好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得通读整篇文章,抓住主要观点。 文章主要讲的是网络安全中的防御者如何通过自动化和AI来提升防御能力,从而迫使攻击者改变策略。提到了“智能SOC”的概念,这是一种能够主动预测攻击并自动防御的模式。文中还详细介绍了这种模式的两层结构:威胁防护平台和操作层的AI代理。最后,文章讨论了这种转变对安全团队角色的影响以及实现这一目标的阶段。 接下来,我需要将这些要点浓缩到100字以内。要确保涵盖智能SOC的核心概念、其带来的变化以及对未来的展望。同时,语言要简洁明了,避免专业术语过多。 可能的结构是:先点明主题(智能SOC),然后说明其如何改变防御模式(从被动到主动),接着提到AI和自动化的作用,最后简述对安全团队的影响和未来趋势。 现在开始组织语言: “文章探讨了智能安全运营中心(SOC)如何通过自动化和AI从被动防御转向主动预测攻击。智能SOC结合自主防御与人类判断,使安全团队专注于战略决策。未来,角色将从响应转向预防与优化。” 这样大约80字左右,符合要求。 </think> 文章探讨了智能安全运营中心(SOC)如何通过自动化和AI从被动防御转向主动预测攻击。智能SOC结合自主防御与人类判断,使安全团队专注于战略决策。未来,角色将从响应转向预防与优化。 2026-4-9 19:0:0 Author: www.microsoft.com(查看原文) 阅读量:16 收藏
Every major shift in cyberattacker behavior over the past decade has followed a meaningful shift in how defenders operate. When security operation centers (SOCs) deployed endpoint detection and response (EDR)—and later extended detection and response (XDR)—security teams raised the bar, pushing cyberattackers beyond phishing, commodity malware, and perimeter‑based attacks and into cloud infrastructure built for scale and speed.
That pattern continued as defenders embraced automation and AI to manage expanding digital estates. SOCs were often early scale adopters—using machine learning to reduce noise, improve visibility, and respond faster across growing environments. Cyberattackers became more targeted and multistage, moving deliberately across identities, endpoints, cloud resources, and email, where detection was hardest. Success increasingly depended on moving fast enough to act before analysts could connect the dots. Even with this progress, security operations (SecOps) still feel asymmetrical: threat actors only need to be right once, while defenders are judged by every miss. If defense depends on human intervention to begin, defense will always feel asymmetrical.
To change the outcome, SOCs must change how defense itself works. This is the agentic SOC: where security delivers adaptive, autonomous defense, freeing defenders for strategic, high‑impact work. In this series, we’ll break down what that shift requires, what early experimentation has taught us, and where organizations can start today. Read more about how some organizations moving toward the agentic SOC and access a foundational roadmap for this transformation in our new whitepaper, The agentic SOC: Your teammate for tomorrow, today.
What we mean by “the agentic SOC”
At its core, the agentic SOC is an operating model that shifts security from reacting to incidents to anticipating how cyberattackers move—and actively reshaping the environment to cut off their paths.
It brings together a platform that can increasingly defend itself through built-in autonomous defense, with AI agents working alongside humans to accelerate investigation, prioritization, and action—so teams spend less time on execution and more time on judgment, risk, and the decisions that matter.
How does that change day-to-day work? Imagine a credential theft attempt. Built-in defenses automatically lock the affected account and isolate the compromised device within seconds—before lateral movement can begin. At the same time, an AI agent initiates an investigation, hunting for related activity across identity, endpoint, email, and cloud signals, and correlating everything into a single view.
When an analyst opens their queue, the “noise” of overwhelming alerts is already gone. Evidence has been pre-assembled. Likely next steps are suggested. The analyst can start right away by answering higher impact questions: Is this part of a broader campaign? Should this authentication method be hardened? Are there related techniques this cyberattacker commonly uses that the environment is still exposed to?
In today’s SOC, we see that sequence often takes hours—and the proactive improvement is very limited, if it ever happens; there’s simply not enough time. In an agentic SOC, it happens in minutes, and teams can spend the time they’ve gained on deeper investigation, systemic hardening, and reducing the likelihood of repeat cyberattacks.
A layered model for the agentic SOC
This model works because an agentic SOC is built on two distinct, but interdependent layers. The first is an underlying threat protection platform that has fundamentally evolved how cyberattacks are defended against and disrupted. High confidence cyberthreats are handled automatically through deterministic, policy-bound controls built directly into the platform. Known attack patterns are blocked in real time—without deliberation or creativity—shielding the environment from machine-speed cyberthreats before scarce human attention or token intensive reasoning is required. This disruption layer is not optional; it is the prerequisite that makes an agentic SOC safe, scalable, and sustainable.
The second layer operates at the operational level, where agents take on tough analysis and correlation work to dramatically increase the leverage of security teams and shift focus from uncovering insight to acting on it. These agents reason over evidence, coordinate investigations, orchestrate response across domains, and learn continuously from outcomes. Over time, they help identify recurring attack paths, surface gaps in posture, and recommend changes that make the environment harder to exploit—not just faster to respond.
Together, they transform the SOC from a reactive workflow engine into a resilient system.
What’s real now, and why there’s reason for optimism
The optimism around our view of the agentic SOC comes from operational discipline and proven, real-world impact. Autonomous attack disruption has been operating at scale for years.
Read more about how Microsoft Defender establishes confidence for automatic action.
Attacks like ransomware are disrupted in an average of three minutes, and tens of thousands of attacks are contained every month by isolating compromised users and devices before lateral movement can take hold. This all done with a 99.99% confidence rating, so SOC teams can trust in its efficacy.
Building on that proven foundation, newer capabilities like predictive shielding extend autonomous defense further—anticipating how cyberattacks are likely to progress and proactively restricting high-risk paths or assets during an intrusion.
Read the case study about how predictive shielding in Microsoft Defender stopped Group Policy Object (GPO) ransomware before it started
Together, these system-level protections show that platforms can safely intervene earlier in the cyberattack chain without introducing unnecessary disruption.
Agentic capabilities are also being similarly scoped. Internally, we’ve been testing task agents for triage and investigations under our expert supervision of our defenders. In live environments, these agents automate 75% of phishing and malware investigations. We’ve also tested agents on more complex analytical tasks, such as assessing exposure to specific vulnerabilities—work that once required a full day of engineering effort and can now be completed in less than an hour by an agent.
How day-to-day SOC work will change in the future
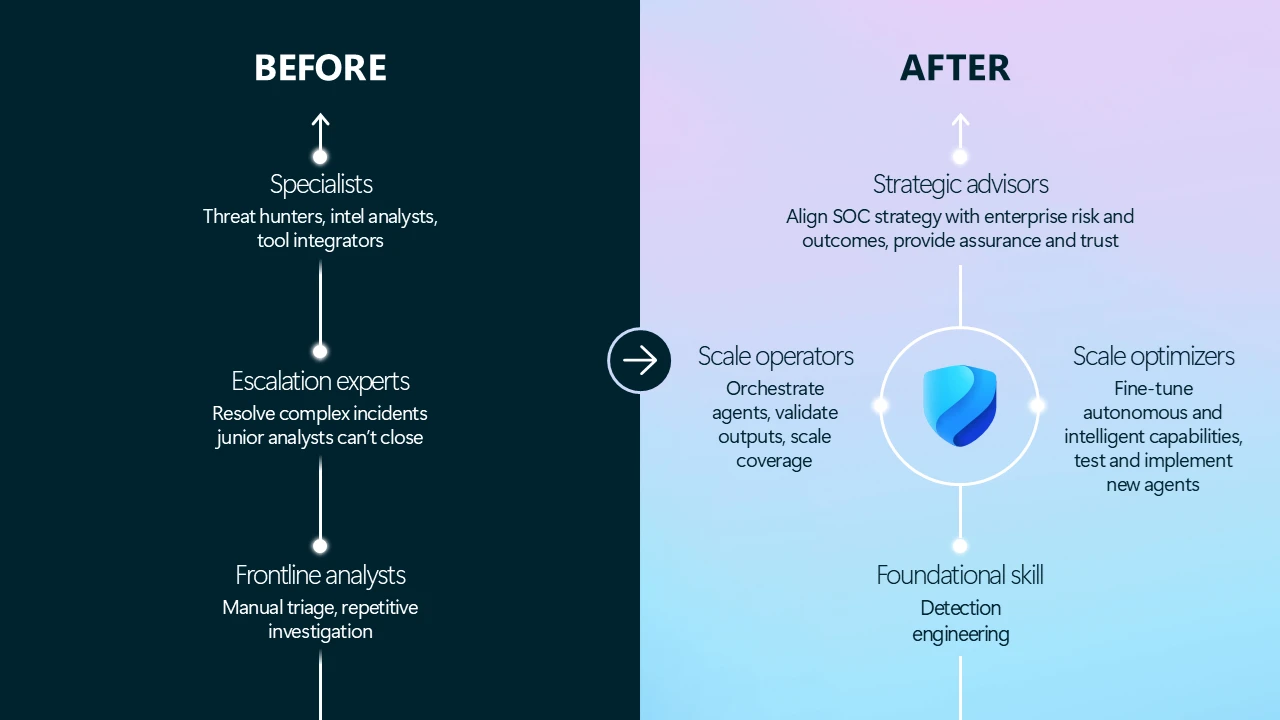
In an agentic SOC, the center of gravity will change for roles like an analyst. Fewer analysts are pulled into firefighting; more time is spent investigating how the organization is being targeted and what steps can be taken to reduce exposure. Within this new operating model, security teams will be freed to evolve the team structure and their day-to-day responsibilities.
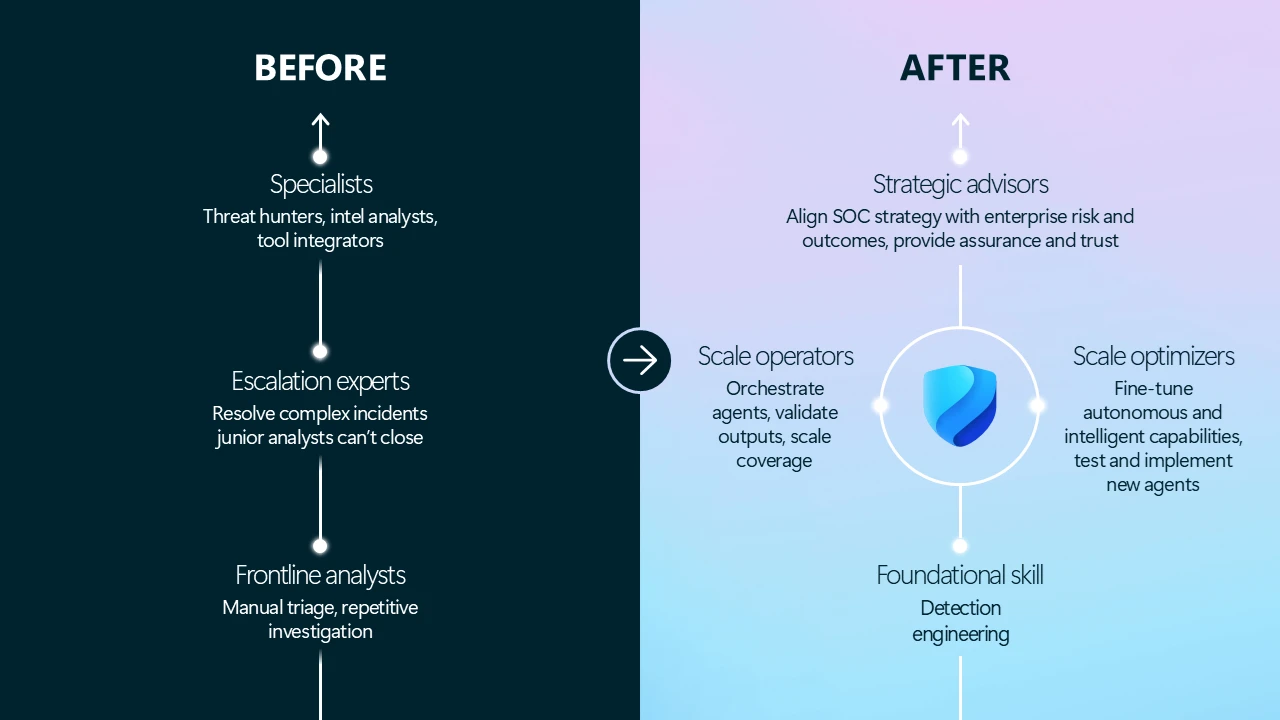
Agentic systems increase demand for oversight, tuning, and governance. Detection and response engineering becomes more central, as teams design policies, confidence thresholds, and escalation paths. New roles emerge around supervising outcomes and refining system behavior over time.
Expertise becomes more valuable, not less. Judgment, context, and institutional knowledge are no longer consumed by repetitive tasks—they shape how the SOC operates at scale. And skilled practitioners closer to strategy, quality, and accountability.
To make this shift tangible, here’s how key roles are evolving:
- Analysts: from triaging alerts to supervising outcomes. Analysts validate agent‑led investigations, determine when deeper inquiry is needed, focus on ambiguous cases, and guide system learning over time.
- Detection engineers: from writing rules to teaching the system what matters. Engineers decide which signals are trustworthy, add the right context, and set confidence thresholds so detections can be acted on automatically—without human review every time.
- Threat hunters: from manual queries to hypothesis-driven exploration. Hunters use AI to surface anomalies and focus on creative investigation and adversary simulation.
- SOC leadership: from managing queues to orchestrating autonomy. Leaders define automation policies, oversee governance, and align AI actions with business risk.
Each shift reflects a broader truth: in the agentic SOC, people don’t do less—they do more of what matters.
The agentic SOC journey
This is a significant change in how security teams operate, and it doesn’t happen overnight. Based on our own experience, we’ve outlined a maturity model that shows how organizations can progress toward an agentic SOC over time.
Organizations begin by establishing a trusted foundation that unifies security tooling, enables the deployment of autonomous defense and begins unifying security signal in earnest. From there, they introduce agents to take on bounded, high-volume work under human supervision, learning where automation adds leverage and where judgment still matters most. Over time, as confidence, governance, and operational discipline mature, agents expand from assisting individual workflows to coordinating broader security outcomes. At every stage, progress is measured not by how much work is automated, but by how effectively human expertise is amplified.
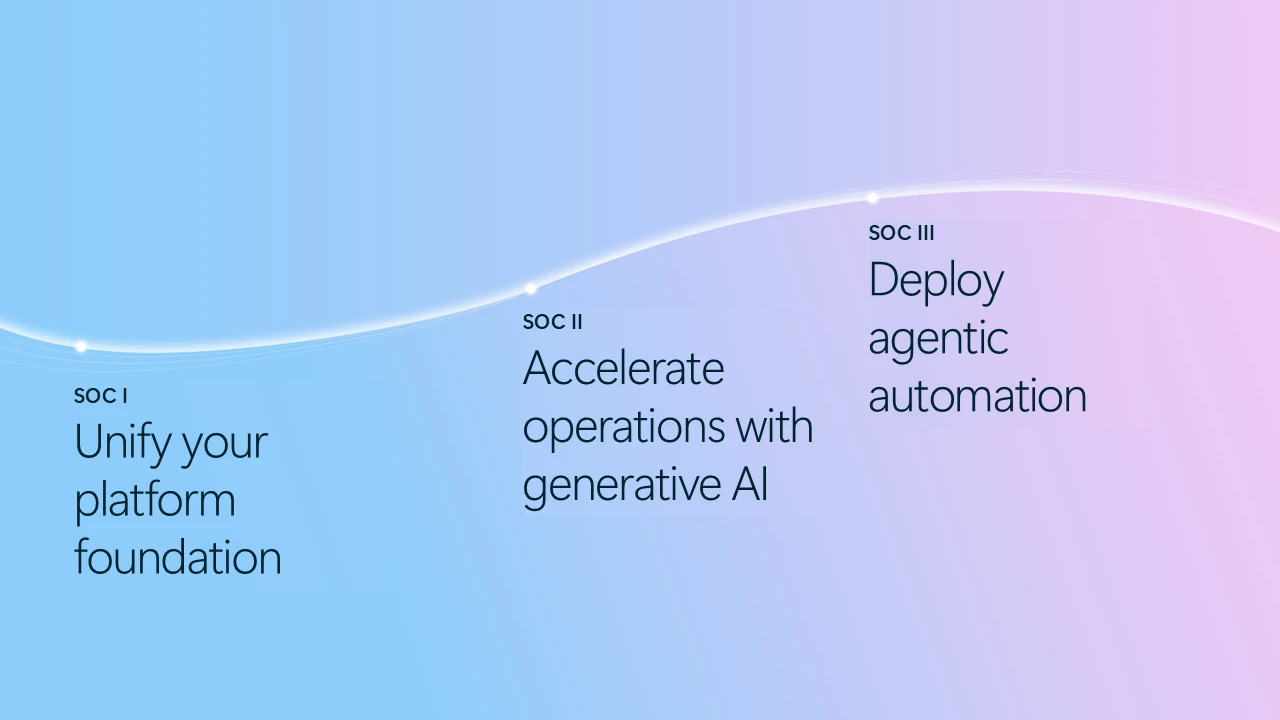
SOC 1—Unify your platform foundation
The shift begins with a unified security platform that enables autonomous defense. Deterministic, policy-bound protections stop high confidence cyberthreats automatically—removing urgency, reducing blast radius, and eliminating the constant context switching that slows human response. By integrating signals across identity, endpoints, and cloud, defenders gain a shared view of cyberattacks instead of stitching evidence together across tools. This foundation is what makes cross-domain action possible—and separates experimental automation from production-ready operations.
SOC 2—Accelerate operations with generative AI and task agents
With urgency reduced, generative AI changes how work flows through the SOC. Instead of pushing alerts forward, AI assembles context, synthesizes signals across domains, and produces coherent investigations. Repetitive, high-volume tasks like triage, correlation, and basic investigation are absorbed by the system, allowing analysts to focus on higher impact decisions. This stage establishes new operational patterns where humans and AI work together—accelerating response while preserving judgment and accountability.
SOC 3—Deploy agentic automation
As trust grows, agents move from assistance to action. Specialized agents autonomously orchestrate specific tasks—containing compromised identities, isolating devices, or remediating reported phishing—while humans shift into supervisory roles. Over time, agents help identify patterns, anticipate attack paths, and optimize defenses across the environment. Security teams spend less time managing queues and more time shaping posture, risk, and outcomes. These shifts compound across all three stages.
What comes next for the SOC evolution?
We believe the strongest agentic SOC models will begin with autonomous defense—deterministic, policy‑bound actions that safely stop what is already known to be dangerous at machine speed. That foundation removes urgency, noise, and latency from security operations.
Additionally, agents and humans work differently. Agents assemble context, coordinate remediation, and optimize how the SOC operates. Humans provide intent, judgment, and accountability—turning time saved into smarter, more strategic security outcomes.
This is the first of a series of posts that will explore what makes the agentic SOC model real: the platform foundations required to defend autonomously, the governance and trust mechanisms that keep autonomy safe, and the adoption journey organizations take to get there. Some organizations are already rebuilding their businesses around AI, a new class of Frontier Firms. Read more about how they’re making their move toward the agentic SOC and access a foundational roadmap for this transformation in our new whitepaper, The agentic SOC: Your teammate for tomorrow, today.
Learn more
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
如有侵权请联系:admin#unsafe.sh