嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读这篇文章,了解它的主要内容。 文章主要讨论了制药行业在遭受网络攻击时面临的挑战,特别是计算机系统验证(CSV)的重要性。CSV确保系统按设计运行,符合法规要求。网络攻击可能导致数据完整性受损,进而影响产品质量和患者安全。 接下来,文章提到传统的安全措施可能不够,因为攻击可能会扩散到关键系统。因此,制药企业需要做好应对准备,比如通过微分段和零信任架构来限制攻击范围,并利用自动化和AI加速恢复过程。 用户的要求是总结内容在100字以内,所以我要抓住关键点:网络攻击对制药行业的影响、CSV的作用、传统安全措施的不足以及建议的解决方案。 最后,组织语言,确保简洁明了。可能需要调整句子结构,去掉不必要的细节,只保留核心信息。 </think> 文章探讨了网络攻击对制药行业的严重影响,特别是计算机系统验证(CSV)在保障数据完整性、产品质量和患者安全中的关键作用。传统安全措施无法有效应对现代网络攻击的扩散风险。文章建议通过微分段、零信任架构和自动化工具等手段提升 breach readiness(应急准备能力),以最小化攻击影响并快速恢复运营。 2026-4-13 16:9:18 Author: securityboulevard.com(查看原文) 阅读量:1 收藏
In the pharmaceutical industry, a cyberattack does more than breach systems; it undermines the integrity of operational reality.
During a discussion with pharmaceutical CISOs at RSA, one asked a critical question: “How did you deal with CSV after a breach?”
The reality is that without breach readiness, CSV does not merely slow operations; it halts them entirely.
Before addressing the main topic, it is important to define CSV.
The Complexity of Computer Systems Validation
While all industries are affected by breaches, pharmaceutical companies face unique and more severe consequences due to a regulatory framework that many leaders do not fully appreciate until after an incident.
CSV is a documented process for ensuring that a computer system performs exactly as designed, consistently and reproducibly, by meeting all predetermined requirements and is fit for its intended use.
CSV helps to ensure data integrity, patient safety, and product quality, and reduces the risk of product recalls and regulatory action. CSV is often required when changes to software, hardware, or configurations may affect the performance, data integrity, or compliance of a Digital Industrial System.
Digital Industrial Systems include all digital industrial systems used by the pharmaceutical company, whether on-premises, in the cloud, or in OT (including Industrial Control Systems, Industrial IoT, Cyber-Physical Systems, or the Internet of Medical Devices), which constitutes the entire attack surface of a pharma company. Regulations in the pharma industry require these Digital Industrial Systems to undergo Computerized System Validation (CSV) following significant changes or events that may affect their validated state.
And a cyberattack, especially ransomware or a wiper attack, is the most severe form of unplanned change that can disturb the validated state of a Digital Industrial System. Pharmaceutical enterprises can no longer demonstrate that their electronic records are Attributable, Legible, Contemporaneous, Original, and Accurate (the ALCOA+ standard) because an adversary may have altered, deleted, or fabricated them.
CSV extends beyond compliance; it represents the essential agreement between digital systems and regulatory trust.
Once a cyberattack undermines this trust, multiple critical elements fail simultaneously:
- Data integrity
- Product quality
- Regulatory confidence
These elements are not merely degraded.
They are voided across all connected systems. Whether it is a Manufacturing Execution System, SCADA controller, LIMS, ERP, or a cloud-based quality management system, the validated state is immediately considered void under FDA 21 CFR Part 11, EU GMP Annex 11, and similar global regulations.
Most pharmaceutical companies have invested in perimeter controls, yet maintain flat networks. As a result, regulatory authorities typically assume that all connected systems have experienced a loss of integrity during a cyberattack.
Traditional flat networks do more than enable breaches.
They industrialize the blast radius.
In the pharmaceutical sector, the blast radius is not solely an IT concern.
It results in:
- a manufacturing shutdown
- a regulatory freeze
- a patient safety risk
Unless you can demonstrate that the blast radius was contained and the attack did not spread, regulators will assume:
- Enterprise-wide contamination
- Loss of data integrity
- Collapse of the validated state
When a cyberattack is suspected of compromising the integrity of a GxP computerized system through uncontrolled lateral movement, a CSV must be generated before systems can be operated. No pharmaceutical enterprise can legally release batches manufactured on those systems until full Computer System Validation (CSV) or Computer Software Assurance (CSA) has been re-executed and documented.
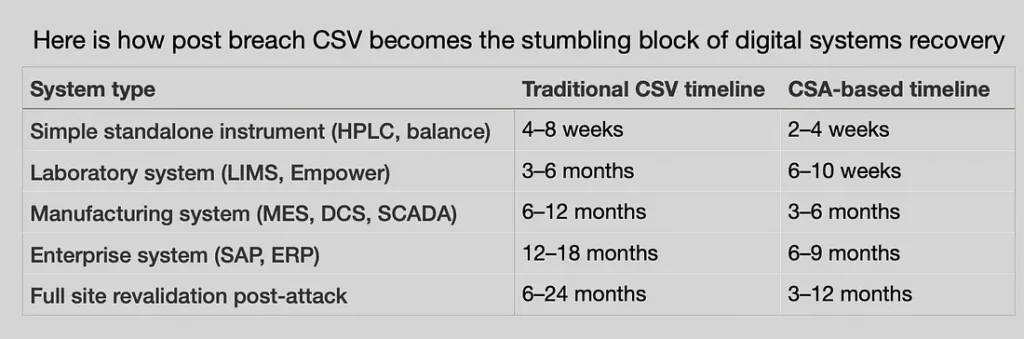
For enterprises that are not breach-ready, recovery plans often fail even after restoring all backed-up data. Recovery timelines can range from two weeks to twelve months.
Here is the real impact:
- Any batch manufactured on a system whose validated state was compromised must be treated as potentially adulterated. It cannot be released to market.
- If regulatory inspectors discover an attack and find no evidence of revalidation, they will issue observations for all affected systems, effectively halting quality assurance.
- The company cannot submit data to regulators (NDA, BLA, ANDA, MAA) generated on systems whose integrity has not been demonstrated post-attack.
- If products from compromised batches have already been released, a recall is mandatory.
Cyberattacks Introduce an Additional Layer of Complexity
To understand the risks faced by a non-breach-ready pharmaceutical enterprise, consider the example of Merck. The NotPetya attack did more than encrypt systems.
The attack:
- erased 30,000 machines, caused $1.4 billion in total damages, and a multi-year insurance litigation battle.
- led to two weeks of total operational paralysis, halting production globally.
- forced the borrowing of national vaccine reserves, the US government’s entire emergency supply of Gardasil 9.
This was not a routine cyber incident; it represented a systemic collapse.
This occurred before the modern era of AI-assisted attacks, before the IT/OT convergence had gone as far as it has today, and before regulators had written cybersecurity explicitly into Annex 11 and FDA’s OT guidance.
Other notable examples include the Cencora cascade (27 pharma victims from a single breach), Change Healthcare ($100M/day in losses, $2B in advances paid), Pharmascience Canada (June 2024), and Inotiv (August 2025, Qilin ransomware, 176 GB exfiltrated).
By 2026, it is clear that cyberattacks are increasing. The question is no longer if an organization will be attacked, but when.
Access Forrester Wave Report: Discover why ColorTokens was rated ‘Superior’ in OT, IoT, and Healthcare Security.
Report: Discover why ColorTokens was rated ‘Superior’ in OT, IoT, and Healthcare Security.
And that means pharmaceutical enterprises must invest to anticipate the next breach, prepare to withstand its effects, and evolve those capabilities over time.
Now let’s walk through what failure actually looks like:
A medium-sized pharmaceutical company, such as a contract research organization, experiences a cyberattack. Lacking breach readiness, it shuts down all operations and engages external cybersecurity experts.
Week 1–4: Forensics. No answers.
Week 5–6: Recovery attempts. Partial success.
Week 7: Data gaps are identified. The CEO decides to proceed with available resources.
Week 8 and beyond: CSV requirements arise. GMP-certified systems require CSV or CSA before recovered data can be used for batch manufacturing, resulting in a minimum delay of eight additional weeks.
Enduring the cyberattack was already challenging and caused unexpected delays. Even after aligning digital systems and accepting data loss, regulatory requirements further delay business resumption by at least eight weeks. Many CISOs view this as discouraging.
I assume most modern pharmaceutical companies are aware of this risk and may already be prepared for the next breach.
Breach readiness is not about avoiding CSV, but about ensuring CSV requirements do not extend across the entire enterprise.
Enterprises should prioritize the following five actions:
- Break the attack path before it reaches GxP systems. Design your enterprise as critical zones with hardened microsegments and software-controlled conduits. Because if an attacker reaches GxP, you have already lost the CSV battle. This not only reduces the attack surface but also the blast radius, denying attackers who misuse stolen credentials access to GxP systems. Document the reduced blast radius, demonstrating the possible spread of a cyberattack.
- Build breach readiness capabilities to deny cyberattacks. Model cyber defenses using artificial intelligence to determine context-specific breach-response capabilities that can quarantine cyberattacks within microsegments and zones by disconnecting conduits at the push of a button. This ensures that should a CSV be necessary, the scope is limited to a small microsegment.
- Enhance operational capabilities to expedite CSV delivery. Shift from exhaustive manual testing to a risk-based approach, such as Computer Software Assurance (CSA), and incorporate automation into the development lifecycle. Prioritize validation of high-risk functions affecting patient safety or product quality, rather than minor features. Ensure all backups are restorable.
- Implement AI tools to eliminate manual data manipulation. Accelerate CSV processes by automating data cleaning, enabling complex transformations through conversational prompts, and utilizing parallel processing to reduce task durations from hours to seconds. Use browser-based spreadsheets with integrated AI for data cleaning, analysis, and visualization.
- Establish strict governance over user requirement specifications and change management. Delays in CSV often result from inadequate planning and poorly defined requirements. Vague or incomplete User Requirement Specifications (URS) create cascading issues. Centralize and adequately resource CSV operations to eliminate bottlenecks.
A key differentiator for prepared pharmaceutical enterprises is the ability to keep critical digital systems unaffected during major cyberattacks. Since April 2024, the sector has experienced a 30% increase in ransomware targeting more than just IT. In the event of a breach, restoring from backup is only the initial step toward resuming normal operations.
Breach readiness involves managing and containing damage, rather than preventing every attack.
It is about engineering controls to determine where a breach stops, how far it spreads, and what remains unaffected. It is about designing your digital enterprise so that when the inevitable breach occurs, the critical digital business stays unaffected, ensuring a Minimum Viable Digital Business.
No operational shutdown.
No prolonged forensic investigations.
Only a contained incident occurs, while your Minimum Viable Digital Business continues to deliver medicines, release batches, and protect patients.
As boards invest heavily in digital transformation and AI-driven drug discovery, cybersecurity can no longer be viewed solely as an IT issue. Ignoring the realities of post-breach business resumption risks both patient safety and shareholder value. A new approach is required immediately.
This is accomplished through foundational capabilities such as microsegmentation, which enables organizations to anticipate, withstand, and evolve breach readiness. Adopting a zero-trust architecture and conducting regular drills can develop operational muscle memory, making containment instinctive.
The result is that core operations remain unaffected and continue without interruption.
The Call to Action for Pharma Leaders
CEOs and Boards: If not already addressed, make 2026 the year to integrate breach readiness into your strategy by enhancing CSV management and preparing for potential breaches.
- Approach breach readiness as a board-level strategy, not merely a responsibility for the CISO or Head of Quality. The ability to anticipate, withstand, and evolve breach-readiness capabilities will assure stakeholders that digital and AI initiatives will deliver promised value.
- Demand microsegmentation that seamlessly integrates with your existing investments in cybersecurity, like Firewalls, EDR, WAF, Deception, and Identity Management. Something that can be both agent and agentless and delivers real containment pervasively across IT and OT, cloud and on-prem.
- Demand progressive reduction of your attack surface and breach exposure, ensuring your business runs seamlessly as your lateral movement is reduced, making it difficult for cyberattackers to navigate unchallenged.
- Demand an architecture and design using microsegmentation that uses artificial intelligence to customize breach readiness for your enterprise. Make CSV the centerpiece of your breach readiness. Enhance your operational readiness.
- Ensure your enterprise is organized into zones based on critical digital infrastructure, each containing microsegments connected by conduits. Build software-based controls to disconnect the smallest microsegment at the first sign of a cyberattack.
- Prioritize operational excellence by modeling cyber defenses, developing playbooks for CSV activities, and practicing responses until they become instinctive. Conduct regular tabletop exercises to test containment, CSV validation, and business resumption, not just detection.
- Lead from the front. Conduct a Breach Readiness Impact Assessment today. Build an integrated closed-loop cybersecurity program. And then assess your current CSV data preparation and AI capabilities.
In 2026, threats are AI-powered and persistent. The need for breach readiness is immediate. Organizations must choose between continuing reactive approaches or building a breach-ready enterprise that assures stakeholders of resilience during unprecedented cyberattacks. Strengthen your CSV capabilities.
Cybersecurity is no longer about protection. It is about preserving trust under attack.
And in pharma, trust is binary:
Either your systems are validated.
Or they are not
There is no middle ground.
So the question is no longer:
Will you be breached?
The question is:
When it happens, will your enterprise still be able to release a batch?
If the answer is no, you are not breach-ready.
If the answer is yes, you are building trust and confidence.
Be known as an enterprise that never shuts down core operations. Be breach ready.
Talk to us about building a breach-ready pharma environment that contains attacks, limits CSV scope, and keeps critical operations running.
The post CSV: The X Factor for Being Breach Ready in Pharma appeared first on ColorTokens.
*** This is a Security Bloggers Network syndicated blog from ColorTokens authored by Agnidipta Sarkar. Read the original post at: https://colortokens.com/blogs/computer-system-validation-pharma-breach-readiness/
如有侵权请联系:admin#unsafe.sh