![]()
I’ve spent nearly 30 years in cybersecurity. I’ve seen a lot of “game changers” come and go. Mythos is different.
When Anthropic’s model chained 32 steps of a corporate network attack — start to finish — in hours, I wasn’t shocked. I was sobered. Because I’ve been telling enterprises for years: your flat network isn’t a security architecture. It’s a waiting room for attackers.
Mythos just proved the wait is over.
Here’s what I think every enterprise security leader needs to hear right now:
1. VLANs are not microsegmentation — and the difference is costing you.
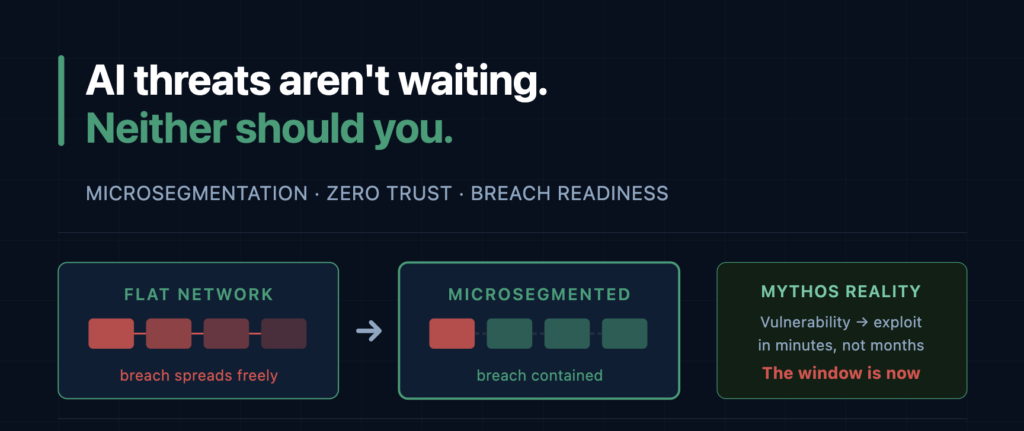
VLANs group devices by subnet. Microsegmentation controls by identity, role, and behavior — at the workload level, at the device level. When an AI model chains vulnerabilities and moves laterally, it doesn’t care about your subnet boundaries. It cares about what can talk to what. A compromised endpoint and a healthy one sitting on the same VLAN? That’s not containment. That’s a buffet. Ask your team: do we enforce policy based on what a device is — or just where it sits? The answer tells you everything.
2. Your unpatchable devices are the weakest link. Contain them now.
There are billions of deployed IoT sensors, OT systems, and legacy devices that will never receive another security patch. Mythos didn’t create this problem — it made it urgent. I’ve seen hospitals where an infusion pump and a workstation share the same flat network segment. No isolation, no enforcement, no visibility. When you can’t fix a device, segmentation is the only answer. If you’re running legacy OT or IoT at scale — and almost every enterprise is — micro-perimeters around those assets aren’t optional anymore.
3. More vulnerability findings isn’t the victory you think it is.
Most security teams I talk to are already drowning in scanner output. AI-powered discovery doesn’t solve that — it amplifies it, unless you have the architecture to triage intelligently. A critical CVE in an internet-facing payment microservice with no isolation around it is an emergency. The same CVE behind three layers of enforcement? It’s Tuesday. Segmentation doesn’t just protect you from breaches — it gives you context. And context is what separates teams that respond intelligently from teams that chase their tails.
4. The window to prepare isn’t 6 to 18 months. It’s now.
I keep hearing people say we have time before AI-powered attacks become widespread. I don’t buy it. Every time this industry has said “we have time,” we didn’t. The threat moves faster than the planning cycle — every single time. Adversaries don’t need Anthropic’s model. They’re already working with what’s available today, and what’s available today is more than enough to cause serious damage to an unprepared enterprise. Mythos was the public announcement. The capability is already spreading.
The enterprises that survive this era won’t be the ones with the best incident response plan. They’ll be the ones that were breach-ready before the breach happened.
Microsegmentation. Least-privilege enforcement. Identity-aware policy at every workload. This is the architecture that contains damage when the perimeter fails. And the perimeter will fail. The only question is what’s waiting on the other side when it does.
Stop treating this like a future problem. Your flat network, your unpatched devices, your over-privileged service accounts — those are live vulnerabilities right now. Start there.
Contact us to see how ColorTokens can help you build breach-ready microsegmentation for the AI threat era.
The post AI Threats Aren’t Waiting appeared first on ColorTokens.
*** This is a Security Bloggers Network syndicated blog from ColorTokens authored by Rajesh Khazanchi. Read the original post at: https://colortokens.com/blogs/microsegmentation-ai-threats-flat-networks-anthropic-mythos/