The average enterprise SOC receives over 4,400 alerts per day. Large organizations face 10,000 or more across 30 integrated security tools. Analysts investigate only 37% of them. The rest are triaged superficially, deprioritized, or ignored entirely.
This is not a staffing problem. It is a structural one.
Why Tuning Your SIEM Won’t Solve Alert Fatigue
Most organizations treat alert fatigue as a tuning problem. Adjust correlation rules. Raise severity thresholds. Add suppression filters. These measures reduce noise temporarily. Tuning addresses symptoms, not root causes.
Alert fatigue has five structural root causes that persist regardless of which SIEM you run:
- Volume exceeds human capacity. A single analyst can investigate 8–12 alerts per shift at full depth. At 4,400+ alerts per day, you would need 200+ full-time analysts to cover every alert manually.
- False positives erode trust. Over 50% of SIEM alerts are false positives. Some organizations report rates as high as 80%. When most alerts are noise, analysts treat all alerts as noise.
- Alerts lack context. A SIEM alert says something happened. It does not explain why it matters or what the attacker is trying to achieve. Analysts spend 56 minutes gathering context before investigation even begins.
- Static playbooks cannot adapt. Traditional SOAR playbooks execute identical steps regardless of context. The same response applies whether the target is an intern or the CFO.
- Analyst burnout creates a talent drain. Over 70% of SOC analysts report burnout. The average analyst stays in the role under three years.
61% of SOC teams have ignored alerts that later proved to be genuine security incidents. Alert fatigue is not an inconvenience. It is a direct threat vector.
Five Approaches to Reduce SIEM Alert Fatigue: Compared
Organizations have tried multiple strategies. Each has a specific role and a specific ceiling.
| Approach | Impact on Fatigue | Key Limitation |
|---|---|---|
| SIEM Tuning | Reduces noise 10–20% temporarily | New sources reintroduce noise; risk of suppressing real threats |
| Alert Aggregation | Reduces visible volume 20–30% | Clusters still require manual investigation |
| SOAR Playbooks | Covers 30–40% at maturity | 12–18 month deployment; $150K–$250K SOAR architect required |
| AI Alert Scoring | Improves prioritization accuracy | Better ranking is not investigation; analysts still investigate manually |
| Autonomous Investigation | 90%+ reduction in analyst workload; 100% alert coverage day one | Requires purpose-trained cybersecurity AI |
The critical distinction: Most approaches reduce the number of alerts analysts see. Autonomous investigation eliminates the bottleneck by cutting investigation time from hours to minutes.
How Autonomous Investigation Eliminates the Bottleneck
D3 Security’s Morpheus AI takes a fundamentally different approach. Instead of filtering or scoring alerts, it investigates every alert at L2 analyst depth in under two minutes, 24/7.
On every incoming alert, Morpheus AI:
- Queries the SIEM to pull correlated logs and enrichment data
- Correlates across the full stack (EDR, identity, cloud, and network) to build a cross-tool timeline
- Traces the attack path both vertically (initial access through execution) and horizontally (lateral movement across systems)
- Generates a contextual playbook at runtime from the evidence itself, not from a pre-authored template
- Self-heals integrations when vendor API changes break tool connections, keeping the investigation pipeline running
The result: analysts review completed investigation reports instead of building them. Escalation decisions go from hours to minutes. False positives are resolved with full documented reasoning.
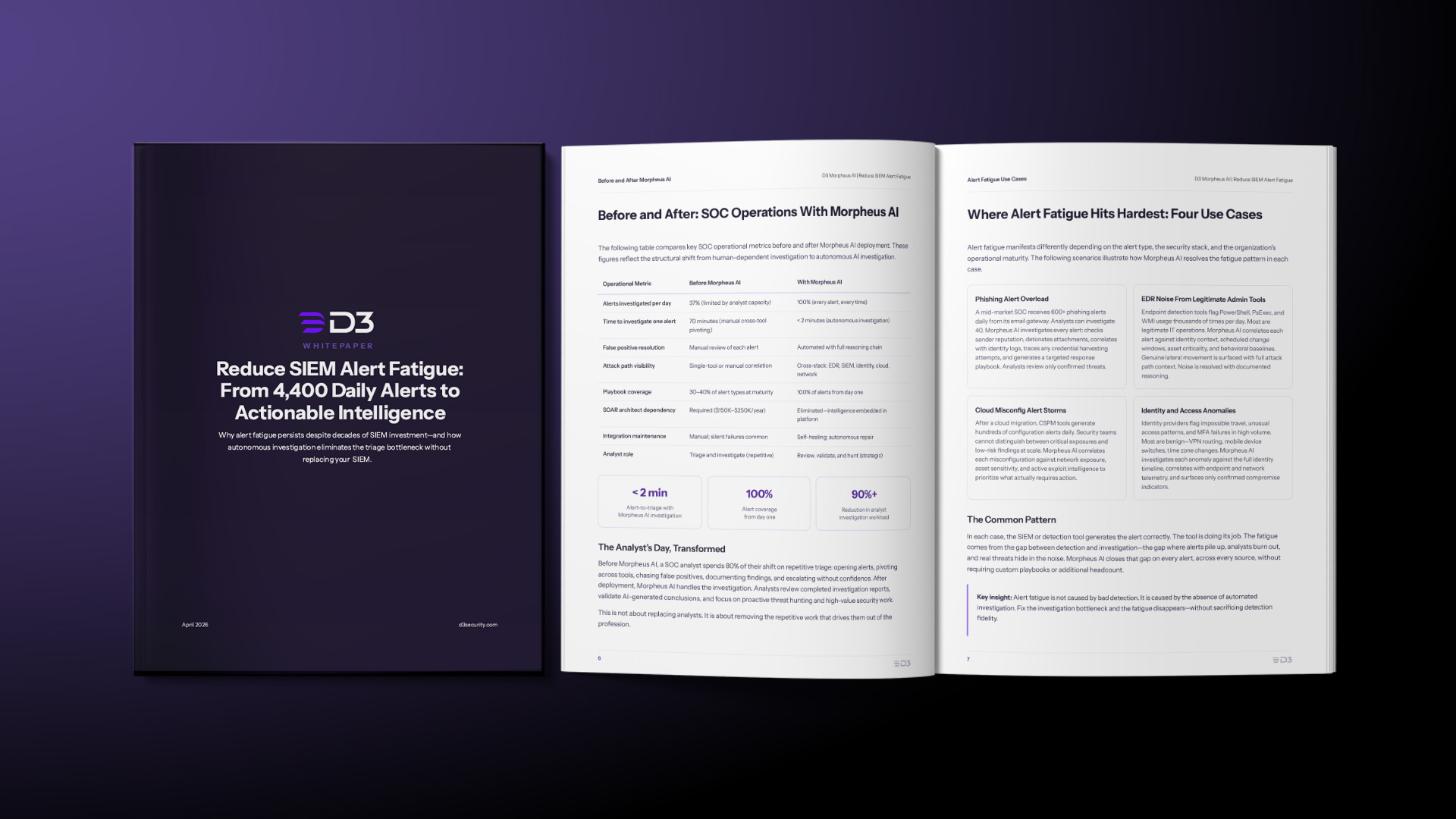
Before and After: What Changes
| Metric | Before Morpheus AI | With Morpheus AI |
|---|---|---|
| Alerts investigated/day | 37% | 100% |
| Investigation time | 70 minutes | <2 minutes |
| Playbook coverage | 30–40% at maturity | 100% from day one |
| SOAR architect | Required ($150K–$250K/yr) | Not required |
| Integration failures | Manual; silent failures | Self-healing; autonomous |
| Analyst role | Triage (repetitive) | Review, validate, hunt (strategic) |
The Right Questions to Ask Any Vendor
Not every product that claims to reduce SIEM alert fatigue delivers the same depth. Ask these questions when evaluating:
- Does the platform investigate alerts or only score them?
- What percentage of alert types does it cover on day one?
- Does it correlate across EDR, SIEM, identity, cloud, and network?
- Are playbooks generated from evidence or selected from templates?
- Is the AI purpose-trained for cybersecurity or a general-purpose LLM?
- Can it show its full reasoning chain for every investigation?
Read The Whitepaper: Reduce SIEM Alert Fatigue: From 4,400 Daily Alerts to Actionable Intelligence
Read The Glossary: What Is SIEM Alert Fatigue?
See Morpheus AI Investigate Your Alerts
Schedule a live demonstration with real data. Watch Morpheus AI investigate alerts across your stack in under two minutes.
The post SIEM Alert Fatigue Has Five Root Causes. Tuning Fixes Zero of Them. appeared first on D3 Security.
*** This is a Security Bloggers Network syndicated blog from D3 Security authored by Shriram Sharma. Read the original post at: https://d3security.com/blog/reduce-siem-alert-fatigue/