
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住关键点。 文章主要讲的是一个新的信息窃取软件Storm,它在2026年初出现在地下网络犯罪市场。Storm的价格每月不到1000美元,可以窃取浏览器凭证、会话cookie和加密钱包信息,并将数据传送到攻击者的服务器进行解密。 接下来,文章解释了为什么企业应该关注Storm。传统的窃取软件会在受害者机器上解密浏览器凭证,但随着Google引入App-Bound Encryption,这种方法变得困难。Storm则通过服务器端解密,绕过了传统的检测方法。 此外,Storm支持Chromium和Gecko浏览器,并且可以自动恢复会话cookie,让攻击者无需手动操作。收集的数据包括密码、信用卡信息等敏感信息,甚至可以通过一个被入侵的浏览器访问企业资源。 最后,文章提到Storm的基础设施和定价策略,以及它如何帮助攻击者绕过检测机制。 现在我要把这些关键点浓缩到100字以内。重点包括Storm的功能、价格、技术变化、对企业的影响以及其独特之处。 </think> 新的网络犯罪工具Storm以每月不到1000美元的价格提供浏览器凭证、会话cookie和加密钱包窃取功能,并通过服务器端解密绕过传统检测机制。它支持Chromium和Gecko浏览器,并自动恢复会话cookie,使攻击者无需手动操作即可获取敏感数据。 2026-4-13 14:16:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏

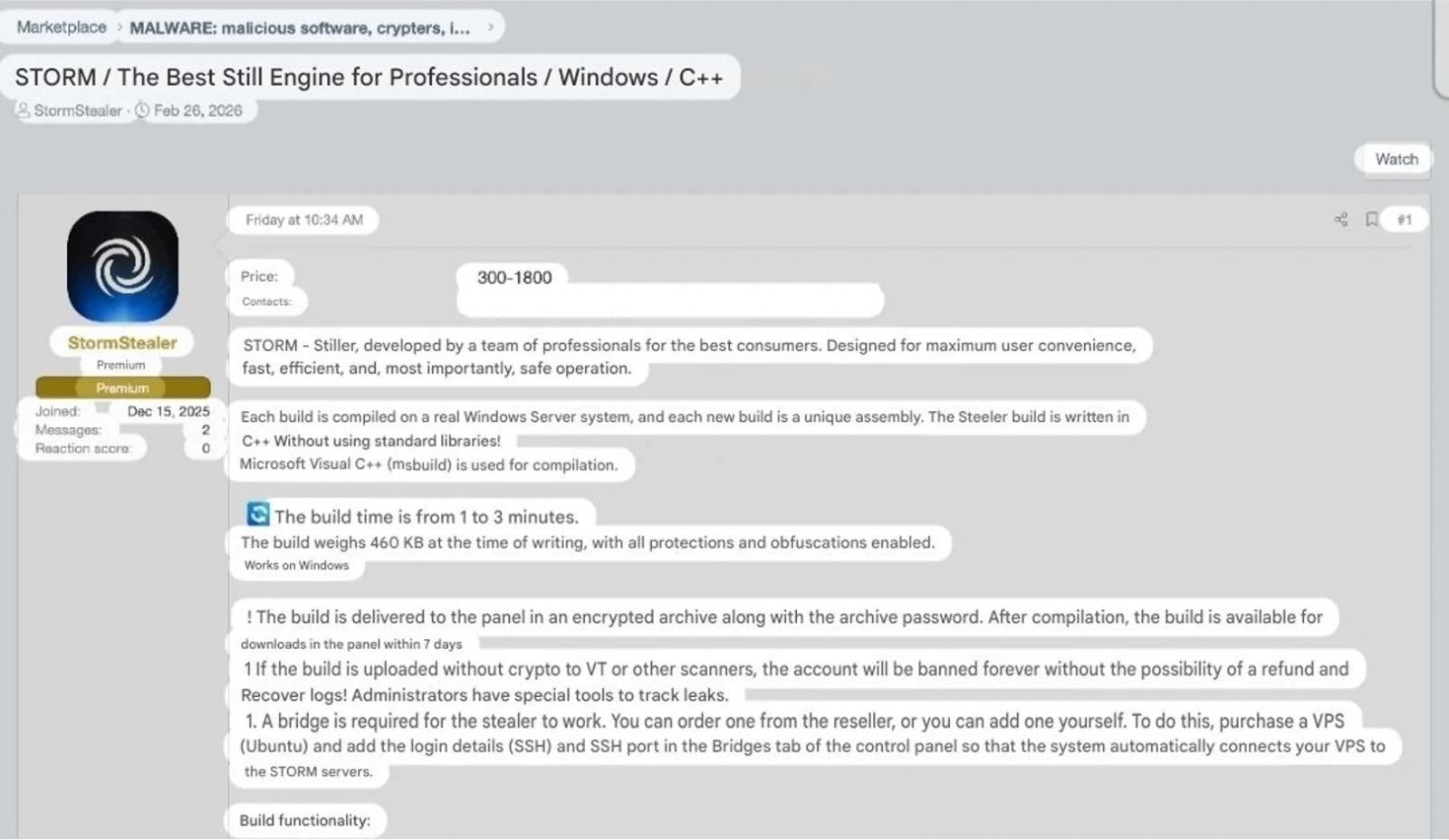
A new infostealer called Storm appeared on underground cybercrime networks in early 2026, representing a shift in how credential theft is developing. For under $1,000 a month, operators get a stealer that harvests browser credentials, session cookies, and crypto wallets, then quietly ships everything to the attacker's server for decryption.
To understand why enterprises should care, it helps to know what changed. Stealers used to decrypt browser credentials on the victim's machine by loading SQLite libraries and accessing credential stores directly. Endpoint security tools got good at catching this, making local browser database access one of the clearest signs that something malicious was running.
Then Google introduced App-Bound Encryption in Chrome 127 (July 2024), which tied encryption keys to Chrome itself and made local decryption even harder. The first wave of bypasses involved injecting into Chrome or abusing its debugging protocol, but those still left traces that security tools could pick up.
Stealer developers responded by stopping local decryption altogether and shipping encrypted files to their own infrastructure instead, removing the telemetry most endpoint tools rely on to catch credential theft.
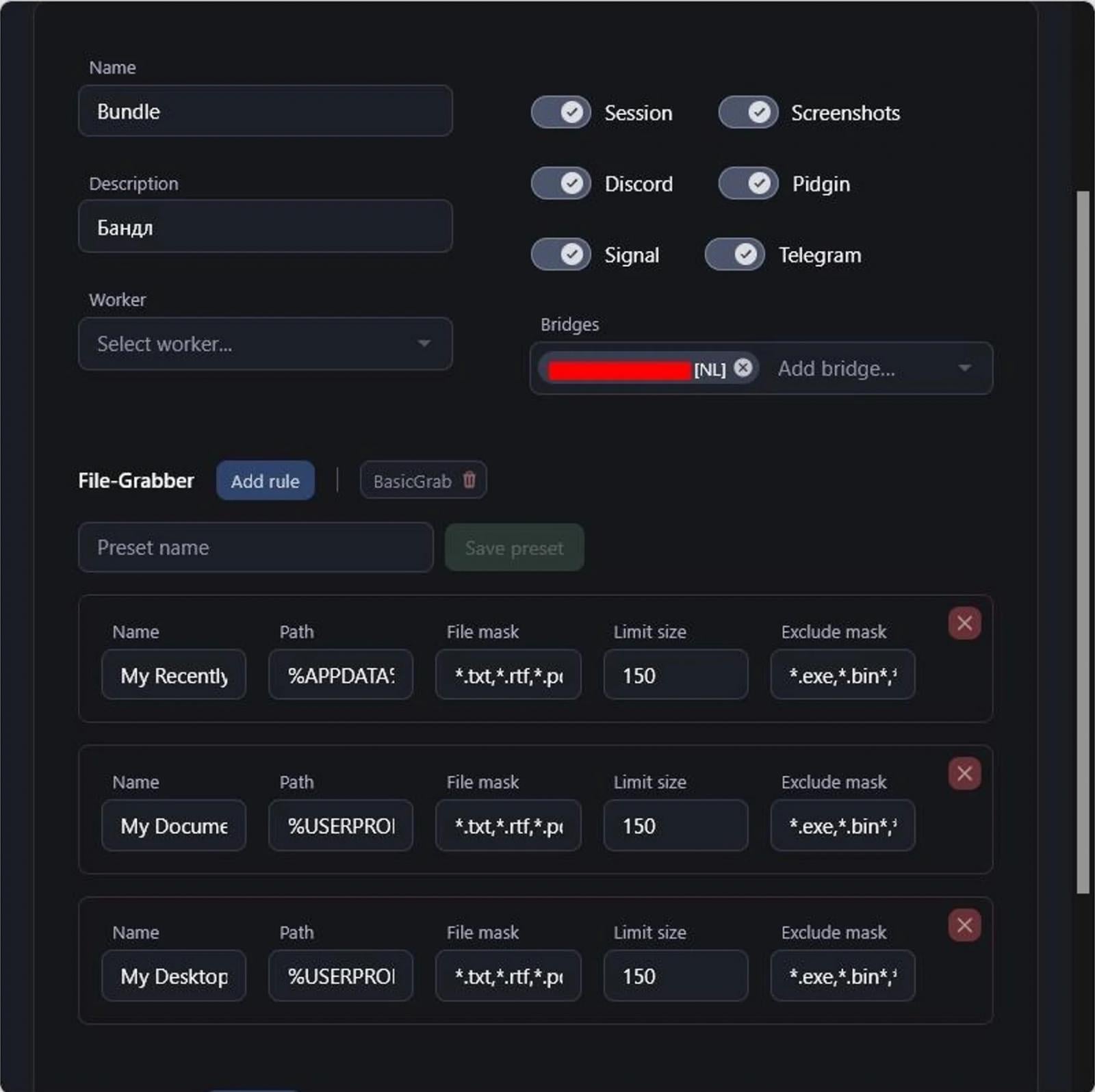
Storm takes this approach further by handling both Chromium and Gecko-based browsers (Firefox, Waterfox, Pale Moon) server-side, where StealC V2 still processes Firefox locally.
Collected data includes everything attackers need to restore hijacked sessions remotely and steal from their victims: saved passwords, session cookies, autofill, Google account tokens, credit card data, and browsing history.
One compromised employee browser can hand an operator authenticated access to SaaS platforms, internal tools, and cloud environments without ever triggering a password-based alert.
Cookie restore and session hijacking
Once Storm has decrypted the browser data, stolen credentials and session cookies are dumped directly into the operator's panel. Where most stealers require buyers to manually replay stolen logs, Storm automates the next step.
Feed in a Google Refresh Token and a geographically matched SOCKS5 proxy, and the panel silently restores the victim's authenticated session.

Varonis Threat Labs has covered this class of attack before. Our Cookie-Bite research demonstrated how stolen Azure Entra ID session cookies render MFA irrelevant, giving attackers persistent access to Microsoft 365 without ever needing a password.
The SessionShark analysis showed how phishing kits intercept session tokens in real time to defeat Microsoft 365 MFA. Storm's cookie restore is the same underlying technique, productised and sold as a subscription feature.
Introducing Varonis Interceptor
AI introduces a new breed of email threats that are more deceptive than ever. Varonis Interceptor is the AI-native email security solution built to stop today's most sophisticated threats before they ever reach your inbox.
Watch the Interceptor webinar to see how Varonis enables true AI-powered security outcomes.
Collection and infrastructure
Beyond credentials, Storm grabs documents from user directories, pulls session data from Telegram, Signal, and Discord, and targets crypto wallets through both browser extensions and desktop apps. System information and screenshots are captured across multiple monitors. Everything runs in memory to reduce the chance of detection.
On the infrastructure side, operators connect their own virtual private servers (VPS) to Storm's central servers, routing stolen data through infrastructure they control rather than a shared platform. This keeps the central servers insulated from takedown attempts, because law enforcement or abuse reports hit the operator's node first.
Team management supports multiple workers with permissions covering log access, build creation, and cookie restoration, so a single Storm licence can support a small cybercriminal operation with divided responsibilities.
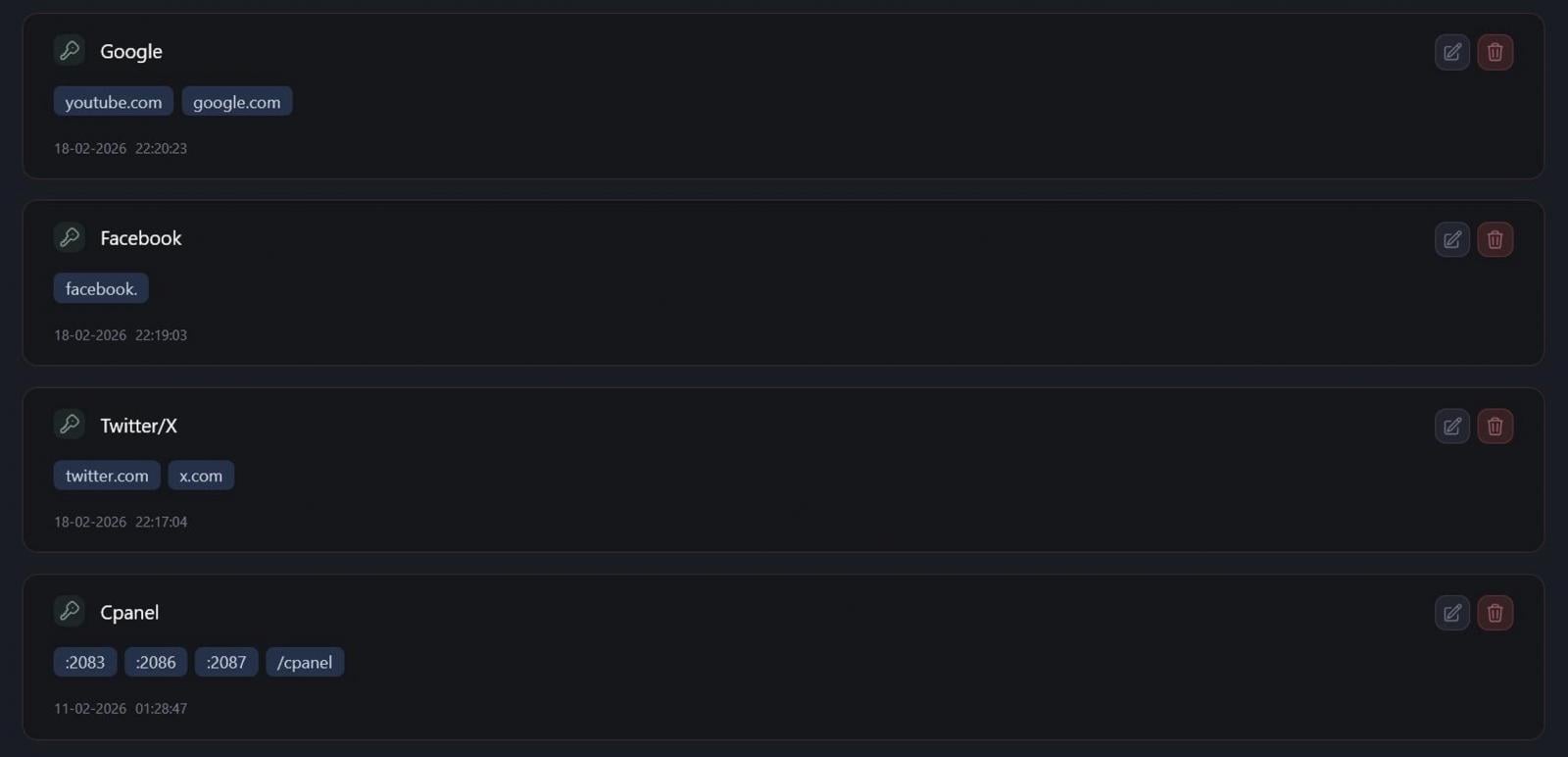
Domain detection auto-labels stolen credentials by service, with rules visible for Google, Facebook, Twitter/X, and cPanel, making it straightforward for operators to filter and prioritise the accounts they want to exploit first.
Active campaigns and pricing
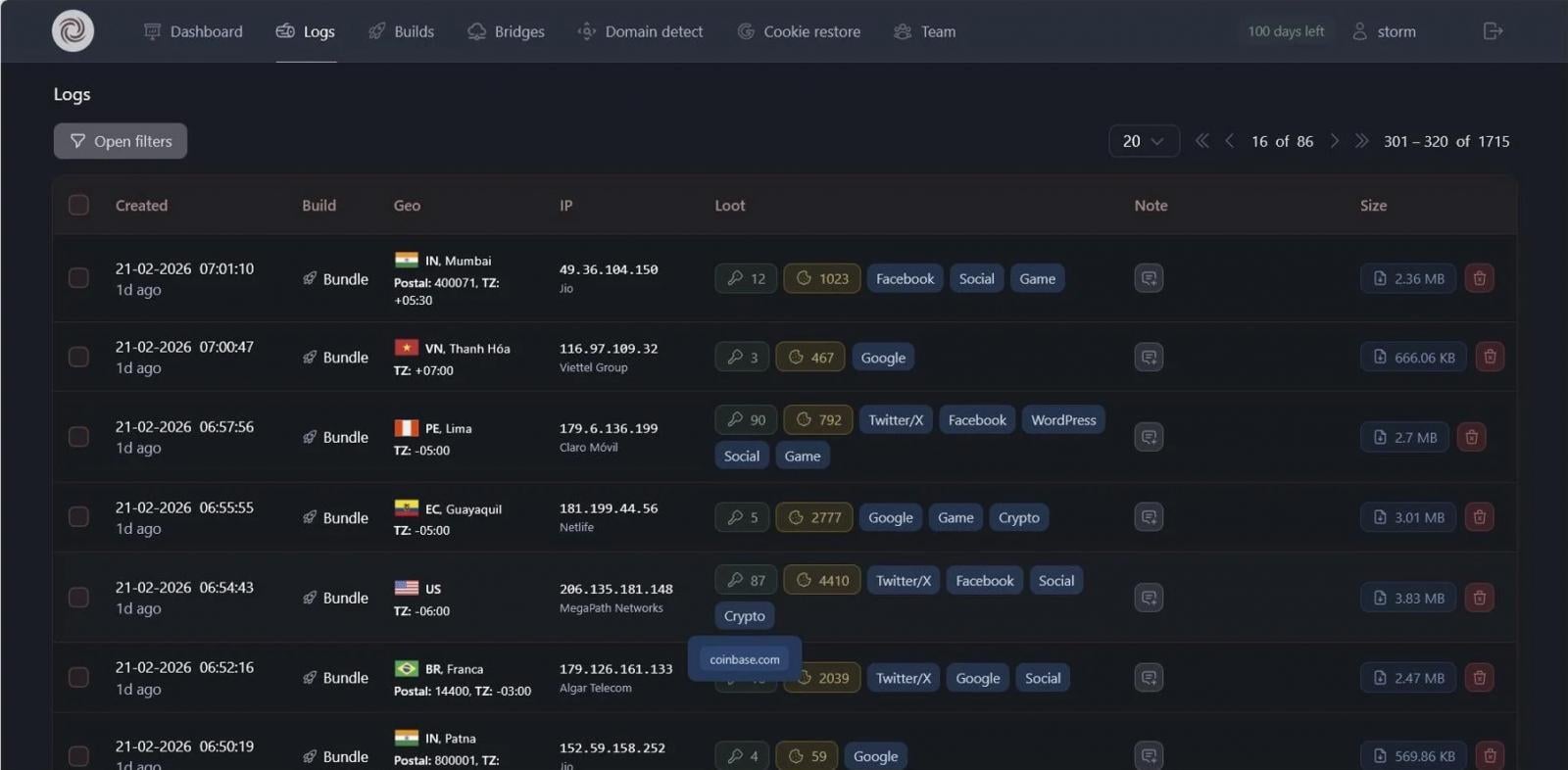
At the time of investigation, the logs panel contained 1,715 entries spanning India, the US, Brazil, Indonesia, Ecuador, Vietnam, and several other countries. Whether all of these represent real victims or include test data is difficult to confirm from panel imagery alone, but the varied IPs, ISPs, and data sizes look consistent with active campaigns.
Credentials tagged to Google, Facebook, Twitter/X, Coinbase, Binance, Blockchain.com, and Crypto.com appear across multiple entries, the kind of data that typically ends up on the credential marketplaces that feed account takeover, fraud, and initial access for more targeted intrusions.

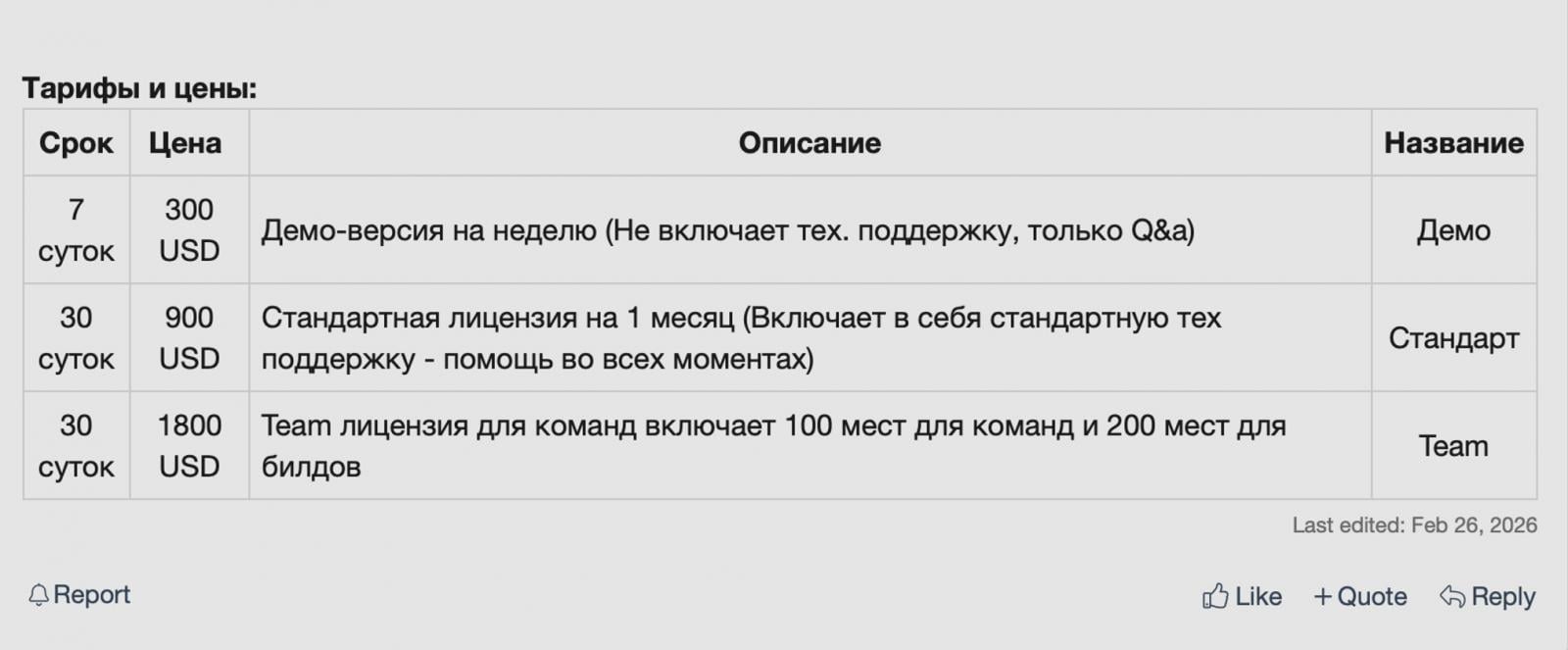
Storm is sold on a tiered subscription: $300 for a 7-day demo, $900/month standard, $1,800/month for a team license with 100 operator seats and 200 builds. A crypter is required on top.
Builds keep running after a subscription expires, so deployed stealers continue harvesting data regardless of the operator’s license status.
Detecting stolen sessions
Storm is consistent with a broader shift in the stealer market. Server-side decryption enables attackers to avoid tripping endpoint tools designed to catch traditional on-device decryption, and session cookie theft has been replacing password theft as the primary objective for a while now.
The credentials and sessions that stealers like Storm harvest are the start of what comes next: logins from unfamiliar locations, lateral movement, and data access that breaks established patterns.
Indicators of compromise
-
Forum handle: StormStealer
-
Forum ID: 221756
-
Account registered: 12/12/25
-
Current version: v0.0.2.0 (Gunnar)
-
Build characteristics: C++ (MSVC/msbuild), ~460 KB, Windows only
This article originally appeared on the Varonis blog.
Sponsored and written by Varonis.
如有侵权请联系:admin#unsafe.sh