好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住关键点。 文章讲的是黑客入侵了CPUID项目的API,篡改了官方网站上的下载链接,导致用户下载到恶意软件。受影响的工具是CPU-Z和HWMonitor,它们有很多用户。用户在Reddit上报告说下载的文件其实是HWiNFO的恶意版本。恶意文件名是HWiNFO_Monitor_Setup,运行后会启动一个俄罗斯安装程序,这很可疑。 进一步的信息显示,原始文件没有被破坏,但分发链接被污染了。研究人员确认了这一点,并指出这是一个复杂的恶意软件,使用了多种技术来逃避检测。此外,攻击者之前还攻击过FileZilla的用户。最后,CPUID确认问题已经解决,并提供了修复后的干净版本。 现在我需要把这些信息浓缩到100字以内。重点包括:黑客入侵API篡改链接、分发恶意软件、影响广泛使用的工具、恶意软件复杂且逃避检测、CPUID已修复问题。 接下来组织语言,确保简洁明了。避免使用“这篇文章”这样的开头,直接描述内容。 </think> 黑客入侵CPUID项目API,在其官网上篡改下载链接,分发针对CPU-Z和HWMonitor工具的恶意可执行文件。这些工具拥有大量用户群体。恶意文件伪装成另一诊断工具HWiNFO的版本,并使用复杂技术逃避检测。事件已修复,官方确认原始文件未被破坏。 2026-4-10 13:16:12 Author: www.bleepingcomputer.com(查看原文) 阅读量:6 收藏
Hackers gained access to an API for the CPUID project and changed the download links on the official website to serve malicious executables for the popular CPU-Z and HWMonitor tools.
The two utilities have millions of users who rely on them for tracking the physical health of internal computer hardware and for comprehensive specifications of a system.
Users who downloaded either tool reported on Reddit recently that the official download portal points to the Cloudflare R2 storage service and fetches a trojanized version of HWiNFO, another diagnostic and monitoring tool from a different developer.
The name of the malicious file is HWiNFO_Monitor_Setup, and running it launches a Russian installer with an Inno Setup wrapper, which is atypical and highly suspicious.
Users reported that downloading the clean hwmonitor_1.63.exe from the direct URL was still possible, indicating that the original binaries were intact, but the distribution links appear to have been poisoned.
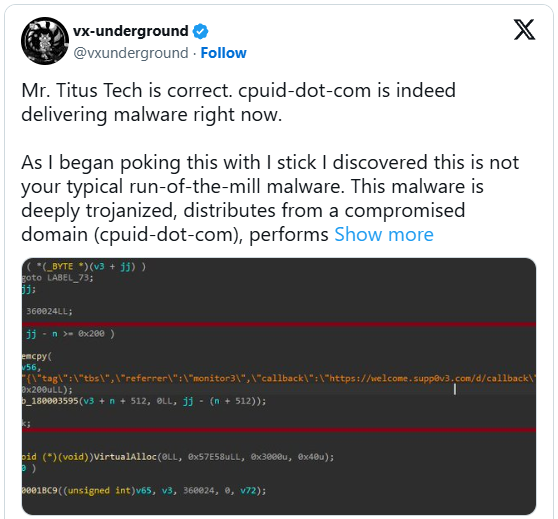
The externalized download chain was also confirmed by Igor’s Labs and @vxunderground, who reported that a fairly advanced loader using known techniques, tactics, and procedures (TTPs) is involved.
“As I began poking this with a stick, I discovered this is not your typical run-of-the-mill malware,” stated vxunderground.
“This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs file masquerading, is multi-staged, operates (almost) entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly.”
The researcher claims that the same threat group targeted users of the FileZilla FTP solution last month, suggesting that the attacker is focusing on widely used utilities.
The downloaded ZIP is flagged by 20 antivirus engines on VirusTotal, although not clearly identified. Some classify it as Tedy Trojan, and others as Artemis Trojan.
Some researchers on Virustotal say that the fake HWiNFO variant is an infostealer malware.
BleepingComputer has contacted CPUID to learn more about what happened, the date of the compromise, the affected versions, and what impacted users should do. A spokesperson has provided the following statement.
"Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display malicious links (our signed original files were not compromised). The breach was found and has since been fixed." - CPUID
The same person told us that the hackers hit them at a time when the main developer was away on holiday.
Currently, it appears that CPUID has fixed the problem and now serves clean versions for both CPU-Z and HWMonitor.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh