
嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内,而且不需要特定的开头。首先,我得通读一下这篇文章,了解它的主要观点。 文章主要讲的是OT( operational technology)安全的重要性,以及传统的“空气间隙”隔离方法已经过时了。现在IT和OT之间的界限变得模糊,安全团队需要统一的视角来管理风险。Tenable公司推出了VM-Native OT Discovery功能,整合到他们的漏洞管理和安全中心中,提供对OT、IoT和影子IT资产的统一可见性。 接下来,我需要提取关键点:停止孤立管理风险、统一可见性、VM-Native OT Discovery的功能、解决黑盒问题、无需额外硬件、提升整体安全性。 然后,把这些点浓缩成一段话,不超过100字。要确保涵盖主要技术点和解决方案的优势。 最后,检查一下是否符合用户的要求:直接描述内容,不使用特定开头语,并且简洁明了。 </think> 文章指出传统“空气间隙”隔离已失效,IT与OT界限模糊。Tenable推出VM-Native OT Discovery功能,整合至漏洞管理和安全中心,提供跨IT与OT的统一资产可见性及风险评估能力。该方案无需额外硬件投资或复杂部署流程,助力企业实现高效OT安全防护。 2026-4-15 12:50:0 Author: www.tenable.com(查看原文) 阅读量:15 收藏
April 15, 2026
5 Min Read
Stop managing risk in silos. VM-Native OT Discovery, now available in Tenable Vulnerability Management and Tenable Security Center provides unified visibility across IT and OT domains. See every asset and manage your total cyber exposure in a unified view.
Key takeaways
- The air gap is dead. IT security teams are inheriting responsibility for operational technology (OT), but often lack visibility into these systems.
- Security teams face significant barriers with OT security. Fear of disrupting fragile devices and the high cost of specialized hardware have created a dangerous "black box" in the attack surface.
- The perfect “on-ramp” to OT security. A new OT Discovery engine embedded in Tenable Vulnerability Management and Tenable Security Center allows security teams to safely profile OT, IoT, and shadow IT assets using the tools they already own.
For decades, the concept of the "air gap" — a physical isolation between IT networks and critical operational technology (OT) — provided security leaders with a sense of comfort. The assumption was simple. Digital threats stay on the corporate network, while physical operations run safely in isolation.
In today's hyper-connected world, that assumption is often wrong and leaves your OT environment exposed to preventable cyber risk.
From modern data centers and smart hospitals to commercial real estate and universities, the line between the digital and the physical has blurred. IT security teams are increasingly inheriting responsibility for securing cyber-physical systems (CPS) — the HVAC controllers keeping servers cool, the badge readers securing facility entrances, and the power distribution units keeping the lights on.
Yet, for many organizations, these OT assets are a massive blind spot.
The "black box" problem
While vulnerability management programs have matured rapidly for IT assets, covering everything from cloud workloads to laptops, operational environments are often a "black box."
This visibility gap usually stems from two distinct barriers:
- There is a pervasive (and historically valid) fear that scanning OT/IoT assets with traditional IT security tools could knock fragile devices offline, disrupting critical business operations.
- Traditional OT security tools often require a massive undertaking. The complexity and cost of deploying expensive specialized hardware, managing long-term evaluations, architecting complex mirror ports, and navigating the political minefield of installing new appliances in sensitive production environments make these projects difficult to justify.
The result is a dangerous paradox. Security teams are responsible for the risk of interconnected systems, but don’t have the tools to see or secure them. Attackers, however, face no such barriers, frequently pivoting from compromised IT networks to poorly defended OT assets to maximize impact.
Rethinking converged OT/IT security
To secure the modern attack surface, organizations must stop managing IT and OT risk in silos. Security leaders need a unified view that treats a vulnerability on a programmable logic controller (PLC) with the same rigor and context as a vulnerability on a Windows server.
Achieving this requires a fundamental shift in how we approach asset discovery. Security teams need streamlined methods that provide the necessary depth of OT visibility for compliance and risk reduction, without the friction of deploying hardware across physical sites. They need a way to safely seeshadow OT assets using the infrastructure already in place.

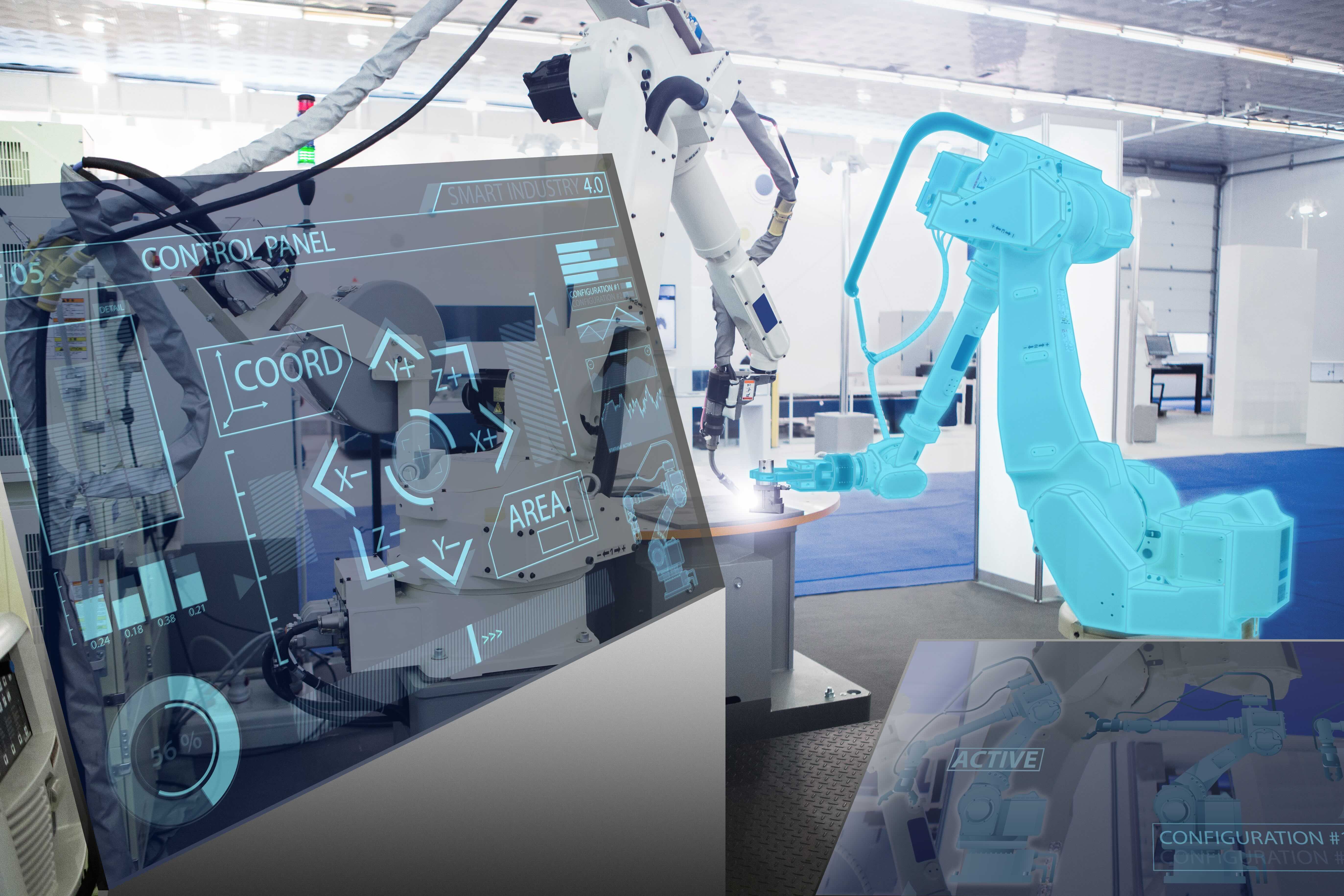
Image: A segment of Tenable’s research and testing lab for operational technology (OT).
Introducing VM-Native OT Discovery
Our latest release fundamentally changes the economics and accessibility of OT security tools. We are excited to announce OT Discovery, a new capability embedded directly inside the Tenable One Exposure Management Platform that provides security teams with foundational visibility into OT and IoT environments. It’s the perfect on-ramp to OT security, so you can uncover hidden OT risks and deep asset-level details.
Here is how it changes the game for your security program:
- Safe visibility for cyber-physical systems. OT Discovery uses the same Active Query engine found in our specialized Tenable OT Security solution—now natively integrated into Tenable Vulnerability Management and Tenable One. It performs "smart," protocol-aware handshakes to verify assets before querying them so you can safely profile PLCs, human-machine interfaces (HMIs), IoT devices, and shadow IT assets across your environment.
- Unified OT/IT exposure management. By integrating OT asset data, including vendor, model, and firmware details, directly into your existing dashboards, you can break down silos and view your organization's total risk exposure in a single pane of glass.
- Extend the value of your security investments. No need to rip and replace or install new hardware. This capability enables you to extend the value of your existing vulnerability management toolsets to uncover the OT risk hiding on your network.
Breaking down silos across IT and OT
Adopting a unified approach to OT/IT exposure management builds trust.
Historically, the relationship between IT security and facility operations teams has been strained. IT wants to scan and patch known vulnerabilities. Operations teams require uptime and stability. When IT security teams try to enter the OT space with aggressive scans or unfamiliar hardware, friction is inevitable.
VM-Native OT Discovery changes the conversation. Because Tenable relies on trusted, safe query methods through familiar infrastructure, the security team can approach the ops team with reliable data and real-time exposure intelligence.
Instead of asking, "Can we install a black box on your network?" you can say, "We noticed three unmanaged PLCs communicating on the subnet. Here is exactly what they are. Let’s work together to secure them now rather than waiting 6-12 months to patch during the next maintenance interval."
Get started with OT security today
OT security is no longer just for industrial giants and organizations managing critical national infrastructure. Every manufacturer, warehouse operator, and organizations smart building management systems face operational risk.
Ready to get visibility into your OT blind spots? You don't need a massive budget or a year-long deployment project to get started. Watch this quick demo to see how you can secure your most critical assets with the vulnerability management tools you already use.
Are you an existing Tenable customer? Explore the user guide documentation for Scan Templates and Discovery Settings to get started.
Learn more
- Dive deeper into the challenges and solutions for securing OT with our eBook, “Blackbox to blueprint: A security leader’s guide to managing OT and IT risk.”
- Explore our complete Tenable One exposure management platform, offering scalable security solutions for the entire attack surface.
- Request a demo to find out how Tenable exposure management solutions fit into your cybersecurity roadmap.

Anthony Johnson
Senior Product Marketing Manager
Anthony Johnson leads product marketing and GTM strategy for Tenable’s operational technology (OT) security and vulnerability management practice areas. He focuses on the convergence of industrial innovation and cyber resilience, exploring critical themes such as CPS/IoT security, cloud adoption in OT, and the role of AI in protecting critical infrastructure. Drawing on a diverse background across technology, management consulting and public sector verticals, Anthony provides strategic insights to help organizations drive innovation without compromising security.
- OT Security
- Risk-based Vulnerability Management
Cybersecurity news you can use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
如有侵权请联系:admin#unsafe.sh