好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。用户的要求很明确,直接写文章描述,不需要开头。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是网络钓鱼已经发展成一个服务生态系统,称为PhaaS。这个系统由多个专业化角色组成,包括基础设施提供者、交付服务、凭证收集和资金套现。文章还提到PhaaS如何降低了网络犯罪的门槛,提高了攻击的规模和成功率。 接下来,我需要提取关键点:Phishing不再是单一战术,而是服务生态系统;涉及多个专业化角色;降低了犯罪门槛;提高了攻击效率和成功率;结合MFA绕过和AI技术提升能力。 然后,我要把这些点浓缩成一句话,不超过100字。确保涵盖主要概念:服务生态系统、专业化角色、门槛降低、效率提升以及技术因素。 最后,检查语言是否简洁明了,没有冗余信息。确保总结准确传达文章的核心内容。 </think> 网络钓鱼已发展为一个基于服务的生态系统(PhaaS),由专业化角色分工协作完成攻击生命周期的各个环节。这一模式降低了网络犯罪门槛,提高了攻击规模、效率和成功率,并结合MFA绕过技术和AI加速欺诈能力。 2026-4-10 16:19:54 Author: securityboulevard.com(查看原文) 阅读量:2 收藏
Phishing is no longer a standalone tactic. It has matured into a service-based ecosystem where specialized actors provide each component of an attack lifecycle, from infrastructure and delivery to credential harvesting and cash-out.
Flashpoint analysts, working with partner financial institutions, have observed a growing number of PhaaS operations operating with a level of coordination and specialization more commonly associated with legitimate software platforms. These ecosystems bring together phishing kit developers, infrastructure providers, spam delivery services, and financially motivated actors into a single, scalable pipeline for fraud.
This shift has significantly lowered the barrier to entry for cybercriminals while increasing the scale, efficiency, and success rate of phishing campaigns.
From Phishing Kits to a Service-Based Fraud Economy
PhaaS emerged from early phishing kits into a full cybercrime-as-a-service model built on commercialization, modular tooling, and operational scalability.
Early phishing activity relied on standalone kits — basic login pages and scripts that allowed attackers to collect credentials. Over time, operators began centralizing these capabilities into subscription-based platforms offering hosting, domain management, campaign tooling, and ongoing support.
Modern PhaaS platforms now operate similarly to legitimate SaaS providers:
- Subscription-based pricing models
- Prebuilt templates for major brands and services
- Integrated delivery mechanisms (email, SMS, QR phishing)
- Real-time dashboards for campaign tracking and credential harvesting
This model has made sophisticated phishing accessible to low-skill actors. Kits can cost as little as US$10, while full platforms enable large-scale campaigns for relatively modest monthly fees.
MFA Bypass and AI Are Reshaping Phishing Capabilities
As organizations adopted multifactor authentication (MFA), PhaaS operators adapted.
Modern platforms increasingly rely on adversary-in-the-middle (AiTM) techniques, using reverse proxy infrastructure to intercept login sessions in real time. This allows attackers to capture not only credentials, but also MFA tokens and session cookies, effectively bypassing traditional authentication controls.
At the same time, AI is accelerating the scale and effectiveness of phishing campaigns.
Threat actors are using AI to:
- Generate convincing, localized phishing lures
- Clone brand interfaces with high fidelity
- Optimize campaigns through automated testing and iteration
This combination of MFA bypass and AI-driven automation has transformed phishing from a volume-based tactic into a precision-driven access vector.
The PhaaS Pipeline: How the Ecosystem Operates
What distinguishes modern phishing operations is not just tooling, but coordination.
A typical PhaaS campaign follows a structured lifecycle:
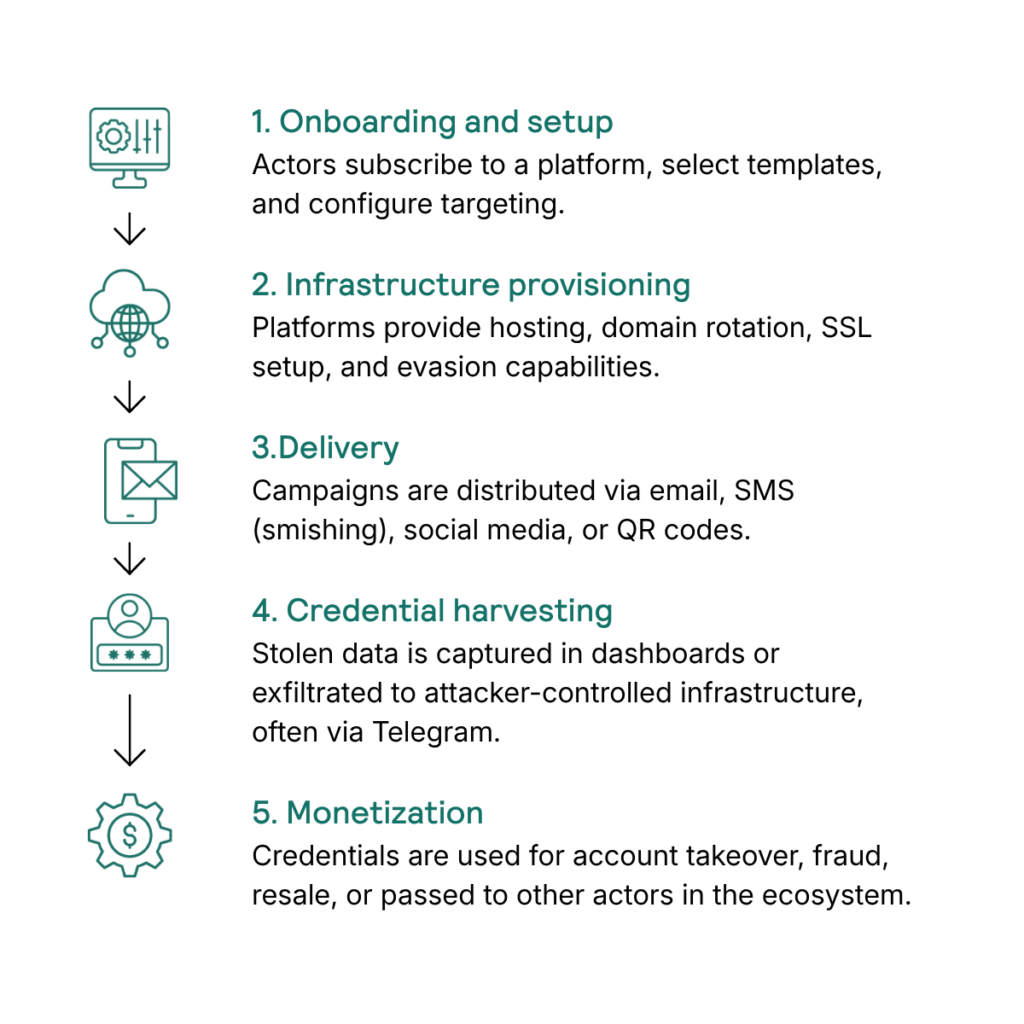
This pipeline is supported by a network of specialized providers, each responsible for a different stage of the attack lifecycle.
Infrastructure, Delivery, and Exfiltration Are Increasingly Specialized
Flashpoint analysis highlights how different actors focus on distinct parts of the ecosystem.
Infrastructure and Kit Development
Phishing kit developers provide increasingly sophisticated tooling, including:
- Reverse proxy (AiTM) capabilities for MFA bypass
- Anti-bot protections to evade researchers
- “Live panels” enabling real-time interaction with victims
Platforms such as GhostFrame, Rapid Pages, and MUH Pro Admin illustrate how these tools are being productized and distributed at scale.
SMS Delivery and Spoofing
Smishing has become a critical delivery vector.
Threat actors operate dedicated SMS gateway services capable of sending large volumes of messages via APIs or bulk uploads. Others actively seek advanced spoofing capabilities to bypass authentication controls such as SPF, DKIM, and DMARC, enabling phishing messages to appear legitimate at the protocol level.
Credential Exfiltration and Telegram Integration
Credential collection is increasingly automated and centralized.
Many campaigns exfiltrate stolen credentials directly to Telegram bots or channels, enabling real-time access to victim data. This infrastructure also allows for rapid scaling and coordination across actors participating in the same campaign or ecosystem.
From Credential Theft to Financial Monetization
The ultimate goal of PhaaS operations is monetization.
Stolen credentials are used to enable account takeover (ATO), which allows attackers to:
- Access financial accounts
- Lock out legitimate users
- Initiate fraudulent transactions
- Launch follow-on scams
Flashpoint analysis of actors such as “JUN JUN,” associated with the Squirtle group, illustrates how these operations extend into structured financial fraud and laundering.
Observed activity shows a progression from acquiring phishing logs (“fish material”) to targeting high-value accounts and ultimately laundering funds through complex mechanisms, including tax fraud and credit card repayment schemes designed to recycle illicit funds.
This highlights how phishing is only the entry point into a broader fraud pipeline.
A Distributed Ecosystem of Threat Actors
The PhaaS landscape is not controlled by a single group, but by a network of loosely connected actors and clusters.
Examples include:
- Fluffy Spider: Focused on large-scale infrastructure deployment and domain generation
- IVAN: A more exclusive, high-tier operation leveraging SEO poisoning and advanced evasion techniques
- Smishing Triad: A highly coordinated group conducting global SMS phishing campaigns
- System Bot: A modular phishing toolkit with credential harvesting and OTP bypass capabilities
These actors operate across different regions and languages but demonstrate comparable levels of technical capability and operational maturity.
Many of these groups function with enterprise-like structures, including support teams, affiliate models, and performance-based operations, further reinforcing the industrialization of phishing-driven fraud.
Law Enforcement Pressure Is Increasing, but the Model Persists
Recent takedowns, including operations targeting platforms such as Tycoon 2FA, demonstrate growing coordination between public and private sector defenders.
These efforts have:
- Disrupted infrastructure
- Increased operational costs for threat actors
- Accelerated collaboration between intelligence providers and law enforcement
However, the underlying PhaaS model remains resilient.
Even as major platforms are dismantled, operators frequently rebrand, migrate infrastructure, or fragment into smaller services. The demand for scalable, low-cost phishing capabilities continues to sustain the ecosystem.
What This Means for Security Teams
Phishing-as-a-service has evolved from a tactic to an ecosystem that industrializes fraud.
Flashpoint assesses that the increasing coordination between phishing kit developers, infrastructure providers, and financial fraud actors will continue to drive large-scale credential harvesting and account takeover activity targeting global organizations.
For defenders, this means that effective mitigation requires more than user awareness and traditional controls. Organizations must account for:
- MFA bypass techniques such as AiTM
- Rapid infrastructure rotation and evasion
- The integration of phishing into broader fraud and access broker pipelines
Protecting Your Organization from the PhaaS Ecosystem
Understanding how phishing ecosystems operate — from infrastructure and delivery to monetization — is critical for disrupting attacks before they result in fraud.
Flashpoint provides intelligence that helps organizations track phishing campaigns, identify emerging threat actors, and detect compromised credentials in real time. By correlating activity across the full attack lifecycle, security teams can better anticipate threats and respond before they escalate.
To learn how Flashpoint can support your team with actionable intelligence on phishing and fraud ecosystems, schedule a demo.
如有侵权请联系:admin#unsafe.sh