
嗯,用户让我帮忙总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读这篇文章,理解它的主要观点。 文章讨论了传统网络安全工具的问题。过去,组织通过增加工具来加强防御,比如防火墙、端点解决方案等。但尽管投入增加,安全效果并没有显著提升。问题出在这些工具之间缺乏协同,导致可见性碎片化、警报疲劳、反应迟缓等问题。 然后,文章提出了统一的人工智能平台作为解决方案。这种平台整合多种安全能力,提供整体视图,通过行为分析和自动化响应来提升安全性。Seceon公司的产品就是一个例子。 所以,总结的时候需要涵盖传统工具的缺陷和AI平台的优势。控制在100字以内,直接描述内容。 可能的结构是:传统工具的问题→统一AI平台的解决方案→Seceon的作用。 现在开始组织语言:传统网络安全工具因缺乏协同导致问题增多;统一AI平台整合能力,提供整体视图和智能自动化;Seceon帮助组织实现更主动的安全策略。 检查字数是否合适,并确保直接描述内容。 </think> 传统网络安全工具因缺乏协同与整合而难以应对复杂威胁;统一AI平台通过整合多源数据、智能分析与自动化响应提升安全性;Seceon等解决方案助力企业实现更高效、主动的安全防护。 2026-4-17 11:13:24 Author: securityboulevard.com(查看原文) 阅读量:4 收藏
When More Tools Create More Problems
For years, organizations have approached cybersecurity with a simple mindset-add more tools to strengthen defenses. Firewalls, endpoint solutions, intrusion detection systems, and monitoring platforms have all been layered together to create what appears to be a comprehensive security posture.
Yet, despite this growing investment, security outcomes have not improved at the same pace. Breaches continue to occur, response times remain slow, and security teams often struggle to keep up with the volume of alerts and data.
The issue is not a lack of tools. It is the lack of cohesion between them.
Traditional security architectures were not designed for today’s interconnected, fast-moving environments. As a result, they often introduce complexity instead of clarity-making it harder, not easier, to detect and respond to threats.
The Structural Weakness of Traditional Security Models
Fragmentation That Breaks Visibility
Most security environments evolve over time, with new tools added to address specific challenges. While each tool may perform its role effectively, they rarely operate as part of a unified system.
This fragmentation creates gaps in visibility. Security data is distributed across multiple platforms, making it difficult to understand what is happening across the environment at any given moment. Analysts are forced to manually correlate events, which slows investigations and increases the risk of missing critical signals.
In complex attack scenarios, where multiple actions occur across endpoints, networks, and cloud systems, this lack of unified visibility becomes a serious limitation.
Alert Fatigue: When Everything Feels Important
Security tools are designed to detect suspicious activity-but they often generate far more alerts than teams can realistically handle. Over time, this leads to alert fatigue, where analysts become overwhelmed by the sheer volume of notifications.
Not all alerts are equal. Many are false positives or low-risk events, yet they still require attention. As a result, valuable time is spent filtering noise instead of responding to real threats.
This imbalance creates a dangerous situation: critical alerts may be delayed or even ignored, giving attackers the opportunity to move undetected.
A Reactive Approach in a Proactive Threat Landscape
Traditional systems rely heavily on signatures and predefined rules. While this approach works for known threats, it struggles against modern attack techniques that are designed to evade detection.
Today’s attackers are not static-they continuously adapt their methods. This includes using fileless malware, exploiting zero-day vulnerabilities, and blending malicious activity with normal behavior.
Because traditional tools depend on what is already known, they often detect threats only after damage has begun. This reactive model is no longer sufficient in a landscape where speed and stealth define successful attacks.
Lack of Context Limits Effective Response
An isolated alert rarely tells the full story. A login anomaly, for example, may seem harmless on its own-but when combined with unusual network activity and data access patterns, it could indicate a larger breach.
Traditional tools often fail to provide this level of context because they operate independently. Without a connected view, security teams must piece together information manually, which delays response and increases uncertainty.
Effective security requires understanding not just individual events, but how they relate to each other across the entire environment.
Complexity That Slows Down Security Operations
Managing multiple tools introduces operational challenges that go beyond detection. Each system requires configuration, maintenance, and expertise. Integrating them into a cohesive workflow is often time-consuming and resource-intensive.
This complexity impacts:
- Speed of investigation and response
- Efficiency of security teams
- Overall cost of operations
Instead of enabling agility, traditional architectures often create friction, making it harder to scale security as the organization grows.
Why Modern Threats Exploit These Gaps
The nature of cyber threats has changed significantly. Attackers now operate with a level of coordination and persistence that traditional defenses were never designed to handle.
Modern attacks are rarely isolated events. They unfold as a sequence of actions-initial access, lateral movement, privilege escalation, and data exfiltration. Each step may appear insignificant on its own but becomes dangerous when viewed as part of a larger pattern.
This is precisely where traditional tools fall short. Without integration and real-time correlation, they struggle to detect these multi-stage attack chains.
Unified AI Platforms: A Shift Toward Intelligent Security
To address these limitations, organizations are moving toward unified AI-driven security platforms. These platforms are designed to bring together multiple security capabilities into a single, integrated system.
Rather than treating security as a collection of separate tools, this approach treats it as a connected ecosystem-one that can analyze data holistically, adapt to new threats, and respond in real time.
The key difference lies in intelligence and integration. Unified platforms do not just collect data-they understand it.
How Unified AI Platforms Change the Game
Connected Visibility Across the Entire Environment
Unified platforms aggregate and normalize data from across endpoints, networks, cloud environments, and user activity. This creates a single, coherent view of the organization’s security posture.
With everything in one place, security teams can quickly identify patterns, trace attack paths, and understand the full scope of an incident without switching between tools.
Smarter Detection Through Behavioral Intelligence
Instead of relying solely on predefined rules, AI-driven platforms analyze behavior. They establish a baseline of normal activity and detect deviations that may indicate a threat.
This approach is particularly effective against:
- Unknown or emerging threats
- Insider risks
- Subtle anomalies that traditional tools overlook
By focusing on behavior rather than signatures, organizations gain a more adaptive and resilient defense.
Context-Driven Insights That Improve Decision-Making
One of the most powerful advantages of unified platforms is their ability to correlate data across multiple sources. This provides a deeper level of context for every alert.
For example, a single incident can include:
- User activity patterns
- Endpoint behavior
- Network interactions
- Historical data
This enriched context allows security teams to assess risk more accurately and respond with confidence.
Automation That Reduces Response Time
Speed is critical in cybersecurity. The longer a threat remains active, the greater the potential impact.
Unified platforms incorporate automation to handle routine and time-sensitive tasks. These may include isolating compromised systems, blocking malicious activity, or initiating response workflows.
By reducing manual intervention, automation ensures faster and more consistent responses.
Simplified Operations Without Losing Depth
One of the most overlooked benefits of unification is simplification. Instead of managing multiple disconnected tools, teams operate within a single platform that streamlines workflows and reduces redundancy.
This not only improves efficiency but also allows security teams to focus on higher-value activities such as threat analysis and strategy.
How Seceon Helps Address These Challenges
Modern organizations need more than just tools-they need a cohesive, intelligent security framework. This is where Seceon’s approach aligns with the needs of today’s security landscape.
Seceon enables organizations to overcome the limitations of traditional security by delivering a unified, AI-driven platform that focuses on visibility, intelligence, and automation.
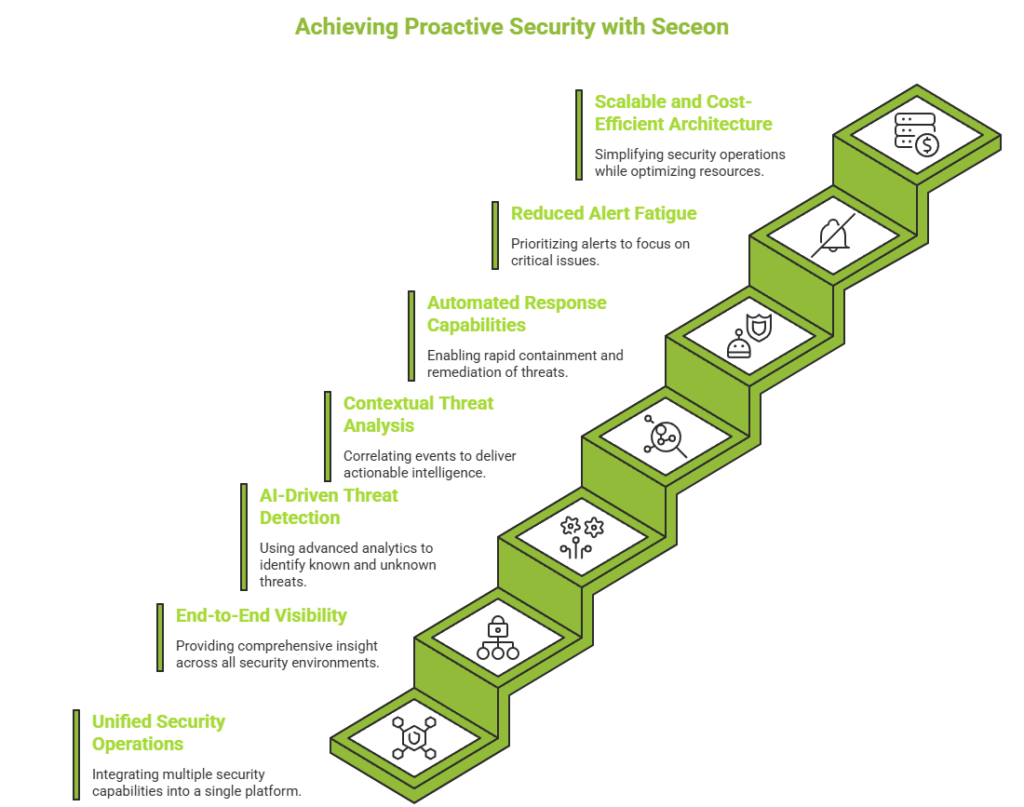
Key ways Seceon helps:
- Unified Security Operations
Brings together multiple security capabilities into a single platform, reducing tool sprawl and simplifying operations. - End-to-End Visibility
Provides comprehensive insight across endpoints, networks, cloud environments, and user activity-eliminating blind spots. - AI-Driven Threat Detection
Uses advanced analytics and machine learning to identify both known and unknown threats with high accuracy. - Contextual Threat Analysis
Correlates events across the environment to deliver actionable intelligence and reduce investigation time. - Automated Response Capabilities
Enables rapid containment and remediation of threats through automated workflows. - Reduced Alert Fatigue
Prioritizes alerts based on risk, helping teams focus on what truly matters. - Scalable and Cost-Efficient Architecture
Simplifies security operations while optimizing resource utilization and reducing overall costs.
By combining these capabilities into a unified platform, Seceon helps organizations transition from reactive security to a more proactive and resilient approach.
From Reactive Defense to Proactive Security
The shift to unified AI platforms represents more than a technological upgrade-it marks a change in mindset.
Traditional security focuses on reacting to alerts. Modern security focuses on anticipating threats.
By continuously analyzing behavior and identifying early indicators of compromise, organizations can detect risks before they escalate. This proactive approach reduces reliance on post-incident response and strengthens overall resilience.
Conclusion: Building Security That Works Together
The challenges facing modern cybersecurity are not just about sophistication-they are about scale, speed, and complexity. Traditional tools, operating in isolation, are no longer equipped to handle this reality.
Unified AI platforms offer a more effective path forward by integrating capabilities, enhancing visibility, and enabling intelligent automation.
The goal is no longer to have more tools.
It is to have smarter, more connected security that works as a single system.

The post Why Traditional Security Tools Fail-and How Unified AI Platforms Solve the Problem appeared first on Seceon Inc.
*** This is a Security Bloggers Network syndicated blog from Seceon Inc authored by Anamika Pandey. Read the original post at: https://seceon.com/why-traditional-security-tools-fail-and-how-unified-ai-platforms-solve-the-problem/
如有侵权请联系:admin#unsafe.sh