好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。用户给的文章是关于ShinyHunters黑客组织入侵Rockstar Games的事件。首先,我得通读整篇文章,抓住主要信息。 文章提到ShinyHunters泄露了8.1GB的数据,包括反作弊代码、玩家分析、游戏资产等。数据是通过Anodot获取的,Rockstar Games则淡化了事件的影响,称只有少量非敏感信息被访问。此外,ShinyHunters通常通过第三方云环境进行攻击,而不是直接攻击公司内部系统。 接下来,我需要将这些信息浓缩成一个简洁的总结。要确保涵盖主要事件:数据泄露、涉及的内容、Rockstar的回应以及ShinyHunters的策略。 然后,我要注意字数限制在100字以内,并且不要使用“文章内容总结”之类的开头。直接描述事件即可。 最后,检查是否有遗漏的重要信息,并确保语言简洁明了。 </think> ShinyHunters声称入侵Rockstar Games并通过Anodot泄露8.1GB数据,包括反作弊代码、玩家分析、游戏资产及财务信息。Rockstar淡化影响称仅有限非敏感信息被访问。ShinyHunters利用第三方云环境进行攻击。 2026-4-14 11:1:56 Author: securityaffairs.com(查看原文) 阅读量:22 收藏
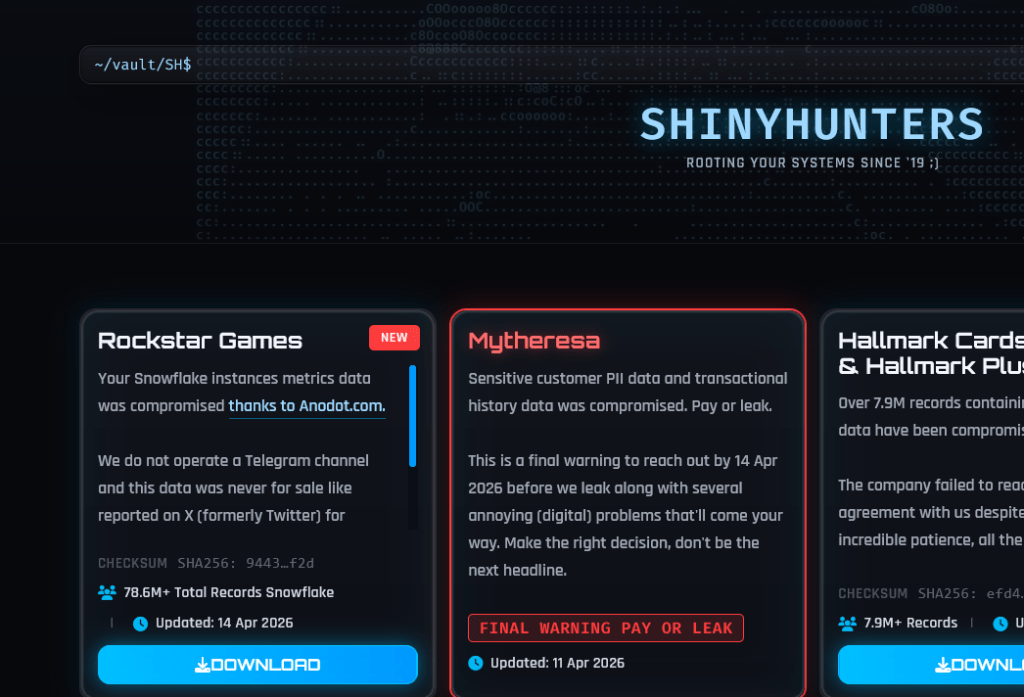
ShinyHunters claim the hack of Rockstar Games breach and started leaking data

Leak of 8.1GB data tied to Rockstar Games includes anti-cheat code, game data, analytics and more, reportedly exposed by ShinyHunters.
An 8.1GB data leak reportedly linked to Rockstar Games has surfaced, with files shared by ShinyHunters after being obtained via Anodot. The dataset includes anti-cheat source code, player analytics, game assets, Zendesk support tickets and financial information.
— International Cyber Digest (@IntCyberDigest) April 13, 2026🚨 BREAKING: Rockstar Games breach data obtained through Anodot has been leaked by ShinyHunters.
The files total 8.1GB and contain anti-cheat source code, player analytics, game data, Zendesk ticket feeds, financial data and more.
A thread analyzing what has been leaked… 🧵 pic.twitter.com/qi8cOXJOnL
Rockstar Games, one of the major companies in the video game industry, known for popular titles like Grand Theft Auto.
The cybercrime group claims they managed to access Rockstar-related systems hosted through a third-party cloud provider. The group alleges that sensitive internal data was exfiltrated and threatened to publish it.
The group attempted to pressure the company with public posts suggesting that failure to comply would result in both data leaks and further “digital disruption.”
Rockstar Games, however, has publicly minimized the impact of the incident. In its statement, the company indicated that only a limited amount of non-sensitive corporate information was accessed and emphasized that neither its operations nor its player community were affected.
“We can confirm that a limited amount of non-material company information was accessed in connection with a third-party data breach,” a Rockstar Games spokesperson told BBC.
The firm’s response suggests that, at least from its perspective, the breach did not compromise core systems or player-facing services.
Security researchers note that groups like ShinyHunters have increasingly focused on exploiting third-party cloud environments rather than directly attacking corporate infrastructure. This approach allows attackers to bypass stronger internal defenses by targeting external service providers with weaker security postures or misconfigurations.
The incident marks the second major security event involving the company in just a few years, highlighting how high-profile gaming studios remain attractive targets for data theft and extortion schemes.
In a previous incident in 2022–2023, a hacker affiliated with the Lapsus$ collective gained access to internal systems and leaked early development footage of Grand Theft Auto VI. That breach resulted in significant operational disruption and forced the company to adjust its communication strategy around one of its most secretive projects.
The financial and reputational implications of such incidents are substantial. Beyond direct recovery costs, companies often face delays in development, increased security investments, and intensified scrutiny from both regulators and the public. In the case of Rockstar, the stakes are even higher due to the secrecy surrounding upcoming releases and the enormous expectations tied to its flagship titles.
As investigations continue, the Rockstar breach serves as another reminder of the evolving threat landscape facing major digital entertainment companies. In an era where cloud infrastructure, third-party vendors, and remote access systems are deeply integrated into business operations, securing the full supply chain has become as critical as protecting internal networks.
ShinyHunters is a well-known name in the cybercriminal ecosystem. The group is associated with a broader loosely connected network often referred to as “the Com,” made up largely of young, English-speaking individuals. Their operations typically focus on stealing data from large organizations and using leak sites to pressure victims into paying ransoms in cryptocurrency.
ShinyHunters has recently targeted major companies and organizations, leaking data when ransom demands fail. Victims include the European Commission, Odido, Figure, Canada Goose, and SoundCloud. The group primarily uses social engineering, especially voice phishing, to steal credentials and access SaaS platforms like Salesforce, Okta, and Microsoft 365.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Rockstar Games)
如有侵权请联系:admin#unsafe.sh
