好的,我需要帮用户总结这篇文章的内容,控制在100个字以内,而且不需要特定的开头。首先,我得通读整篇文章,抓住主要点。 文章主要讲的是退税欺诈在网络安全中的持续威胁。威胁者通过获取身份数据、绕过验证、使用社会工程学和复杂的提现方法来进行欺诈。文章还提到这些活动在Telegram和暗网论坛中活跃,威胁者分享教程和工具,使得欺诈手段不断进化。 接下来,我需要将这些要点浓缩成一句话,确保不超过100字。重点包括:退税欺诈、网络犯罪、身份数据、验证绕过、社会工程学、提现方法以及社区支持。 可能的结构是:“退税欺诈在网络安全中持续存在,威胁者利用身份数据、验证绕过、社会工程学和复杂提现方法进行攻击,并通过社区分享工具和技术。” 这样既涵盖了主要威胁手段,也提到了社区的作用。 最后检查一下字数和表达是否流畅,确保信息准确传达。 </think> 退税欺诈在网络安全中持续存在,威胁者利用身份数据、验证绕过、社会工程学和复杂提现方法进行攻击,并通过社区分享工具和技术。 2026-4-9 20:47:20 Author: securityboulevard.com(查看原文) 阅读量:1 收藏
Tax refund fraud remains a persistent and evolving threat within cybercrime and fraud communities. Threat actors actively advertise and refine schemes designed to file fraudulent returns and intercept refund payments from legitimate taxpayers.
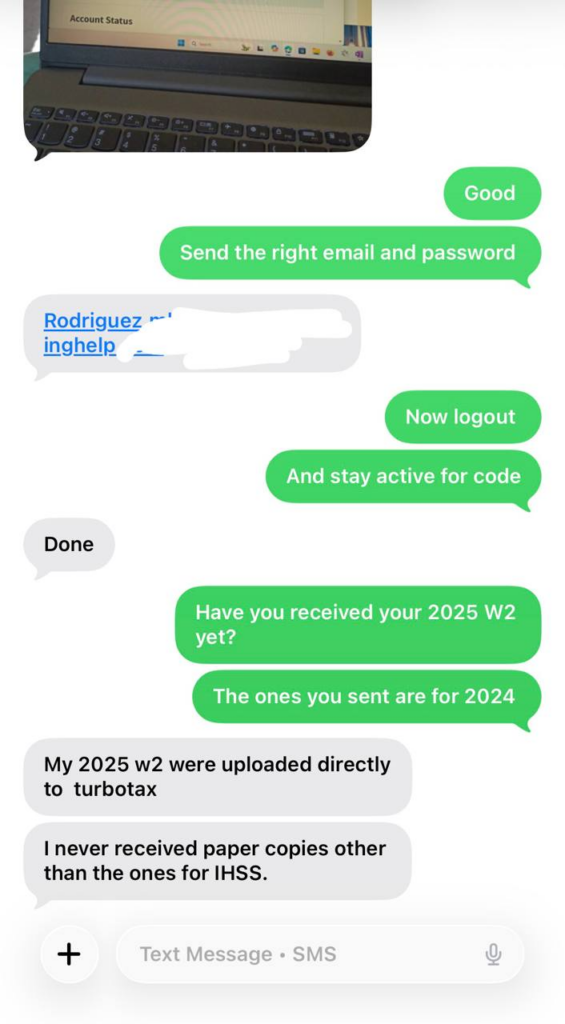
Across illicit forums, Telegram channels, and marketplaces, discussions point to a structured ecosystem built around identity data, social engineering, verification bypass, and increasingly sophisticated cash-out methods.
For intelligence teams, these conversations provide insight into how fraud operations are scaling and where defenses are being tested and adapted.
The Structure of Modern Tax Refund Fraud Schemes
At a high level, most tax refund fraud schemes follow a consistent model: obtain identity data, file a fraudulent return, bypass verification, and extract funds.
Flashpoint analysis shows that threat actors focus on several key stages:
- Sourcing victims or identity “fullz” (complete PII packages)
- Obtaining or bypassing identity and return verification
- Leveraging social engineering to support fraud workflows
- Using tutorials and shared methods to maximize refund amounts
- Converting refunds into cash or cryptocurrency
These stages are not isolated. They are supported by overlapping communities that specialize in identity theft, financial fraud, and account access.
Identity Data as the Foundation of Fraud
The success of tax refund fraud depends heavily on access to high-quality identity data.
Threat actors typically rely on “fullz,” which include a victim’s name, date of birth, address, and Social Security number. In some cases, fraudsters also recruit “clients” or “tax heads” — individuals who knowingly or unknowingly provide accurate tax documents and assist in bypassing verification steps.
This distinction is important. While fullz can be purchased or harvested at scale, clients often provide more reliable and current information, increasing the likelihood that a fraudulent return will be accepted.
Threat actors also seek additional data points to legitimize filings, including:
- Identity Protection (IP) PINs
- Adjusted Gross Income (AGI) from previous tax years
- Access to tax preparation accounts or IRS records
These elements are frequently obtained through compromised accounts, social engineering, or access to verified identity platforms.
Verification Bypass as a Critical Enabler
Filing a fraudulent return is only part of the process. Successfully passing identity and return verification is often the deciding factor.
Threat actors place significant emphasis on accessing or creating verified accounts tied to identity systems used by government agencies. These accounts allow fraudsters to:
- Retrieve tax transcripts and historical data
- Respond to IRS verification requests
- Validate identity during filing and follow-up processes
In many cases, fraudsters rely on social engineering to obtain this access. Common approaches include:
- Creating fake job postings or tax preparation services to collect documents
- Running romance or employment scams to gather personal information
- Coercing victims into creating or sharing verified accounts
Threat actors also prepare for additional verification steps, such as responding to IRS letters or completing phone and in-person identity checks. These workflows often involve scripts, impersonation tactics, and coordination with cooperating “clients.”
Fraud Tactics Are Increasingly Systematic
Beyond basic filing, threat actors share detailed tutorials and playbooks designed to maximize refunds and improve success rates.
These often include:
- Using real or falsified income data to inflate returns
- Targeting specific tax credits, such as the Child Tax Credit (CTC), Earned Income Tax Credit (EITC), or Employer Retention Credit (ERC)
- Claiming dependents or benefits that increase refund amounts
- Adapting methods based on state-specific programs or eligibility requirements
A notable development is the use of fraudulent income submission schemes, where threat actors pre-populate tax records with inflated income and withholding data before filing a return.
This process typically involves:
- Submitting false wage data to the IRS or Social Security Administration using employer identifiers
- Waiting for the data to appear on official tax transcripts
- Filing a return that matches the fabricated figures
By aligning submitted data with filed returns, fraudsters increase the likelihood that filings will appear legitimate during verification.
Social engineering plays a central role throughout the fraud lifecycle—and not just at the initial data collection stage.
Threat actors also target:
- IRS representatives, attempting to verify fraudulent returns over the phone
- Clients, persuading them to attend verification appointments or share official correspondence
- Government offices, including outreach to congressional staff to resolve refund holds
In some cases, fraudsters use AI-generated communications to scale these efforts, including drafting messages designed to appear legitimate and urgent.
These tactics highlight how fraud operations extend into real-world processes and human interactions, not just digital systems.
Cash-Out Methods Continue to Evolve
Once a fraudulent refund is secured, the focus shifts to converting funds into usable, untraceable assets.
Common cash-out methods include:
- Direct deposits into accounts controlled by the fraudster
- Accounts opened by “clients” on behalf of the operation
- Digital banking platforms and payment apps
- Prepaid cards and alternative financial instruments
Increasingly, threat actors are moving funds into cryptocurrency to reduce traceability. This often involves:
- Using verified exchange accounts to pass KYC requirements
- Converting refunds into Bitcoin or other assets
- Transferring funds to wallets controlled by the fraudster
In some workflows, the entire process — from filing to conversion — can occur within a single mobile or digital ecosystem.
Fraud Communities Enable Scale and Adaptation
Tax refund fraud does not operate in isolation. It is embedded within broader fraud ecosystems where identity data, tools, and tutorials are continuously shared.
Telegram remains a central hub for this activity, with large channels distributing:
- Screenshots of successful refunds
- Tutorials and “sauce” (paid or free methods)
- Listings for identity data and services
Dark web forums also host discussions, though typically with lower volume and higher signal.
The structure of these communities allows fraud techniques to spread quickly, adapt to changing controls, and persist across multiple platforms.
What This Means for Threat Intelligence Teams
Tax refund fraud reflects a broader shift toward operationally mature, community-driven fraud ecosystems.
Flashpoint analysts assess that these schemes are becoming more structured, with clearly defined workflows for identity acquisition, verification bypass, and monetization.
For security and intelligence teams, this has several implications:
- Identity data remains a critical point of exposure across multiple fraud types
- Verification systems are actively targeted and tested by threat actors
- Social engineering continues to bridge technical and human vulnerabilities
- Fraud techniques are rapidly shared, refined, and scaled across communities
Understanding how these components connect is essential for identifying emerging fraud patterns and anticipating how threat actors will adapt.
Supporting Security Teams with Threat Intelligence During Tax Season and Beyond
Understanding how tax fraud schemes are executed from identity sourcing to verification bypass and cash-out provides critical context for detecting and disrupting fraudulent activity.
Flashpoint delivers leading intelligence that helps organizations monitor fraud communities, track evolving tactics, and identify emerging schemes before they scale. By combining primary source collection with contextual analysis, security teams can move from reactive detection to proactive defense.
To learn how Flashpoint can support your team with real-time intelligence and analysis, request a demo.
Frequently Asked Questions About Tax Refund Fraud
What is tax refund fraud?
Tax refund fraud is a form of identity-based financial crime in which threat actors file fraudulent tax returns using stolen or manipulated personal information to obtain refund payments before the legitimate taxpayer files.
How do threat actors obtain the information needed to commit tax fraud?
Threat actors typically rely on stolen identity data, often referred to as “fullz,” which includes a victim’s name, date of birth, address, and Social Security number. This information is sourced from infostealer malware logs, phishing campaigns, data breaches, social engineering, and illicit marketplaces.
In some cases, fraudsters also recruit “clients” who provide real tax documents or assist in verification processes.
How do fraudsters bypass identity verification for tax returns?
Fraudsters use a combination of tactics to bypass identity and return verification, including:
- Accessing or creating verified identity accounts used for tax authentication
- Obtaining prior-year tax data such as adjusted gross income (AGI)
- Using stolen or socially engineered identity protection (IP) PINs
- Responding to IRS verification requests using scripts, impersonation, or cooperating individuals
These methods allow fraudulent returns to appear legitimate during processing.
What are common tax fraud tactics used by threat actors?
Common tactics include:
- Filing returns using stolen personal information
- Inflating income or tax withholding amounts to increase refunds
- Claiming fraudulent dependents or tax credits
- Submitting false wage data to government systems before filing
- Using real tax forms combined with manipulated data
These approaches are often shared and refined within fraud communities.
What is a “fullz” in tax fraud?
A “fullz” refers to a complete set of personally identifiable information (PII) about an individual, typically including name, date of birth, address, and Social Security number. Fullz are used by fraudsters to file tax returns, open accounts, and conduct other identity-based financial crimes.
How do fraudsters cash out fraudulent tax refunds?
After a fraudulent return is accepted, threat actors typically attempt to convert the refund into usable funds through:
- Direct deposits into controlled or intermediary accounts
- Accounts opened by recruited participants
- Digital banking platforms or prepaid cards
- Cryptocurrency conversion using verified exchange accounts
The goal is to move funds quickly and reduce traceability.
Why is tax refund fraud difficult to detect?
Tax refund fraud can be difficult to detect because it leverages legitimate systems and processes, including real identity data, authentic tax preparation services, and verified accounts. Fraudsters also adapt quickly by sharing new techniques and bypass methods across online communities.
How do fraud communities support tax refund fraud schemes?
Fraud communities, particularly on platforms like Telegram and dark web forums, enable threat actors to share tutorials, tools, and identity data. These communities accelerate the spread of techniques, allowing fraud schemes to scale and evolve rapidly.
What should security and fraud teams monitor to detect tax fraud activity?
Teams should monitor for:
- Unusual access to identity data or tax-related accounts
- Indicators of compromised credentials or identity verification systems
- Discussions of tax fraud methods, tutorials, or cash-out techniques in illicit communities
- Patterns in fraudulent filings or refund activity
Incorporating intelligence from fraud communities can provide early visibility into emerging tactics.
How does Flashpoint help organizations detect and prevent tax refund fraud?
Flashpoint helps organizations detect and respond to tax fraud by providing intelligence on how threat actors source identity data, bypass verification systems, and cash out fraudulent returns.
Through primary source collection across platforms like Telegram and dark web forums, Flashpoint enables teams to monitor fraud communities, identify emerging tactics, and understand how schemes are evolving. This intelligence helps organizations move from reactive detection to more proactive identification of fraud risk.
如有侵权请联系:admin#unsafe.sh