
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解主要观点。 文章主要讨论了Black Hat Asia 2026大会前的网络安全威胁形势。重点包括勒索软件的增长、AI驱动的威胁以及供应链风险。勒索软件已经进入高频阶段,攻击频率显著增加,攻击手段更加系统化和工业化。同时,AI技术被用于攻击中,扩大了攻击面。供应链的漏洞也被利用,导致更大的影响范围。 接下来,我需要将这些关键点浓缩到100字以内。要确保涵盖勒索软件、AI威胁、供应链风险以及大会的主题。同时,语言要简洁明了,直接描述内容。 可能的结构是:先点明大会主题和主要威胁类型,然后简述勒索软件的情况和AI的影响,最后提到供应链风险和大会的关注点。 现在试着组织语言: Black Hat Asia 2026大会探讨了勒索软件增长、AI驱动的网络威胁及供应链风险对全球网络安全的影响。勒索软件进入高频阶段,攻击更加系统化;AI技术扩大了攻击面;供应链漏洞导致更大影响。大会将聚焦于这些趋势和系统性风险。 检查字数是否在100字以内,并调整用词使其更简洁。 最终版本: Black Hat Asia 2026探讨了勒索软件增长、AI驱动的网络威胁及供应链风险对全球网络安全的影响。勒索软件进入高频阶段,攻击更加系统化;AI技术扩大了攻击面;供应链漏洞导致更大影响。大会将聚焦于这些趋势和系统性风险。 </think> Black Hat Asia 2026探讨了勒索软件增长、AI驱动的网络威胁及供应链风险对全球网络安全的影响。勒索软件进入高频阶段,攻击更加系统化;AI技术扩大了攻击面;供应链漏洞导致更大影响。大会将聚焦于这些趋势和系统性风险。 2026-4-13 13:19:24 Author: cyble.com(查看原文) 阅读量:34 收藏
Black Hat Asia 2026 Is Coming to Singapore — Here’s What the Threat Landscape Looks Like Ahead of It
Black Hat Asia 2026 explores ransomware growth, AI-driven cyber threats, and supply chain risks reshaping global cybersecurity and digital resilience.
As the cybersecurity community prepares for Black Hat Asia 2026 Singapore, the conversation is shifting from isolated incidents to systemic risk. The Black Hat Asia 2026 conference arrives at a moment when cyber threats are no longer sporadic disruptions. Instead, they are persistent, industrialized, and intertwined with global infrastructure.
The discussions expected in the Black Hat Asia 2026 schedule and among Black Hat Asia 2026 speakers will likely reflect a reality that defenders are already grappling with: scale has become the defining feature of modern cybercrime.
Ransomware Has Entered a High-Throughput Era
Ransomware activity since late 2025 has moved beyond periodic spikes into a sustained, high-frequency operating model. Over the last four months, threat actors have claimed roughly 700 victims per month on average. This marks a notable jump from the approximately 512 monthly victims observed in the first three quarters of 2025, an increase of more than 30 percent.
This is not just growth; it highlights maturation. Ransomware groups are no longer operating like loosely organized gangs. They resemble production systems, automated, repeatable, and optimized for throughput. Attack pipelines now rely heavily on credential theft, automated exploitation of known vulnerabilities, and scalable infrastructure that allows campaigns to run continuously.
Supply chain compromises have amplified this efficiency. Rather than targeting organizations individually, attackers breach IT providers or managed service vendors to access multiple downstream victims. One compromised vendor can cascade into dozens of affected organizations, dramatically increasing operational impact.
Key Players and Tactical Shifts
Among active groups, Qilin has demonstrated particularly aggressive activity, with over 100 claimed victims in a single month.
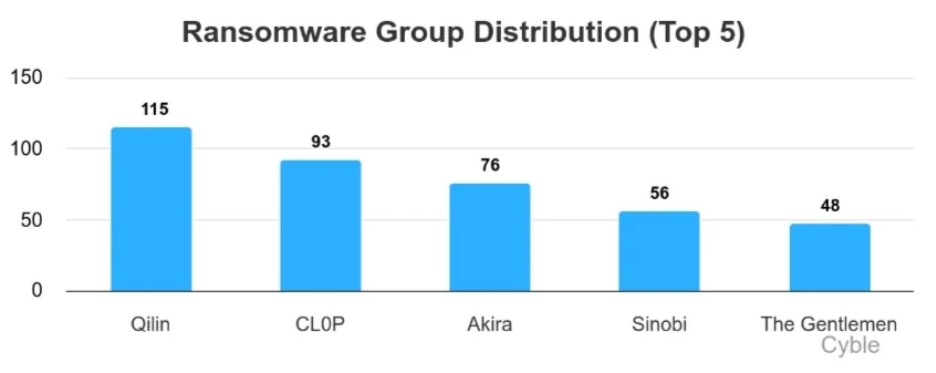
Meanwhile, CL0P has re-emerged with campaigns targeting enterprise software ecosystems, an approach that historically yields high-volume results when successful.
Other groups, such as Akira continue to operate at a steady pace, while newer entrants like Sinobi and The Gentlemen are quickly establishing themselves. This constant churn reflects a competitive underground economy where innovation is driven by survival.
Notably, the tactics themselves are evolving. Traditional ransomware encryption is no longer the centerpiece. Instead, attackers prioritize data exfiltration, public exposure threats, and rapid monetization. Negotiation cycles are shrinking, and pressure tactics are intensifying.
Where Attacks Are Landing
Geographically, ransomware activity continues to concentrate in highly digitized economies. The United States remains the primary target, accounting for nearly half of observed incidents in early 2026. However, the United Kingdom and Australia have also seen increased activity, partly linked to large-scale exploitation campaigns.
The logic is straightforward: attackers follow digital density. Regions with mature enterprise ecosystems, extensive outsourcing, and interconnected infrastructure offer higher payouts and more opportunities for lateral movement.
From a sector perspective, construction, manufacturing, and professional services remain frequent targets. These industries often operate with fragmented security controls and rely heavily on interconnected supplier networks, conditions that attackers exploit.
The IT services sector is also attractive. Compromising a service provider can unlock access to multiple client environments, effectively multiplying the impact of a single intrusion.
Real-World Incidents Reflect Broader Trends
Recent incidents highlight the diversity and scale of ransomware impact. CL0P-linked campaigns have affected organizations across the finance, healthcare, and hospitality sectors in multiple regions. Meanwhile, the Everest group has reportedly targeted a U.S.-based telecommunications manufacturer, exfiltrating sensitive engineering data such as circuit schematics and design files, assets that carry long-term intellectual property risks.
Critical infrastructure-adjacent organizations are also under pressure. A breach attributed to Qilin reportedly exposed sensitive data from a U.S. airport authority, including financial records and operational documents.
In Asia, attacks against IT service providers underscore the ongoing vulnerability of managed environments. When attackers access centralized infrastructure, they gain leverage over multiple organizations simultaneously.
The Constant Arrival of New Threat Actors
Even as established groups dominate headlines, new ransomware operations continue to emerge. Groups like Green Blood, DataKeeper, and MonoLock highlight how accessible the ransomware ecosystem has become. Many operate under ransomware-as-a-service models, lowering the barrier to entry for affiliates.
These newer groups often emphasize technical features such as in-memory execution, multithreaded encryption, and hybrid cryptographic techniques. But more importantly, they reflect a broader trend: ransomware is becoming a business model, complete with revenue-sharing schemes and affiliate programs.
Beyond Ransomware: Expanding Threat Vectors
While ransomware dominates, it is only part of the threat landscape leading into Black Hat Asia 2026. Hacktivist activity has expanded, with loosely aligned groups forming coordinated networks across geopolitical lines. These operations are often low in sophistication, focused on DDoS attacks and defacements, but high in volume and visibility.
At the same time, mobile-based threats and social engineering campaigns are accelerating. Attackers are leveraging real-world events to craft convincing phishing messages, malicious apps, and even voice-based scams. The use of AI tools has made these attacks more scalable and believable, reducing the skill required to execute them.
AI: A Double-Edged Sword
The rapid adoption of artificial intelligence, particularly in countries like India, is introducing both opportunity and risk. AI systems are no longer passive tools; they are active decision-makers embedded in critical workflows.
This shift expands the attack surface. Threats now include data poisoning, model manipulation, prompt injection, and unintended data leakage through AI outputs. At the same time, AI is enabling attackers to automate reconnaissance, personalize phishing, and accelerate vulnerability discovery.
The result is a more balanced battlefield; both attackers and defenders have access to powerful tools, but the speed of offense is increasing faster than defensive adaptation.
What This Means for Black Hat Asia 2026
The Black Hat Asia 2026 schedule is likely to reflect these converging trends: industrialized ransomware, supply chain fragility, AI-driven threats, and the growing complexity of global cyber operations. The Black Hat Asia 2026 speakers will not just be discussing vulnerabilities; they will be addressing systemic risk across interconnected ecosystems.
The current threat landscape suggests a fundamental shift in how organizations must approach security. Prevention alone is no longer sufficient. Resilience, through segmentation, strong identity controls, continuous monitoring, and robust backup strategies, has become essential.
Equally important is understanding external risk. Third-party exposure, supply chain dependencies, and shared infrastructure are now central to organizational security posture.
As Black Hat Asia 2026 Singapore approaches, one thing is cannot be overlooked: cybersecurity is no longer a technical function operating in the background. It is a discipline that must evolve continuously to keep pace with an organized, adaptive, and relentless adversary ecosystem.
如有侵权请联系:admin#unsafe.sh
