
Apple account change notifications are being abused to send fake iPhone purchase phishing s 2026-4-19 16:16:42 Author: www.bleepingcomputer.com(查看原文) 阅读量:20 收藏

Apple account change notifications are being abused to send fake iPhone purchase phishing scams within legitimate emails sent from Apple's servers, increasing legitimacy and potentially allowing them to bypass spam filters.
A reader shared an email with BleepingComputer that appeared to be a standard Apple security notification that stated their account information had been updated.
However, embedded within the message was a phishing lure claiming that an $899 iPhone purchase had been made via PayPal, along with a phone number to call to cancel the transaction.
"Dear User 899 USD iPhone Purchase Via Pay-Pal To Cancel 18023530761," reads the Apple account phishing email.
"The following changes to your Apple Account, [email protected], were made on April 14, 2026 at 7:01:40 PM GMT:"
"Shipping Information"
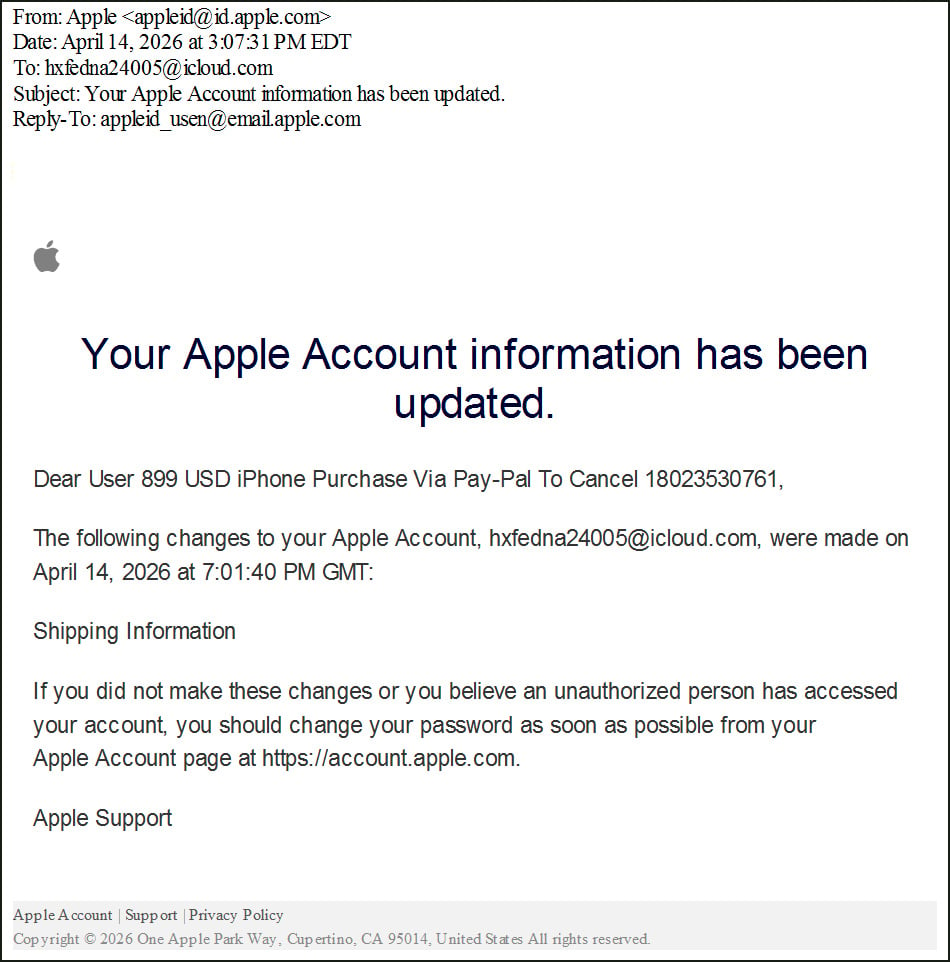
Source: BleepingComputer
These emails are designed to trick recipients into thinking their accounts were used for fraudulent purchases and scare them into calling the scammer's "support" number.
When calling the number, scammers typically try to convince victims that their accounts have been compromised and may instruct them to install remote access software or provide financial information.
In previous callback phishing campaigns, this remote access has been used to steal funds from bank accounts, deploy malware, or steal data.
Abusing Apple account notifications
While the phishing lure is not new, the campaign illustrates how threat actors continue to evolve their tactics by exploiting legitimate website features to conduct attacks.
The phishing email was sent from Apple's infrastructure using the address [email protected] and passed SPF, DKIM, and DMARC authentication checks, indicating it was a legitimate email from Apple.
dkim=pass header.d=id.apple.com [email protected] header.b=o3ICBLWN
spf=pass (spf.icloud.com: domain of [email protected] designates 17.111.110.47 as permitted sender) [email protected]
Further analysis of the email headers shows that the message originated from Apple mail infrastructure and was not spoofed.
Initial server: rn2-txn-msbadger01107.apple.com
Outbound relay: outbound.mr.icloud.com
IP address: 17.111.110.47 (Apple-owned)To conduct the attack, the threat actor creates an Apple ID and inserts the phishing message into the account's personal information fields, splitting the text across the first and last name fields.
BleepingComputer was able to replicate this behavior by creating a test Apple account and adding similar callback phishing language to the first and last name fields. This is because each field cannot contain the entire scam message.
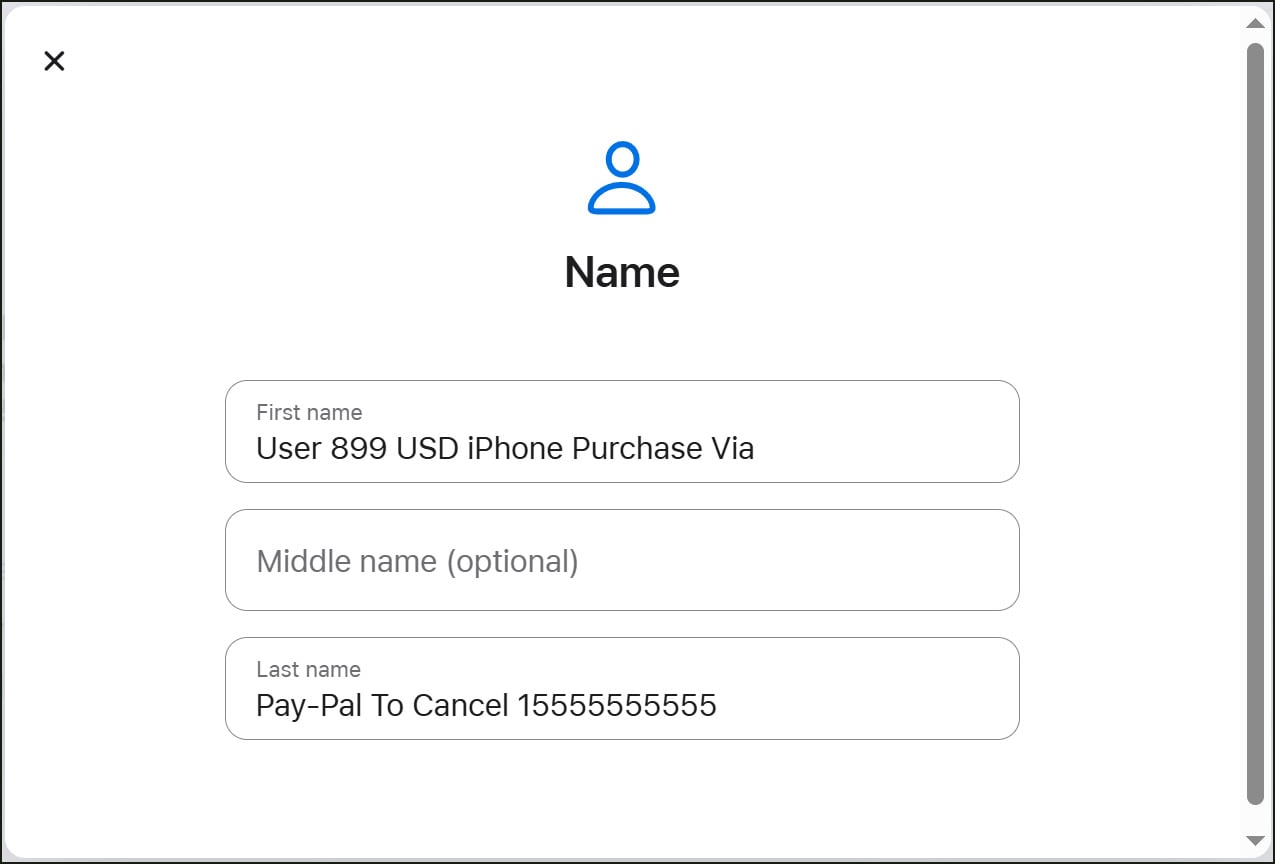
Source: BleepingComputer
To trigger the Apple account profile change notification, the attacker modifies the account's shipping information, which causes Apple to send a security alert notifying the user of the change.
Because Apple includes the user-supplied first and last name fields within these notifications, the phishing message is embedded directly into the email and delivered as part of a legitimate alert.
While the target of the attacks received the message, the email was initially sent to an iCloud email address associated with the attacker's account. This email address is also included in the notification email, making the email look more concerning and potentially leading someone to believe the account was hacked.
Header analysis shows that the original recipient differs from the final delivery address, indicating that the attacker is likely using a mailing list to distribute the emails to multiple targets.
This campaign is similar to a previous phishing campaign that abused iCloud Calendar invites to send fake purchase notifications through Apple's servers.
As a general rule, users should treat unexpected account alerts claiming purchases or urging them to call support numbers with caution, especially if they did not initiate any recent changes or if they contain unusual email addresses.
BleepingComputer contacted Apple on Friday about this campaign, but did not receive a response, and the abuse is still possible.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.
如有侵权请联系:admin#unsafe.sh

