
嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”之类的开头。我先看看这篇文章讲了什么。 文章主要描述了作者参加2026年在Reims举行的Botconf大会的经历。他做了一个关于识别恶意软件代码相似性的 workshop,并且带去了特别的LockBite饼干。还提到了其他几位演讲者的主题和内容,以及晚宴的活动。 好的,我需要把这些信息浓缩到100字以内。重点包括:大会地点、时间、参与者人数、workshop内容、LockBite饼干的制作和分发、其他演讲者的主题,以及晚宴的情况。 可能的结构是:Botconf大会在Reims举办,作者分享了识别恶意软件代码相似性的 workshop,并制作了LockBite饼干。其他演讲者探讨了DDoS市场、恶意软件家族、Golang逆向工程等主题。晚宴在香槟酒窖举行,气氛愉快。 检查一下字数是否合适,确保不超过100字。这样应该可以满足用户的需求。 </think> 2026年Botconf大会在法国Reims举行,吸引了近400名参与者。作者分享了识别恶意软件代码相似性的workshop,并制作了特别的LockBite饼干。会议期间,多位演讲者探讨了DDoS市场、恶意软件家族及Golang逆向工程等主题。晚宴在香槟酒窖举行,气氛热烈。 2026-4-27 09:20:49 Author: maxkersten.nl(查看原文) 阅读量:16 收藏
For the 2026 edition of Botconf, and the 13th edition overall, we found ourselves in Reims. From the 14th through the 17th of April, nearly 400 attendees gathered in what has become a yearly pilgrimage for many. As with the previous editions, the food, atmosphere, and talks were well worth a visit.

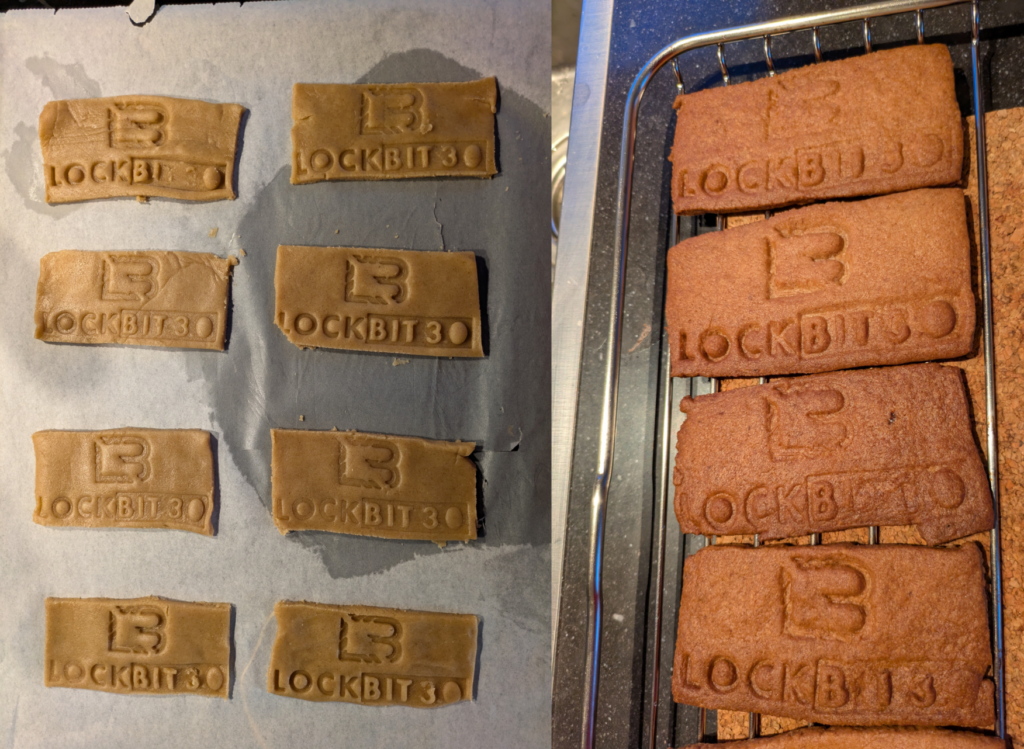
This year, I gave a workshop on recognizing code similarity between malware samples. This year, I brought a surprise for the attendees. As a backstory, we need to go back to 2024, when Bea gave me a cookie stamp with the LockBit 3 logo on it to make LockBite cookies. They designed it and used their 3D printer to print the stamp. They made LockBites for a workshop. While I wasn’t there, I did like the idea, and ever since I got the cookie stamp, I wanted to make these cookies and hand them out during a workshop. Whereas this wouldn’t seem to be an issue, there are two problems that arise that hindered my attempts until now.
First, the time between making the cookies and giving the workshop. To take summercamp in Las Vegas as an example: I’d leave on Monday morning early from home to leave for the airport, meaning I’d need to make the cookies the evening prior. Due to the magic of time difference, I’d also arrive in Las Vegas on Monday afternoon. The past few years I gave workshops at DEFCON, which ranged anywhere between Friday and Sunday. As such, the cookies would need to travel halfway across the world and stay tasty for nearly a week. Needless to say, that’d not be the most enjoyable experience.
The second reason is even more relevant: its not allowed to bring in fresh produce/food into most continents, when coming from another continent. Traveling from Europe to the US (or from Europe to Asia or Oceania for that matter) would make it impossible to bring said cookies.
Given that Reims is a drivable distance from The Netherlands, and the fact that Botconf’s workshops are on the day prior to the conference, I could bake the cookies on Sunday evening, travel on Monday, and hand them out on Tuesday. And that is exactly what I did!
The cookies were tasty per the attendees (and per myself, but that’s a rather biased opinion). Aside from that, the workshop went really well, barring some of the issues I had with the OVA image that I shared upfront. This year, Botconf also had a feedback form integrated for attendees, from which I received the following feedback (copied verbatim): “Great talk, extremely clear. He took time to re explain topics if anyone asked a question, which was helpful for those of us who don’t use ghidra daily!”. The feedback is anonymous, so I cannot thank the person who submitted it directly. If you did, thank you! I’m happy that the workshop was received as I intended it to be.
Talks
The following days were filled with talks. Next, I’ll discuss a few, but this is not an exhaustive list by any means.
Early on day, Maarten Weyns spoke about power proofs in the DDoS market, titled “Botnet Boasting: Investigating Power Proofs in the DDoS-for-Hire Market”. This talk dove into the nitty-gritty details behind the proof of a DDoS botnet’s power, including limits and the abuse of open servers online to monitor traffic. This talk was a great follow-up (of sorts) to last year’s DDoS talk by Maarten. Aside from the technical details, the slides were slick.
Later that day, Kyle Cucci gave a talk about Stealerium and PhantomStealer, and how they were related (and different) based on his tracking over time. The intricate relations between the two families, and the different branches within these families, became clear during the talk. Once again, Kyle’s talk kept us all entertained with technical insights paired with a healthy dose of humour.
Near the end of the day, Eric Howard gave a talk titled “Meet GopherWhisper: Uncovering an APT’s secrets through its own words”. For those who aren’t aware: I thoroughly enjoy reversing Golang based malware. Or in the words of a good friend and old colleague of mine: “you are mentally sick”. I’ll leave that decision to you. The talk itself dove into the used components in great detail, painting a clear picture of what the attackers did.
During the second day of the conference, Souhail and Alexey spoke about XLoader in their talk titled “Chasing XLoader: Tracking a Notoriously Complex Malware Family at Scale”. The technical analysis was, as Souhail and Alexey proved in the past, great. The AI segment of the talk was clear and did not shroud the process in mystery as some other articles tend to.
Later on the second day, Maddie and Charlie gave a talk about the macOS stealer ecosystem: “Mac-ulate Conception: The Birth of the macOS Stealer Ecosystem”. The talk didn’t serve to dive too deep into one single element, but rather to provide a clear overview of the (as the talk’s title implies) ecosystem as a whole. While I had heard of the common macOS stealer names, I haven’t really taken the time to reverse them, nor dive into the ecosystem itself. A solid overview while sticking to the facts made the talk enjoyable and informative.
The gala reception at the end of the second day was in a champagne distillery, if that’s the correct name. We had a tour through the 30 meter deep caves where the wine ages, and is turned into champagne. The location was beautiful, and was a great place to talk to friends old and new.
The third and final day of the conference was filled with talks. The first one I’d like to mention in this blog was by Andreas and Hanno, titled “When One Botnet Leads to Another: Pivoting from Quad7-like Activity to Unknown Proxy Networks on Embedded Devices”. The talk details how a seemingly random event, coupled with stubborn researchers, lead to a deep dive into an actual threat. The long-running collaboration was great to see, especially as Andreas and Hanno work for different employers which can sometimes make it more difficult.
The final talk I want to mention is by Fabian Marquardt, titled “Izanagi RAT: Discovery and Analysis of a Cross-Platform, Long-Lived Go Backdoor”. The Golang-based RAT (please refer to my odd Golang reversing preference) itself was interesting to see taken apart, especially given its years long existence without (public) reporting about it. Fabian was also present in my workshop, and was kind enough to give me a shoutout during the talk, as the workshop’s content could’ve helped him save quite some time during his original research.
All in all, I had a blast meeting new people and catching up with old friends. I’ve not named many in this blog out of respect for their privacy, but you know who you are. I thank you all for the good time, and I hope to see you next year at Botconf!
To contact me, you can e-mail me at [info][at][maxkersten][dot][nl], or DM me on BlueSky @maxkersten.nl.
如有侵权请联系:admin#unsafe.sh