FAA, and faculty at universities across the US.
When software is a weapon
The applications Wu was after handle aerospace engineering and computational fluid dynamics. It’s the kind of intellectual property that helps develop advanced tactical missiles and evaluate weapons performance, and it sits squarely inside US export controls, according to NASA’s Office of the Inspector General. Sharing it with the wrong person, even by accident, is a federal problem.
Some victims did transmit the requested code. They were, in the OIG’s careful phrasing, “unwittingly” violating export control law.
How a four-year campaign finally broke
It wasn’t a firewall that caught Wu. It was a tip.
NASA’s Cyber Crimes Division got a report that someone had set up a Gmail account claiming to be an established aerospace professor who frequently collaborated with NASA. From that single thread, investigators unwound a campaign that had quietly targeted dozens of researchers across the federal government and academia.
The OIG also noted the giveaways: Wu asked for the same software multiple times and never explained why he needed it. Those are tells that anyone could have spotted on a slow afternoon if they’d been looking.
What’s coming next
Wu’s campaign worked for four years using nothing more sophisticated than fake email accounts and decent target research. He’s one engineer, but the problem is far bigger than him.
Then-FBI Director Christopher Wray told the House Select Committee in 2024 that:
“the PRC has a bigger hacking program than every other major nation combined.”
Chinese hackers would still outnumber FBI cyber personnel 50 to 1 even if every US cyber agent worked nothing else, he said.
Social engineering continues to be a problem, and impersonators are getting more convincing thanks to the use of deepfake technology. Online criminals are using voice cloning and even deepfake video to infiltrate their targets by posing as job interviewees. And others are flipping the script, posting as recruiters on LinkedIn to fool would-be job candidates into downloading malware.
Spear-phishing was problem enough when it was one guy in Beijing with a Gmail account. It’s going to become a much bigger problem when the next Wu uses generative AI to draft the emails, clones a real researcher’s writing voice, and runs the playbook at machine speed across a thousand inboxes.
Browse like no one’s watching.
Malwarebytes Privacy VPN encrypts your connection and never logs what you do, so the next story you read doesn’t have to feel personal. Try it free →

