A previously undocumented threat cluster dubbed UAT-10362 has been attributed to spear-phishing campaigns targeting Taiwanese non-governmental organizations (NGOs) and suspected universities to deploy a new Lua-based malware called LucidRook.
"LucidRook is a sophisticated stager that embeds a Lua interpreter and Rust-compiled libraries within a dynamic-link library (DLL) to download and execute staged Lua bytecode payloads," Cisco Talos researcher Ashley Shen said.
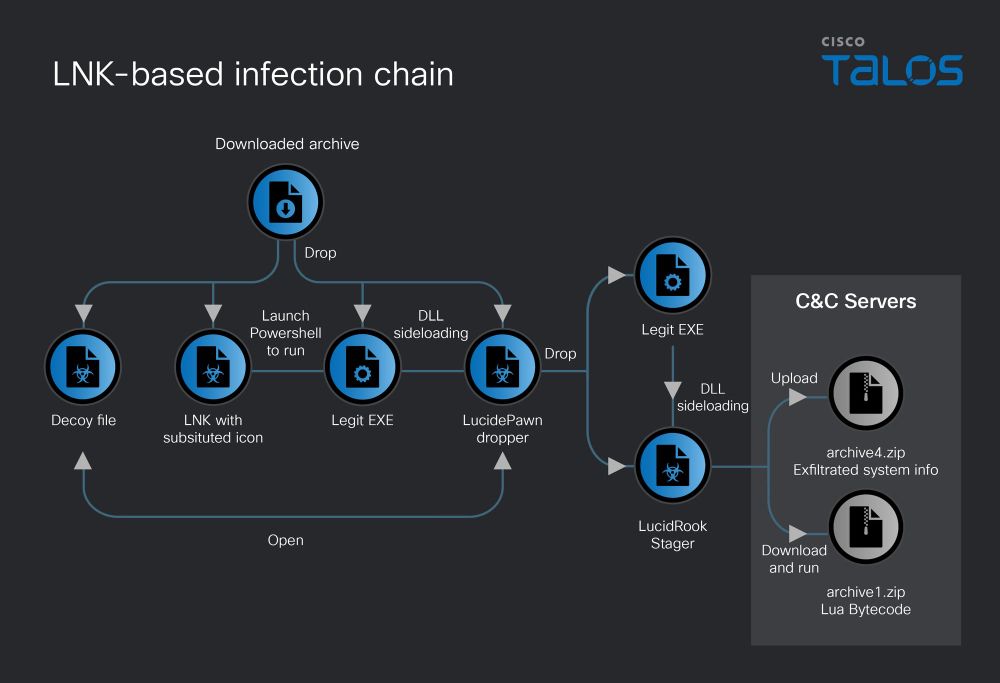
The cybersecurity company said it discovered the activity in October 2025, with the attack using RAR or 7-Zip archives lures to deliver a dropper called LucidPawn, which then opens a decoy file and launches LucidRook. A notable characteristic of the intrusion set is the use of DLL side-loading to execute both LucidPawn and LucidRook.
There are two distinct infection chains that lead to LucidRook, one using a Windows Shortcut (LNK) file with a PDF icon and another involving an executable that masquerades as an antivirus program from Trend Micro. The entire sequence is listed below -
- LNK-based infection chain - When the user clicks the LNK file, assuming it's a PDF document, it executes a PowerShell script to run a legitimate Windows binary ("index.exe") present in the archive, which then sideloads a malicious DLL (i.e., LucidPawn). The dropper, for its part, once again employs DLL side-loading to run LucidRook.
- EXE-based infection chain - When the purported Trend Micro program ("Cleanup.exe") within the 7-Zip archive is launched, it acts as a simple .NET dropper that employs DLL side-loading to run LucidRook. Upon execution, the binary displays a message stating the cleanup process has completed.
A 64-bit Windows DLL, LucidRook, is heavily obfuscated to deter analysis and detection. Its functionality is two-pronged: it collects system information and exfiltrates it to an external server, and then receives an encrypted Lua bytecode payload for subsequent decryption and execution on the compromised machine using the embedded Lua 5.4.8 interpreter.
"In both cases, the actor abused an Out-of-band Application Security Testing (OAST) service and compromised FTP servers for command-and-control (C2) infrastructure," Talos said.
LucidPawn also implements a geofencing technique that specifically queries the system UI language and continues execution only if it matches Traditional Chinese environments associated with Taiwan ("zh-TW"). This offers two-fold advantages, as it limits execution to the intended victim geography and avoids getting flagged in common analysis sandboxes.
Furthermore, at least one variant of the dropper has been found to deploy a 64-bit Windows DLL named LucidKnight that's capable of exfiltrating system information via Gmail to a temporary email address. The presence of the reconnaissance tool alongside LucidRook suggests the adversary operates a tiered toolkit, potentially using LucidKnight to profile targets before delivering the LucidRook stager.
Not much is known about UAT-10362 at this stage other than the fact that it's likely a sophisticated threat actor whose campaigns are targeted rather than opportunistic, while prioritizing flexibility, stealth, and victim-specific tasking.
"The multi-language modular design, layered anti-analysis features, stealth-focused payload handling of the malware, and reliance on compromised or public infrastructure indicate UAT-10362 is a capable threat actor with mature operational tradecraft," Talos said.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.