If there is anything that annoys me more than a scammer, it’s companies that behave like one, while staying just on the right side of the law. They manage to linger and disappoint customers for years.
It’s also why sometimes people think that Malwarebytes Scam Guard can be overly cautious when flagging websites. Some sites sit in a grey area where even seasoned researchers have to look twice to figure out whether something is an outright scam.
That’s exactly what happened here.
After receiving an anonymized report from a customer, I started an investigation into an email Scam Guard flagged as highly suspicious.
The email
The email came from the address anna@cosmosshift[.]org and promoted a service called Credit Resources Vault, urging recipients to click a button labelled Check Eligibility Now..
There are immediate red flags:
- The sender domain (
cosmosshift.org) has no clear connection to credit services or financial products. There is no “Cosmos Shift” financial institution. - The message creates urgency around credit approval, a classic social engineering pressure tactic.
- It includes a physical address and an opt-out link which appear to be legitimate, but are also a common technique in phishing called legitimacy laundering.
Unlike most phishing emails, this one includes a personalized greeting using the recipient’s email address. Since the recipient says they’ve never interacted with the sender, this suggests their details may have come from a data broker or a past data breach.
The website paints a suspicious picture
Clicking the link leads to (yourcreditvault.com), a polished-looking site that appears to offer credit services.
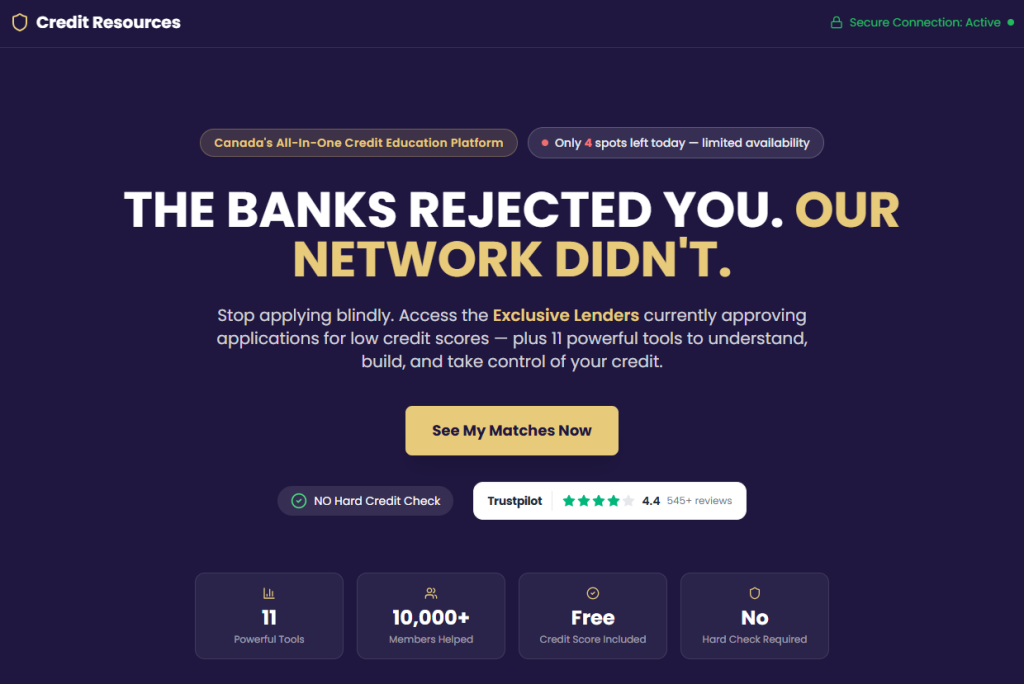
But under the hood we found more red flags:
- The website was built with Vite/React, a modern JavaScript framework more typical of startup side projects than regulated financial services.
- References to bolt.new suggest the site may have been assembled using AI tools
- There are no visible indicators of banking-grade security. The HTML source shows only a basic app shell with no indicators of financial-sector encryption infrastructure.
- The branding (including the logo) looks hastily put together
- The JavaScript bundle (
index-B54Ghi53.js) behind the submission form is heavily obfuscated: a technique used by cybercriminals to hide where the submitted data is being sent.
None of this proves malicious intent on its own. But together, it paints a picture of something built quickly, and designed to collect data rather than deliver a robust financial service.
The form collects data, and $20/week
The biggest concern is the form, which collects an extraordinary amount of data for what’s presented as a basic credit eligibility check.
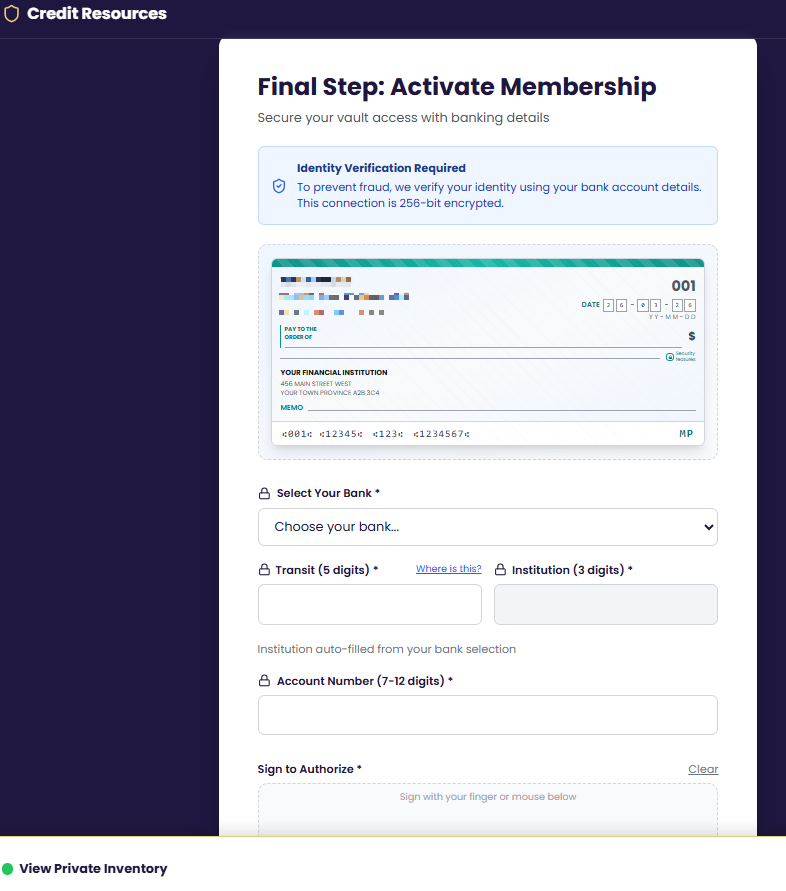
By monitoring network traffic during form submission, we were able to capture exactly what fields are transmitted:
- Personal: first name, last name, email, phone
- Address: street, city, province, postal code
- Full banking details: bank name, institution number, transit number, account number
- Tracking data tied to advertising campaigns
- A drawn-on-screen signature, which gets uploaded to the owner’s Google Drive.
See if your personal data has been exposed.
That’s far more than what’s needed for a credit eligibility check.
With those banking details alone, someone can set up fraudulent Pre-Authorized Debits (PADs). A PAD is a form of direct bank withdrawal used legitimately by billers, but can also be abused.

And that’s exactly what appears to happen.
A small checkbox, paired with fine print, authorizes the company to withdraw $20 weekly per the PAD agreement the target just signed. This checkbox serves two purposes: it provides the operators with legal cover (“you agreed to it!”) and it weaponizes the very bank account details the form just collected.
Targeting the financially vulnerable
This campaign seems to deliberately target people with poor or limited credit history. The promise of “approval when others say no” is powerful, especially for people under financial pressure.
These are not random victims, but people targeted because their need makes them more likely to hand over sensitive information without scrutinizing the source.
The $20/week PAD charge (over $1,000 per year) can lead to overdrafts, fees, and further financial harm.
Where your data goes
Our network traffic analysis revealed a sophisticated, multi-service backend that uses individual components which all might be legitimate.
Supabase: Victim data is sent via POST request to a Supabase project:
POST https://bstvkdzfgpktokbiagsc.supabase.co/rest/v1/vault_memberships
Supabase is a legitimate, well-regarded cloud database platform with free tiers.
Brevo (formerly Sendinblue): This is a legitimate mass-email platform. Enrolling victims here means they can be targeted with follow-up campaigns indefinitely.
POST https://bstvkdzfgpktokbiagsc.supabase.co/functions/v1/add-to-brevo
Google Drive and Sheets: The signature data field includes a signature_drive_url, indicating victims’ handwritten signatures might get stored on Google Drive infrastructure. A google_sheets_synced field confirms that incoming victim records are mirrored to a live Google Sheet, giving the operators a real-time dashboard of everyone that submitted a form.
Individually, these are trusted platforms. Together, they form a system designed to:
- Collect sensitive personal and banking data
- Store it in accessible formats
- Add users to ongoing marketing or even phishing campaigns
In other words, submitting the form doesn’t just risk your bank account, but may also put you on a list of people likely to be targeted again.
Infrastructure
The infrastructure behind this campaign spans multiple domains:
cosmosshift[.]org(email sender)yourcreditvault[.]com(landing page).-
yourscore[.]ca(redirect after submitting the form) creditresources[.]ca(follow-up email that included the phone number 1-833-427-1562)debtlesscredit[.]com(another website using that same phone number)
Using multiple domains and having one telephone number associated with more than one domain raising red flags about the legitimacy of the company.
So is this a scam?
That depends on how you define it.
While this may not meet the strict legal definition of a scam, we can see why Scam Guard flagged it, as many of the tactics used here are also seen in phishing emails and on scam websites.
The evidence suggests these sites are operated by real companies, but they sit firmly in a grey area. On one hand, they have corporate registrations, public websites, and apparently even some satisfied customers. On the other, the business model—charging recurring fees for credit or debt “programs”—has generated a steady stream of consumer complaints and scam accusations. The use of multiple domains (Credit Resources, Debtless Credit, Your Credit Vault) also points to a lead-generation strategy that’s common in the debt-relief space.
It’s also likely that these companies rely on purchased mailing lists and may have found our customer’s email address on a list of likely candidates. Unfortunately, lists like these are bought and sold by legitimate marketers and cybercriminals alike.
We have reached out to the sender of the email and Credit Resources for comment but had not received an answer at the time of publication.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
