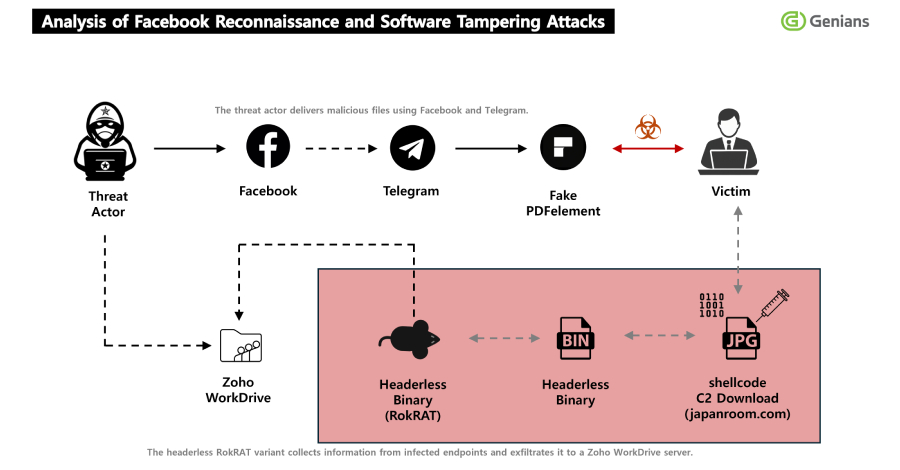
The North Korean hacking group tracked as APT37 (aka ScarCruft) has been attributed to a fresh multi-stage, social engineering campaign in which threat actors approached targets on Facebook and added them as friends on the social media platform, turning the trust-building exercise into a delivery channel for a remote access trojan called RokRAT.
"The threat actor used two Facebook accounts with their location set to Pyongyang and Pyongsong, North Korea, to identify and screen targets," the Genians Security Center (GSC) said in a technical breakdown of the campaign. "After building trust through friend requests, the actor moved the conversation to Messenger and used specific topics to lure targets as part of the initial social engineering stage of the attack."
Central to the attack is the use of what the GSC describes as pretexting, a tactic where the threat actors aim to trick unsuspecting users into installing a dedicated PDF viewer, claiming the software was necessary to open encrypted military documents. The PDF viewer used in the infection chain is a tampered version of Wondershare PDFelement, which, when launched, triggers the execution of embedded shellcode that allows the attackers to obtain an initial foothold.
Another significant aspect of the campaign is that it utilizes legitimate but compromised infrastructure for command-and-control (C2), weaponizing the website associated with the Seoul arm of a Japanese real estate information service to issue malicious commands and payloads. What's more, the payload takes the form of a seemingly harmless JPG image to deliver RokRAT.
"This is assessed as a highly evasive strategy that combines legitimate software tampering, abuse of a legitimate website, and file extension masquerading," the GSC said.
In the attack sequence detailed by the South Korean cybersecurity company, the threat actors have been found to create two Facebook accounts -- "richardmichael0828" and "johnsonsophia0414," both of which were created on November 10, 2025 -- and deliver a ZIP file after moving the conversation to Telegram, with the archive containing the trojanized version of Wondershare PDFelement along with four PDF documents and a text file containing instructions to install the program to view the PDFs.
The encrypted shellcode executed after the launch of the tampered installer allows it to establish communication with the C2 server ("japanroom[.]com") and download a second-stage payload, a JPG image ("1288247428101.jpg") that's then used to final RokRAT payload.
The malware, for its part, abuses Zoho WorkDrive as C2 – a tactic also detailed by Zscaler ThreatLabz in February 2026 as part of a campaign codenamed Ruby Jumper – enabling it to capture screenshots, enable remote command execution via "cmd.exe," collect host information, perform system reconnaissance, and evade detection by security programs like Qihoo's 360 Total Security, while disguising malicious traffic.
"Its core functionality has remained relatively stable and has been reused repeatedly across multiple operations over time," the GSC said. "This shows that RokRAT has focused less on changing its core functionality and more on evolving its delivery, execution, and evasion chain."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.