
Most phishing advice is written for the person staring at a suspicious email. This guide is for the other kind of victim: The website owner whose legitimate site has been quietly turned into the attacker’s weapon.
You didn’t send the message or build the fake login page. You just woke up to a browser warning, a suspended hosting account, or a polite note from someone’s security team asking why your domain is requesting Apple ID credentials. What follows is how to find the phishing content, clean it up without inviting the attacker straight back in, and recover your reputation afterward.
It’s not always you they’re phishing
It’s common to find directories on legitimate sites with names like login-apple-account or secure-paypal-verify, serving pixel-perfect clones of real login pages. In one case we’ve written about before, a hacked WordPress site was used to host a fake “database upgrade” notice that redirected users to a spoofed WordPress login page designed to harvest admin credentials.
In many of these cases, the site owner isn’t the target. The attacker is borrowing the site’s clean reputation as camouflage. A legitimate domain, working HTTPS, and a clean record with Google Safe Browsing let a phishing page last longer, reach more inboxes, and fool more people than one hosted on a throwaway domain. That’s why this particular outcome is one of the more damaging things that can follow a successful compromise.
How you usually find out
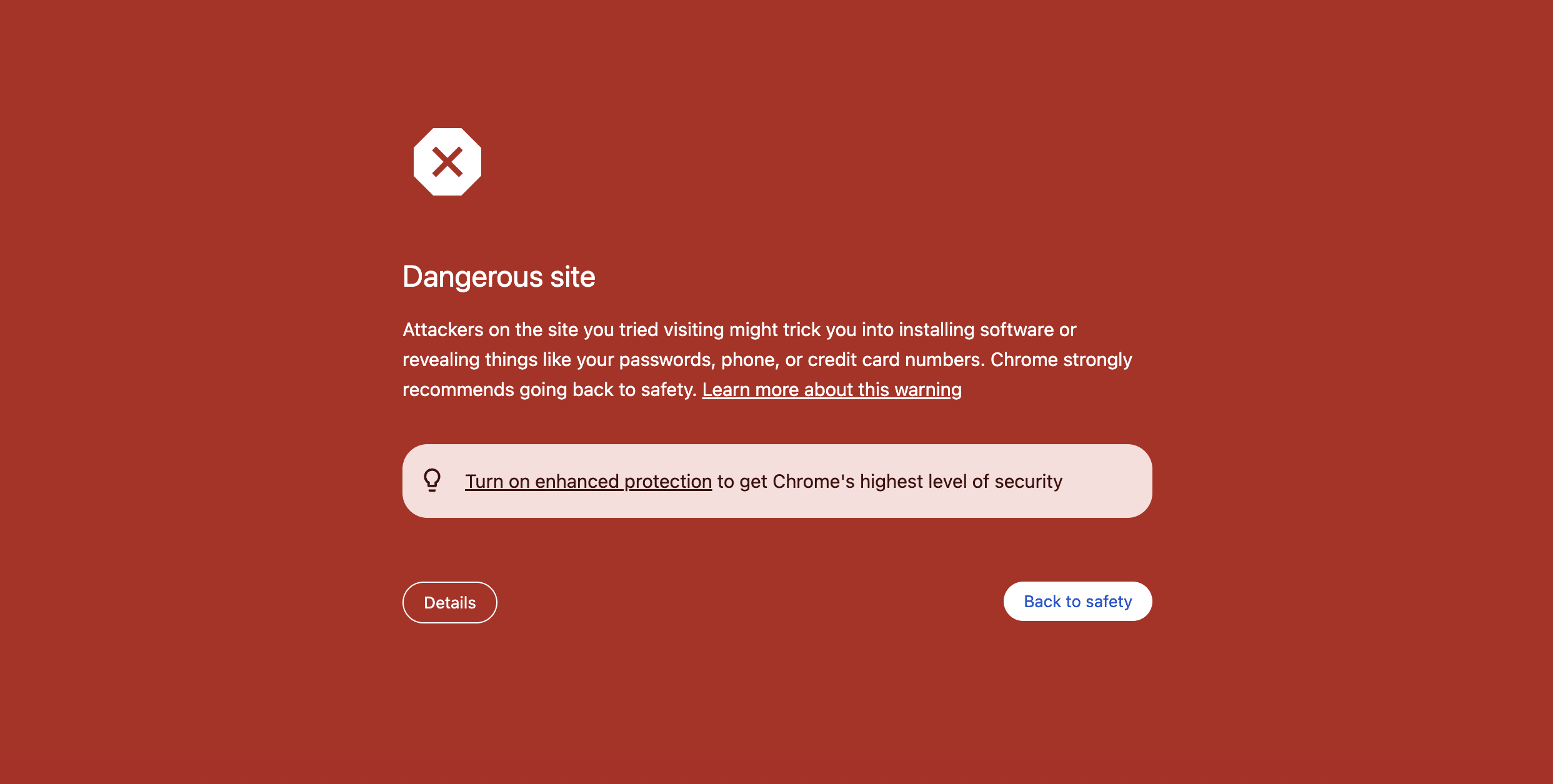
Very few owners discover this on their own. The first sign is almost always external. This could be a browser warning from Google Safe Browsing or Microsoft SmartScreen, an abuse notice or suspension from your host, or the realization that your outbound mail is bouncing because your domain has landed on a spam blocklist.
Sometimes the alert comes from a customer, a partner, or the security team of the brand being impersonated. Occasionally, it arrives as a sharp drop in search visibility or traffic after browsers and search authorities begin warning users away from the site.
Whichever channel brings the news, the page has usually been live for some time by the time you hear about it. The sooner you start, the less damage accumulates, both for the people being phished and for your own domain’s reputation.
How it got there
Before you start removing files, spend a few minutes narrowing down the root cause. Clean up the phishing kit but miss the entry point and you’ll be doing this again in two weeks. The usual suspects fall into a few buckets:
- A vulnerable or outdated plugin, theme, or CMS core is, by a wide margin, the most common cause of issues on WordPress sites.
- Stolen or brute-forced admin credentials are often harvested by a phishing attack against someone on your team.
- Compromised SFTP, FTP, cPanel, or hosting control panel passwords, especially ones reused across services.
- Cross-contamination on shared hosting, where a compromise on a neighboring site got used to pivot sideways onto yours.
- Forgotten staging environments, abandoned subdomains, or unmaintained sub-installations nobody has patched in years.
- Nulled or tampered plugins and themes from unofficial sources, which sometimes ship with backdoors preinstalled.
Keep that shortlist in mind as you investigate. You’re looking for the answer to “how did they get in?” and “what did they leave behind?”
Finding the phishing kit
Phishing kits leave a recognizable footprint, and a targeted search usually surfaces them faster than a full site audit.
- Start by looking for directories whose names impersonate well-known brands, like
login-apple-account,secure-paypal,office365-verify,chase-update, etc., most often in the web root or insidewp-content/uploads/. The uploads directory deserves a second pass specifically for.phpfiles, since legitimate uploads almost never contain executable PHP. - From there, widen the search. A list of files modified in the last two weeks will usually let you spot what doesn’t belong at a glance.
- Audit your WordPress users for admin accounts you don’t recognize, and scan
wp-cronfor unexpected scheduled tasks. - Check the outbound mail queue and your mail server logs as well. Phishing kits often ship with a PHP mailer script that sends lure emails from your compromised site, which is a fast way to pile up blocklist entries on top of the phishing page itself.
- Cross-check by running a free remote scan and review Google Search Console’s Security Issues report. Services like PhishTank.com and VirusTotal.com will also tell you whether your URL has already been flagged elsewhere, which is useful context both for cleanup and for the blocklist-removal work that comes later.
Also look for anti-bot or access-control files around the kit. We’ve found phishing kits that block search engines, security vendors, VirusTotal, PhishTank, hosting providers, and broad IP ranges so the phishing page returns an error to scanners while still loading for victims.
Don’t stop at the first suspicious file, and don’t rely on the homepage looking clean. If you only remove the phishing page, you’ve done maybe a third of the job. Phishing kits often coexist with backdoors, mailers, rogue admin users, or other persistence mechanisms. We’ve found phishing content buried in exact paths that aren’t linked from the visible site, meaning remote scanners may miss them unless they know the URL. Server-side scanning and file integrity monitoring are much more reliable for this.
Contain first, clean second
Order of operations here matters. The instinct to “just delete the bad files” could get your site re-infected the same afternoon. Work through these steps in sequence:
- Take the phishing content offline immediately. Rename the directory, block it at the web server, or move the files out of the web root. You don’t need a perfect cleanup to stop the bleeding.
- Take a full backup of the site in its current, infected state before you touch anything, and copy the phishing kit and any suspicious files into a quarantined folder outside the web root. You’ll want the evidence for abuse reports and the backup as a safety net if anything in the cleanup goes sideways.
- Rotate every credential the attacker could plausibly have touched. WordPress admin passwords, database passwords, SFTP and FTP, cPanel and hosting panel, SSH keys, API keys, and any third-party integration tokens. Don’t forget dormant or rarely used accounts. Those are exactly the kind of leftover access attackers like to hold onto.
- Force logout of all active sessions and revoke any SSH keys or panel sessions you don’t explicitly recognize.
Only after containment is complete should you proceed to a full cleanup.
Cleaning up
With containment in place, the cleanup itself is relatively mechanical. What matters is being thorough, because phishing kits and their accompanying backdoors are designed to survive a halfhearted purge.
- Delete the phishing files and directories outright rather than just renaming them, then hunt down every backdoor. The common patterns are short PHP files with obfuscated payloads (watch for base64, gzinflate, and eval combinations), files with randomized names tucked into uploads or wp-includes, and modified versions of legitimate core files.
- Reinstall WordPress core, plugins, and themes from official sources. Don’t trust the existing files, even the ones that look untouched.
- Remove any unfamiliar admin users.
- Review scheduled tasks.
- Inspect .htaccess, wp-config.php, and any must-use plugins for injected redirects or hidden include statements.
Finally, patch the root-cause vulnerability you identified earlier. Update the plugin, reissue the credentials, enable multi-factor authentication, and whatever matches what you found.
Getting off the blocklists
Getting the rest of the internet to believe you’ve cleaned your site can be slow. Expect anywhere from a few hours to several days.
Google Safe Browsing is usually the most urgent, since it drives both browser warnings and search visibility. You can request a review through Google Search Console once the site is verifiably clean. Microsoft SmartScreen has its own submission process through the Microsoft Security Intelligence portal, and if your URL was reported to APWG or PhishTank, both allow re-evaluation requests once the content is gone.
If your domain sends email, check the major email blocklists (Spamhaus, Barracuda) and loop in your hosting provider next if they haven’t already contacted you. If the phishing form was submitting data back to your domain rather than exfiltrating it elsewhere, you may have actual victim data sitting in server logs or a database table.
One note on timing: Don’t submit a review while malicious content is still present. That just resets the clock. Don’t rush it.
Preventing the next one
Once the fire is out, the honest question is why your site became a useful host for an attacker in the first place. The answer is often some combination of outdated software, over-permissive access, and a credential that lived somewhere it shouldn’t have.
The key habits to keep in mind are few and familiar:
- Keep WordPress core, plugins, and themes up to date. Unpatched third-party code is still the single most common entry point.
- Require multi-factor authentication on every administrative account, without exceptions.
- Use unique, strong passwords and a password manager, with least-privilege roles so that blog contributors aren’t sitting on administrator permissions they don’t need.
- Put a website firewall (WAF) in front of the site to block the automated reconnaissance that precedes most compromises.
- Turn on file integrity monitoring and continuous malware scanning so unexpected changes surface in minutes, and connect Google Search Console so security issues are flagged the moment Google sees them.
- Keep regular, tested backups stored offsite. A clean, recent backup is the difference between an afternoon of cleanup and a weekend of regret.
- Train your team to recognize phishing emails targeting them, because stolen admin credentials are a leading route into compromised sites.
Many sites that require cleanup have at least one of these controls missing. Our guide on Phishing Attacks & How to Prevent Them and how-to on cleaning a hacked website cover the broader playbook if you want to learn more.
Closing thought
Having your site used as a phishing host is one of the most common outcomes of any successful website compromise. It doesn’t mean you ran a careless operation or that your visitors can’t trust you, but it does mean someone found a small opening and used it to borrow your domain’s good name for a few days.
The goal, after you’ve closed the opening, is to make your site a worse target than the next one. And as always, if you believe your website has been compromised and you need a hand, our experienced analysts are available 24/7 to help clean up malware and restore your site.

