好的,我现在需要帮用户总结一篇关于Cisco漏洞的文章,控制在100字以内。首先,我得仔细阅读文章内容,找出关键信息。 文章标题提到的是Cisco Smart Software Manager On-Prem的任意命令执行漏洞。接着,文章说明这是一个未认证的远程漏洞,攻击者可以执行任意命令并获得root权限。漏洞原因是内部服务意外暴露,通过精心构造的API请求即可利用。Cisco将其评为Critical级别,CVSS评分9.8,没有补丁可用。 技术细节部分提到该软件用于管理本地许可证,通常部署在可信网络中。成功利用后可完全控制设备,并可能用于横向移动和获取敏感数据。修复只能通过升级到特定版本。 总结时需要包括:漏洞名称、影响、攻击方式、CVSS评分、修复措施等。要简洁明了,不超过100字。 </think> Cisco Smart Software Manager On-Prem存在严重漏洞(CVE-2026-20160),允许未认证远程攻击者通过API请求执行任意命令并获得root权限。该漏洞影响版本9-202502至9-202510,需升级至9-202601或更高版本修复,无临时解决方案。 2026-4-8 18:50:21 Author: horizon3.ai(查看原文) 阅读量:23 收藏
Cisco Smart Software Manager On-Prem Arbitrary Command Execution Vulnerability
A vulnerability in Cisco Smart Software Manager On-Prem (SSM On-Prem) could allow an unauthenticated, remote attacker to execute arbitrary commands on the underlying operating system with root-level privileges. The issue is caused by the unintended exposure of an internal service that can be accessed via a crafted API request. Cisco rates this vulnerability as Critical with a CVSS 3.1 score of 9.8 and states there are no workarounds.
Technical Details
Cisco Smart Software Manager On-Prem is designed for organizations that manage Cisco software licenses locally without allowing direct communication to Cisco over the internet. As a result, it is typically deployed inside trusted management networks.
CVE-2026-20160 is an unauthenticated remote command execution vulnerability. The root cause is the unintended exposure of an internal service. An attacker can send a crafted request to the exposed API endpoint and execute commands as root on the underlying host.
Successful exploitation grants full control of the SSM On-Prem appliance. Because the system manages licensing and deployment metadata and operates within a trusted network segment, compromise provides a high-privilege foothold that can be used for lateral movement, persistence, and access to sensitive operational data.
Cisco has confirmed:
- Patching is required to remediate
- No authentication is required
- Exploitation results in root-level command execution
- No workarounds are available
NodeZero® Proactive Security Platform — Rapid Response
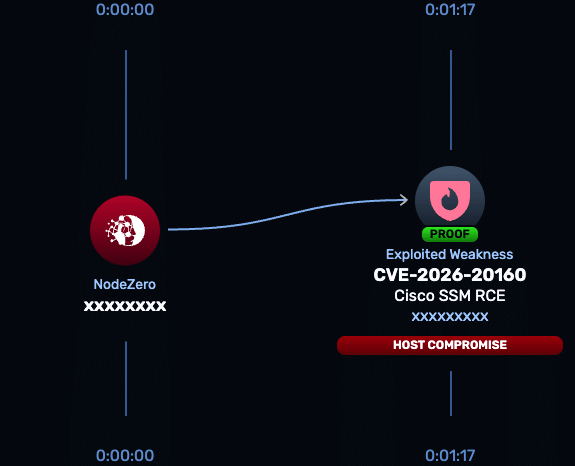
The NodeZero Rapid Response test for CVE-2026-20160 validates whether Cisco Smart Software Manager On-Prem is exploitable in your environment. The test safely exercises the exposed service to determine if unauthenticated command execution is possible.
- Run the Rapid Response test: Launch from the platform to verify exposure.
- Patch immediately: Cisco requires upgrading to a fixed release; no workarounds exist.
- Re-run the Rapid Response test: Confirm that exploitation is no longer possible after remediation.
Rapid Response tests are developed by Horizon3.ai’s research team through reverse engineering and safe exploit development to validate real-world risk.
Affected versions & patch
- Affected: Cisco Smart Software Manager On-Prem releases 9-202502 through 9-202510
- Not affected: Releases earlier than 9-202502
- Fixed: Release 9-202601 and later
- Workarounds: None
Cisco states that upgrading to the fixed release is the only remediation.
Timeline
- April 1, 2026: Cisco publishes advisory for CVE-2026-20160
- April 1, 2026: CVE record published
- April 8, 2026: Horizon3.ai research team reverses the vulnerability and releases Rapid Response coverage
References
Read about other CVEs
NodeZero® Platform
Implement a continuous find, fix, and verify loop with NodeZero
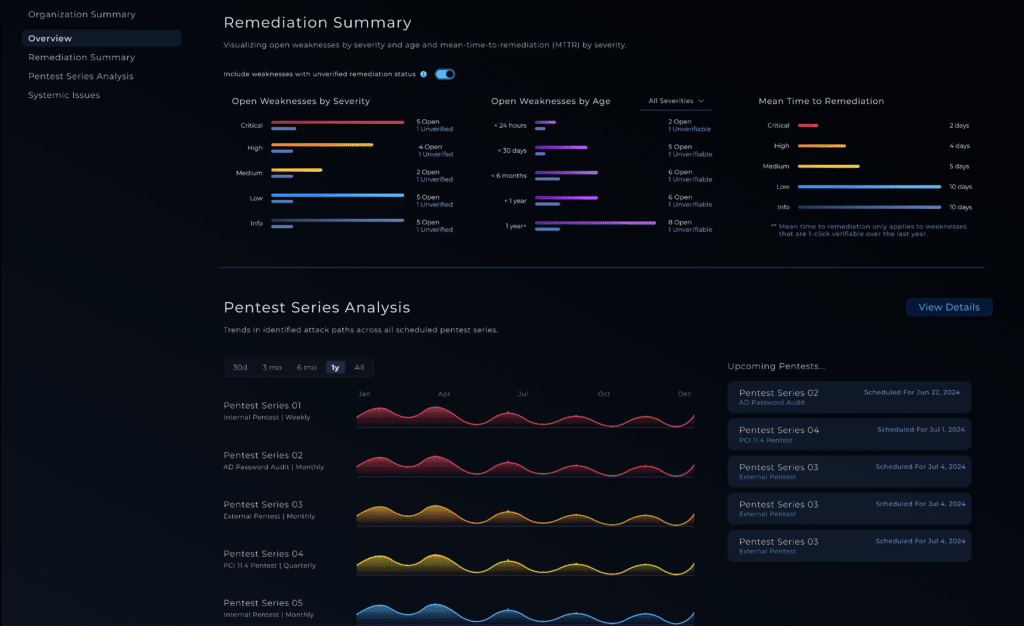
The NodeZero® platform empowers your organization to reduce your security risks by autonomously finding exploitable weaknesses in your network, giving you detailed guidance around how to priortize and fix them, and having you immediately verify that your fixes are effective.
Recognized By
如有侵权请联系:admin#unsafe.sh