We’ve uncovered multiple campaigns distributing an infostealer we track as NWHStealer, using everything from fake VPN downloads to hardware utilities and gaming mods. What makes this campaign stand out isn’t just the malware, but how widely and convincingly it’s being spread.
Once installed, it can collect browser data, saved passwords, and cryptocurrency wallet information, which attackers may use to access accounts, steal funds, or carry out further attacks.
We detected multiple campaigns using different platforms and lures to distribute NWHStealer. The stealer is loaded and executed in several ways, such as self-injection or injection into other processes like RegAsm (Microsoft’s Assembly Registration Tool). Often, additional wrappers such as MSI or Node.js are used as the initial loader.
The stealer is distributed using lures (what the file claims to be) such as:
- VPN installers
- Hardware utilities (e.g.
OhmGraphite,Pachtop,HardwareVisualizer,Sidebar Diagnostics) - Mining software
- Games, cheats, and mods (e.g.
Xeno)
It’s hosted or shared across multiple distribution channels, including:
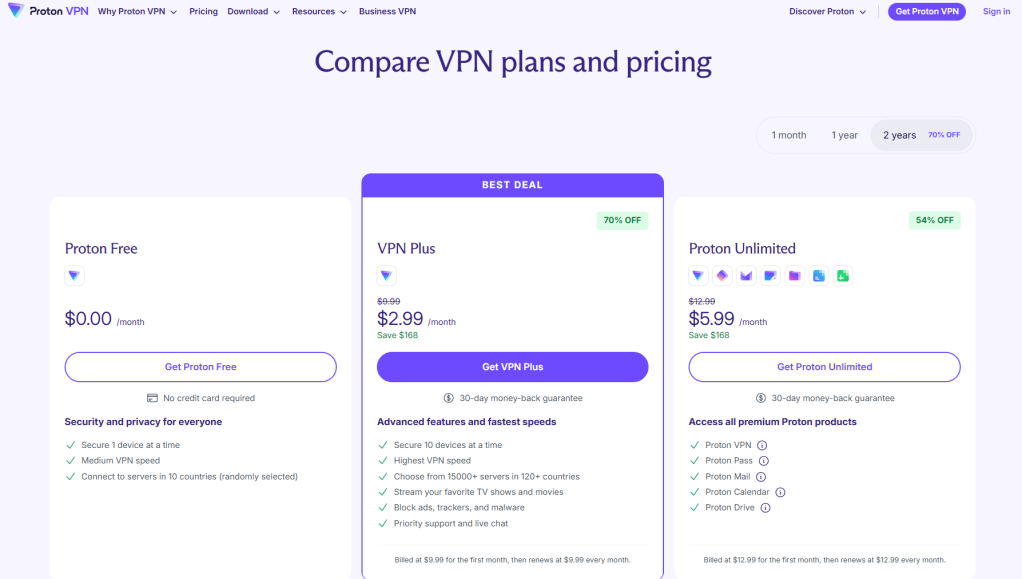
- Fake websites impersonating legitimate services, like Proton VPN
- Code hosting platforms like GitHub and GitLab
- File hosting services such as MediaFire and SourceForge
- Links and redirects from gaming- and security-related YouTube videos
Although there are many distribution methods, in this blog we look at two cases:
- Case 1: A free web hosting provider distributing a malicious ZIP file that loads the stealer using self-injection
- Case 2: Fake websites that load the stealer using DLL hijacking and injection into the RegAsm process
Case 1: Free web hosting provider distributes the stealer
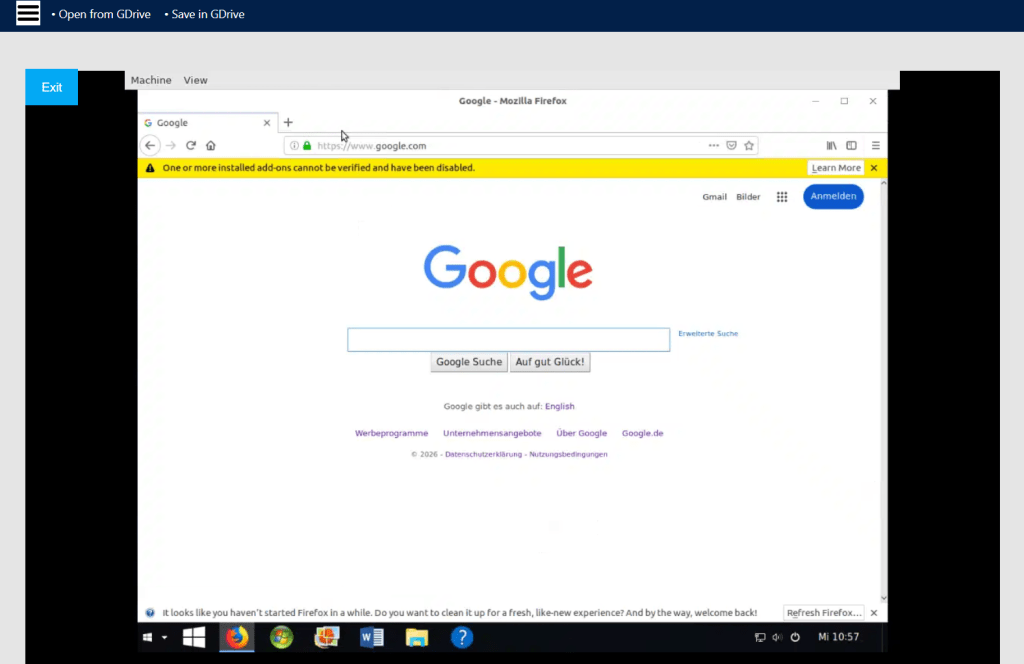
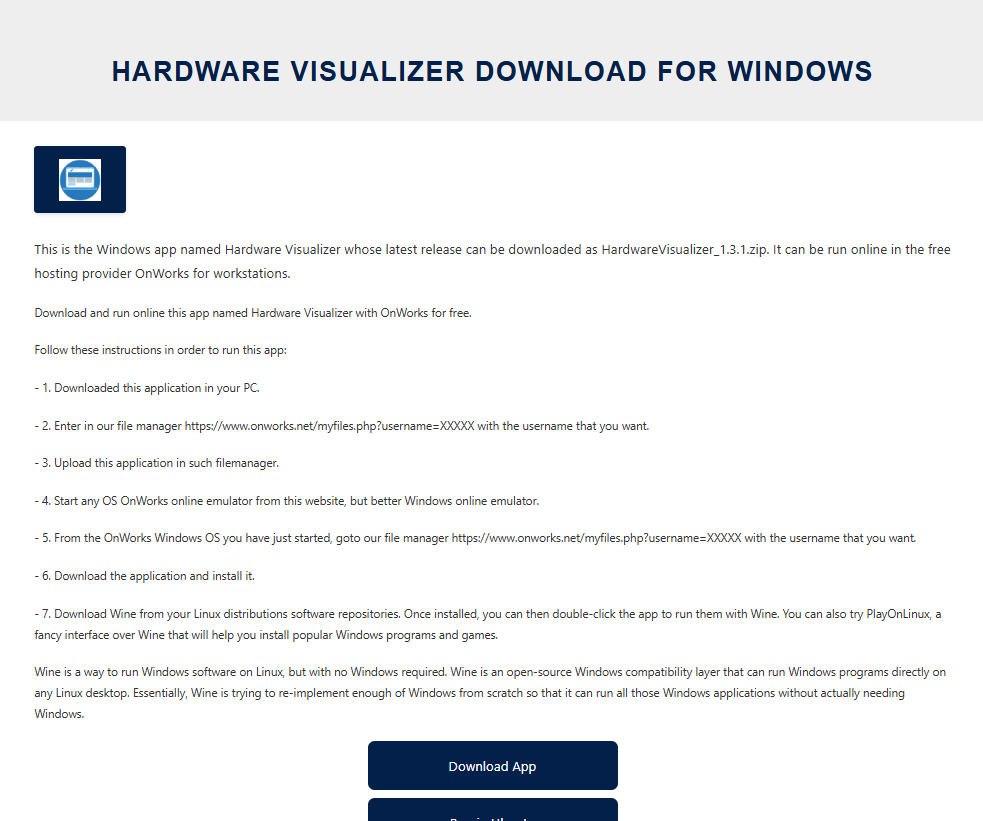
The first case is the most unexpected. We found that a free web hosting provider, onworks[.]net, hosts ZIP files in its download section that ultimately distribute the stealer.
The website, ranked in the top 100,000, allows users to run virtual machines entirely in the browser.
Through this site, users download a malicious ZIP with names like:
OhmGraphite-0.36.1.zipSidebar Diagnostics-3.6.5.zipPachtop_1.2.2.zipHardwareVisualizer_1.3.1.zip
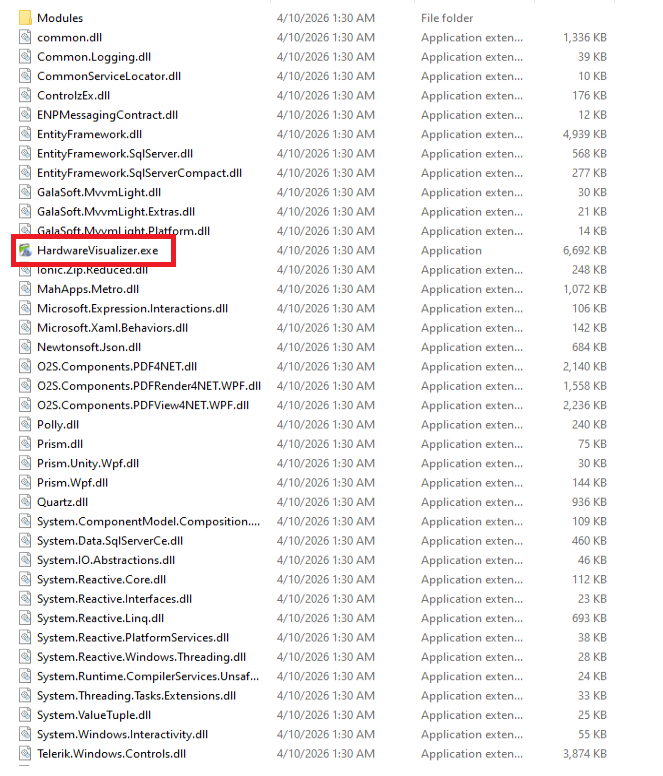
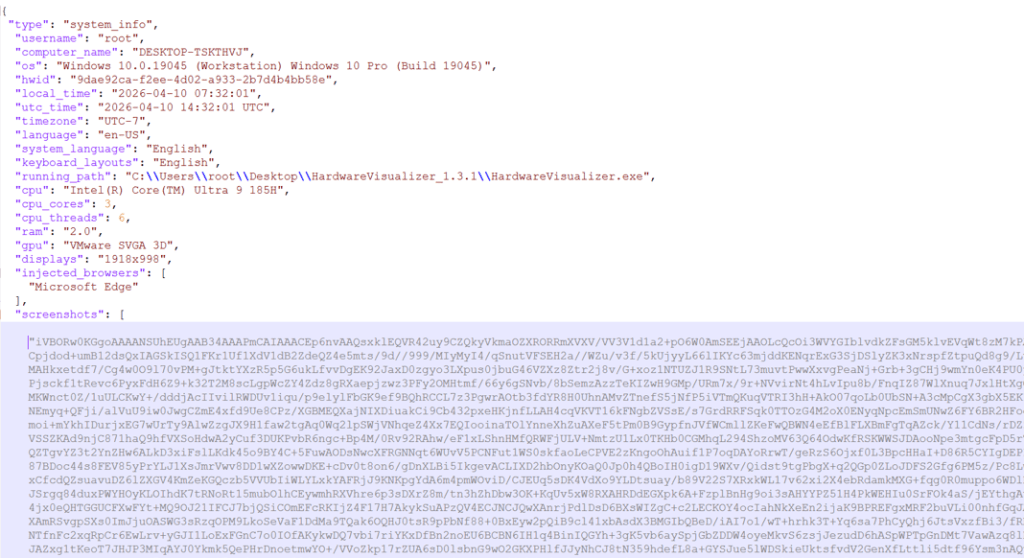
In this case, the malicious code responsible for loading the stealer is embedded in the executable, for example HardwareVisualizer.exe.
The loader contains junk code to make analysis more difficult and performs several operations, including:
- Checking the environment for analysis tools and terminating if detected
- Implementing a custom decryption function for strings
- Resolving functions using
LoadLibraryAandGetProcAddress - Decrypting and loading the next stage using AES-CBC via BCrypt APIs
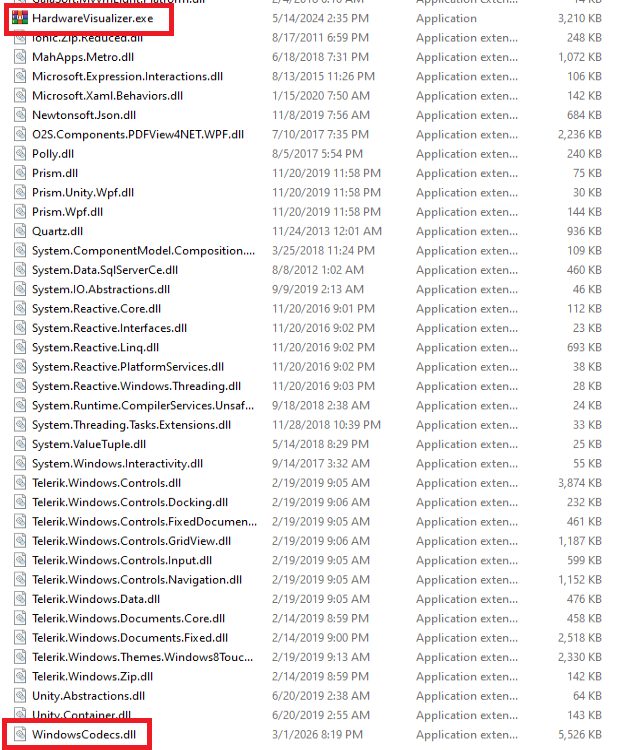
This isn’t the only way the stealer is distributed. We found similar lures, with the same ZIP names, that instead distribute the stealer via DLL hijacking.
In this case, HardwareVisualizer.exe is actually the WinRAR executable, and the malicious code resides in WindowsCodecs.dll.
While tracking the DLL loader, we also saw it distributed in other campaigns with different lures. For example, in the second case analyzed, this malicious DLL is delivered through fake websites.
Case 2: Fake Proton VPN website and DLL loader
In the second case, we detected a website impersonating Proton VPN that delivers a malicious ZIP. This archive executes the stealer using DLL hijacking or an MSI file. To be clear, this has no affiliation with Proton VPN, and we’ve contacted them to let them know what we found.
Links to the website appear in several compromised YouTube channels, along with AI-generated videos demonstrating the installation process:
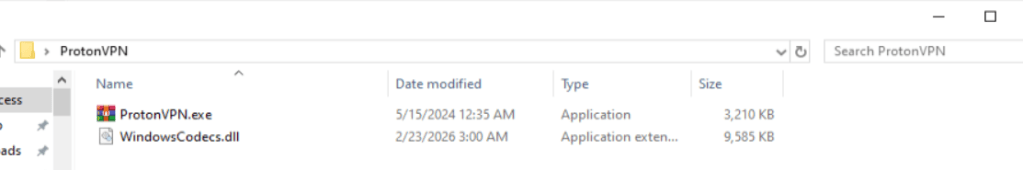
In other infection chains, this DLL appears under different names, such as:
iviewers.dllTextShaping.dllCrashRpt1403.dll
This DLL decrypts two embedded resources. The decryption method varies between samples: Some use custom AES implementations, while others rely on the OpenSSL library.
One of the decrypted resources is a second-stage DLL, runpeNew.dll, which is loaded and executed via the GetGet method.
The second-stage DLL starts a process (such as RegAsm) and performs process hollowing using low-level APIs, including:
NtProtectVirtualMemoryNtCreateUserProcessNtUnmapViewOfSectionNtAllocateVirtualMemoryNtResumeThread
The final payload: NWHStealer
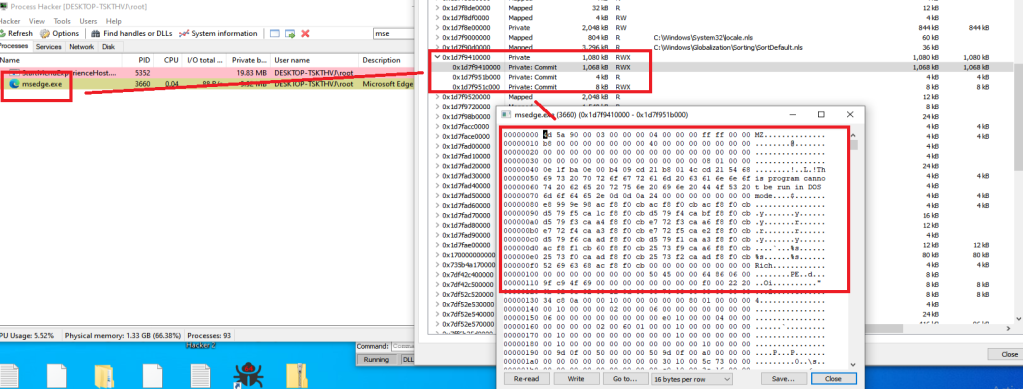
At the end of these infection chains, the attacker deploys NWHStealer. The stealer runs directly in memory or injects itself into other processes such as RegAsm.exe.
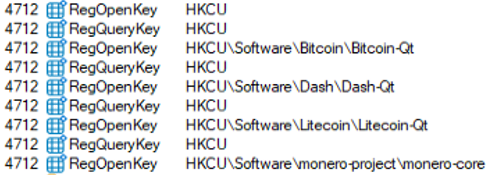
It enumerates more than 25 folders and registry keys associated with cryptocurrency wallets.
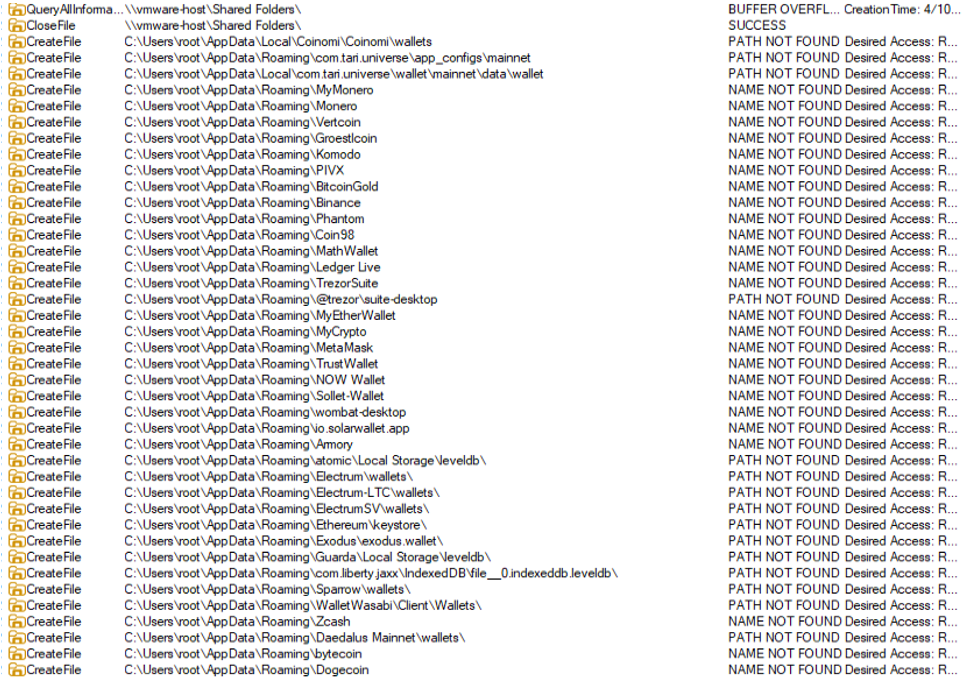
The stealer also collects and exfiltrates data from multiple browsers, including Edge, Chrome, Opera, 360 Browser, K-Melon, Brave, Chromium, and Chromodo.

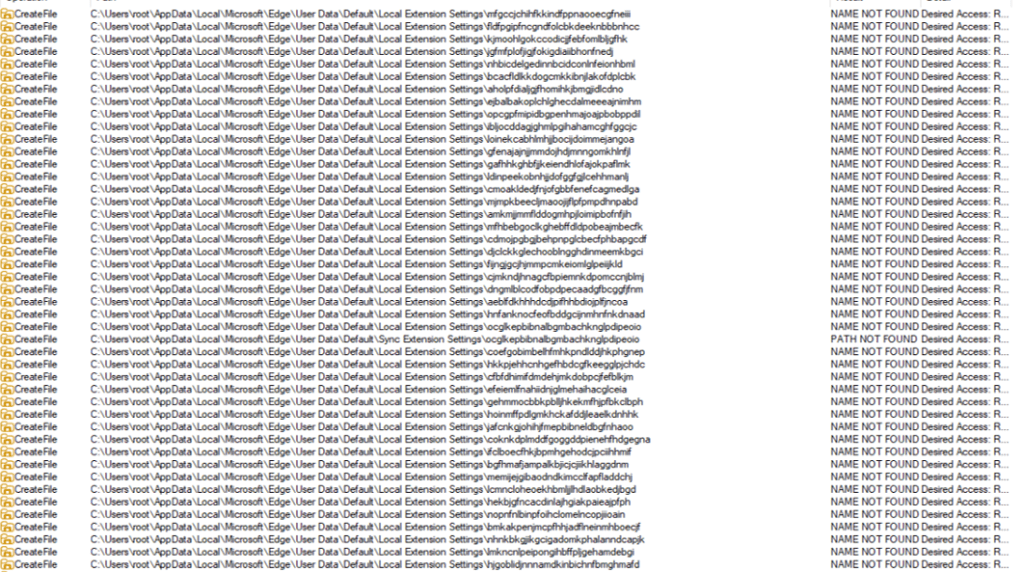
Additionally, it injects a DLL into browser processes such as msedge.exe, firefox.exe, or chrome.exe. This DLL extracts and decrypts browser data before sending it to the command-and-control (C2) server.
The injected DLL also executes a PowerShell command that:
- Creates hidden directories in
LOCALAPPDATA - Adds those directories to Windows Defender exclusions
- Forces a Group Policy update
- Encrypts a
getPayloadrequest and sends it to the C2 - Receives and executes additional payloads disguised as system processes (e.g.,
svchost.exe,RuntimeBroker.exe) - Creates scheduled tasks to run the payload at user logon with elevated privileges
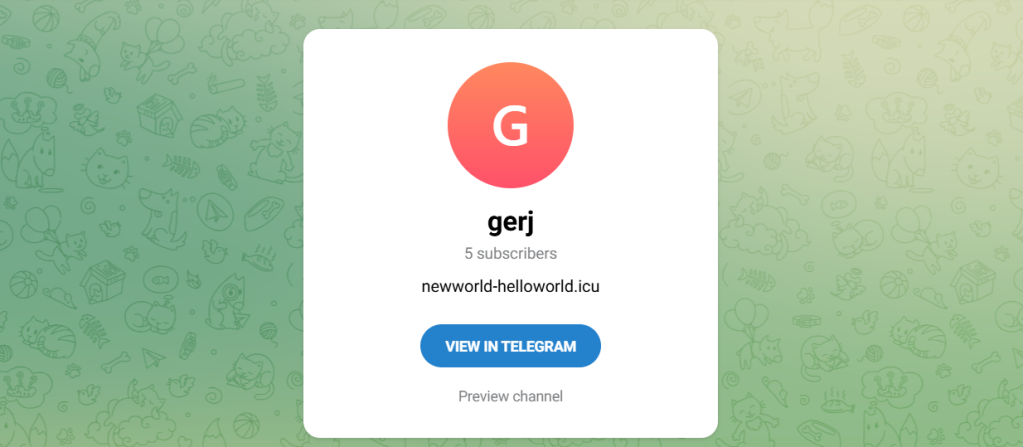
Data sent to the C2 is encrypted using AES-CBC. If the primary server is unavailable, the malware can retrieve a new C2 domain via a Telegram-based dead drop.
The stealer also uses a known CMSTP User Account Control (UAC) bypass technique to execute PowerShell commands:
- Generates a random
.inffile in the temp folder - Uses
cmstp.exeto elevate privileges - Automatically confirms the prompt using Windows APIs
How to stay safe
Instead of relying on phishing emails or obvious scams, the attackers behind this campaign are hiding malware inside tools people actively search for and trust. By spreading through platforms like GitHub, SourceForge, and YouTube, they increase the chances that users will let their guard down.
Once installed, the impact can be serious. Stolen browser data, saved passwords, and cryptocurrency wallet information can lead to account takeovers, financial loss, and further compromise.
Here are our tips for avoiding being caught out:
- Download software only from official websites
- Be cautious with downloads from GitHub, SourceForge, or file-sharing platforms unless you trust the source
- Check file signatures and publisher details before running anything
- Avoid downloading tools from links in YouTube descriptions
- Pro tip: Install Malwarebytes Browser Guard on your browser to block malicious URLs.
Indicators of Compromise (IOCs)
Check the signature and version of software in suspicious archives.
Hashes
e97cb6cbcf2583fe4d8dcabd70d3f67f6cc977fc9a8cbb42f8a2284efe24a1e3
2494709b8a2646640b08b1d5d75b6bfb3167540ed4acdb55ded050f6df9c53b3
Domains
vpn-proton-setup[.]com (fake website)
get-proton-vpn[.]com (fake website)
newworld-helloworld[.]icu (C2 domain)
https://t[.]me/gerj_threuh (Telegram dead drop)
URLS
https://www.onworks[.]net/software/windows/app-hardware-visualizer
https://sourceforge[.]net/projects/sidebar-diagnostics/files/Sidebar%20Diagnostics-3.6.5.zip
https://github[.]com/PieceHydromancer/Lossless-Scaling-v3.22-Windows-Edition/releases/download/Fps/Lossless.Scaling.v3.22.zip
This is only a partial list of malicious URLs. Download the Malwarebytes Browser Guard plugin for full protection and to block the remaining malicious URLs.
