
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得通读整篇文章,抓住主要信息。 文章讲的是CISA要求美国政府机构在四天内修复Ivanti Endpoint Manager Mobile中的一个严重漏洞。这个漏洞CVE-2026-1340已经被利用了,从一月份开始。Ivanti在1月29日发布了补丁,并强烈建议客户更新系统。Shadowserver监测到近950个暴露的IP地址,主要来自欧洲和北美。CISA将此漏洞加入已知被利用的漏洞目录,并要求联邦机构在4月11日前修复。 接下来,我需要把这些信息浓缩到100字以内。要包括CISA的要求、漏洞的严重性、影响范围以及修复措施。同时,要避免使用“文章内容总结”之类的开头,直接描述。 可能的结构是:CISA要求政府机构四天内修复Ivanti EPMM中的严重漏洞CVE-2026-1340,该漏洞已被攻击利用。Ivanti已发布补丁,Shadowserver发现大量暴露IP。CISA强调修复重要性,并将其加入KEV目录。 这样应该能涵盖主要点,并且控制在字数范围内。 </think> CISA要求美国政府机构在四天内修复Ivanti Endpoint Manager Mobile中的严重漏洞CVE-2026-1340,该漏洞已被用于攻击。Ivanti已发布补丁并敦促客户更新系统以阻止进一步利用。Shadowserver监测到近950个暴露的EPMM设备IP地址,主要来自欧洲和北美。CISA警告该漏洞对联邦企业构成重大风险,并将其加入已知被利用的漏洞目录。 2026-4-8 18:30:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:14 收藏

CISA has given U.S. government agencies four days to secure their systems against a critical-severity vulnerability in Ivanti Endpoint Manager Mobile (EPMM) that has been exploited in attacks since January.
Tracked as CVE-2026-1340, this critical-severity code injection flaw enables threat actors without privileges to gain remote code execution on Internet-exposed and unpatched EPMM appliances.
Ivanti flagged this and a second security bug (CVE-2026-1281) as abused in zero-day attacks when it released security updates on January 29 to patch both vulnerabilities and "strongly" encouraged all customers to update their systems to block ongoing exploitation.
"Successful exploitation could lead to unauthenticated remote code execution. We are aware of a very limited number of customers whose solution has been exploited at the time of disclosure," the company said at the time.
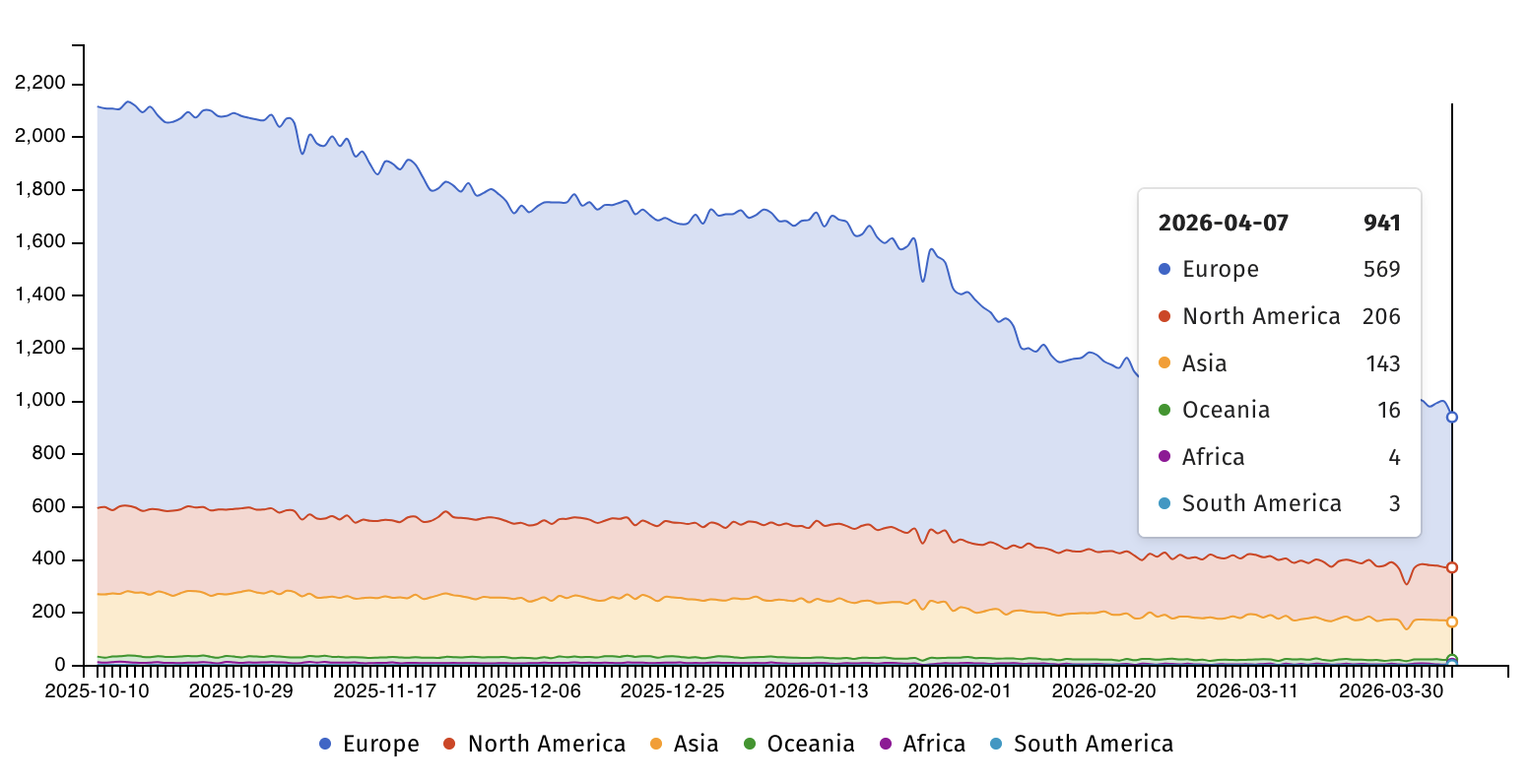
Internet security watchdog group Shadowserver is currently tracking nearly 950 IP addresses with Ivanti EPMM fingerprints still exposed online, most of them from Europe (569) and North America (206). However, there is no information on how many of them have already been patched.
On Monday, the U.S. Cybersecurity and Infrastructure Security Agency added the vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog and ordered Federal Civilian Executive Branch (FCEB) agencies to patch their EPMM systems by Saturday midnight, April 11, as mandated by Binding Operational Directive (BOD) 22-01.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," CISA warned. "Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable."
CISA advised all defenders, including those in the private sector, to prioritize applying patches for CVE-2026-1340 to secure their organizations' devices as soon as possible, even though BOD 22-01 applies only to U.S. federal agencies.
Multiple other Ivanti vulnerabilities have been exploited in recent years via zero-day attacks to breach a wide range of targets, including government agencies worldwide.
In total, CISA has tagged 33 Ivanti vulnerabilities as exploited in attacks, 12 of which have been used by various ransomware operations.
Ivanti provides IT asset management products to over 40,000 customers through a network of more than 7,000 partners around the globe.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

