好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,抓住关键点。 文章主要讲的是EngageLab SDK的一个漏洞,影响了5000万台安卓设备,其中3000万是加密钱包用户。微软的研究人员发现了这个漏洞,它允许应用绕过安卓的安全沙盒保护,访问用户的隐私数据。漏洞被修复后,相关应用从Google Play下架了,但没有证据显示被利用过。 接下来,我需要把这些信息浓缩成一句话。要包含漏洞的影响范围、问题的严重性以及修复情况。同时,避免使用“这篇文章”或“内容总结”这样的开头。 可能的结构是:EngageLab SDK漏洞影响50M安卓设备和30M加密钱包用户,允许应用绕过安全措施访问隐私数据。已修复并移除相关应用。 检查一下字数是否在100字以内,并且信息准确无误。 </think> EngageLab SDK漏洞影响50M安卓设备和30M加密钱包用户,允许应用绕过安全措施访问隐私数据。已修复并移除相关应用。 2026-4-10 08:41:39 Author: securityaffairs.com(查看原文) 阅读量:13 收藏
EngageLab SDK flaw opens door to private data on 50M Android devices

A flaw in EngageLab SDK exposed up to 50M Android users, including 30M crypto wallets, letting apps bypass security and access private data.
Microsoft researchers found a critical flaw in EngageSDK that lets apps bypass Android sandbox protections and access private data. The flaw put millions of users, including over 30M crypto wallet installs, at risk.
Developers fixed it in version 5.2.1 after coordinated disclosure, and vulnerable apps were removed from Google Play. The good news is that no active exploitation has been confirmed, but the case highlights risks from third-party SDKs widely used in mobile apps.
“As mobile wallets and other high‑value apps become more common, even small flaws in upstream libraries can impact millions of devices. These risks increase when integrations expose exported components or rely on trust assumptions that aren’t validated across app boundaries.” reads the report published by Microsoft.
“Because Android apps frequently depend on external libraries, insecure integrations can introduce attack surfaces into otherwise secure applications.”
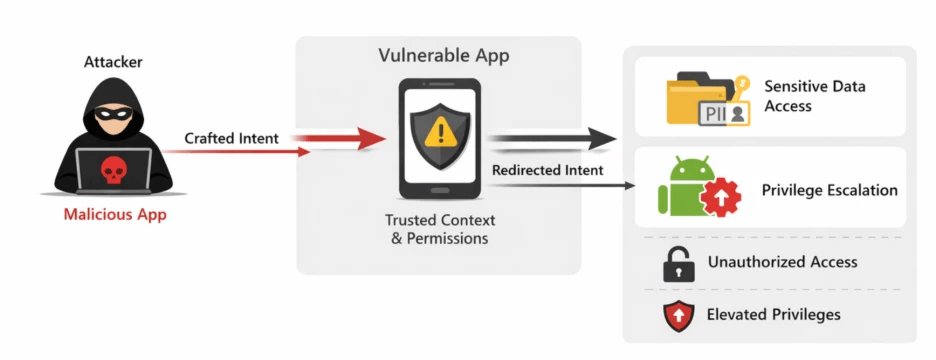
Android protects apps by isolating them with unique IDs, private storage, and controlled communication through intents. The EngageLab SDK flaw breaks this protection using an intent redirection issue.
“Intent Redirection occurs when a threat actor manipulates the contents of an intent that a vulnerable app sends using its own identity and permissions.
In this scenario, the threat actor leverages the trusted context of the affected app to run a malicious payload with the app’s privileges.” continues the report. “This can lead to:
- Unauthorized access to protected components
- Exposure of sensitive data
- Privilege escalation within the Android environment

A malicious app can send a crafted intent to a vulnerable app, which then processes it and unknowingly sends a new intent with its own permissions. This allows the attacker to act with higher privileges.
The problem comes from an exported component called MTCommonActivity, automatically added during the build process. Many developers miss it because it only appears in the merged app configuration. Since it is exported, any app on the device can interact with it. This component reads attacker-controlled data and builds a new intent, but instead of keeping it safe, it creates a targeted intent that directly calls internal components.
The flaw becomes more dangerous because it uses unsafe flags that grant read and write access to data. Once triggered, the attacker can access private files through the app’s content providers, even if those were not meant to be exposed.
In simple terms, this vulnerability lets one app trick another into opening its doors, giving access to sensitive data and bypassing Android’s core security protections.
Many affected apps belong to the crypto and digital wallet ecosystem, making the flaw particularly severe. Microsoft confirmed the issue in multiple Google Play apps before disclosure. Wallet apps alone reached over 30 million installs, while total exposure across all affected apps exceeded 50 million.
Microsoft discovered the vulnerability in EngageLab SDK v4.5.4 and reported it in April 2025, later involving the Android Security Team in May due to Play Store impact. EngageLab fixed the issue in version 5.2.1, released on November 3, 2025, by making the vulnerable component non-exported, blocking access from other apps.
“To keep your apps secure, always review the merged Android manifest, especially when you incorporate third‑party SDKs. This helps you identify any components or permissions that might affect your app’s security or behavior.” concludes Microsoft.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Android)
如有侵权请联系:admin#unsafe.sh