嗯,用户让我用中文总结这篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要通读整篇文章,抓住主要信息。 文章讲的是NightSpire勒索软件集团,他们在2025年初出现,最初是封闭运作的,后来转向RaaS模式。主要攻击中小企业,使用Go语言编写恶意软件,加密文件并使用双重勒索策略。攻击链包括钓鱼、利用漏洞、横向移动等。AttackIQ还推出了模拟工具帮助防御。 现在要总结这些内容,控制在100字左右。要简洁明了,涵盖主要点:NightSpire的出现时间、运营模式转变、目标、技术手段、双重勒索和模拟工具。 可能的结构:NightSpire是2025年出现的勒索软件集团,最初封闭运作,后转向RaaS。攻击中小企业,使用Go语言加密文件并双重勒索。AttackIQ提供模拟工具帮助防御。 检查字数是否合适,并确保涵盖所有关键点。 </think> NightSpire 是一个于 2025 年初出现的勒索软件团伙,最初以封闭模式运营,并通过双重勒索策略实施攻击。该团伙主要针对中小企业和跨行业机构,利用 Go 语言编写的恶意软件加密文件并索取赎金。其攻击链包括钓鱼、漏洞利用和横向移动等步骤,并通过专用泄密网站施压受害者。NightSpire 近期转向 RaaS 模式扩展业务。安全公司 AttackIQ 提供模拟工具帮助防御此类威胁。 2026-4-14 15:41:31 Author: securityboulevard.com(查看原文) 阅读量:3 收藏
Overview
NightSpire is a financially motivated ransomware and data extortion group that emerged in early 2025. Initially operating as a closed, self-managed group, it conducted intrusions end-to-end without a public affiliate structure, leveraging double extortion through a dedicated leak site (DLS). The group has since announced the launch of a ransomware-as-a-service (RaaS) program, signaling a shift toward an affiliate-based model to scale operations.
The group primarily targets small- to medium-sized organizations with less mature security controls, with victims spanning multiple sectors, including manufacturing, technology, healthcare, financial services, and government across more than 30 countries.
The ransomware payload, written in Go (Golang), encrypts files and appends the “.nspire” extension while dropping a ransom note with payment instructions. Initial access is typically achieved via phishing or exploitation of exposed services, including observed abuse of CVE-2024-55591 in FortiOS firewall appliances. Following compromise, NightSpire follows a structured attack chain that relies heavily on living-off-the-land techniques such as PowerShell, WMI, and PsExec for lateral movement, alongside credential dumping utilities like Mimikatz.
With the transition to a RaaS model, these techniques are expected to vary depending on the affiliate, likely expanding the range of initial access vectors, tooling, and operational patterns observed across intrusions.
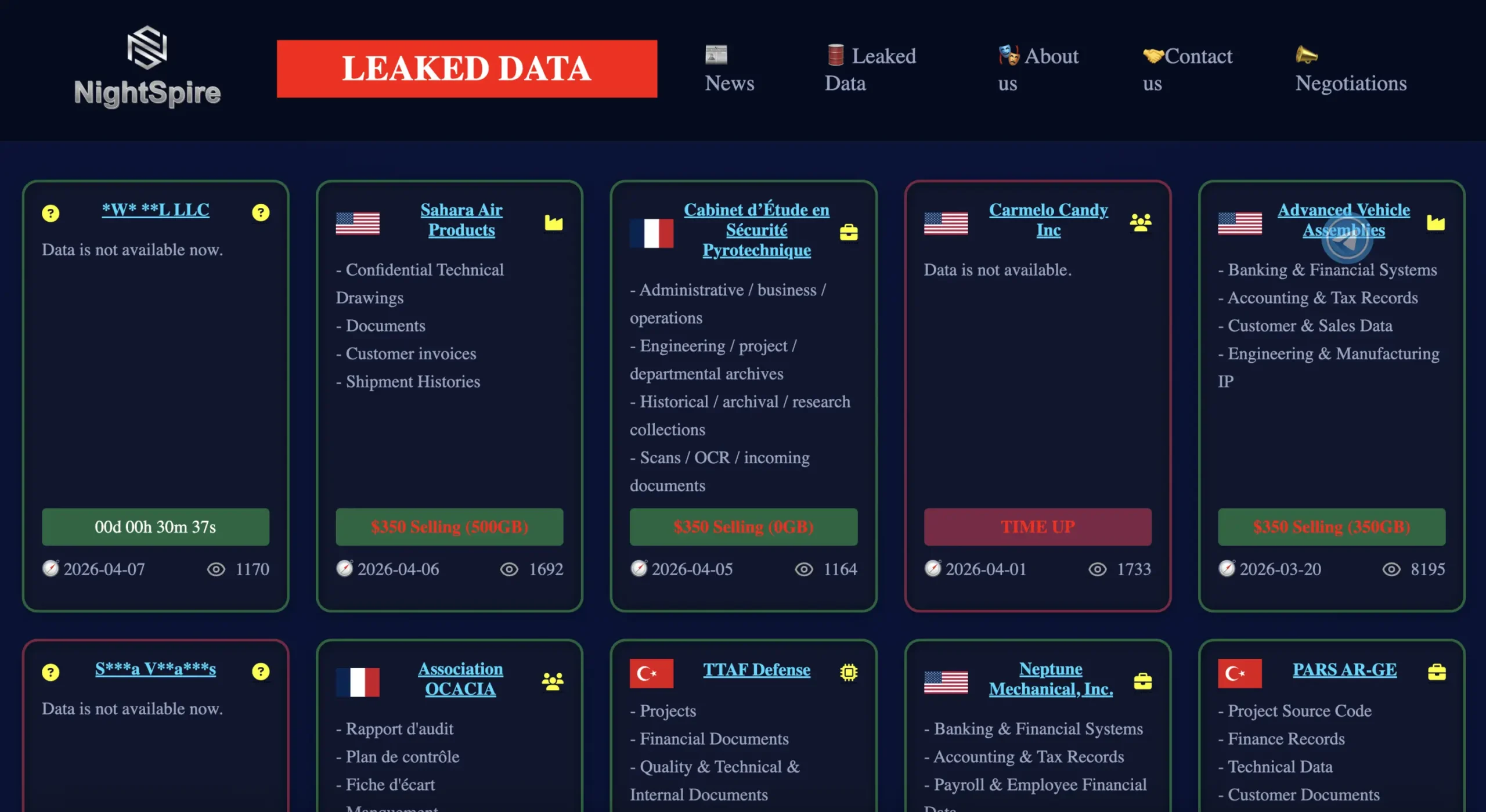
Dedicated Leak Site (DLS)
NightSpire operates a dedicated leak site (DLS) as part of its double extortion strategy. The platform is used to advertise and sell data stolen from victims who refuse to comply with ransom demands, increasing pressure by exposing sensitive information.
Entries typically include structured metadata such as the victim name, country, estimated data volume, publication date, view count, and the price assigned to the dataset. Newly listed victims initially appear with redacted names accompanied by a countdown timer, indicating the time remaining before their data is fully disclosed or made available for purchase. In some cases, limited data samples are released to demonstrate proof of compromise.
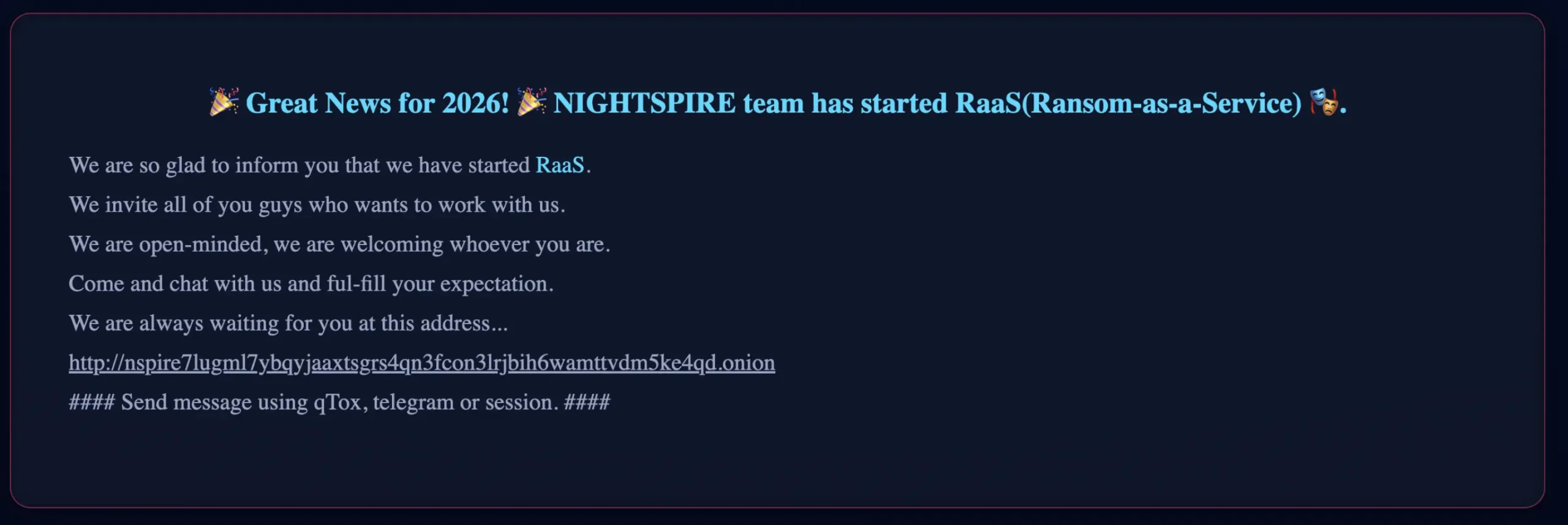
RaaS Program Announcement
NightSpire has recently announced the launch of a ransomware-as-a-service (RaaS) program, signaling a transition from a closed, operator-driven model to an affiliate-based structure. This shift enables external actors to leverage NightSpire’s ransomware tooling and infrastructure, likely increasing the scale and variability of operations while introducing a broader range of tactics, techniques, and procedures (TTPs) across intrusions.
Encryption and Ransom Notes
NightSpire employs a hybrid encryption approach designed to balance speed and impact:
- Block Encryption: Large and high-value files (e.g., .iso, .vhdx, .zip, .bak, .mdf) are partially encrypted by targeting specific segments (typically ~1 MB blocks). This technique accelerates the encryption process while still rendering files unusable.
- Full Encryption: Smaller files, such as documents and images, are fully encrypted, significantly reducing the likelihood of recovery without access to the decryption key.
This partial encryption approach allows NightSpire to significantly reduce encryption time while maintaining operational impact. The “.nspire” extension is appended to each encrypted file.
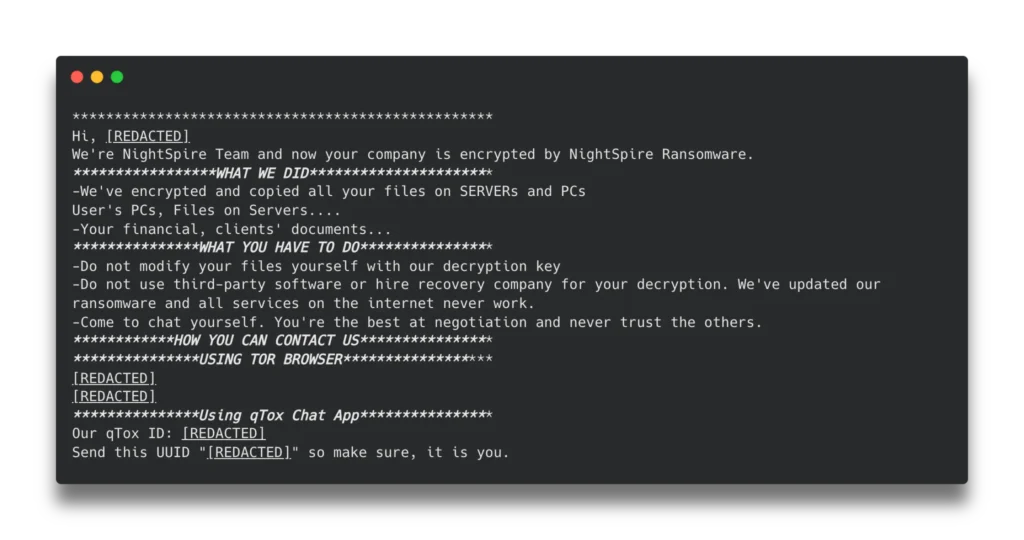
Then, Nightspire drops a ransom note containing a unique victim identifier (UUID) and, in some cases, a password, along with instructions and contact channels for negotiation. The use of system-specific artifacts (e.g., MachineGUID) combined with unique identifiers embedded in ransom notes indicates that NightSpire generates victim-specific payloads and tailored negotiation parameters, likely through build-time configuration. The two ransom note examples below illustrate the significant differences between them:
File Hash (SHA-256):
c5f526cc62688cf34c49d098dab81e24e4294f832ada57433ef505d5ac6da8f3
Ransom Note:
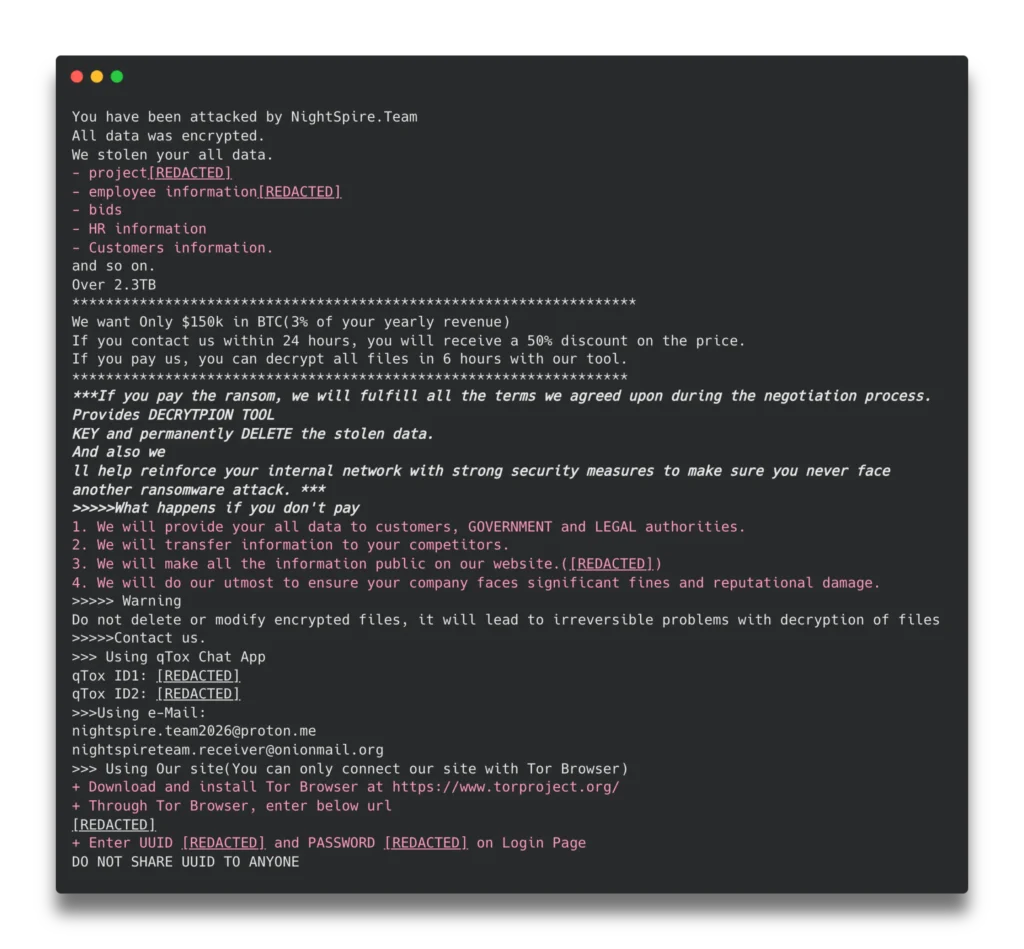
File Hash (SHA-256):
8f58870a3e5df1d904940c7ef2ad160b90ba739c7e5e21e4c908945e0a6f3f60
Ransom Note:
AttackIQ’s Nightspire Emulation
AttackIQ has released a new attack graph that emulates the Tactics, Techniques, and Procedures (TTPs) associated with the deployment of NightSpire Ransomware to help customers validate their security controls and their ability to defend against this threat.
[Malware Emulation] NightSpire Ransomware – 2026-01 – Associated Tactics, Techniques and Procedures (TTPs)

This emulation replicates the sequence of behaviors associated with the deployment of NightSpire ransomware on a compromised system with the intent of providing customers with the opportunity to detect and/or prevent a compromise in progress.
This emulation is based entirely on internal analysis of the samples.
Initial Access & Discovery – NightSpire Ransomware Deployment
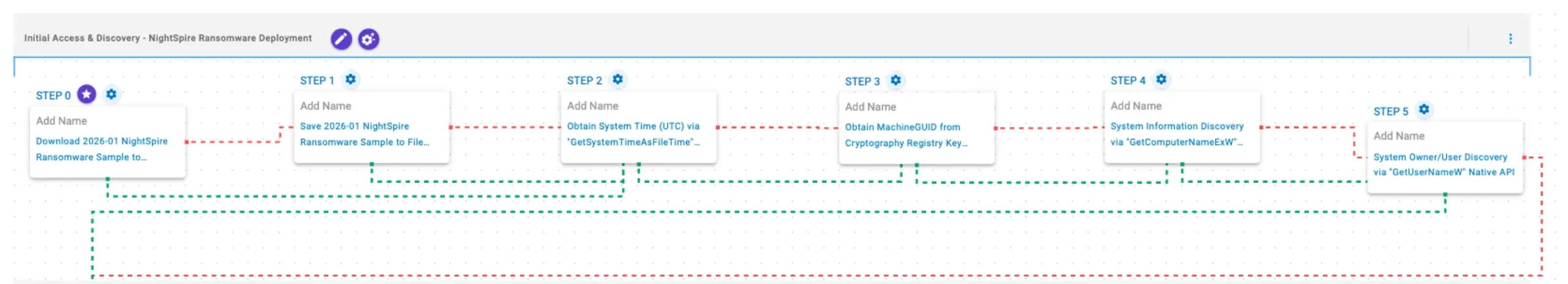
This stage begins with the deployment of NightSpire ransomware, initiating early system profiling to uniquely identify the infected host. It first retrieves the current system time using GetSystemTimeAsFileTime and obtains the system’s MachineGUID from the registry to establish a unique victim identifier. NightSpire then gathers additional host context by querying the computer name via GetComputerNameExW and the logged-in user information using GetUserNameExW, building a baseline profile of the compromised system prior to further execution stages.
Download and Save Scenarios (T1105): The Nightspire Ransomware Sample (SHA256: c5f526cc62688cf34c49d098dab81e24e4294f832ada57433ef505d5ac6da8f3) is first downloaded and then saved to disk in two separate scenarios to test network and endpoint controls and their ability to prevent the delivery of known malicious samples.
Obtain System Time (UTC) via “GetSystemTimeAsFileTime” Windows API (T1124): This scenario simulates checking system time using the GetSystemTimeAsFileTime Windows API, which returns the current UTC time.
Obtain MachineGUID from Cryptography Registry Key using “reg query” Command (T1012): This scenario executes the reg query command to obtain information from the registry. It targets the MachineGUID entry within the HKLM\SOFTWARE\Microsoft\Cryptography registry key which contains a unique identifier of the system.
System Information Discovery via “GetComputerNameExW” Native API (T1082): This scenario executes the GetComputerNameExW Windows native API call to retrieve a NetBIOS or DNS name associated with the local computer.
System Owner/User Discovery via “GetUserNameW” Native API (T1033): This scenario executes the GetUserNameW Windows native API call to retrieve the account name associated with the local computer.
Discovery – System Reconnaissance
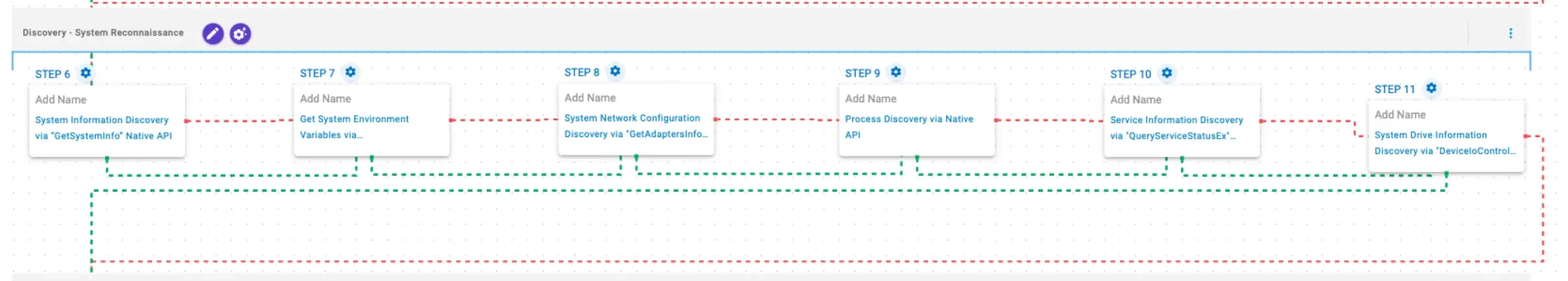
In this stage, NightSpire expands system reconnaissance by gathering detailed host and environment information using GetSystemInfo and GetEnvironmentStrings. It also retrieves network adapter details via GetAdaptersInfo to understand available interfaces and connectivity. The malware then performs process discovery to enumerate running processes, followed by service enumeration using QueryServiceStatusEx to identify active services. Finally, NightSpire uses DeviceIOControl to obtain system drive information.
System Information Discovery via “GetSystemInfo” Native API (T1082): This scenario executes the GetSystemInfo Windows native API call to retrieve system information. This can be used to detect sandboxes, create unique identifiers, and adjust execution behaviors.
Get System Environment Variables via “GetEnvironmentStrings” Native API (T1082): This scenario executes the GetEnvironmentStrings Windows native API call to discover environmental variables, usually used to fingerprint the system or search for stored passwords and secrets.
System Network Configuration Discovery via “GetAdaptersInfo” Native API (T1016): This scenario executes GetAdaptersInfo Windows native API call to retrieve adapter information from the local computer.
Process Discovery via Native API (T1057): This scenario executes the CreateToolhelp32SnapshotWindows native API call to receive a list of running processes and iterates through each process object with Process32FirstW and Process32NextW.
Service Information Discovery via “QueryServiceStatusEx” Native API (T1007): This scenario executes the QueryServiceStatusEx and EnumDependentServices Windows API calls to retrieve information corresponding to a given service.
System Drive Information Discovery via “DeviceIoControl” Native API (T1082): This scenario executes the DeviceIoControl Native API function to retrieve system drive information, such as the serial number, to profile the target’s system.
Impact – NightSpire File Encryption
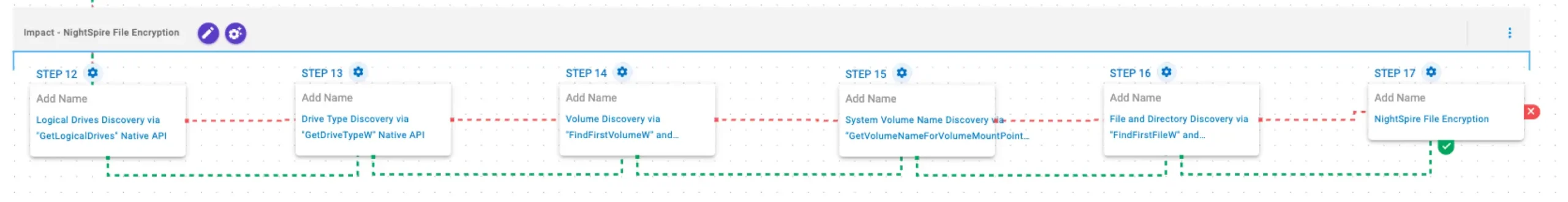
In this stage, NightSpire identifies and prioritizes storage targets by enumerating available drives using GetLogicalDrives and determining their types via GetDriveTypeW. It further enumerates volumes using FindFirstVolumeW and FindNextVolumeW, and retrieves volume names with GetVolumeNameForVolumeMountPoint to map accessible storage locations. The malware then traverses the file system using FindFirstFileW and FindNextFileW to identify files for encryption. Finally, NightSpire encrypts files using AES-256 in CBC mode and RSA-2048 to protect encryption keys.
Logical Drives Discovery via “GetLogicalDrives” Native API (T1082): This scenario executes the GetLogicalDrives Windows API call to retrieve the currently available disk drives.
Drive Type Discovery via “GetDriveTypeW” Native API (T1120): This scenario retrieves information about the system’s physical disks using the GetDriveTypeW Windows API call.
Volume Discovery via “FindFirstVolumeW” and “FindNextVolumeW” Native API (T1082): This scenario executes the FindFirstVolumeW and FindNextVolumeW Windows API calls to iterate through the available volumes of the system.
System Volume Name Discovery via “GetVolumeNameForVolumeMountPointA” Native API (T1082): This scenario calls the GetVolumeNameForVolumeMountPointA Windows API function for each drive letter to retrieve the volume GUID path.
File and Directory Discovery via “FindFirstFileW” and “FindNextFileW” Native API (T1083): This scenario executes the FindFirstFileW and FindNextFileW Windows native API calls to enumerate the file system.
NightSpire File Encryption (T1486): This scenario performs the file encryption routines used by common ransomware families. Files matching an extension list are identified and encrypted in place using similar encryption algorithms as used by NightSpire ransomware.
Validating your security program performance against these behaviors is vital in reducing risk. By using this new emulation in the AttackIQ Adversarial Exposure Validation (AEV) Platform, security teams will be able to:
- Evaluate security control performance against baseline behaviors associated with the NightSpire ransomware.
- Assess their security posture against an opportunistic adversary, which does not discriminate when it comes to selecting its targets.
- Continuously validate detection and prevention pipelines against a playbook similar to those of many of the groups currently focused on ransomware activities.
Opportunities to Expand Emulation Capabilities
In addition to the released assessment template, AttackIQ recommends the following existing scenarios for emulating the capabilities identified by Halcyon.
Dump Windows Passwords with Obfuscated Mimikatz (T1003): This scenario utilizes an obfuscated version of Mimikatz to dump passwords and hashes for Windows accounts.
Lateral Movement Through PAExec (T1021.002): This scenario simulates lateral movement within a network using PAExec, an open-source version of PSExec.
Lateral Movement Through WMI (T1047): This scenario attempts to move laterally to any available asset inside the network through the use of WMI. If the remote asset can be accessed, a configurable command is executed.
Wrap-up
In summary, this emulation will evaluate security and incident response processes and support the improvement of your security control posture against the behaviors exhibited by NightSpire ransomware. With data generated from continuous testing and use of this assessment template, you can focus your teams on achieving key security outcomes, adjust your security controls, and work to elevate your total security program effectiveness against a known and dangerous threat.
AttackIQ is the industry’s leading Continuous Threat Exposure Management (CTEM) platform, enabling organizations to measure true exposure, prioritize risk, and disrupt real-world attack paths. By moving beyond static vulnerability data, AttackIQ operationalizes CTEM by continuously validating exposures against real adversary behavior and defensive controls. The platform connects vulnerabilities, configurations, identities, and detections into adversary-validated attack paths—quantifying the likelihood of attacker movement and impact. This evidence-based approach empowers security leaders to focus on what matters most, optimize defensive investments, and strengthen resilience through threat-informed, AI-driven security operations.
The company is committed to supporting its MSSP partners with a Flexible Preactive Partner Program that provides turn-key solutions, empowering them to elevate client security. AttackIQ is passionate about giving back to the cybersecurity community through its free, award-winning AttackIQ Academy and founding research partnership with MITRE Center for Threat-Informed Defense.
如有侵权请联系:admin#unsafe.sh