
好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户已经给出了文章的英文内容,看起来是关于后量子密码学(PQC)的准备工作的。 首先,我需要通读整篇文章,抓住主要观点。文章提到,PQC的到来对大多数组织来说,最大的挑战不是选择新算法,而是找到当前应用、基础设施、设备和服务中使用密码学的地方。微软的观点是,这是量子准备的实际基础:无法看到的东西就无法保护或迁移。 接下来,文章详细讨论了密码学在现代IT环境中的嵌入情况,并提到了许多组织面临的挑战:缺乏全面的清单和有效的生命周期流程。因此,建立全面的密码学清单是迈向量子安全未来的关键第一步。 然后,文章介绍了什么是密码学清单,包括证书、密钥、协议、库、算法等,并解释了为什么这个清单很重要:治理与合规、风险优先级和敏捷性。接着讨论了客户主导的密码学态势管理生命周期模型,包括发现、规范化、风险评估、优先级排序、补救和持续监控。 最后,文章提到了微软的安全工具和合作伙伴生态系统如何帮助组织构建和管理这个清单,并提供了一些开始的步骤和检查表。 现在,我需要将这些信息浓缩到100字以内。重点应放在PQC的重要性、挑战在于识别现有加密使用情况以及微软的方法论:构建全面的加密清单作为量子准备的基础,并通过持续监控和合作伙伴工具实现这一点。 可能的结构是:后量子密码学准备的关键在于识别现有加密使用情况;构建全面清单以规划现代化;微软提供工具和合作伙伴支持持续监控和合规。 这样可以确保内容准确且简洁。 </think> 后量子密码学(PQC)准备的关键在于识别现有加密技术的应用场景。构建全面的加密资产清单是基础,涵盖证书、协议、库等。微软通过工具和合作伙伴生态系统支持持续监控与合规管理。 2026-4-16 16:0:0 Author: www.microsoft.com(查看原文) 阅读量:17 收藏
Post-quantum cryptography (PQC) is coming—and for most organizations, the hardest part won’t be choosing new algorithms. It will be finding where cryptography is used today across applications, infrastructure, devices, and services so teams can plan, prioritize, and modernize with confidence. At Microsoft, we view this as the practical foundation of quantum readiness: you can’t protect or migrate what you can’t see.
As described in our Quantum Safe Program strategy, cryptography is embedded in all modern IT environments across every industry: in applications, network protocols, cloud services, and hardware devices. It also evolves constantly to ensure the best protection from newly discovered vulnerabilities, evolving standards from bodies like NIST and IETF, and emerging regulatory requirements. However, many organizations face a widespread challenge: without a comprehensive inventory and effective lifecycle process, they lack the visibility and agility needed to keep their infrastructure secure and up to date. As a result, when new vulnerabilities or mandates emerge, teams often struggle to quickly identify affected assets, determine ownership, and prioritize remediation efforts. This underscores the importance of establishing clear, ongoing inventory practices as a foundation for resilient management across the enterprise.
The first and most critical step toward a quantum-safe future—and sound cryptographic hygiene in general—is building a comprehensive cryptographic inventory. PQC adoption (like any cryptographic transition) is ultimately an engineering and operations exercise: you are updating cryptography across real systems with real dependencies, and you need visibility to do it safely.
In this post, we will define what a cryptographic inventory is, outline a practical customer-led operating model for managing cryptographic posture, and show how customers can start quickly using Microsoft Security capabilities and our partners.
What is a cryptographic inventory?
A cryptographic inventory is a living catalog of all the cryptographic assets and mechanisms in use across your organization. This includes the following examples:
| Category | Examples/Details |
|---|---|
Certificates and keys | X.509 certificates, private/public key pairs, certificate authorities, key management systems |
Protocols and cipher suites | TLS/SSL versions and configurations, SSH protocols, IPsec implementations |
Cryptographic libraries | OpenSSL, LibCrypt, SymCrypt, other libraries embedded in applications |
Algorithms in code | Cryptographic primitives referenced in source code (RSA, ECC, AES, hashing functions) |
Encrypted session metadata | Active network sessions using encryption, protocol handshake details |
Secrets and credentials | API keys, connection strings, service principal credentials stored in code, configuration files, or vaults |
Hardware security modules (HSMs) | Physical and virtual HSMs, Trusted Platform Modules (TPMs) |
Why does this inventory matter? First, governance and compliance: 15 countries and the EU recommend or require some subset of organizations to do cryptographic inventorying. These are implemented through regulations like DORA, government policies like OMB M-23-02, and industry security standards like PCI DSS 4.0. We expect the number and scope of these polices to grow globally.
Second, risk prioritization: Cryptographic assets present varying levels of risk. For example, an internet-facing TLS endpoint using weak ciphers poses different threats compared to an internal test certificate, or local disk encryption utilizing the AES standard. Maintaining a comprehensive inventory enables effective assessment of exposure and facilitates the prioritization of remediation efforts, ensuring that risk-based decisions incorporate live telemetry and data sensitivity.
Third, it helps enable crypto agility: When a vulnerability is discovered in an encryption algorithm, an inventory can tell you exactly what needs updating and where.
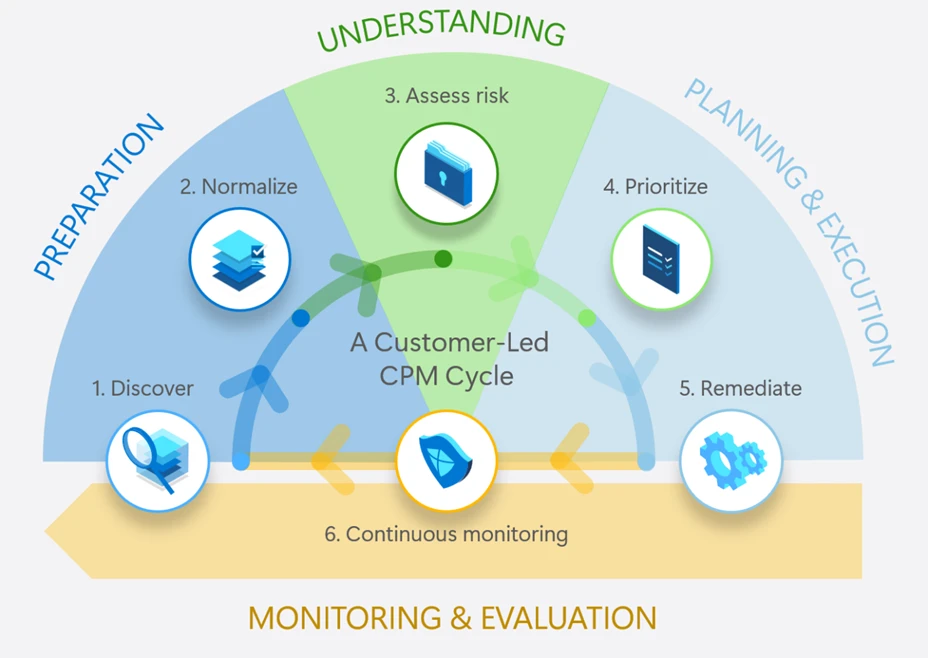
Customer-led cryptography posture management lifecycle
Cryptography Posture Management (CPM) is not a single product, it’s an ongoing lifecycle that customers build and maintain using a combination of tools, integrations, and processes. Many organizations are building Quantum Safe Programs as a broader umbrella for cryptographic readiness. Whether or not you use that exact label, the technical foundation tends to look the same:
- Define what you are managing (the inventory scope and critical assets).
- Define how you make decisions (risk assessment and prioritization).
- Define how you execute change safely (remediation and validation).
- Define how you keep it current (continuous monitoring).
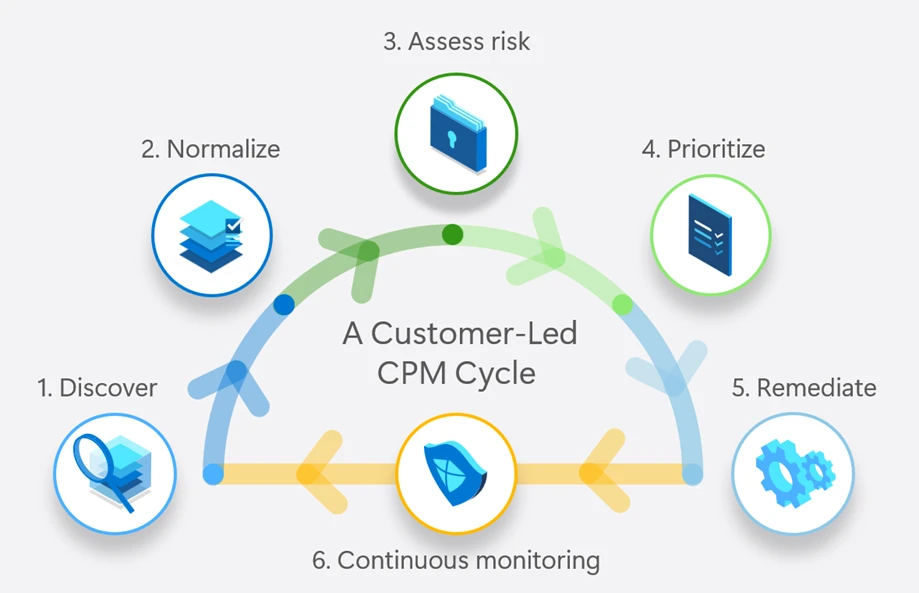
This is where CPM is best understood as a lifecycle you run continuously:
- Discover: Collect cryptographic signals from across your environment – code repositories, runtime environments, network traffic, and storage systems.
- Normalize: Aggregate signals into a unified inventory with consistent data schema (certificate thumbprints, algorithm types, key lengths, and expiration dates).
- Assess Risk: Evaluate cryptographic assets against policy baselines, industry standards, and known vulnerabilities. Identify weak algorithms, expired certificates, and non-compliant configurations.
- Prioritize: Rank findings by risk based on asset criticality, exposure (internal vs. internet-facing), and compliance requirements.
- Remediate: Rotate keys, update libraries, reconfigure protocols, and replace weak algorithms—using available automation and tooling.
- Continuous Monitoring: Continuously track changes. New code commits, certificate renewals, configuration drift, and emerging vulnerabilities all require ongoing vigilance.
You can apply the lifecycle above across four domains: code, network, runtime, and storage:
- Code: Cryptographic primitives and libraries in source code, detected through source code analysis.
- Storage: Certificates, keys, and secrets stored on disk, in databases, in key vaults, or configuration files.
- Network: Encrypted traffic sessions, TLS/SSH handshakes, cipher suite negotiations.
- Runtime: In-memory usage of cryptographic libraries, active key material, process-level crypto operations.
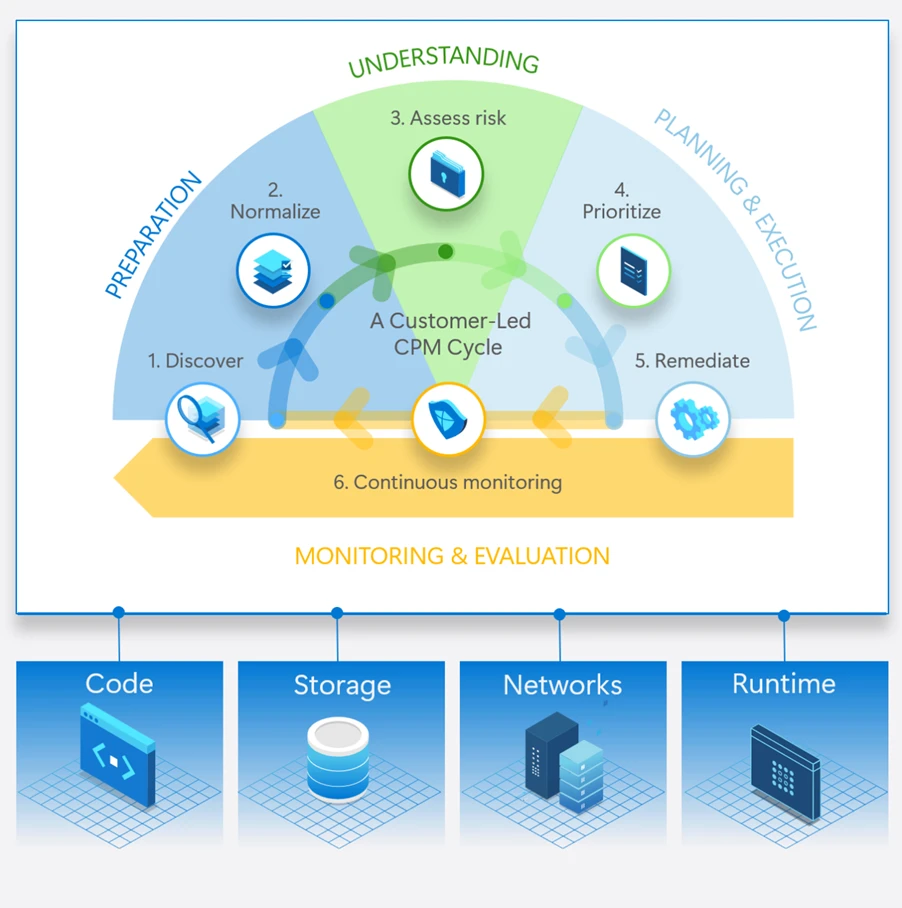
Since the operating model is broad across multiple signals with no single team or platform, ensure you define clear ownership for each stage, with consistent inputs and measurable outputs. That’s why a “one-and-done” scan rarely holds up. The environment changes constantly new deployments, new libraries, renewed certificates, new endpoints, and new policies. The path that scales is an operating model, not a one-time project. By organizing your approach around these domains, you can systematically identify gaps, leverage the right tools for each domain, and build a holistic view of your cryptographic posture.
You don’t have to start from scratch. Many organizations already have Microsoft Security and Azure capabilities deployed that can generate cryptographic signals across code, endpoints, cloud workloads, and networks. The goal is to connect and normalize those signals into an inventory that supports risk-based decisions—then extend coverage with partner solutions where you need deeper visibility, automation, or multi-vendor reach:
| Microsoft Tool | Cryptographic Signals | Domain Coverage | Public Documentation |
|---|---|---|---|
GitHub Advanced Security (GHAS) | Identifies cryptographic algorithm artifacts in code via CodeQL | Code | |
Microsoft Defender for Vulnerability Management (MDVM) | Certificate inventory from devices with MDE agents, including asymmetric keys algorithm details; detects cryptographic libraries and their vulnerabilities | Runtime, Storage | |
Microsoft Defender for Endpoint (MDE) | Identifies encrypted traffic sessions (TLS, SSH) via network detection and response | Runtime, Network | |
Microsoft Defender for Cloud (MDC) | Secret scanning for private keys exposed on cloud infrastructure; DevOps security for code repositories | Storage, Code | |
Azure Key Vault | Centralized inventory of keys, secrets, and certificates stored in Azure | Storage | |
Azure Networking (Firewall, Network Watcher) | High-level indication of encrypted traffic, protocol information (TLS, encrypted communication types) | Network |
Using these tools in the initial phases:
- Code Domain: Activate GitHub Advanced Security for your repositories. Use CodeQL queries to scan for cryptographic algorithm usage, and export results for central oversight.
- Runtime and Storage Domain: Deploy Microsoft Defender for Endpoint and Defender Vulnerability Management across your endpoints. Use the certificate inventory feature to discover certificates and their associated algorithms. Review vulnerable cryptographic libraries flagged by MDVM.
- Network Domain: Enable network protection in MDE to identify encrypted sessions. If you’re using Azure, configure Azure Network Watcher to capture traffic metadata and identify encrypted flows.
- Storage Domain: Audit your Azure Key Vault instances to inventory secrets, keys, and certificates. Use Defender for Cloud secret scanning to detect exposed keys in IaaS and PaaS resources.
- Normalize & Centralize: Bring outputs together in a common view and schema for tracking (for example, in a security data platform or SIEM such as Microsoft Sentinel). Many teams start with supported exports/connectors and existing reporting workflows—then mature toward automation and governed data pipelines as the program scales. The goal is a single, queryable inventory that teams can operate.
- Assess & Prioritize: Define your cryptographic policy baselines (e.g., minimum key lengths, approved algorithms, certificate expiration thresholds). Compare your inventory against these baselines and prioritize based on risk.
This approach leverages tools many organizations already have deployed, providing a pragmatic starting point without requiring significant new investment.
Accelerating your journey with the partner ecosystem
As organizations progress from initial cryptographic inventory to ongoing posture management, Microsoft partners with leading CPM providers to deliver comprehensive solutions that address complex environments across code, infrastructure, devices, applications, and both cloud and on-premises systems. These integrated CPM solutions—running on Azure and deeply connected with the Microsoft Security platform—enable holistic inventory, visibility, and risk assessment by collecting cryptographic signals from Microsoft and non-Microsoft sources, supporting industries with stringent regulatory demands and complex legacy estates, and providing unified management, guided remediation, and quantum security readiness at scale.
Microsoft partners such as Keyfactor, Forescout, Entrust, and Isara, have CPM solutions available today. Each partner delivers unique capabilities spanning certificate and key lifecycle management, network visibility, software supply chain, and code analysis. Together, this growing ecosystem gives customers the flexibility to adopt CPM solutions integrated with the Microsoft Security platform that support a broad range of customer scenarios and align to your architecture, risk profile, and operational maturity.
- Keyfactor: Keyfactor AgileSec discovers, then continuously monitors, all instances of your cryptography, known and unknown, to understand where and how they are used across the organization. Assets are then processed to flag vulnerabilities to enable teams to efficiently remediate risks with advanced integration workflows, providing the base for crypto-agility and quantum readiness.
- Forescout: Forescout Cyber Assurance solution on Azure allows a customer to determine real-time network risk of an enterprise asset including its usage of PQC and non-PQC communications, matrixed by 1,000’s of other attributes including application, protocol, country, geo, risk and posture across IT, IoT and OT environments.
- Entrust: Entrust Cryptographic Security Platform delivers visibility, automation, and control across PKI, key and certificate lifecycle management, and HSMs within a scalable architecture built for crypto-agility and post-quantum readiness.
- Isara: ISARA Advance™ is a crypto posture management solution for enterprises and agencies. Advance is deployed on Microsoft Azure to automate discovery and inventory, quantify the risks, prioritize, and remediate. Within hours of deployment, it discovers cryptographic threats due to outdated protocols, weaknesses in key strengths and algorithms, prioritizes, and allows remediation of the cryptography and configuration changes on the servers, apps, databases, and source code components.
Getting started: a customer checklist
Ready to begin building your cryptographic inventory? Here’s a practical checklist to get started:
- Establish ownership: Assign clear accountability for cryptographic governance. This often spans security, infrastructure, and development teams. It ensures someone owns the overall inventory and posture.
- Start inventory collection: Use the starter playbook above or a Microsoft Partner to begin collecting signals from code, runtime, network, and storage domains using Microsoft tools you already have.
- Define crypto policy baselines: Document your organization’s cryptographic standards (approved algorithms, minimum key lengths, certificate validity periods, protocol versions). Align with industry standards and compliance requirements.
- Prioritize exposures: Not all findings are equal. Prioritize based on asset criticality, exposure (internet-facing vs. internal), and compliance mandates.
- Plan remediation: Identify remediation approaches for high-priority findings—library updates, certificate rotations, protocol reconfigurations. Build runbooks and automation where possible.
- Leverage partners to accelerate: If you need broader coverage, faster deployment, or specialized capabilities, explore the partner ecosystem on Azure Marketplace to find solutions that integrate with your Microsoft security investments and accelerate your efforts.
Cryptographic posture management is a journey, not a destination. As standards evolve, new vulnerabilities emerge, and quantum computing advances, your inventory and operating model will need to adapt. But, by starting now, with the tools you have, the partners who can help, and a clear operating model, you’ll be well-positioned not only for the quantum era but for sound cryptographic hygiene in the years ahead.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
如有侵权请联系:admin#unsafe.sh