
好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,了解主要内容。 文章主要讲的是CRIL分析了一个名为MiningDropper的Android恶意软件框架的激增情况。这个框架结合了加密货币挖矿和部署信息窃取者、远程访问木马和银行恶意软件的能力。它的多阶段有效负载交付架构使用了XOR和AES加密、动态DEX加载和反仿真技术,使得检测困难。 接下来,文章提到MiningDropper被用于多个活动,特别是针对印度用户的info-stealer活动和影响拉美、欧洲和亚洲的BTMOB RAT活动。此外,大规模遥测分析显示了广泛的分布和低检测率,突显了其规避技术的有效性。 关键点包括:它是多阶段的Android恶意软件框架,结合挖矿和恶意有效负载;使用XOR和AES加密;通过钓鱼网站分发;以及影响多个地区的用户。 现在,我需要将这些信息浓缩到100字以内。要抓住核心: MiningDropper是什么、它的功能、分发方式、目标地区以及检测情况。 可能的结构:MiningDropper是一个复杂的Android恶意软件框架,结合挖矿和部署多种恶意软件。它使用多阶段加密技术来逃避检测,并通过钓鱼活动分发到印度、拉美、欧洲和亚洲。超过1500个样本被发现,低检测率显示其高效传播能力。 这样应该能涵盖主要信息,并且控制在100字左右。 </think> MiningDropper 是一种复杂的 Android 恶意软件框架,结合了加密货币挖矿与信息窃取者、远程访问木马(RAT)及银行恶意软件的部署能力。其采用多阶段有效负载交付架构,通过 XOR 和 AES 加密、动态 DEX 加载及反仿真技术逃避检测。该框架被用于针对印度用户的 info-stealer 活动及影响拉美、欧洲和亚洲的 BTMOB RAT 活动。分析显示超过 1,500 个样本中 50% 以上具有低检测率,表明其高效的传播与规避能力。 2026-4-15 12:5:10 Author: cyble.com(查看原文) 阅读量:31 收藏
CRIL analyzes a surge in an ongoing campaign to deliver MiningDropper — a modular Android malware framework - at scale.
Executive Summary
Cyble Research and Intelligence Labs (CRIL) has been monitoring a significant surge in the use of “MiningDropper”, a sophisticated Android malware delivery framework that combines cryptocurrency mining capabilities with the deployment of infostealers, Remote Access Trojans (RATs), and banking malware.
MiningDropper employs a multi-stage payload delivery architecture that combines XOR-based native obfuscation, AES-encrypted payload staging, dynamic DEX loading, and anti-emulation techniques. This layered design enables threat actors to evade static detection, delay analysis, and dynamically control the delivery of the final payload.
Our analysis indicates that MiningDropper is being actively leveraged across multiple campaigns, with a particularly notable infostealer campaign targeting Indian users, alongside a BTMOB RAT campaign affecting LATAM, Europe, and Asia.
Additionally, large-scale telemetry analysis shows widespread distribution with low detection rates, highlighting the effectiveness of its evasion techniques and the rapid reuse of its modular architecture across campaigns.
Key Takeaways
- MiningDropper is a multi-stage Android malware delivery framework that combines cryptocurrency mining activity with the deployment of additional malicious payloads.
- The recently identified MiningDropper variant leverages a trojanized version of the open-source Android application project “Lumolight”.
- Dropper implements layered obfuscation (XOR + AES) and native code execution to evade detection and hinder analysis
- Uses a state-driven payload execution, initially deploying a miner before transitioning to user-defined payloads
- Actively used in phishing campaigns impersonating RTO services, banks, telecom providers, and popular applications
- Delivers malware payloads, including infostealers and BTMOB RAT, capable of full device compromise
- Over 1,500+ samples observed, with more than 50% exhibiting low antivirus detection, indicating ongoing evasion and rapid campaign scaling
Dropper Characteristics
| Category | Description |
| Type | Multi-stage dropper |
| Capabilities | Crypto mining |
| Infection Vector | Smishing, Social Media, and Fraudulent Websites |
| Initial Payload | Trojanized LumoLight application |
| Final Payloads | Infostealer, RAT, Banking Trojan |
| Obfuscation Techniques | XOR-based string obfuscation in native code, AES-encrypted asset files |
| Target Region | Asia, Europe, LATAM |
Overview
Recently, CRIL observed a notable surge in the use of MiningDropper (also referred to as BeatBanker) as an adaptable malware delivery framework for distributing infostealers, Remote Access Trojans (RATs), and banking malware.
The threat actor employs a multi-stage payload architecture that incorporates XOR-based native-string obfuscation, AES-encrypted payload staging, and anti-emulation techniques, significantly complicating detection and analysis.
Our investigation revealed that MiningDropper is actively leveraged across multiple campaigns, with particularly notable activity observed in two primary campaign clusters:
Infostealer Campaign
This campaign primarily targets users in India by impersonating:
- Regional Transport Office (RTO) services
- Banking institutions
- Telecom providers
In October 2025, Cyble analyzed a campaign that used RTO services as a lure, during which multiple malware variants were identified, including one that used MiningDropper. In its more recent variant, MiningDropper incorporates native code along with a trojanized open-source application.
In this campaign, victims are lured to download malicious APK files via phishing websites or social media platforms, ultimately leading to the deployment of infostealer payloads designed to harvest sensitive user and financial data.
The following sites were identified as distributing MiningDropper as part of an infostealer campaign:
- hxxps://cardcpp[.]online/imobile.apk
- hxxps://hamzaansari1612-ux[.]github.io/ICICI00/imobile.apk
- hxxps://getchaiian[.]short.gy/Getchallan0176
- hxxps://raw.githubusercontent[.]com/singhsonali3021-pixel/my-apk/main/ICICI%20BANK%20CREDIT%20CARD.apk
- hxxps://cardhelp[.]live/SBICreditCard.apk
- hxxps://downloadhdfcapp[.]pythonanywhere.com/download/latest.apk
- hxxps://protectcc[.]online/imobile.apk
- hxxps://dkfootwearstore[.]shop/Jio%20Free%20Recharge.apk
- hxxps://www.icicimanagecards[.]online/iMobile%20Lite.apk
BTMOB RAT Campaign
The second campaign distributes MiningDropper via fraudulent sites targeting users across:
- Europe
- Latin America
- Asia
In this case, the dropper delivers BTMOB RAT, a full-featured Android remote access trojan. We first identified BTMOB RAT in February 2024 as a variant of the SpySolr malware, capable of credential harvesting, device takeover, real-time remote control, and facilitating financial fraud operations.
At the time of its initial discovery, the malware was distributed without a packer and was detected by multiple antivirus products. However, in recent campaigns this year, BTMOB RAT is being distributed via MiningDropper, significantly reducing its detection footprint to as few as 1–3 detections.
The following phishing sites were identified as distributing MiningDropper as part of a BTMOB RAT campaign:
- hxxps://www[.]kavoutai[.]com/signed[.]apk
- hxxps://free-secure[.]com/Free%20Secure%20-%20Annulation[.]apk
- hxxps://litter[.]catbox[.]moe/o6pxvp[.]apk
- hxxps://tv-pluto[.]vercel[.]app/PlutoTv[.]apk
- hxxps://www[.]dl[.]dropboxusercontent[.]com/scl/fi/r9d5y9ch1k7dwvw6l36rj/TecnoCasaFotosPiso[.]apk?rlkey=z6n2qvft8v3nzm66fgy6acwcx
- hxxps://googleeplaaystore[.]pages[.]dev/assets/AGENDA2026[.]apk
Over the past month, we identified more than 1,500 MiningDropper samples in the wild, highlighting the rapid proliferation and reuse of this malware framework. Detection telemetry reveals:
- A majority of samples cluster at very low detection rates, with over 50% exhibiting minimal antivirus coverage, indicating effective evasion techniques
- The largest concentration of samples (~668) shows only 3 AV detections, suggesting widespread undetected distribution
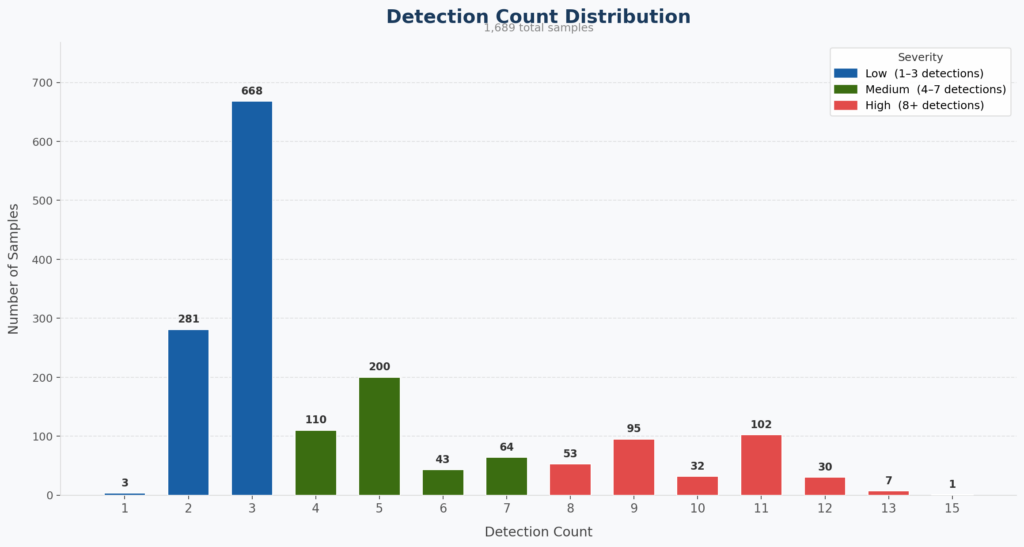
These observations underscore that MiningDropper is not merely another Android dropper, but a scalable malware-as-a-framework, enabling threat actors to efficiently deploy diverse payloads while maintaining a low detection footprint.
A detailed technical analysis is presented in the following section.
Technical Analysis
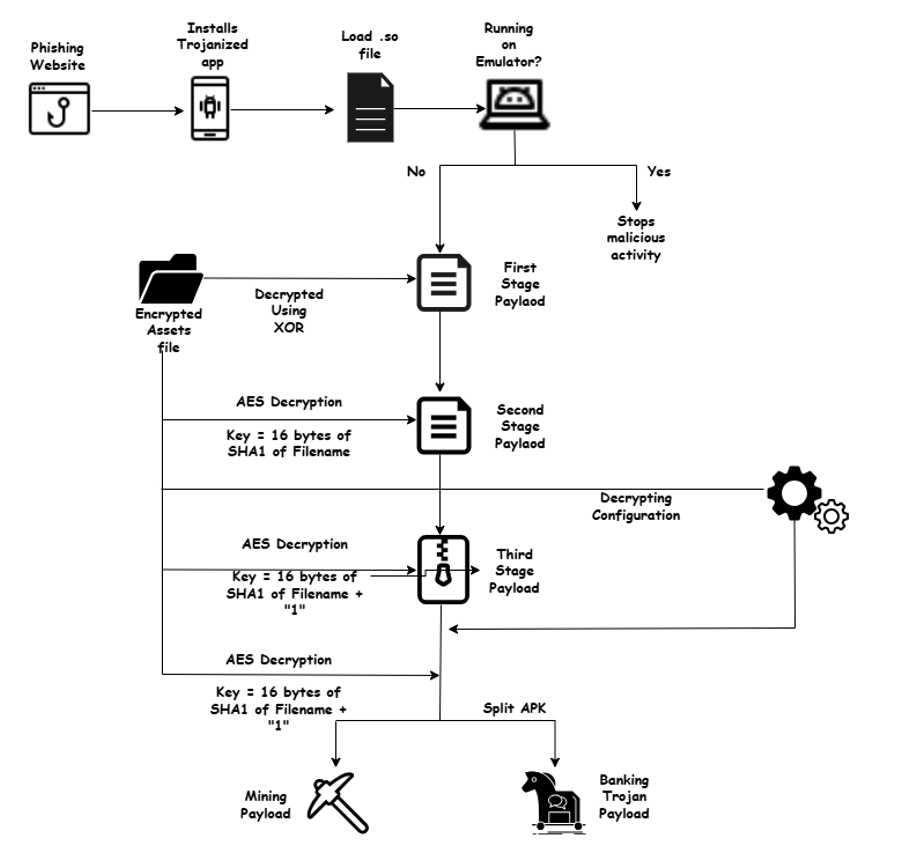
MiningDropper employs a multi-stage, modular architecture combining native code, dynamic loading, staged decryption, and configuration-driven payload delivery. Each stage progressively unpacks the next payload while minimizing static exposure and hindering detection.
For the technical analysis, we analyzed the APK “Free Secure – Annulation.apk” (58a94f889547db8b2327a62e03fb2cce3bda716278d645ee8094178ecda2e9e6), which is being distributed via a phishing site “hxxps://free-secure[.]com/Free%20Secure%20-%20Annulation.apk”.
Initial Native Stage
The threat actors appear to have trojanized the open-source Android application project “LumoLight.” The malicious activity is executed via the application subclass, which loads the native library “librequisitionerastomous.so.” This library contains XOR-obfuscated strings that are decrypted at runtime, a technique used to hinder static analysis and evade automated detection mechanisms.
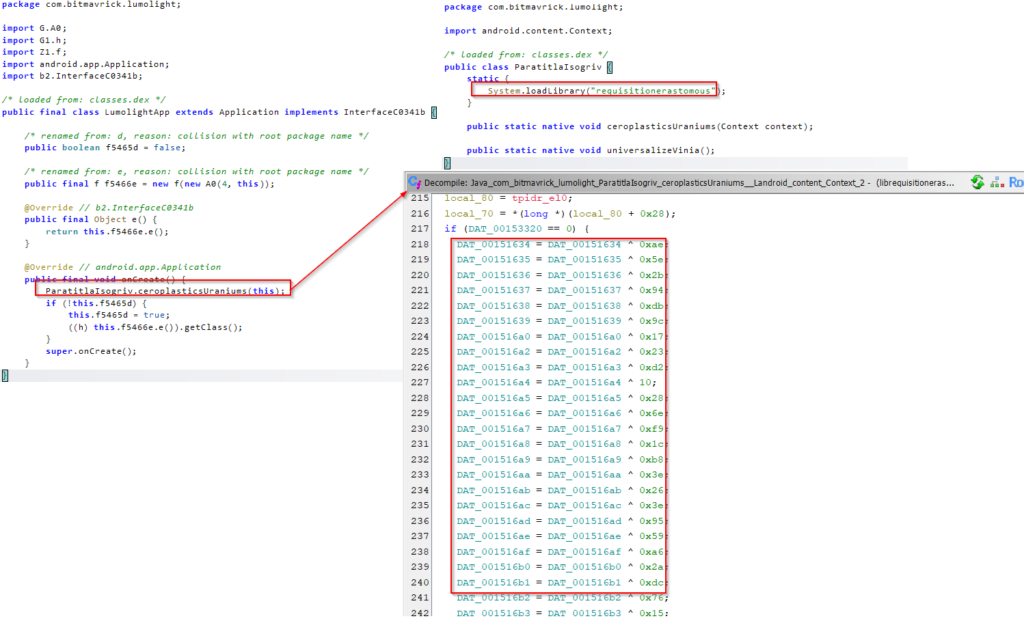
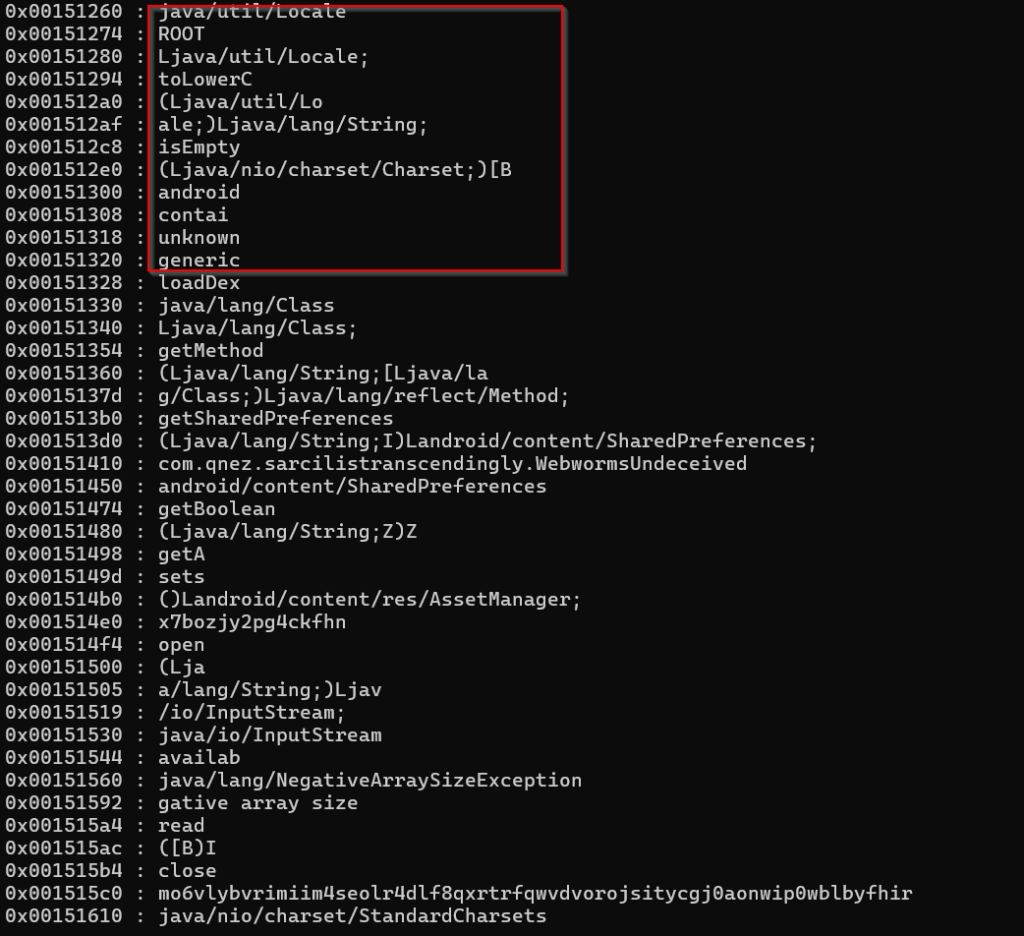
After decrypting the strings from the native code, it is evident that the native library has implemented anti-emulation techniques. The application checks platform details, system architecture, and device model information to determine whether it is running on an emulator.
If an emulated or rooted environment is detected, the malware terminates its malicious execution.
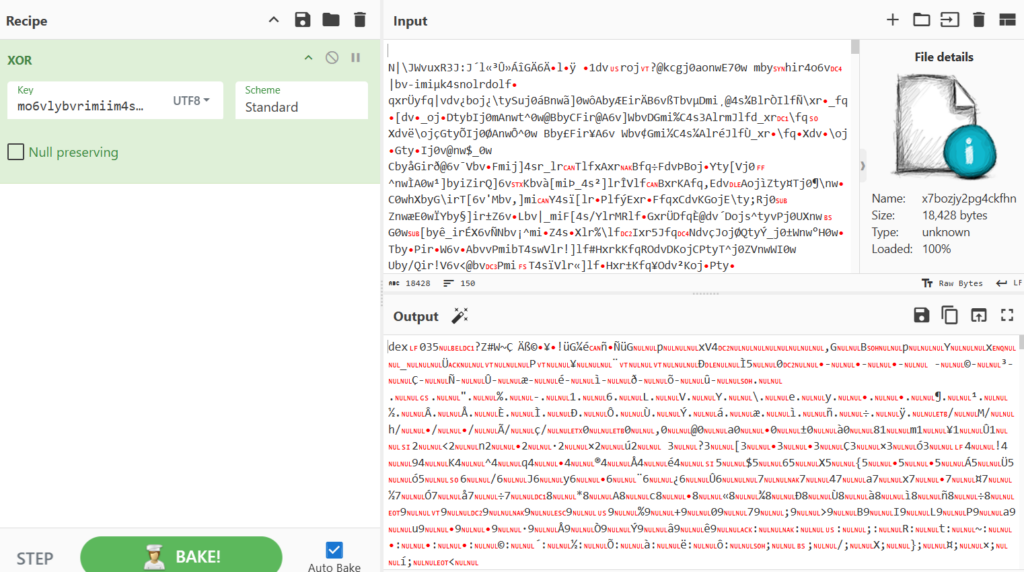
The native library is also responsible for decrypting and executing the first-stage payload from the APK’s assets directory. The asset “x7bozjy2pg4ckfhn” is decrypted using a long hardcoded XOR key, producing the first-stage DEX payload.
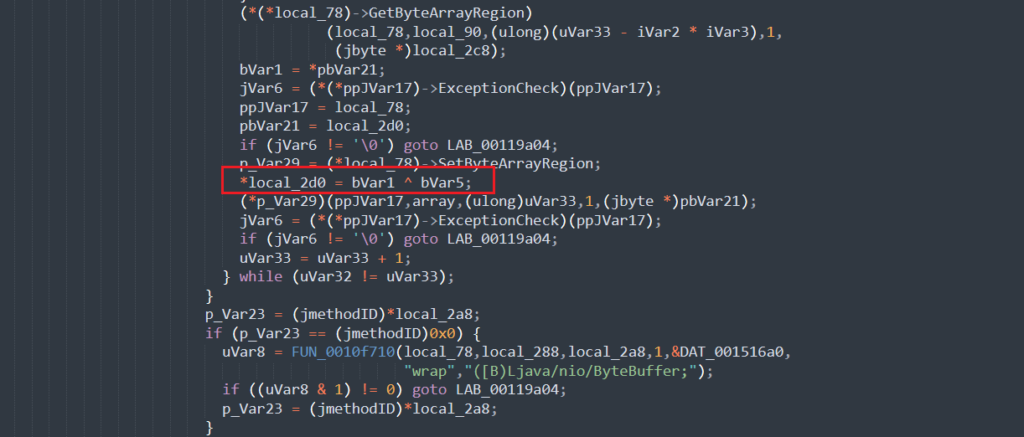
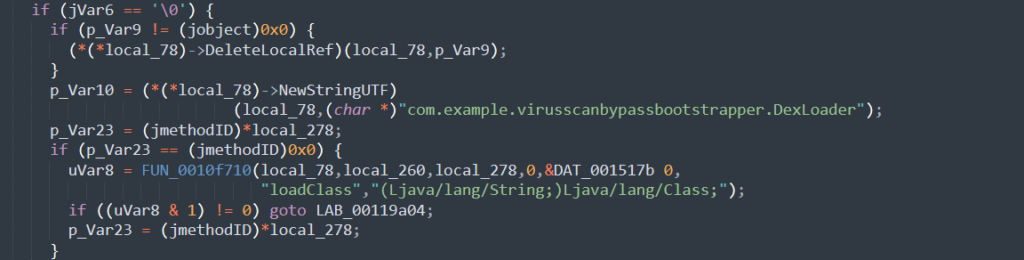
After decrypting the first-stage payload, the native code dynamically loads the DEX file using DexClassLoader and invokes the malicious class “com.example.virusscanbypassbootstrapper.DexLoader.”
First Stage Payload
The decrypted first-stage payload acts primarily as a bootstrap loader. Its main purpose is to receive execution from the native library, decrypt the next-stage payload, and execute it. This stage contains a loadDex() method that decrypts the second-stage payload and executes it via dynamic code loading.
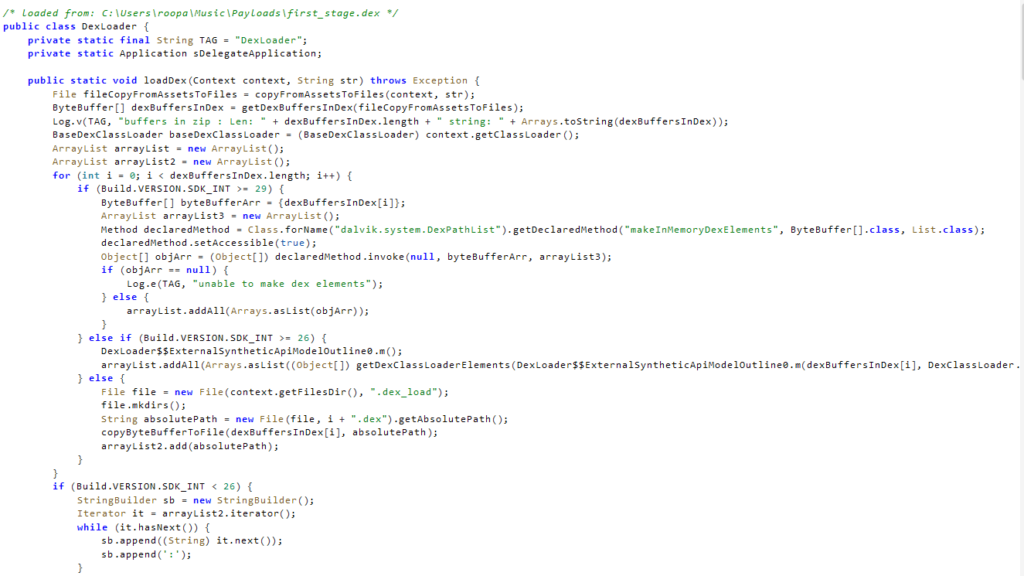
The first stage retrieves the encrypted second-stage file “4ozvcznaamqmioqf/sorxbqp8” from the assets folder and decrypts it using AES.
The AES key is derived from the first 16 bytes of the SHA-1 hash of the filename sorxbqp8, showing that the TA uses filename-derived key material rather than storing raw AES keys directly.
This approach slightly increases analysis effort because the decryption key must be reconstructed from the naming logic rather than extracted as a static constant.
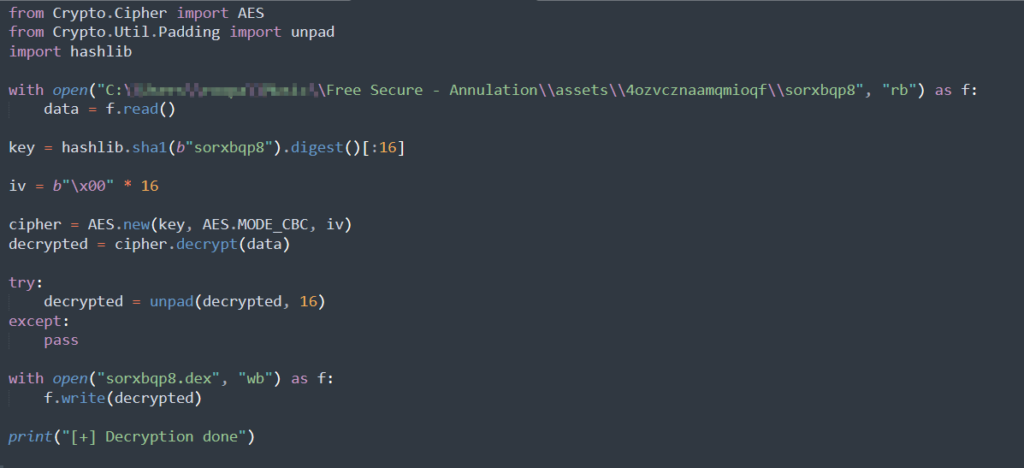
After decryption, the first stage loads the recovered second-stage dex using Dex Class Loading.
Second Stage Payload
The second-stage payload is the most visible portion of the chain from the victim’s perspective. It presents a fake Google Play update interface that deceives the user into believing a legitimate update or service repair is underway.
This stage effectively serves as the social-engineering layer of the infection flow, masking the malicious installation behind a familiar Android/Google-themed update prompt.
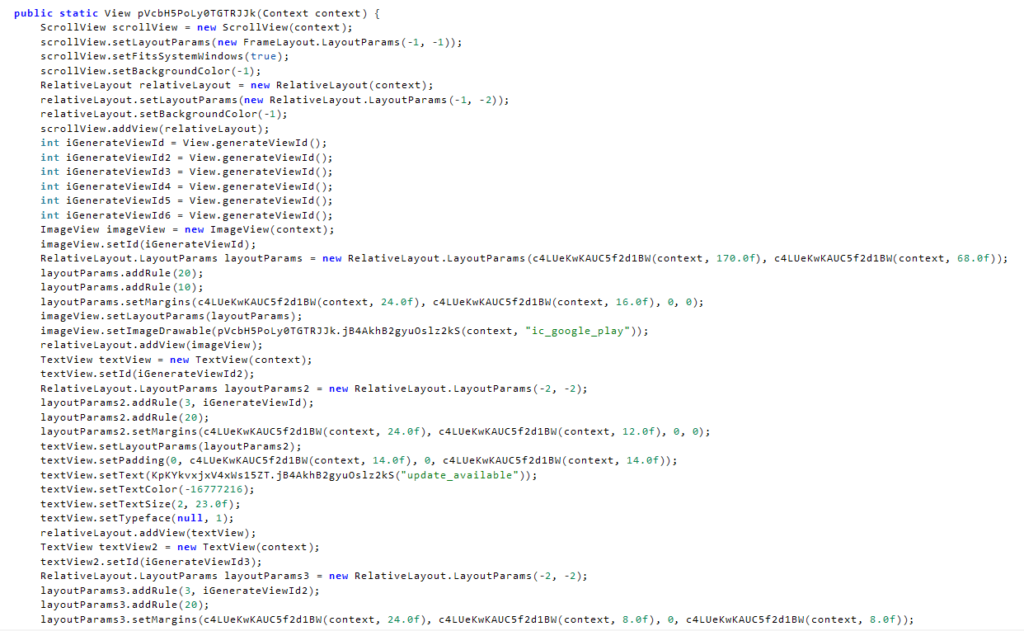
In addition to the visual lure, the second stage loads the class com.qnez.sarcilistranscendingly.App responsible for decoding and orchestrating the remaining stages. This component decrypts the file “jajmanpongids” using AES, again deriving the key from the first 16 bytes of the SHA-1 hash of the filename plus the suffix 1.
In this case, the effective key material is based on jajmanpongids1. The decrypted output is a ZIP archive that contains the third-stage installer components.
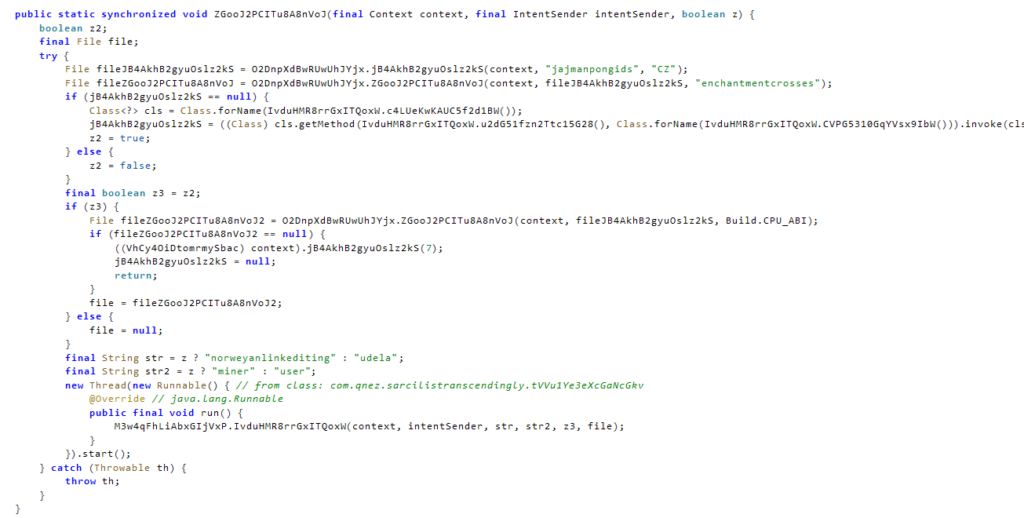
Based on the observed code paths, the malware operates in two distinct modes: one linked to the “miner” component and the other to a “user payload.”
The behavior indicates that the second-stage payload initially activates the miner module, then transitions state—either upon completion or failure—and then executes the user-defined payload.
This distinction highlights that the campaign is built to support flexible, multi-purpose monetization rather than a fixed single-payload approach.
The second stage also decrypts one of two configuration files from assets: “norweyanlinkediting” for the miner path or “udela” for the user-defined path. Both use the same AES pattern, with the key derived from the first 16 bytes of the SHA-1 hash of the filename plus 1.
For the user-defined payload, the decrypted configuration contains:
{"isRemoteControl": true, "isTestKeyEnabled": false, "splits": ["transnaturationsaxhorn", "mischanterperilling", "unwieldlyostearthritis"], "subscriptionEndMillis": 1777220616438, "messageAuthenticationCode": "HaZRwGj6UZDpqKSf43o/Cg==", "simpleInstaller": "deprecated"}For the miner payload, the configuration contains:
{"isRemoteControl": false, "isTestKeyEnabled": false, "splits": ["bilbopseudomelanosis"], "subscriptionEndMillis": 4611686018427387903, "messageAuthenticationCode": "eVAmHju3UqrVWR56gOMaUQ==", "simpleInstaller": "deprecated"}The third-stage payload uses these configuration files to identify which encrypted asset files correspond to the remote control payload and which are associated with the miner component.
Third Stage Payload
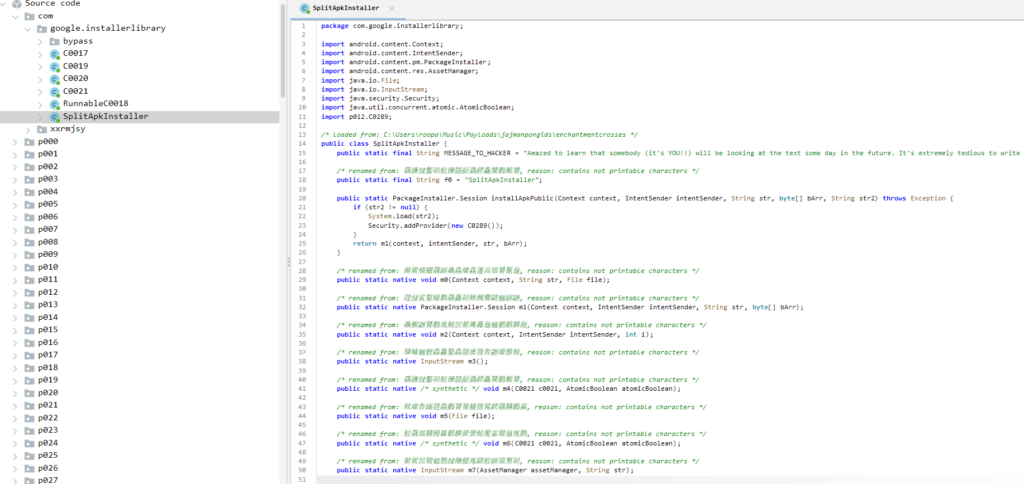
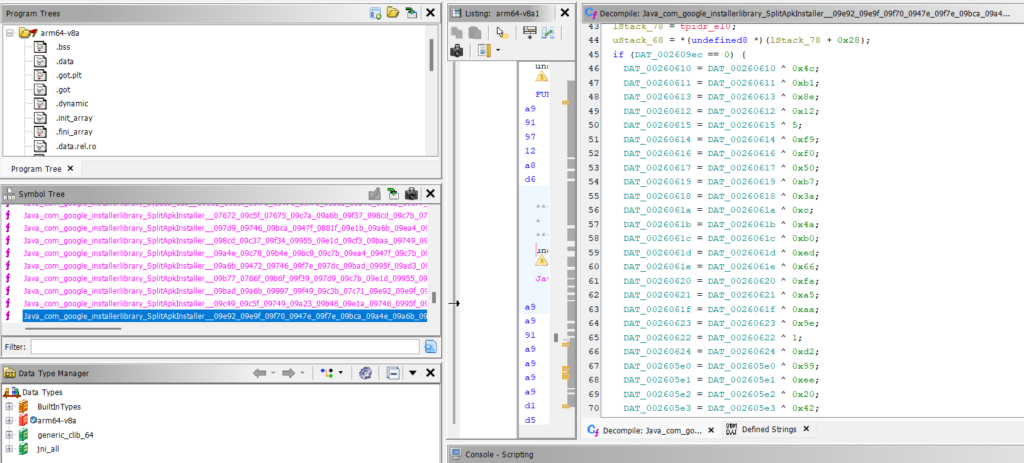
The third-stage payload is extracted from the decrypted ZIP archive “jajmanpongids.zip”, which contains the DEX file “enchantmentcrosses” along with ARM native libraries. Similar to earlier stages, this payload leverages native code and XOR-based string obfuscation to evade analysis.
Functionally, it operates as a split-APK installer module that reconstructs and installs the final payload package using components defined in the configuration.
Final Payloads
For the user-defined path, the third stage processes the three split entries listed in the configuration: transnaturationsaxhorn, mischanterperilling, and unwieldlyostearthritis. These files are present in the APK assets and are encrypted using the same AES pattern used elsewhere in the chain.
After decryption, the components are merged to reconstruct the final malicious package. In this sample, this merged payload is attributed to BTMOB RAT.
BTMOB RAT can perform multiple malicious activities, including credential theft via WebView-based injections, keylogging, and data exfiltration. It abuses Android Accessibility Services to gain extensive control over the device, enabling actions such as unlocking the device, simulating user interactions, and granting additional permissions.
Furthermore, it supports real-time remote control via WebSocket-based C2 communication, enabling attackers to monitor the infected device’s screen in real time, manage files, record audio, and execute commands.
For the miner path, the third stage decrypts the single asset bilbopseudomelanosis, again using filename-derived AES key material. In this branch, the output is a standalone APK that handles cryptocurrency mining.
Taken together, the final stage design reveals that MiningDropper is better understood as a multi-payload Android delivery framework than a simple miner dropper.
The same loader family can deliver radically different end payloads with only configuration and asset changes, which explains how the campaign can scale across a large number of samples while maintaining a consistent core architecture.
Conclusion
MiningDropper demonstrates a layered, modular Android malware architecture designed to make static analysis difficult while giving Threat Actors flexibility in final payload delivery.
The malware combines a native bootstrapper, memory-only string deobfuscation, filename-derived AES decryption, staged DEX loading, configuration-driven payload delivery, and split APK reconstruction to install either a cryptocurrency miner or a more capable user-defined payload such as BTMOB RAT.
This design allows the threat actor to reuse the same distribution and installation framework across hundreds of samples while adapting the final monetization objective to operational needs.
Our Recommendations
We have listed some essential cybersecurity best practices that serve as the first line of defense against attackers. We recommend that our readers follow the best practices given below:
- Install Apps Only from Trusted Sources:
Download apps exclusively from official platforms, such as the Google Play Store. Avoid third-party app stores or links received via SMS, social media, or email. - Be Cautious with Permissions and installs:
Never grant permissions and install an application unless you’re certain of an app’s legitimacy. - Watch for Phishing Pages:
Always verify the URL and avoid suspicious links and websites that ask for sensitive information. - Enable Multi-Factor Authentication (MFA):
Use MFA for banking and financial apps to add an extra layer of protection, even if credentials are compromised. - Report Suspicious Activity:
If you suspect you’ve been targeted or infected, report the incident to your bank and local authorities immediately. If necessary, reset your credentials and perform a factory reset. - Use Mobile Security Solutions:
Install a mobile security application that includes real-time scanning. - Keep Your Device Updated:
Ensure your Android OS and apps are updated regularly. Security patches often address vulnerabilities exploited by malware.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Procedure |
| Initial Access (TA0027) | Phishing (T1660) | MiningDropper is distributed via phishing sites |
| Execution (TA0041) | Native API (T1575) | Dropper used native code to decrypt payloads |
| Defense Evasion (TA0030) | Obfuscated Files or Information (T1406) | Dropper stores the encrypted payload in the assets |
| Defense Evasion (TA0030) | Virtualization/Sandbox Evasion (T1633) | Dropper implemented anti-emulation techniques |
| Discovery (TA0032) | System Information Discovery (T1426) | Dropper checks the device information to identify the running environment |
Indicators of Compromise (IOCs)
The IOCs have been added to this GitHub repository. Please review and integrate them into your Threat Intelligence feed to enhance protection and improve your overall security posture.
如有侵权请联系:admin#unsafe.sh
