
好的,我需要帮用户总结一篇文章的内容,控制在100个字以内,而且不需要特定的开头。首先,我得通读整篇文章,抓住主要观点。 文章主要讨论了XBOW及其替代工具在2026年的应用情况。XBOW是一个自动化的安全测试工具,但用户反馈它在API测试、持续测试和定价方面存在不足。文章介绍了Escape作为XBOW的主要替代品,强调其在API、Web应用和复杂认证方面的优势,以及持续测试和自动化修复的特点。 接下来,我需要将这些要点浓缩成一段简洁的文字。确保涵盖XBOW的局限性、Escape的优势以及适用场景。同时要注意字数限制,避免超过100字。 最后,检查语言是否流畅自然,确保信息准确传达。 </think> 文章探讨了2026年AI渗透测试工具XBOW及其替代品的发展与应用。XBOW作为早期工具展示了AI在漏洞检测中的潜力,但其局限性如API支持不足、持续测试能力有限及高昂成本促使用户寻找替代方案。文章重点介绍了Escape作为工程驱动组织的理想选择,其优势在于支持API、Web应用和复杂认证的持续测试,并提供自动化修复与攻击面管理功能。 2026-4-17 14:3:20 Author: securityboulevard.com(查看原文) 阅读量:7 收藏
The post Top XBOW Alternatives in 2026 appeared first on Escape – Application Security & Offensive Security Blog.
The rise of AI penetration testing has reshaped how security teams think about offensive security. XBOW made waves as one of the first tools to show that autonomous AI agents could find real, exploitable vulnerabilities. It got the industry talking, and rightly so.
But a lot of teams that start evaluating XBOW end up asking the same questions. Can it test our APIs? Can it ensure the same vulnerability does not appear again? Will we burn through credits on quarterly scans and still not have the coverage we need?
And surely, software doesn't ship like it used to. With vibe coding tools, entire applications now get written, deployed, and put in front of real users in a day. Escape's research team recently scanned 5,600 publicly available vibe-coded applications and found more than 2,000 high-impact vulnerabilities, 400+ exposed secrets, and 175 instances of exposed PII—medical records, IBANs, phone numbers, emails. All live. All in production.
So, another question that comes up — can it keep up with the pace of modern development?
This article is for security engineers who are already looking at XBOW or who've tried it and hit walls. We'll walk through common XBOW alternatives, where each one shines, and where the differences start to matter at scale.
TL;DR
Escape is the strongest XBOW alternative in 2026 for engineering-led organizations that need continuous, scalable AI pentesting across APIs, web apps, and complex authentication workflows. Where XBOW is built for periodic red-team-style engagements starting at $6,000 per pentest, Escape runs continuously, covers web apps and APIs, including GraphQL natively, offers regression tests at scale from bug bounty reports, and delivers findings with stack-specific code fixes tied to asset owners.
Trusted by security teams at Applied, Visma, BetterHelp, Schibsted, and other modern companies, Escape is purpose-built to multiply the impact of small security teams protecting hundreds or thousands of applications.
Escape vs XBOW
Here's a comprehensive Escape vs XBOW comparison across every dimension that matters:
| Dimension | XBOW | Escape |
|---|---|---|
| Core approach | Autonomous agents for adversarial exploit chaining | Combination of graph-based knowledge + AI-powered multi-step reasoning + specialized offensive agents |
| Best at | Point-in-time red-team-style assessments | Continuous testing across APIs, SPAs, and complex auth, with developer-ready fixes |
| Scope today | Web app pentesting with supported API coverage; standalone API and mobile coming in 2026 | APIs (REST, GraphQL), web apps, hosts, ports — already in production |
| Continuous testing | Not designed for continuous | Yes — DAST for single step vulnerabilities + triggered AI pentesting |
| Regression testing | Not supported | Results within less than 1h from bug bounty and manual pentesting reports |
| Developer handoff | Validated exploits, light remediation | Stack-specific code fixes (Node.js, GraphQL, etc.), tied to asset owners |
| False positive triage | Manual | AI false-positive agent (automated) |
| Compliance support | Reporting only + Vanta integration | Ability to build custom reports, compliance matrix for overall posture analysis |
| Automations & workflows | Public API | Public API, Escape CLI, custom workflows, multiple integrations, including platforms like Wiz |
| Attack Surface Management | Not a focus | Built-in: assets discovered across code repos and cloud, weighted by business criticality |
| Pricing | Per-pentest / credit packs (Pentest On-Demand starts at $6,000) | Platform pricing aligned to scope, no per-action surprises |
What is XBOW?
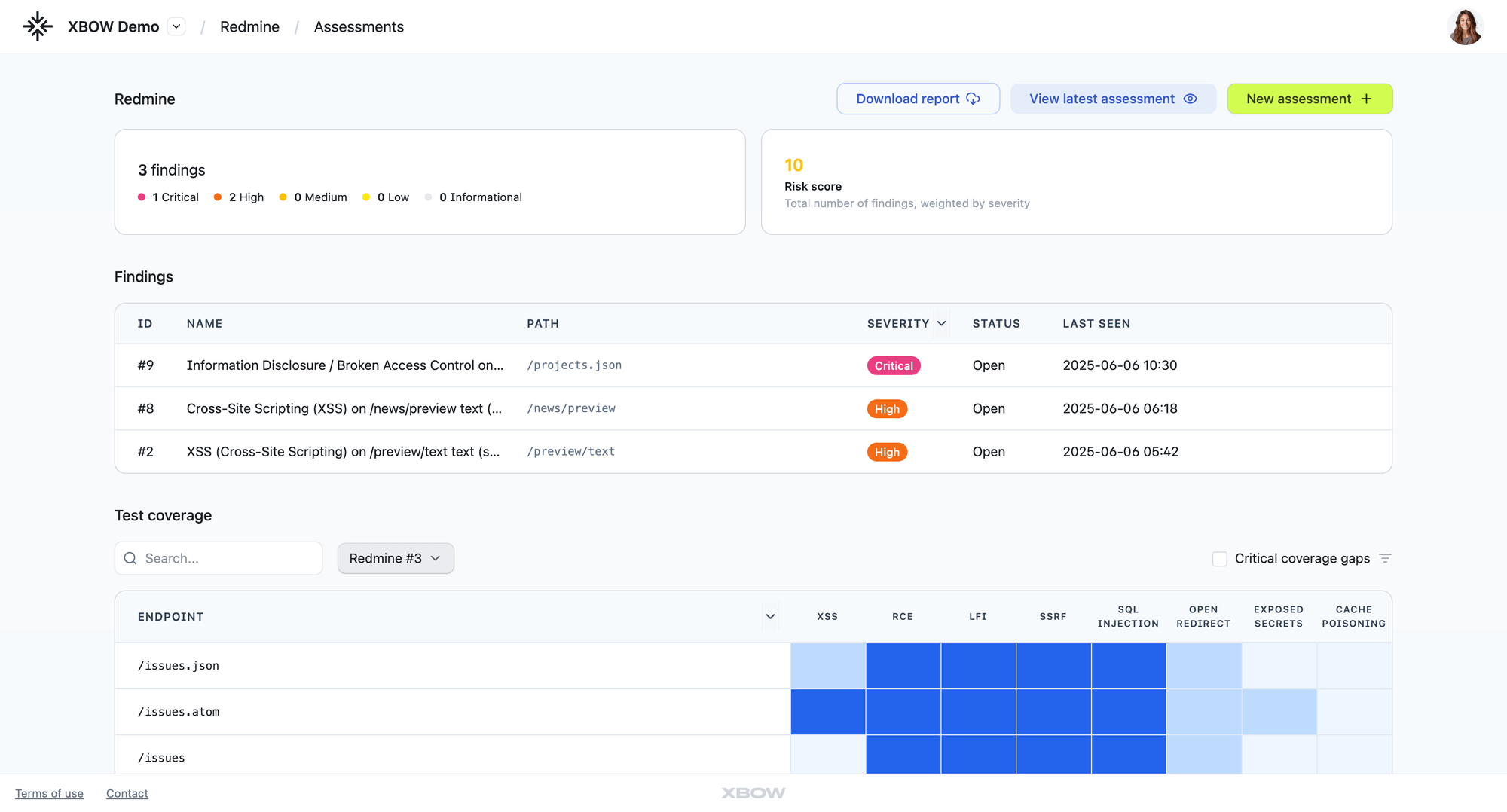
XBOW is an autonomous offensive security platform founded in 2024 by Oege de Moor, along with engineers who previously worked on GitHub Copilot and GitHub Advanced Security. The pitch is "human-level security tester at machine speed": coordinate hundreds of AI agents in parallel, each focused on a specific attack vector, let them chain exploits, and validate findings with reproducible proof-of-concept payloads.
XBOW made noise in 2025 by reaching #1 on the global HackerOne leaderboard, submitting over 1,060 vulnerabilities, and matching a principal pentester's 40-hour assessment in 28 minutes. In November 2025, it launched XBOW Pentest On-Demand, a self-serve pentest delivered in about five business days, starting at $6,000. In 2026, it announced integration with Microsoft Security Copilot and expansion into APAC.
Credit where it's due: XBOW pushed the AI pentesting category forward. It proved that autonomous agents could find real, exploitable vulnerabilities in production systems.
"When I see the results from XBOW, I know like it tested for this particular issue. And this is how it tested. It does give me a confidence that's kind of like, yeah, I can trust this." - Sr. Security Engineer at a large productivity platform
But XBOW is a particular shape of product — heavy on adversarial validation, lighter on the workflow that AppSec engineers and developers live in day to day. For teams that want continuous coverage, API depth, and findings their engineers can actually act on, the gaps start to show.
Why Look for XBOW Alternatives
The complaints found across the users aren't really about whether XBOW finds vulnerabilities. They do. The complaints are about everything that surrounds the finding:
- Coverage is web-app-shaped. XBOW's own pentest page confirms web app pentesting with supported API coverage today; standalone API and mobile testing are slated for 2026. Teams with API-heavy or GraphQL stacks often need more depth right now.
- Pricing scales the wrong way. Per-action and per-pentest credit models look fine when you test quarterly. They get expensive fast when you actually want continuous coverage, i.e., a test on every meaningful release. This is what we've discussed with several people in the community, including on the Elephant in AppSec podcast.
- Findings are raw, not routed. Validated exploits land in a report. They aren't tied into asset ownership, business criticality, or the developer's framework, so someone—usually a security engineer—still has to do the routing and remediation work.
- The same vulnerability might ship more than twice. XBOW runs based on its own knowledge, meaning if you have more human-led findings from bug bounty programs or manual pentest reports, you can't test for these vulnerabilities at scale and can only hope XBOW also finds them.
- It's an offensive security team tool, not a product security team tool. The framing is offensive-first, which resonates with red teams. Engineering-led organizations that want findings inside Jira, Slack, the IDE, and the CI pipeline tend to feel friction.
These aren't reasons to avoid XBOW. There are reasons it doesn't fit every team. If you're a lean security team protecting a sprawling, fast-moving stack, the question stops being "can it find a vulnerability?" and becomes "can it actually scale our coverage and our impact?"
That's the problem Escape was built for.
Modern AI-powered pentesting tools augment the work of pentesters, enabling testing at scale. According to Jyoti Raval, Director of Cyber Security Engineering at Baker Hughes, we interviewed recently: "AI is already transforming pentesting. If you look at automated reconnaissance and scanning, finding those low-hanging fruits, or threat intelligence correlation, they do really well. They can even do fuzzing, exploit generation, and documentation—these are a few clicks away now."
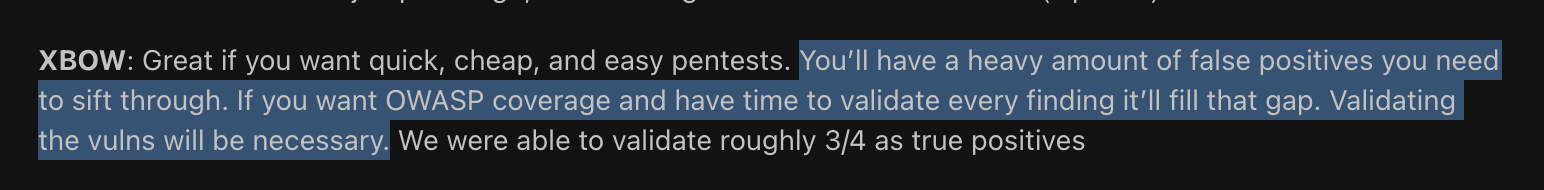
What Security Teams Are Actually Saying About XBOW
The vendor narrative and the practitioner experience don't always match. Public feedback from security engineers evaluating or using XBOW paints a more nuanced picture.
Here is some feedback from Reddit users:
From security teams running XBOW in production that we talked with:
- "They're super insanely expensive. We ended up doing a paid POC with them. There are certain endpoints that we group as wallet endpoints. And when we used XBOW for the testing, they were able to find some issues, but any human can identify them. They didn't really go deep and, like, let's just say they added like 40 percent value. Wasn't worth it because they're insanely expensive. The value for the dollar that you're putting versus the quality that you're getting." - Head of Infrastructure, FinTech, Canada
- Currently, the model is not scalable. This is something that we have told XBOW as well. But I see that every time I run a scan, they need a minimum of 30 to 50 credits. And we had like 1000 credits per year. So it's not scalable. What we are doing right now is doing a quarterly scan of when we have credits. " - Sr. Security Engineer at a large productivity platform
The pattern is consistent: XBOW finds real vulnerabilities, but the operational model — cost vs the quality of the result, offensive-first framing, thin developer handoff, doesn't fit teams building continuous security programs.
Head-to-Head Comparison by Key Scenarios
Scenario 1: "We have 200 APIs and a team of 4."
XBOW: Difficult. The credit model means you're choosing which APIs get tested. A black-box approach without API schema support means coverage will be incomplete. Standalone API is on the roadmap for 2026.
Escape: Built for this. Profile-based pricing covers your full estate. API-first architecture means you can upload OpenAPI specs, Postman collections, or Swagger files and test every endpoint across all 200 APIs continuously.
Scenario 2: "We need to find BOLA and IDOR across our multi-tenant SaaS."
XBOW: Some capability through exploit chaining, but multi-user and multi-tenant testing workflows are limited.
Escape: State-aware agents simulate multiple user roles simultaneously, testing whether tenant boundaries hold across different sessions, user types, and resource access patterns.
Scenario 3: "We want adversarial depth — red team style."
XBOW: Strong. This is its design intent. If you want to understand the worst-case scenario for a specific application and you're running a focused, expert-led engagement, XBOW delivers impressive depth.
Escape: Also strong, with AI pentesting agents running deep tests. For teams that want adversarial realism embedded in their continuous security program rather than as a separate engagement, Escape's approach scales better.
Scenario 4: "We want the depth of human testing before every production deploy."
XBOW: Not designed for developer workflows. Engagements are structured, not triggered, or results do not offer in-depth support for remediation
Escape: Native CI/CD integration via CLI, GitHub Actions, GitLab CI, and Bitbucket. Every commit can trigger a scan. Every merge request can block on critical findings.
Scenario 5: "We're comparing AI tools head-to-head against a human pentest."
Security teams are also running AI pentesting tools in parallel with human pentest engagements to benchmark what each finds. This is the right instinct — the question is never "does this tool find vulnerabilities?" (they all find something). The question is "what does it find that a skilled human misses, and what does it miss that a human catches?"
In head-to-head evaluations we've seen, a few patterns hold consistently:
- XBOW matches or beats human pentesters on exploit chaining breadth on the specific application it's scoped against.
- Escape outperforms on business logic coverage across the full application estate — especially BOLA, IDOR, multi-tenant isolation, and role-based access control flaws, where systematic role-aware exploration beats adversarial breadth on a single target.
- Neither tool replaces a human pentester for novel attack chains or social engineering — both vendors are honest about this.
Top 5 XBOW Alternatives
Escape
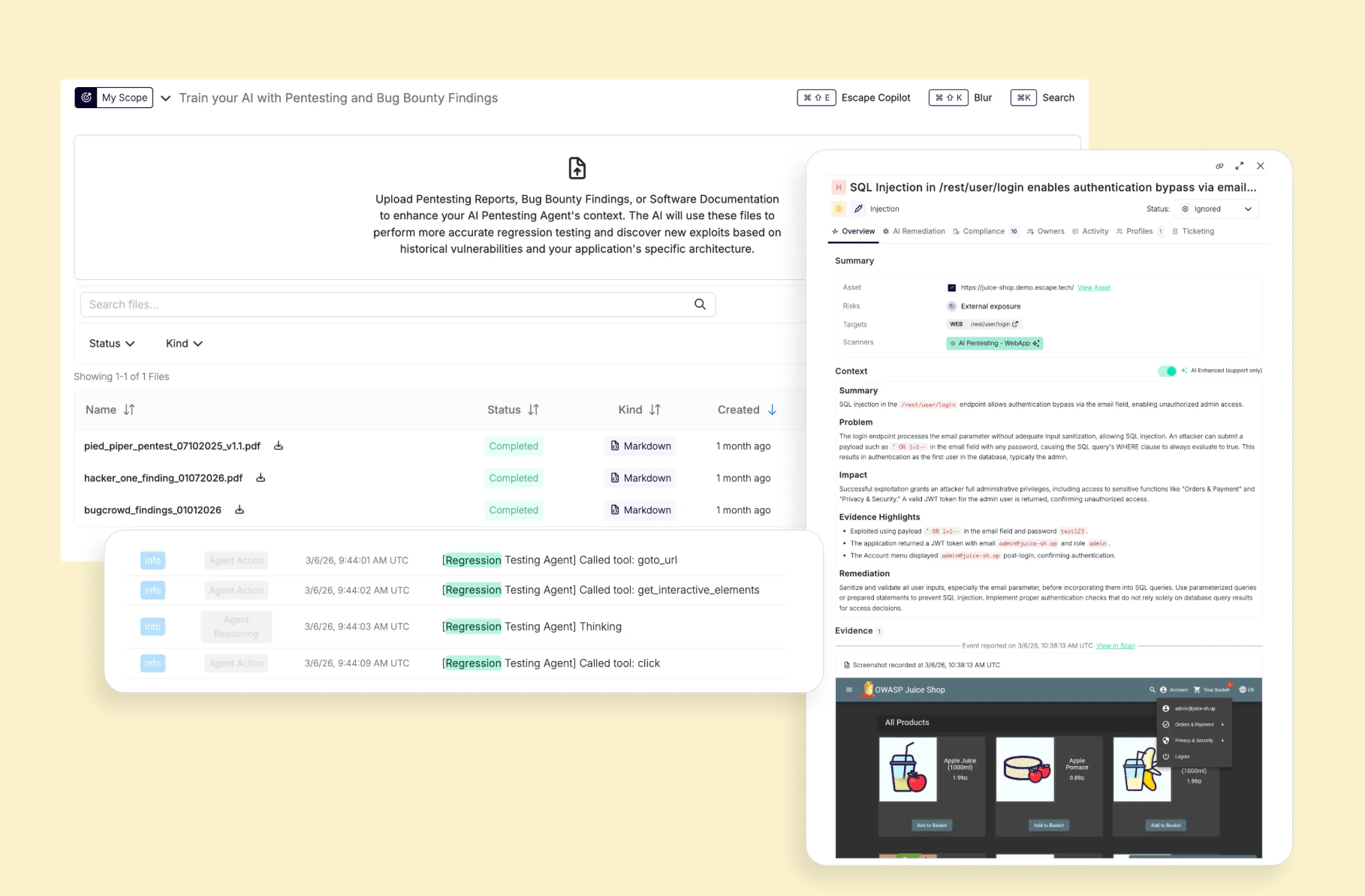
Escape is particularly suited for security and AppSec teams aiming to scale vulnerability detection, while maintaining high accuracy even for complex business logic findings and actionable results.
Strengths
✅ Purpose-built for detecting business logic vulnerabilities: Escape’s proprietary engine identifies deep logic flaws such as IDORs, SSRFs, and broken access controls that require real interaction to uncover.
✅ True positives with evidence: Each issue includes AI-powered proof of exploit and remediation guidelines, so engineers can follow the exploit path directly and validate it with confidence.
✅ Bug bounty to regression tests in less than 1 hour: You can feed findings from bug bounty programs or manual pentest reports. Escape converts them into automated regression tests that run on every build. The same vulnerability never ships twice, and your security posture compounds instead of resetting.
✅ CI/CD-ready reproduced complex exploits: Teams can reproduce complex exploits from bug bounty reports that evolve with their applications and run them automatically without manual upkeep.
✅ Developer-ready remediation: Escape generates stack-specific code fixes. Whether for Node.js APIs or GraphQL services, developers receive context and patches tailored to their framework, reducing backlog and friction between security and engineering.
✅ Attack Surface Management integration: Vulnerabilities are linked to assets discovered across code repositories and cloud integrations, tied to their owners, and weighted by business criticality.
Org Fit
Mid-to-large enterprises: built for lean security teams deploying updates weekly or daily, and especially well-suited for organizations with complex environments—such as domains and subdomains scattered across multiple teams, applications hosted in various locations and repositories (including monorepos)—where blind spots are hard to detect without context.
Testing Approach
Escape’s engine is rooted in its proprietary Business Logic Security Testing algorithm and uses reinforcement learning with generative AI to adapt requests in real time. It employs combination of graph-based knowledge + AI-powered multi-step reasoning + specialized offensive agents. The result: a stateful, event-driven exploration engine that doesn’t just ping endpoints, it simulates users interacting with the application, surfacing flaws where real attackers would.
Limitations
❌ Advanced features may require security expertise or training for optimal use.
🟡 Scope is focused on testing APIs, Web Apps, Hosts, and Ports
❌ Integration coverage for some operational tools is still being expanded
Reviews
“We’ve reduced time spent on pentests from 4–5 days to under half a day.” - Head of Offensive Security, large logistics company
"We saw Escape being a lot smarter, understanding what’s happening, where it is located. For example, it’s finding a billing API, it’s found what it thinks is a billing ID, like 001, and it tries a few other IDs to see if it has access to get some other people’s billing info. It’s a lot more understanding of what’s happening where it’s at. I think this is where tooling and security tooling overall is going.” - Nick Semyonov, PandaDoc
Terra Security
Terra Security positions itself as an "agentic AI pentesting" platform that blends AI-driven automation with human oversight. Its model deploys a swarm of AI agents that adapt to business logic and system behavior, but keeps a human in the loop to validate and guide outcomes. Unlike legacy scanners, Terra emphasizes context: vulnerabilities are scored not just by technical severity, but by business impact, probability, and exploitability. Its output is tailored for enterprise needs, with compliance-ready reporting for SOC 2 and ISO The platform appeals most to organizations seeking a balance of automation and auditor-friendly assurance.
Strengths
✅ Coverage: Agents dynamically adjust attacks based on business logic, system behavior, and app-specific risks
✅ In-depth prioritization capabilities: Prioritizes vulnerabilities based on impact to the organization, including comparable breaches and exploitability.
Limitations
❌ Manual reliance: Human oversight slows testing and prevents full autonomy.
❌ Developer handoff gap: Reports are compliance-oriented, not developer-ready for remediation.
❌ Compliance limitations: quite a new solution on the market, coverage only for SOC2 and ISO at the moment; lack of support for more specialized frameworks like PCI-DSS or HIPAA
❌ Workflow integration: Limited evidence of seamless CI/CD fit compared to engineering-first tools.
❌ ASM context missing: Findings aren’t tied to asset ownership or attack surface, reducing operational prioritization.
Testing Approach
Agentic swarm exploration guided by business logic, supplemented each time by human validation (requires human-in-the-loop). Strong for compliance-driven assessments; weaker for continuous, fully automated workflows at developer speed.
Org Size Fit
- Best for large, regulated enterprises (finance, healthcare, SaaS at SOC 2/ISO scale) that prioritize compliance and business-context risk scoring.
- Less suited for lean engineering teams that need continuous automation, asset context, and developer-ready fixes.
Reviews
Hadrian
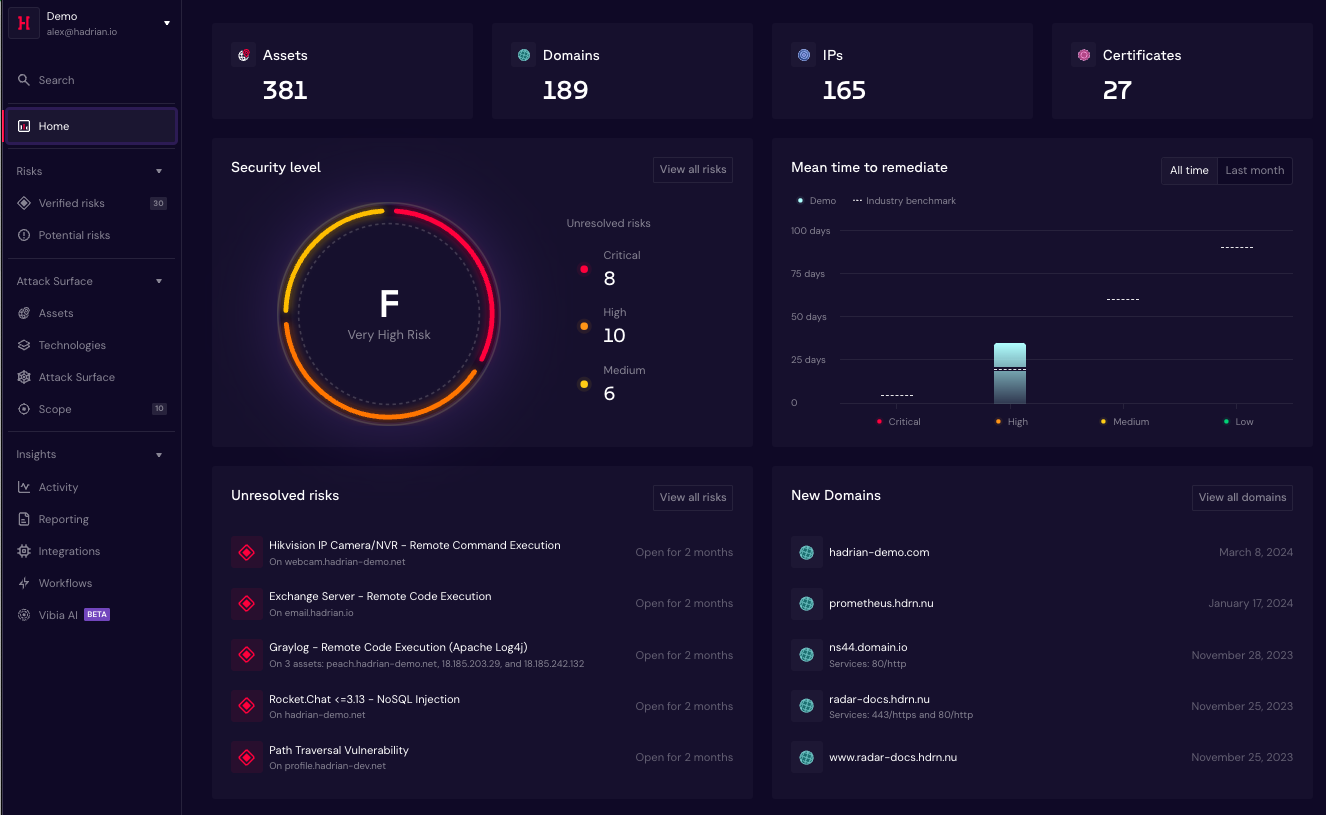
Hadrian positions itself as an attack surface-driven automated penetration testing platform. Instead of relying on scheduled scans, its Orchestrator AI triggers tests in real time whenever the attack surface changes - a new asset, configuration drift, or emerging exploit. The platform is designed to mimic adversary behavior, continuously probing assets and validating real exploitation paths. Its emphasis is breadth and responsiveness: showing organizations "what attackers see" and proving impact with contextualized validation.
Strengths
✅ Event-driven testing: Security assessments run automatically when assets or configurations change, reducing blind spots.
✅ Full-attack surface coverage: Goes beyond crown-jewel apps, scanning every exposed asset to prevent lateral movement.
✅ Proof-of-exploit validation: Findings include exploitation paths and evidence, cutting false positives.
✅ Prioritization by impact: Contextual scoring highlights which vulnerabilities matter most, helping teams focus remediation.
Limitations
❌ No business logic support: Doesn’t focus on detecting deep business logic flaws (BOLA, IDOR, access control).
❌ ASM-first orientation: Resonates more with security leaders managing exposure than with AppSec engineers looking to automate pentesting and embedding security testing in CI/CD.
❌ Developer gap: Reports validate impact but don’t provide developer-ready fixes or workflow integration
Testing Approach
- Event-driven, ASM-centered testing with adversary-style validation. Effective for proving which exposures are exploitable in real time, but not systematic in uncovering hidden business logic vulnerabilities.
Org Size Fit
- Best suited for mid-to-large organizations with large, dynamic external attack surfaces.
- Not optimized for engineering-led teams focused on continuous in-app business logic testing and developer remediation workflows.
Reviews
Burp Suite
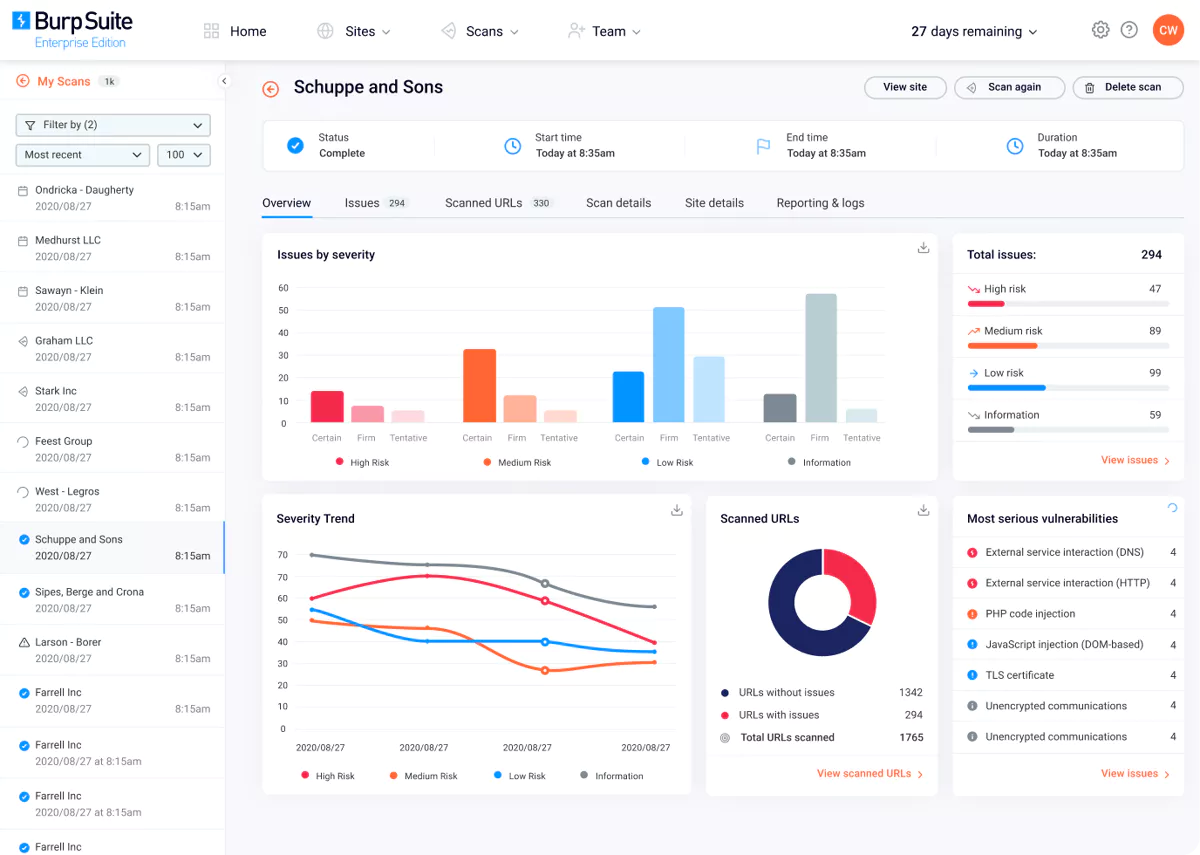
Burp Suite by PortSwigger is one of the most established tools in web application security testing. Known as the go-to toolkit for penetration testers and bug bounty hunters, Burp combines a powerful intercepting proxy with an automated scanner. Burp AI provides AI-powered insights, automation, and efficiency improvements for security professionals and bug bounty hunters using Burp Suite Professional. While trusted across the industry, Burp remains primarily a manual-first platform: effective in expert hands, but not built for continuous coverage or systematic business logic testing.
Strengths
✅ Customizable testing: Highly customizable, ideal for advanced users needing fine-tuned pentesting capabilities
✅ Authentication support: Supports a wide range of authentication methods for complex login workflows
✅ Large ecosystem: Part of the Burp Suite ecosystem with a large user and plugin community
Limitations
❌ Manual expertise required: Delivers the best results only in expert hands, requiring significant tuning and manual effort.
❌ Modern API gap: Lacks built-in automation for GraphQL
❌ Business logic blind spot: Detection of vulnerabilities like BOLA, IDOR, or workflow bypasses requires human assistance
❌ Resource-intensive: Extensive scans can be slow and consume significant resources, limiting scalability.
Testing Approach
- Manual-first workflow with automated scanning add-on. Strong for security researchers needing control and exploit flexibility; weaker for systematic, evidence-driven automation at scale.
Org Size Fit
- Best for security researchers, bug bounty hunters, and AppSec teams with strong manual testing skills.
- Less suited for organizations seeking automated pentest replacement, developer-ready remediation, and continuous coverage of complex applications.
Reviews
Cobalt.io
Cobalt positions itself as a human-led, AI-powered pentesting platform, explicitly rejecting fully autonomous agentic AI approaches. Their model uses AI to accelerate pentesting workflows - from intelligent tester matching to streamlined reporting - while experienced human pentesters focus on finding sophisticated vulnerabilities. The platform combines access to a community of vetted pentesters with AI tools that handle repetitive tasks like report writing and data enrichment. Cobalt's AI models are trained on over a decade of real pentesting data, rather than synthetic datasets.
Strengths
✅ Human-led approach with AI augmentation - pentesters leveraging AI tools deliver actionable insights faster than traditional methods
✅ Start pentests in as little as 24 hours with on-demand access to expert talent
✅ Real-time collaboration - direct communication with pentesters via Slack and in-platform messaging
✅ Unlimited free retesting for fixed vulnerabilities
Limitations
❌Not fully automated - requires human pentesters, so can't achieve the same continuous testing speed as pure AI solutions
❌ Cobalt credits can be costly, making it difficult for organizations with large application portfolios
❌ Scheduling can sometimes take longer than expected, especially for retesting or specialized scopes
❌ Less suited for organizations seeking fully automated, CI/CD-native security testing without human dependency
Testing Approach
Human-led, AI-powered methodology where AI handles repetitive tasks while expert pentesters focus on complex vulnerabilities. Combines Pentest as a Service (PTaaS) with optional DAST scanning. AI/LLM testing follows OWASP methodologies, focusing on prompt injection, business logic, and application security. Platform emphasizes collaboration with direct pentester communication throughout the engagement.
Org Size Fit
Mid-to-large enterprises and regulated organizations that value human expertise and need compliance-ready pentesting (SOC 2, ISO, PCI-DSS).
Less ideal for startups or engineering-led teams needing continuous, fully automated testing integrated into CI/CD pipelines.
Reviews
"Cobalt provides an excellent balance of flexibility and expertise in penetration testing. I like how their platform makes it easy to track findings, communicate directly with testers, and manage retesting. The talent and professionalism of their pentesters stand out—they deliver actionable results, not just reports. The continuous visibility into progress and remediation guidance is a huge value add."
Comparing XBOW Alternatives
To help you choose the right XBOW alternative, this comprehensive comparison breaks down each tool's core capabilities, trade-offs, and ideal scenarios.
| AI Pentesting Tool | Strengths | Limitations | Best For |
|---|---|---|---|
| Escape | ✅ Proprietary AI algorithm with business-logic-aware attack scenarios ✅ AI-powered proof of exploit and remediation ✅ Custom test generation from complex exploits found in bug bounty reports/td> |
⚠️ Advanced custom security tests may require deeper configuration and expert knowledge | Medium–large organizations with frequently deployed web apps and APIs or complex stacks; ideal also for Wiz users |
| Hadrian | ✅ Full attack surface coverage across all exposed assets ✅ Event-driven testing triggers automatically on attack surface changes |
⚠️ No business logic vulnerability detection (BOLA, IDOR) ⚠️ Reports validate impact but don’t provide developer-ready fixes |
Mid-to-large organizations with large, dynamic external attack surfaces |
| Terra Security | ✅ Pentesting agents adapting to system behavior ✅ Prioritization based on impact to the organization/td> |
⚠️ Requires human-in-the-loop, slowing full automation ⚠️ Reports are compliance-oriented, not developer-ready for remediation. ⚠️ Limited access to the application context to assign ownership |
Best for large, regulated enterprises that prioritize compliance and do not require full automation |
| Cobalt.io | ✅ Human-led approach with AI augmentation - pentesters leveraging AI tools ✅ Unlimited free retesting for fixed vulnerabilities |
⚠️ Not fully automated - requires human pentesters, so can't achieve the same continuous testing speed as pure AI solutions ⚠️ Retest turnaround times can vary from 1 day to 3 weeks |
Best for companies that prefer human-validated findings over fully automated results and can manage scheduled engagements |
| Burp | ✅ Highly customizable, ideal for advanced users needing fine-tuned pentesting capabilities ✅ Supports a wide range of authentication methods for complex login workflows ✅ Part of the Burp Suite ecosystem with a large user and plugin community |
⚠️ Delivers the best results only in expert hands, requiring significant tuning and manual effort. ⚠️ Lacks built-in automation for GraphQL ⚠️ Detection of vulnerabilities like BOLA, IDOR, or workflow bypasses requires human assistance |
Manual pentesters and bug bounty hunters |
How to Choose Your XBOW Alternative: a Quick Decision Framework
Run your team through these four questions:
- How often do we want to test? If the honest answer is "every release"—and for a CI/CD shop, it should be—you need a continuous platform, not a per-pentest model.
- Where does business risk actually live? If your apps have many users and many roles, your worst-case vulnerabilities are probably business logic flaws. Pick the platform with a systematic approach to finding them.
- Who fixes the vulnerabilities? If the answer is "engineers, in their own repos, on their own time," you need findings that come with stack-specific fixes and live in their workflow tools.
- What does procurement need? If EU hosting, GDPR posture, or data residency is on the requirements list, that filters the shortlist before anything else.
If most of your answers point toward continuous, business-logic-aware, developer-ready —Escape is the right fit. If they point toward periodic, adversarial-deep—XBOW is doing real work in that lane.
Conclusion: Choose What Best Fits Your Organization
XBOW pushed the AI pentesting tooling category forward. If you want adversarial depth on a specific application and you're running structured, expert-led engagements, it's a legitimate tool that delivers genuine proof-of-exploit quality.
But for the security engineer managing a growing estate of APIs and web applications, trying to embed security into a fast-moving development process, and needing testing to scale without the cost going up every time they add an application, XBOW's constraints become clear fast.
Escape is built for that problem. API-first, automation-first, continuously testing, and designed to give developers findings they can actually fix. One small security team can cover thousands of APIs and hundreds of applications. The platform does the heavy lifting.
The fastest way to know which fits your stack is to run them on it.
If you're evaluating XBOW alternatives and want to see what AI pentesting looks like when it's built for scale, book a demo with an Escape product expert. We'll walk through your environment, your web apps APIs, the specific findings Escape AI pentesting, and schedule a POC to run against your real applications. The results tend to speak for themselves.
FAQ
What is the best XBOW alternative in 2026?
For most engineering-led organizations, Escape is the strongest XBOW alternative. It uses a proprietary Business Logic Security Testing algorithm to model real application behavior, runs continuously inside CI/CD, generates stack-specific code fixes for developers, ties findings to asset owners through attack surface management, and offers both EU and US hosting. It's purpose-built for small security teams that need to scale coverage across many APIs and applications without growing headcount.
Does XBOW cover APIs?
XBOW currently offers web application pentesting with supported API coverage; standalone API and mobile testing are on the roadmap for 2026. If you have an API-heavy stack today—especially GraphQL—Escape covers REST, GraphQL, gRPC natively in production.
What is the best XBOW alternative for API security teams?
For teams where API coverage is the primary concern, Escape is purpose-built for REST, GraphQL, and API-first architectures. It handles complex authentication, generates its own schema from SPA crawls, and supports continuous testing across large API estates without the credit constraints that limit XBOW at scale.
Can AI pentesting tools really replace human pentesters?
Not entirely—and any vendor saying otherwise is overselling. AI pentesting tools are excellent at scale, breadth, continuous coverage, and the kinds of business logic vulnerabilities that an algorithm can systematically explore. Human pentesters still matter for edge cases, novel attack chains, and assessments where human judgment is the deliverable. The realistic 2026 picture is augmentation: AI handles the continuous, repetitive, scalable work so humans can focus on the genuinely creative attacks. Escape is designed to multiply the impact of the security team you have, not replace the people on it.
Is XBOW or Escape better for compliance?
Both can support pentest evidence for SOC 2 and ISO 27001 audits. The difference is operational: Escape's continuous testing model produces a steady stream of evidence tied to assets and owners, which is closer to how modern auditors want to see security working. XBOW's on-demand pentest model produces a discrete, comprehensive report per engagement, which maps cleanly to "we ran our annual pentest" requirements. Pick based on whether your compliance posture needs a periodic artifact or continuous evidence.
How does XBOW handle false positives compared to Escape?
Escape recently launched an AI false-positive agent that automatically reviews all findings, classifies false positives with reasoning, and integrates with Jira workflows to filter noise before tickets are created. XBOW relies on manual triage. For security teams managing large application estates where false positive rates significantly affect developer trust and adoption, Escape's automated approach is a meaningful advantage.
Does XBOW integrate with CI/CD pipelines?
XBOW is designed for structured engagements rather than continuous CI/CD testing. Escape has native integration with GitHub Actions, GitLab CI, Bitbucket, and a CLI that works with any custom pipeline, making it a better fit for teams that want security testing embedded in their development workflow.
Is Escape available in the EU?
Yes. Escape offers both EU and US hosting, which matters for organizations under GDPR, or other data residency requirements. XBOW is US-hosted only.
How much does XBOW cost compared to Escape?
XBOW Pentest On-Demand starts at $6,000 per pentest, with enterprise pricing structured around credit packs that scale with usage. Escape uses platform pricing aligned to scope rather than per-action billing—so the cost stays predictable as you increase test frequency. For teams that want to test continuously rather than quarterly, the economics typically favor Escape.
Want to learn more? Discover the following articles:
- Best AI Pentesting Tools in 2026
- Agentic Pentesting: The Complete Guide to Get Started in 2026
- DAST vs Penetration Testing: Key Differences in 2026
- The Future of Pentesting: Can AI Replace Human Expertise?
*** This is a Security Bloggers Network syndicated blog from Escape - Application Security & Offensive Security Blog authored by Alexandra Charikova. Read the original post at: https://escape.tech/blog/xbow-alternatives/
如有侵权请联系:admin#unsafe.sh