
嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头。直接写描述就行。 首先,我需要通读整篇文章,抓住主要信息。文章讲的是一个针对YouTube创作者的钓鱼攻击。攻击者发送虚假的版权侵权通知,诱导创作者点击链接,进而窃取他们的Google账户信息。 然后,攻击者利用这些信息接管整个Google账户,包括Gmail、文件和支付信息,甚至劫持YouTube频道用于诈骗。文章还提到这个钓鱼活动像连锁店一样运作,多个攻击者共享同一个平台。 接下来,我需要将这些关键点浓缩到100字以内。要确保涵盖攻击方式、目标、后果以及攻击的运作方式。 可能的结构是:描述攻击手段(虚假版权通知),目标(YouTube创作者),后果(窃取Google账户信息),以及攻击的组织方式(像连锁店一样运作)。 最后,检查字数是否符合要求,并确保语言简洁明了。 </think> 这篇文章揭示了一种针对YouTube创作者的钓鱼攻击。攻击者通过伪造版权侵权通知诱导创作者点击链接,并窃取其Google账户信息。一旦得逞,攻击者可接管创作者的Google账户及 YouTube 频道,并利用其受众进行诈骗。该钓鱼活动采用个性化页面和动态生成的侵权指控增加可信度,并通过多个域名轮换以规避打击。 2026-4-15 13:21:25 Author: securityboulevard.com(查看原文) 阅读量:14 收藏
The post Fake YouTube copyright notices can steal your Google login appeared first on Malwarebytes.
A convincing phishing campaign is going after YouTube creators, and if it works, attackers don’t just steal your Google login. They can take over your entire Google account, including Gmail, your files, and payments, then hijack your YouTube channel and use your audience to run scams.
The lure is a fake copyright strike notification that’s so convincing even security-aware users could fall for it. The attack site pulls in your real channel data, such as your profile picture, subscriber count, and latest video, to build a personalized scare page. It funnels you toward a sign-in page designed to steal your Google account.
The operation runs like a franchise: multiple attackers share the same platform, each running their own campaigns against different creators.
Why your YouTube channel is worth more than you think
For full-time creators, a YouTube channel isn’t just a hobby, it’s a business. It generates revenue through ads, sponsorships, and merchandise. And it all sits behind a single Google login that also controls your Gmail, Google Drive, and payment details.
That’s what makes creators such attractive targets. Attackers who hijack a channel often rebrand it within minutes, typically to impersonate a cryptocurrency company, and use the existing audience to livestream scams. The original creator gets locked out and watches their years of work being used to defraud their own subscribers.
A copyright strike is the perfect bait because it exploits the one thing creators fear most: losing their channel overnight.
“Check your Youtube copyright status instantly”
The campaign runs from a site called dmca-notification[.]info. The browser tab reads “Youtube | Copyright strikes,” and the page itself looks clean and professional, complete with YouTube logo, search bar, and helpful instructions.
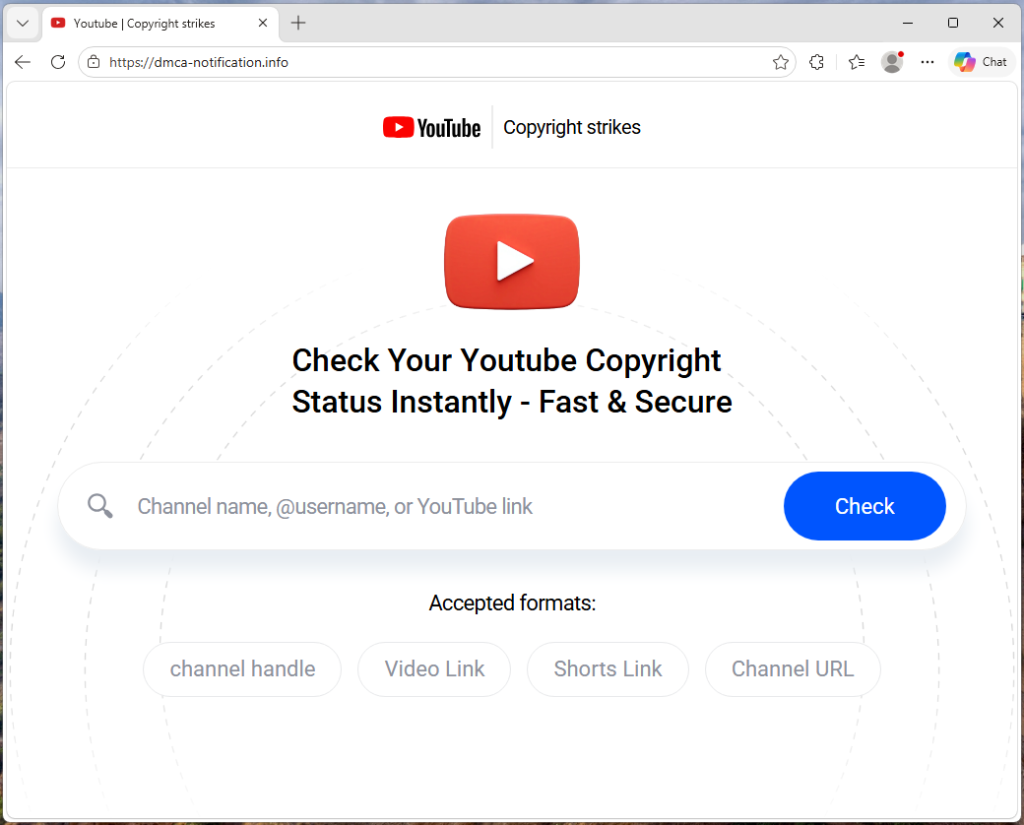
It invites you to enter your channel name, @handle, or video link to check your copyright status. Nothing about it stands out as immediately suspicious.
Each phishing link includes the target’s channel handle directly in the URL, so the page already knows who you are before you type anything.
The source code contains a tracking flag called suppressTelegramVisit, which changes how visits are logged depending on whether an affiliate parameter is present. This suggests the operators may be coordinating traffic through Telegram, although the kit could be distributed through any platform.
Your own videos, used against you
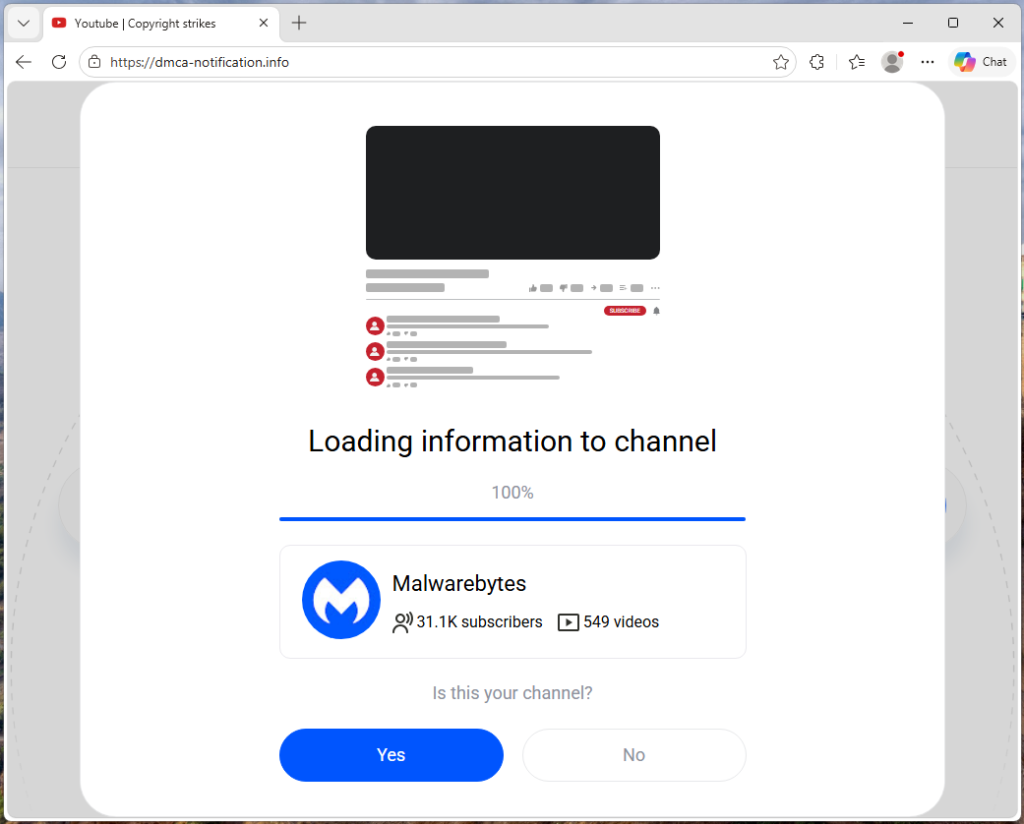
Once the page has your channel name, it fetches real data from YouTube: your avatar, subscriber count, video count, and your most recent upload (including its title, thumbnail, and view count). That information is then used to build a fake copyright complaint.
You see your own branding alongside a claim that a specific segment of your latest video has been flagged for copyright infringement. The timestamps are dynamically generated for each victim based on the video’s length, making each notice look unique and legitimate. It’s similar to receiving a fake legal notice that includes your real home address. The personal details make it harder to dismiss as spam.
“Respond within three days or face enforcement actions”
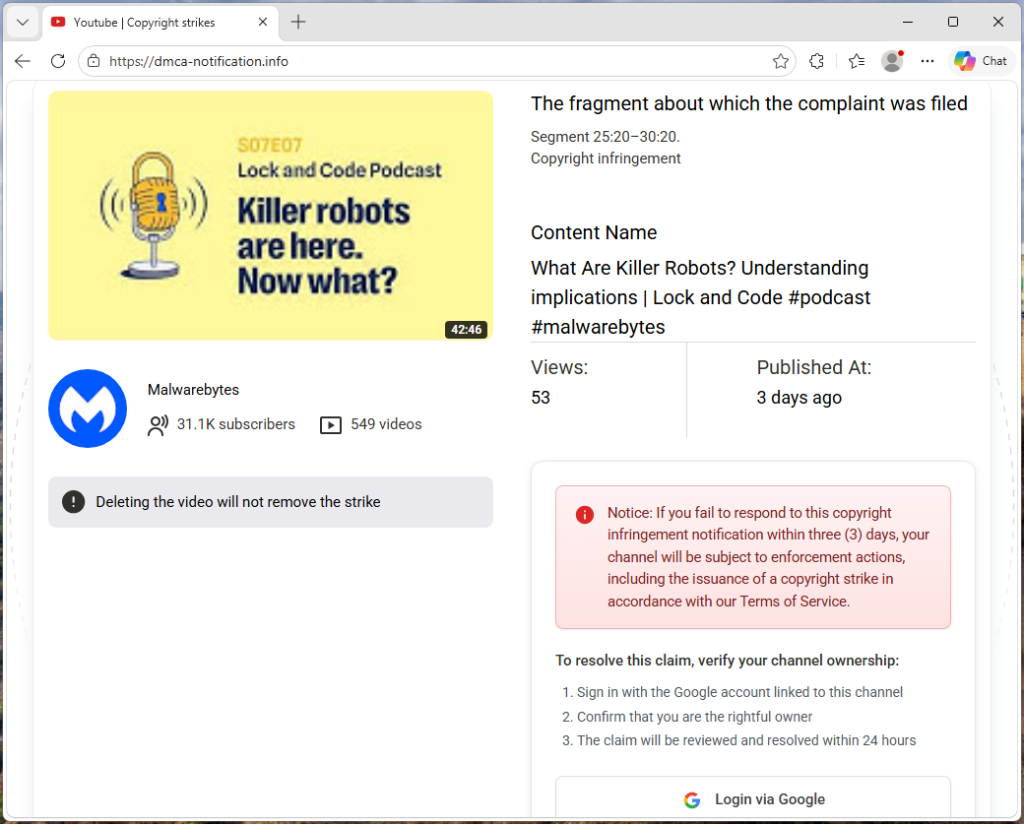
The page piles on the pressure. A warning tells you that deleting the video won’t remove the strike. A red notice threatens that if you don’t respond within three days, your channel will face enforcement actions. The proposed fix is simple: sign in with Google to verify you’re the channel owner, and the claim will be resolved within 24 hours.
Every element on the page is designed to push you toward the “Login via Google” button before you stop to think.
The sign-in page that steals your account
When you click that button, the site contacts its own backend server to fetch the address of an external phishing page, one that the attacker can swap out to a new domain at any time.
In observed traffic, the request to /api/get-active-domain returned the domain blacklivesmattergood4[.]com, which was then loaded inside a full-screen overlay on top of the copyright notice page.
What appears next is a classic Browser-in-the-Browser attack: a fake Chrome pop-up rendered entirely in HTML and CSS. It includes a title bar reading “Sign in – Google Accounts – Google Chrome,” a padlock icon, and a URL that looks like accounts.google.com. None of it is real. They’re all just graphics. The only real address bar is the one at the top of your actual browser, which still shows dmca-notification[.]info.
Inside the fake window sits a convincing replica of Google’s sign-in page. It looks exactly like the real thing, but every keystroke goes to the attacker.

Traffic capture also showed attempts to contact additional domains—dopozj[.]net, ec40pr[.]net, and xddlov[.]net—which returned 502 errors at the time of capture. These may be backup infrastructure or credential relay servers that were offline.
The rotating-domain approach is what makes this campaign resilient. The phishing domain is fetched in real time with no caching, allowing attackers to rotate infrastructure quickly. If one domain is taken down, the next victim is sent to a new one.
Once credentials are entered, the overlay closes and the victim is returned to the copyright notice page with no confirmation or error . It gives the attacker time to use the stolen credentials before the victim realizes anything happened.
Big channels get a free pass (on purpose)
One interesting detail: the kit checks whether the target channel has more than three million subscribers. If it does, the entire phishing flow is skipped. Instead of the copyright strike warning and login button, the page shows a benign message: “Your channel is in good standing. No further action is needed.”
This is almost certainly an evasion tactic. Very large channels are more likely to have dedicated security teams, relationships with YouTube’s trust and safety staff, or the visibility to trigger a rapid takedown if they publicly report the scam. By automatically exempting them, the kit reduces the risk of drawing attention from exactly the people most capable of getting the operation shut down.
Not just one scammer
The source code reveals that this isn’t a single phishing page run by one person. The kit includes an affiliate tracking system where each attacker gets their own ID embedded in the phishing links they send out. A central backend tracks which operator delivered which victim and how far each target got through the funnel. Our traffic capture confirms this: the phishing link included a referral ID (ref=huyznaetdmca), the default affiliate tag, which appears to be a transliteration of a Russian phrase. Brand names like Google and YouTube are also written with lookalike Cyrillic characters in the source code to evade automated security scanners.
In short, this is phishing-as-a-service: a shared platform that multiple attackers can use to run campaigns against YouTube creators at scale.
How to protect yourself
This campaign is a reminder that phishing has moved far beyond badly spelled emails from a Nigerian prince. Today’s phishing kits are professionally engineered platforms with rotating infrastructure, real-time personalization, and franchise-style distribution.
For YouTube creators, the key rule is simple: copyright strikes only appear in YouTube Studio.
If you get a warning anywhere else, treat it as suspicious.
- Be wary of urgency. Real copyright processes don’t rush you into action
- Go directly to studio.youtube.com or through trusted channels to check your status
- Never sign in through a link in an email or message
Spot a fake browser window
- Try dragging it: A real window moves freely. A fake one is stuck inside the page
- Minimize your browser: A real pop-up stays open. A fake one disappears
- Check the URL: If you can’t interact with it, it’s just an image
Even if everything looks right, always check the actual address bar before entering your username and password.
If you’ve already entered your details, act quickly:
- Change your Google password immediately
- Revoke active sessions in your account security settings
- Check your YouTube channel for unauthorized changes
Indicators of Compromise (IOCs)
Domain
dmca-notification[.]info(primary phishing site)blacklivesmattergood4[.]com(credential harvesting domain — active at time of capture)dopozj[.]net(associated infrastructure — 502 at time of capture)ec40pr[.]net(associated infrastructure — 502 at time of capture)xddlov[.]net(associated infrastructure — 502 at time of capture)
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard. Submit a screenshot, paste suspicious content, or share a link, text or phone number, and we’ll tell you if it’s a scam or legit. Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.
*** This is a Security Bloggers Network syndicated blog from Malwarebytes authored by Malwarebytes. Read the original post at: https://www.malwarebytes.com/blog/threat-intel/2026/04/fake-youtube-copyright-notices-can-steal-your-google-login
如有侵权请联系:admin#unsafe.sh