好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得通读整篇文章,理解其主要观点。 文章主要讨论了XDR(扩展检测与响应)在安全运营中心(SOC)中的应用。XDR在检测威胁方面表现出色,能够整合多个数据源,减少警报噪音。然而,文章指出XDR在调查和响应阶段存在不足。分析师仍然需要手动处理大量警报,导致工作压力大。 接下来,文章分析了XDR的五个结构性限制:无法自动调查、供应商锁定、关联上限、响应碎片化以及对人员的依赖。此外,虽然XDR厂商引入了AI协力工具,但并未完全消除手动调查的需求。 最后,文章介绍了Morpheus AI作为解决方案,能够自主进行调查和生成响应工作流程,从而弥补XDR的不足。 总结时,我需要涵盖XDR的优势、其在调查阶段的不足以及Morpheus AI的作用。同时要保持简洁,在100字以内。 </think> 文章指出,尽管XDR在威胁检测和信号关联方面表现出色,但它未能解决人工调查和响应的核心问题。分析师仍需手动处理复杂警报,导致工作量大增。Morpheus AI通过自主调查和生成响应方案弥补了这一缺口。 2026-4-10 20:19:32 Author: securityboulevard.com(查看原文) 阅读量:5 收藏
XDR solved visibility. It didn’t solve investigation. Here’s why the gap is structural.
There is a strange paradox in every SOC that has deployed Extended Detection and Response (XDR): the detection layer has never been better, and the analysts have never been more burned out.
Leading XDR platforms scored 100% technique-level detection in the 2025 MITRE ATT&CK Evaluations — an expanded round that tested cloud attack scenarios and reconnaissance for the first time. The technology detects threats. It correlates signals across endpoints, networks, email, cloud, and identity. It collapses hundreds of noisy alerts into a single correlated incident.
And then it hands that incident to a human analyst and says: “Investigate this.”
That handoff is where the SOC’s hardest problems live. And it is precisely where XDR stops.
Detection Is Not Investigation
XDR surfaces a correlated incident. The analyst must then determine whether the activity is actually malicious, trace the full scope of compromise, identify every affected system, build a timeline, decide on containment, and execute a coordinated response.
That investigation takes an average of 70 minutes per alert, according to industry research compiled in the AI SOC Market Landscape for 2025 report. Phishing-led breaches, by contrast, can succeed in under 60 minutes. The attacker finishes before the analyst completes a single investigation. XDR does not touch any of this. The platform automates response actions (isolate a host, block an IP) but does not automate the investigation that determines which actions to take.
Enterprise SOCs receive an average of 960 alerts per day. Large enterprises see over 3,000, generated by 30 or more security tools (SACR, 2025). At 70 minutes per investigation, a five-person analyst team working eight-hour shifts can thoroughly investigate roughly 34 alerts per day. The rest go uninvestigated. A 2025 study by Omdia commissioned by Microsoft (300 respondents across the US, UK, and ANZ) found that 42 percent of all alerts are never investigated at all.
This is not primarily a false positive problem. XDR correlation does reduce noise: the same Omdia study found 46 percent of alerts are false positives, lower than pre-XDR environments. What remains after correlation is higher-fidelity, more complex, and more time-consuming to investigate. The bottleneck has moved from “too many disconnected alerts” to “too many correlated incidents requiring manual investigation that nobody has capacity to perform.”
Five Architectural Limits
- Detection without investigation. XDR tells you something happened. It does not tell you what it means, how far it spread, or what to do about it. That is the analyst’s job, and XDR does not reduce that workload.
- Vendor lock-in. Native XDR works best within the vendor’s own ecosystem. Organizations that have invested millions in best-of-breed security tools cannot rip-and-replace their stack to match one vendor’s portfolio. Open XDR attempts to fix this, but cross-vendor correlation quality rarely matches native implementations.
- The correlation ceiling. XDR correlation is rule-based, mapped to known threat behaviors. Novel techniques, living-off-the-land attacks, and multi-stage campaigns that unfold in unexpected ways fall outside the correlation rules. The 2025 MITRE Evaluations highlighted this tension when vendors were challenged to distinguish between legitimate business activity and actual threats.
- Response fragmentation. XDR offers tactical actions: isolate an endpoint, block an IP, disable a user account. These are individual building blocks, not coordinated response workflows. For orchestrated response, you need a separate SOAR platform.
- Staffing dependency unchanged. XDR changes what analysts do. It does not reduce how many you need. Investigation, decision-making, and response coordination remain fully human-dependent. The burnout originates in investigation workload. XDR does not touch it.
Adding a Copilot Does Not Close the Gap
XDR vendors are bolting AI copilots onto their platforms: natural language querying, alert summarization, investigation suggestions. These are genuine improvements. They make analysts faster at manual investigation.
They do not eliminate manual investigation.
The AI suggests next steps. It does not execute them autonomously. It does not trace attack paths across tools outside its ecosystem. It does not generate coordinated response workflows at runtime. It does not detect and repair broken integrations.
Agentic XDR features, like Microsoft’s phishing triage agent, handle narrow use cases well. But the SOC needs coverage across all alert types, not one at a time.
The AI Autonomous SOC: From Detection to Decision
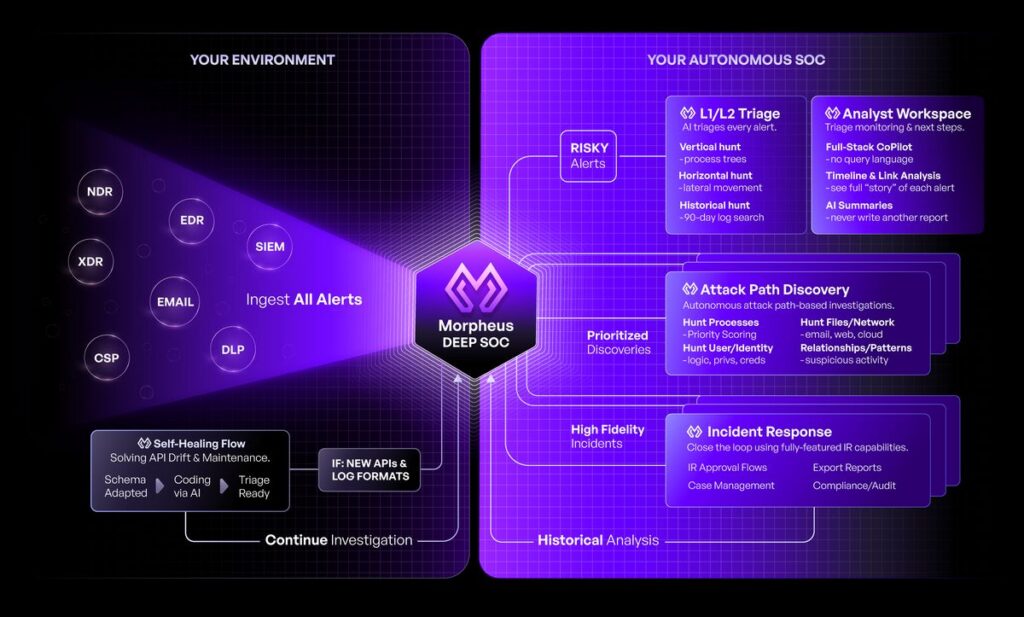
A purpose-built cybersecurity LLM changes the equation. Instead of surfacing correlated alerts for human investigation, the AI investigates every alert autonomously. It traces attack paths across any vendor’s telemetry. It generates contextual response workflows at runtime. It delivers triage reports comparable to L2 analyst depth, in minutes.
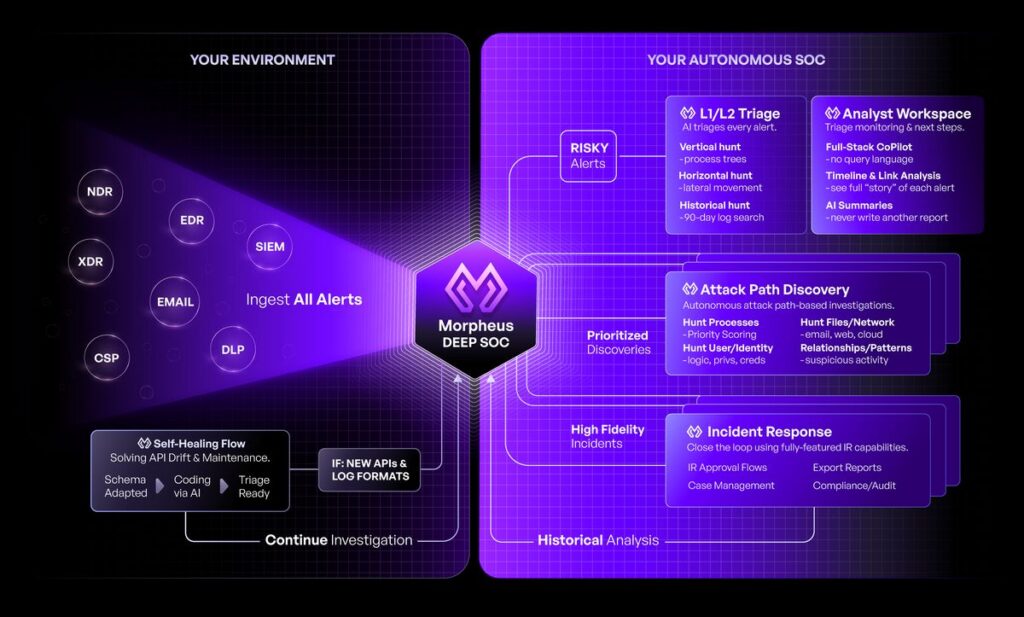
D3 Morpheus AI operationalizes this model:
- Autonomous investigation on every alert. Every single one. Multi-dimensional attack path discovery: vertical deep inspection into the origin tool, horizontal correlation across the full security stack.
- Vendor-agnostic by architecture. Morpheus AI sits above your existing detection layer. Keep your XDR. Keep your best-of-breed tools. Morpheus AI adds the investigation layer they lack.
- Contextual playbook generation. Bespoke response workflows generated per incident at runtime, with coordinated orchestration across domains.
- Self-healing integrations across 800+ tools. When APIs drift, Morpheus AI detects the change and generates corrective code autonomously. In production today.
- Predictable pricing. No token fees. No per-endpoint surprises.
The Honest Assessment
XDR is genuine progress. Unified visibility, strong detection, alert volume reduction, mature deployment ecosystem. For smaller teams without SIEM or SOAR, consolidated detection is a meaningful upgrade.
The question is whether detection and correlation alone constitute an adequate security architecture when adversaries move faster than your analysts can investigate. XDR gets you the first 20% of the problem. The remaining 80%, the investigation and response, is where the actual security outcome is determined.
Morpheus AI does not replace your XDR. It completes it.
Ready to see the difference? Schedule a Morpheus AI demonstration showing autonomous investigation compared side-by-side with your current XDR workflow.
Read the full analysis: The XDR Ceiling: Why Extended Detection and Response Stops Short of the Autonomous SOC
The post MITRE Gave XDR a Perfect Score. Then the Analyst Had to Investigate Alone appeared first on D3 Security.
*** This is a Security Bloggers Network syndicated blog from D3 Security authored by Shriram Sharma. Read the original post at: https://d3security.com/blog/xdr-detection-investigation-gap/
如有侵权请联系:admin#unsafe.sh