
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户的要求是直接写文章描述,不需要特定的开头。 首先,我看看这篇文章主要讲什么。标题是关于漏洞的周报,提到了Azure AI、Spring AI、Fortinet和ICS的暴露。内容里提到Cyble追踪了1431个漏洞和6个ICS问题,其中有270个有PoC,3个在地下论坛被讨论。还有130个被评为CVSS 3.1的严重级别,45个是CVSS 4.0的严重级别。CISA新增了3个到KEV目录,并且发布了5个ICS公告影响西门子等厂商。 文章还列出了前五名的漏洞,包括Azure AI、Claude Code CLI、Spring AI、Cockpit和Fortinet FortiClient EMS。这些都是关键漏洞,可能导致系统被完全控制。 此外,文章提到关键基础设施面临的风险增加,制造业占66.7%,还涉及交通、应急服务等多个领域。最后给出了建议,如优先处理有PoC的漏洞、保护AI环境等。 现在我需要把这些信息浓缩到100字以内。重点包括:上周追踪了1431个漏洞和6个ICS问题;270个有PoC;涉及Azure AI、Spring AI等关键漏洞;CISA新增到KEV;关键基础设施面临风险;建议优先处理高危漏洞等。 确保语言简洁明了,直接描述内容。 </think> 上周报告追踪了1,431个漏洞和6个ICS问题,其中270余个存在公开PoC exploits。微软Azure AI Foundry、Spring AI等关键系统存在严重漏洞。CISA新增3个至KEV目录,并发布5份ICS公告影响西门子等厂商。建议优先处理高危漏洞并加强AI环境防护。 2026-4-16 11:4:48 Author: cyble.com(查看原文) 阅读量:28 收藏
The Week in Vulnerabilities: Azure AI, Spring AI, Fortinet, and Critical ICS Exposure
Cyble’s weekly vulnerability report tracked 1,431 vulnerabilities and 6 ICS flaws last week. Know more...
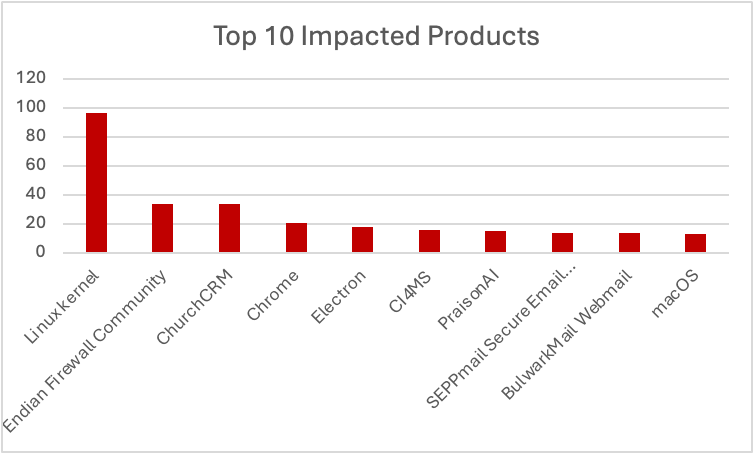
Cyble Research & Intelligence Labs (CRIL) in its weekly vulnerability report tracked 1,431 bugs last week.
Of these, over 270 vulnerabilities have publicly available Proof-of-Concept (PoC) exploits, significantly accelerating exploitation timelines and increasing real-world attack likelihood.
Additionally, 3 vulnerabilities were actively discussed across underground forums, signaling strong adversarial interest and rapid weaponization.
A total of 130 vulnerabilities were rated critical under CVSS v3.1, while 45 were rated critical under CVSS v4.0, reflecting the severity of disclosed issues.
Furthermore, CISA added 3 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
On the industrial front, CISA issued 5 ICS advisories covering 6 vulnerabilities, impacting vendors such as Siemens, Hitachi Energy, and Yokogawa.
Weekly Vulnerability Report’s Top 5 Vulnerabilities
CVE-2026-32213 — Microsoft Azure AI Foundry (Critical)
CVE-2026-32213 is a critical authorization bypass vulnerability in Microsoft Azure AI Foundry.
The flaw exists in the platform’s authorization logic, allowing unauthenticated attackers to bypass security checks and grant themselves administrative privileges. Successful exploitation enables full control over AI environments and associated resources.
CVE-2026-35022 — Claude Code CLI / Agent SDK (Critical)
CVE-2026-35022 is a critical OS command injection vulnerability affecting Anthropic’s Claude Code CLI and Agent SDK.
The vulnerability allows attackers to inject malicious commands into development workflows, resulting in remote code execution and potential compromise of AI pipelines.
CVE-2026-22738 — Spring AI (Critical)
CVE-2026-22738 is a remote code execution vulnerability in Spring AI caused by improper input sanitization in expression evaluation.
Attackers can inject malicious expressions that are executed by the Spring Expression Language, leading to complete application and server compromise.
CVE-2026-4631 — Cockpit (Critical)
CVE-2026-4631 is an unauthenticated remote code execution vulnerability in Cockpit, a web-based Linux server management interface.
The flaw allows attackers to execute arbitrary commands without authentication, potentially leading to full system takeover in enterprise environments.
CVE-2026-35616 — Fortinet FortiClient EMS (Critical)
CVE-2026-35616 is a critical authentication bypass vulnerability in Fortinet FortiClient EMS.
Attackers can bypass authentication and execute arbitrary commands, leading to complete compromise of endpoint management systems.
Vulnerabilities Added to CISA KEV
CISA continues to expand its KEV catalog, reflecting real-world exploitation trends.
Notable addition:
CVE-2026-35616 — Fortinet FortiClient EMS
This vulnerability enables authentication bypass and remote command execution, making it a high-priority remediation target.
The inclusion of enterprise security tools in KEV highlights attackers’ focus on compromising centralized management systems.
Critical ICS Vulnerabilities
CISA issued 5 ICS advisories covering 6 vulnerabilities, many of which impact critical infrastructure environments.
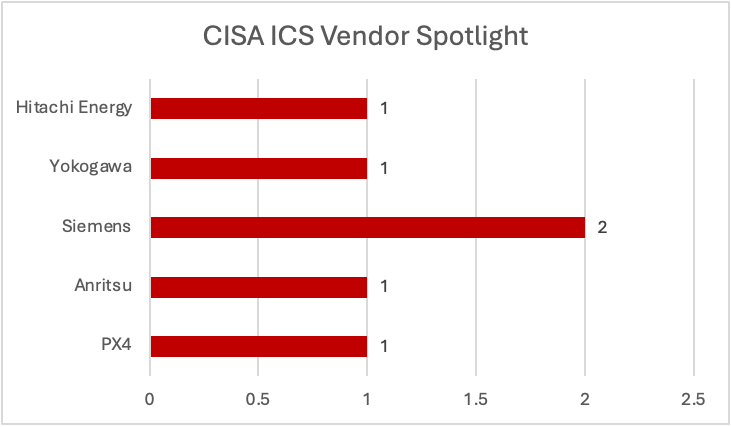
CVE-2026-1579 — PX4 Autopilot (Critical)
A missing authentication vulnerability allowing attackers to execute critical functions without credentials.
This flaw poses risks to autonomous and unmanned systems, potentially enabling unauthorized control.
CVE-2026-3356 — Anritsu Systems (Critical)
This vulnerability involves missing authentication in Anritsu devices, allowing attackers to gain unauthorized access.
CVE-2025-10492 — Hitachi Energy Ellipse (Critical)
A deserialization vulnerability enabling attackers to execute arbitrary code within industrial systems.
Siemens SICAM 8 (Chained Risk)
Two vulnerabilities affecting Siemens SICAM 8 systems—resource exhaustion and out-of-bounds write—can be chained together.
This creates a denial-of-service risk capable of disrupting industrial processes and operational visibility.
CVE-2025-7741 — Yokogawa CENTUM VP (Medium)
A hard-coded password vulnerability that weakens authentication mechanisms and increases risk of unauthorized access.
Critical Infrastructure Sectors Spotlight
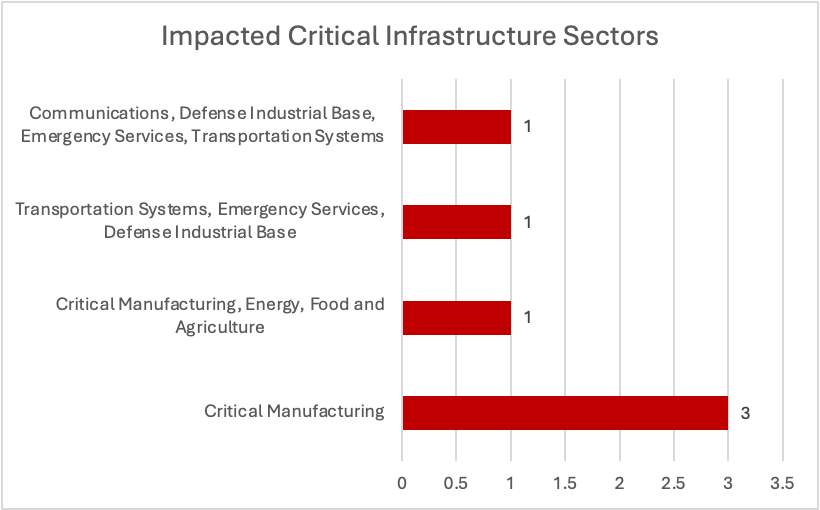
Analysis indicates:
- Critical Manufacturing appears in 66.7% of vulnerabilities
- Cross-sector exposure spans:
- Transportation Systems
- Emergency Services
- Defense Industrial Base
- Communications
This highlights interconnected infrastructure risks, where a single vulnerability can cascade across multiple sectors.
Conclusion
This week’s findings highlight several critical trends:
- Expansion of vulnerabilities into AI and development ecosystems
- Increasing exploitation of enterprise management platforms
- Continued weaknesses in industrial control systems
- Cross-sector risk amplification in critical infrastructure
With 270+ PoCs, KEV-confirmed exploitation, and emerging threats in AI frameworks, organizations face heightened risk across both digital and physical environments.
Key Recommendations
- Prioritize vulnerabilities with PoCs and KEV inclusion
- Secure AI development environments and pipelines
- Patch enterprise management and remote access systems immediately
- Implement strict authentication and access control mechanisms
- Segment IT and OT networks to prevent lateral movement
- Apply compensating controls for unpatched ICS vulnerabilities
- Monitor underground forums and threat intelligence feeds
- Conduct continuous vulnerability assessments and penetration testing
Cyble’s attack surface management and vulnerability intelligence solutions help organizations proactively identify risks, prioritize remediation, and detect emerging threats. By integrating intelligence-driven security strategies, organizations can strengthen resilience across enterprise and critical infrastructure environments.
如有侵权请联系:admin#unsafe.sh
