
嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读文章,抓住主要信息。 文章讲的是VENOM这个新的钓鱼服务攻击平台,专门针对高管的凭证。攻击者使用了高度个性化的钓鱼邮件,模仿微软的 SharePoint 通知。邮件里有随机的HTML噪音和伪造的邮件线程,增加了可信度。 然后,他们用Unicode生成QR码,引导受害者到过滤页面,确保只有真实目标会被重定向到钓鱼平台。如果通过了测试,受害者会被带到一个收集凭证的页面,模拟微软登录流程,窃取MFA代码和会话令牌。 VENOM还使用了设备代码钓鱼方法,让受害者批准流氓设备访问他们的微软账户。这种方法在过去一年非常流行,因为它的有效性以及对密码重置的抵抗力。 最后,研究人员指出MFA不再足够作为防御措施,建议高管使用FIDO2认证,并实施更严格的条件访问策略来阻止令牌滥用。 总结下来,我需要把这些关键点浓缩到100字以内。确保涵盖VENOM是什么、攻击方式、技术手段以及防御建议。 </think> 威胁行为者利用未公开的“VENOM”钓鱼服务攻击高管凭证。该平台通过高度个性化的钓鱼邮件模仿微软通知,并使用Unicode QR码引导至过滤页面。通过实时模拟登录流程窃取凭证和MFA代码。建议高管启用FIDO2认证并加强访问控制以应对威胁。 2026-4-9 21:46:21 Author: www.bleepingcomputer.com(查看原文) 阅读量:40 收藏

Threat actors using a previously undocumented phishing-as-a-service (PhaaS) platform called “VENOM” are targeting credentials of C-suite executives across multiple industries.
The operation has been active since at least last November and appears to target specific individuals who serve as CEOs, CFOs, or VPs at their companies.
VENOM also seems to be closed access, as it has not been promoted on public channels and underground forums, thus reducing its exposure to researchers.
The VENOM attack chain
The phishing emails, observed by researchers at cybersecurity company Abnormal, impersonated Microsoft SharePoint document-sharing notifications as part of internal communication.
The messages are highly personalized and include random HTML noise such as fake CSS classes and comments. The attacker also injects fake email threads tailored to the target, increasing credibility.
A QR code rendered in Unicode is provided for the victim to scan for access. The trick is designed to bypass scanning tools and shift the attack to mobile devices.
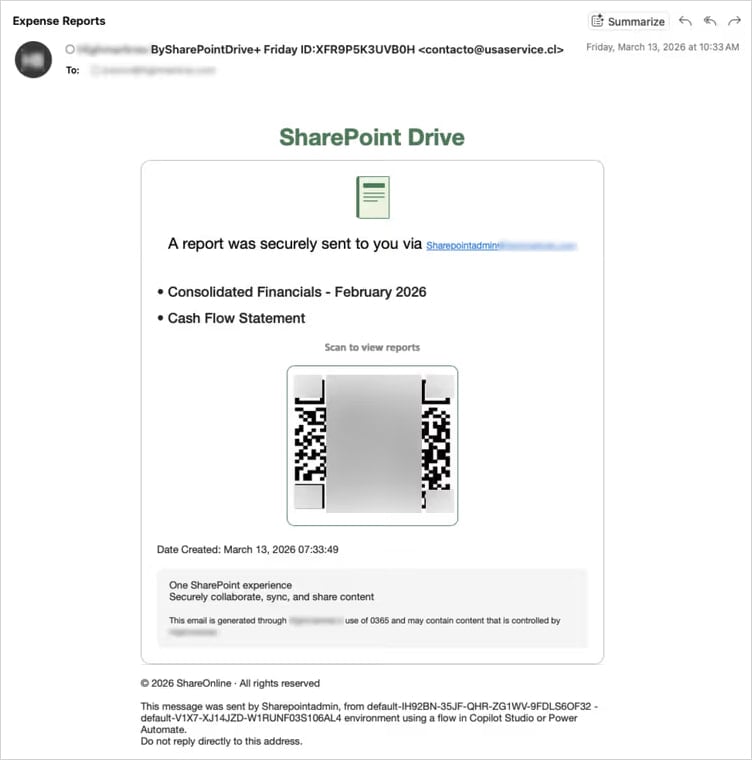
Source: Abnormal
“The target's email address is double Base64-encoded in the URL fragment—the portion after the # character,” Abnormal researchers explain.
“Fragments are never transmitted in HTTP requests, making the target's email invisible to server-side logs and URL reputation feeds.”
When the victim scans the QR code, they are taken to a landing page that serves as a filter for security researchers and sandboxed environments, ensuring that only real targets are redirected to the phishing platform. Users outside the threat actor's interest are redirected to legitimate websites to reduce suspicion.
Those who pass the tests are taken to a credential-harvesting page that proxies a Microsoft login flow in real time, relaying credentials and multi-factor authentication (MFA) codes to Microsoft APIs and capturing the session token.
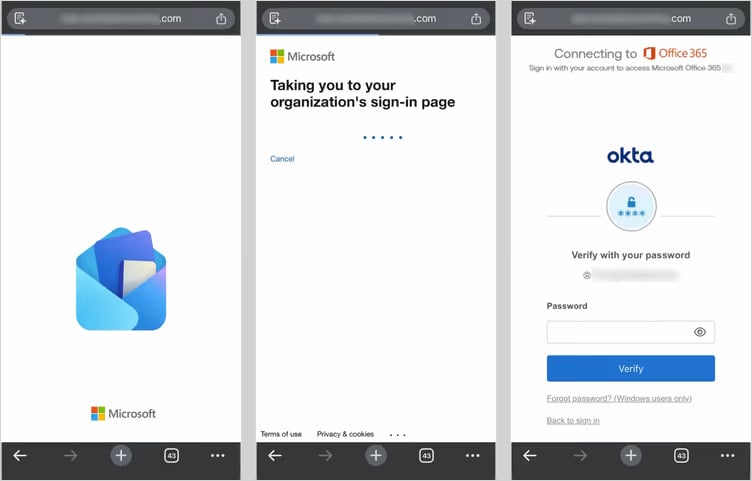
Source: Abnormal
Apart from the adversary-in-the-middle (AiTM) method, Abnormal has also observed a device-code phishing tactic in which the victim is tricked into approving access to their Microsoft account for a rogue device.
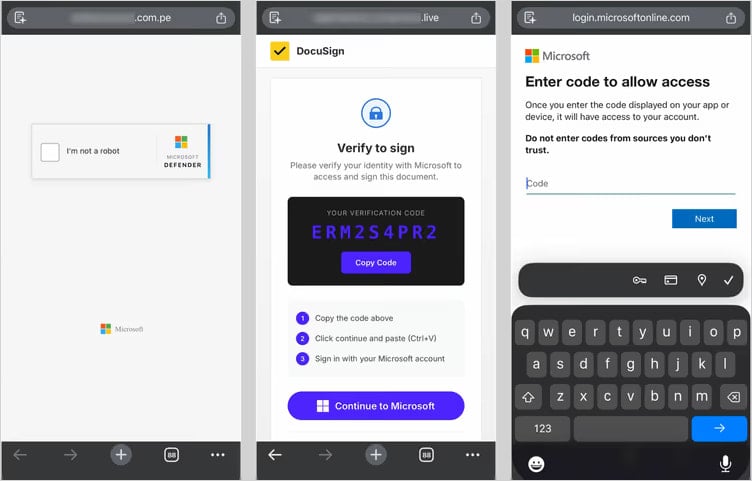
Source: Abnormal
This method has become very popular over the past year due to its effectiveness and resistance to password resets, with at least 11 phishing kits currently offering it as an option.
In both methods, VENOM quickly establishes persistent access during the authentication process. In the AiTM flow, it registers a new device on the victim’s account. In the device code flow, it obtains a token that also provides access to the account.
The researchers note that MFA is no longer sufficient as a defense. C-suite executives should use FIDO2 authentication, disable the device code flow when not needed, and block token abuse by implementing stricter conditional access policies.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

