好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得通读整篇文章,抓住主要观点。 文章主要讲的是2026年的网络攻击趋势,攻击者利用浏览器直接针对云应用和身份认证。传统的安全工具如EDR和网络代理在这种情况下效果不佳,因为攻击发生在浏览器内部。 接着,文章提到了几种主要的攻击手法:Adversary-in-the-Middle(AitM)钓鱼、ClickFix社交工程、OAuth滥用、恶意浏览器扩展以及会话劫持。这些方法都绕过了传统安全措施,使得检测和防御变得困难。 此外,攻击者利用合法服务和快速的域名轮换来逃避检测,传统安全工具如邮件安全、网络网关和EDR对这些攻击无能为力。因此,安全团队需要重新评估现有的防御措施,并考虑在浏览器层面加强防护。 总结起来,文章强调了浏览器成为新的攻击入口,传统安全工具的局限性以及需要采取的新防御策略。 </think> 2026年网络攻击主要通过浏览器针对云应用和身份认证展开。Adversary-in-the-Middle(AitM)钓鱼、ClickFix社交工程、OAuth滥用、恶意浏览器扩展及会话劫持等技术被广泛采用。这些攻击绕过传统安全工具,利用合法服务和快速域名轮换逃避检测。 2026-4-8 14:22:35 Author: www.guidepointsecurity.com(查看原文) 阅读量:37 收藏
Guest Author: Dan Green, Security Researcher, Push Security
The typical breach used to start with a software exploit or malicious payload on an endpoint. In 2026, the picture looks very different. Attackers have moved up the stack, targeting cloud applications (apps) and identities directly through the browser, often without ever touching the endpoint at all. The kill chain has compressed, too: initial access to data exfiltration can happen in minutes, entirely over the internet, abusing legitimate services and authentication flows.
Attackers are following a familiar playbook: hijack apps via accounts, dump the data, and profit through data resale and extortion. Many traditional security tools are effectively bypassed by operating inside the browser sandbox, where EDR (Endpoint Detection and Response) agents see a browser process but not what’s happening within the session, and where web proxies see obfuscated traffic but not client-side page behavior.
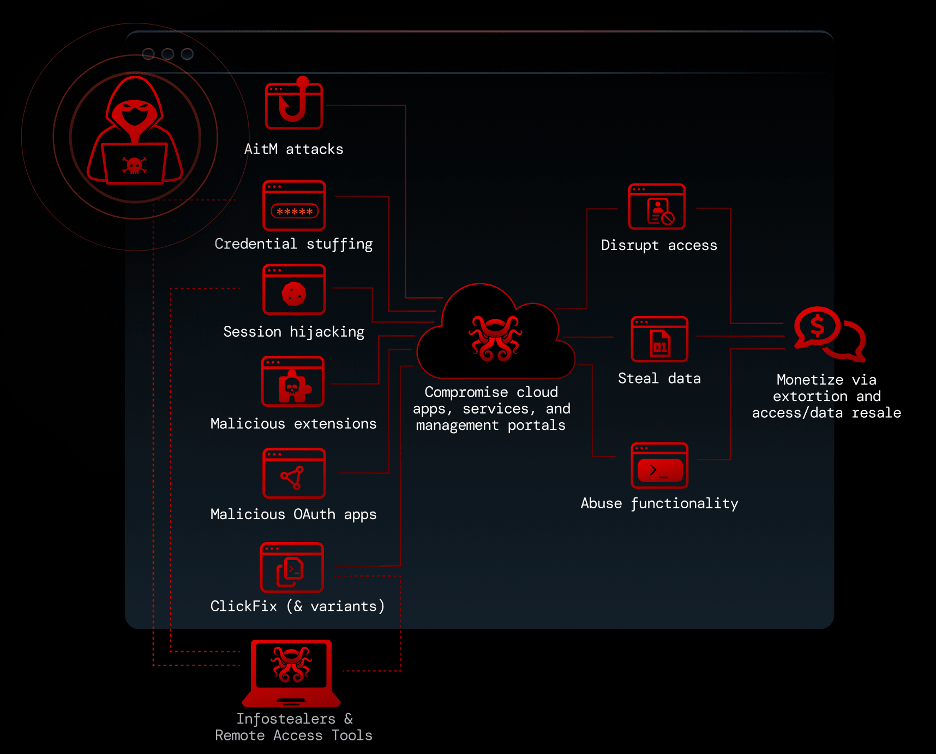
The 2026 cybercriminal playbook leverages primarily browser-based techniques to compromise cloud apps and services accessed in the browser.
Why AitM Phishing is the New Standard
Adversary-in-the-Middle (AitM) phishing has become the default method for credential and session theft. These attacks use a reverse proxy to relay traffic between the victim and the real login page in real time. The victim enters their credentials, completes MFA, and receives a session token — all of which the attacker intercepts. The victim is then redirected to the real site, often without suspecting anything.
The ecosystem is powered by Phishing-as-a-Service kits. Tycoon 2FA is the most prevalent according to Push Security detection data — accounting for around 59% of AitM detections — followed by Sneaky2FA, FlowerStorm, Evilginx, NakedPages, and Gabagool. These kits are continuously updated to impersonate new sites, add evasion techniques, and improve the look and feel of their lures — including Browser-in-the-Browser pop-ups that display convincing fake URLs. Tycoon 2FA alone, available since 2023, has generated tens of millions of phishing emails each month and facilitated unauthorized access to nearly 100,000 organizations globally. Despite a public takedown in March 2026, Tycoon 2FA has already returned to full operating capacity.
As well as sprawling PhaaS-powered campaigns, attackers are also leveraging AitM kits in targeted, human-operated attacks, such as a recent example from Scattered Lapsus$ Hunters. Their latest campaign, targeting over 100 companies and claiming several victims, uses a human-operated AitM kit. The attacker calls the victim impersonating IT, directs them to a company-branded phishing page, captures their session in real time, and then intercepts a passkey enrolment to establish persistent access. Because the phishing domains only activate when an attacker is operating them live, they’re extremely difficult to proactively detect and block.
ClickFix: Social Engineering Meets LOLBins
Since late 2024, ClickFix-style attacks have been tricking users into running malicious commands on their machines under the pretext of “fixing” a page load issue or completing a bot verification challenge. The typical flow copies malicious code to the victim’s clipboard, then guides them through pasting and executing it via a system tool like PowerShell or Terminal.
Microsoft reported ClickFix as the most common initial access vector in 2025 at 47% of observed attacks. CrowdStrike noted a 563% increase in fake CAPTCHA lures. Around 4 in 5 ClickFix payloads arrive via search engines — through malvertising or compromised websites — rather than email.
The technique’s key limitation is that it still requires endpoint-level execution, which means that where EDR is deployed and configured properly, these attacks should be caught. That said, there are always gaps — developer machines where EDR is too noisy, contractors and BYOD with access to enterprise apps but outside the deployment scope of security tools. And since the delivery is fileless and user-initiated, it is less likely to raise alarm than other methods.
But recent examples remove the endpoint from the equation entirely. In late 2025, researchers discovered ConsentFix, a browser-native variant linked to Russian state-affiliated APT29. ConsentFix merges ClickFix-style social engineering with a fully browser-based attack path: the victim is prompted to sign into their Microsoft account, redirected to a localhost URL containing OAuth key material, and then tricked into pasting that URL into a phishing page — giving the attacker access via Azure CLI. No endpoint malware required. We should expect more browser-native ClickFix variants going forward.
OAuth Abuse: Bypassing Authentication Entirely
Malicious OAuth integrations sidestep the authentication process altogether. Rather than stealing credentials or sessions, the attacker gets the victim to authorise an app connection on a legitimate page. This means that even if your account is protected with phishing-resistant controls like passkeys, it can still be phished.
The attack comes in two flavours: consent phishing (authorising an app via an OAuth consent grant) and device code phishing (authorising an app via the device code authorization flow). In both cases, if the victim is already signed in, no additional login is required. They’re clicking a button or entering a code on a real app page. It doesn’t feel like a phishing attack — and that’s precisely why it works.
The 2025 campaign illustrates the threat. Scattered Lapsus$ Hunters registered a fake “DataLoader” app, called victims impersonating IT support, and walked them through authorizing the app in their Salesforce tenant. The app requested broad OAuth scopes including full API access and the ability to generate refresh tokens without re-authentication. The result: a claimed 1,000+ organizations compromised and 1.5 billion records exfiltrated.
And with a tracked 15x increase in device code attacks so far in 2026, this adoption of OAuth consent attacks into the standard phishing toolkit looks set to continue.
The Extension Supply Chain Problem
Malicious browser extensions are increasingly attractive because of their scalability. The typical playbook isn’t to build a malicious extension from scratch — it’s to either legitimately acquire or compromise an extension with an established install base, then push a malicious update to siphon credential and session material directly from the browser.
A December 2024 campaign illustrates the approach. Attackers phished the developers of popular apps into authorising a malicious OAuth app, gained permissions to manage their Chrome Web Store extensions, and uploaded a malicious version. Downstream browsers auto-updated and were infected. Each time an infected browser launched, it fetched a configuration from a remote server, allowing the attacker to vary payloads per browser and only trigger on specific pages — making both static and dynamic analysis unreliable. The broader campaign affected 2.6 million users.
A more recent campaign dubbed “GhostPoster” used similar evasion: 34 extensions, 890,000 installs, 48-hour delays between check-ins, and payloads loaded only 10% of the time. Extension permissions alone aren’t a reliable risk indicator — over half of extensions running in employee browsers have permissions that can be abused for high-risk actions like direct session theft.
Credential Stuffing and Ghost Logins
It’s tempting to treat credential attacks as a solved problem, but the data suggests otherwise. Across a recent sample of a million logins, 1 in 4 were password-based (not SSO), 2 in 5 lacked MFA, and 1 in 5 used a weak, breached, or reused password.
The problem is compounded by “ghost logins” — legacy credentials created when an app was first adopted that continue to work even after SSO is configured. These don’t appear in IdP logs, often lack MFA at the app level, and can sit undetected for years.
There are many reasons these persist. Apps often charge extra for SAML SSO — if they offer it at all. Even when it’s supported, someone needs to configure it. If an app was self-adopted or IT hasn’t gotten to it yet, alternative login methods creep in. And the vast majority of apps support simultaneous login methods by default, with many not allowing them to be restricted.
The canonical example happened when ShinyHunters breached over 165 organizations in 2024, stealing over a billion records by logging into cloud app tenants with stolen credentials. 80% of compromised accounts had prior breach exposure dating back to 2020.
Session Hijacking: Post-auth Account Takeover
Session hijacking rounds out the TTP set. By replaying a stolen session token in their own browser, an attacker can bypass the entire authentication process — including phishing-resistant controls like passkeys. Unlike AitM attacks (which create a new session via a reverse proxy), session hijacking reuses an already-approved token.
The primary source of stolen tokens is infostealer malware, increasingly delivered via ClickFix. Malicious browser extensions are another source, extracting tokens from pages as the user browses the web.
A late 2023 breach showed this at scale. An infostealer on a support engineer’s personal device compromised corporate credentials synced via their personal Google account. The attacker accessed the customer support system, downloaded HAR files containing session tokens, and used them to access 134 downstream customer environments. The root cause: an employee had signed into their personal Google profile on their corporate laptop, and browser profile syncing carried the credentials across.
Built to Evade Detection
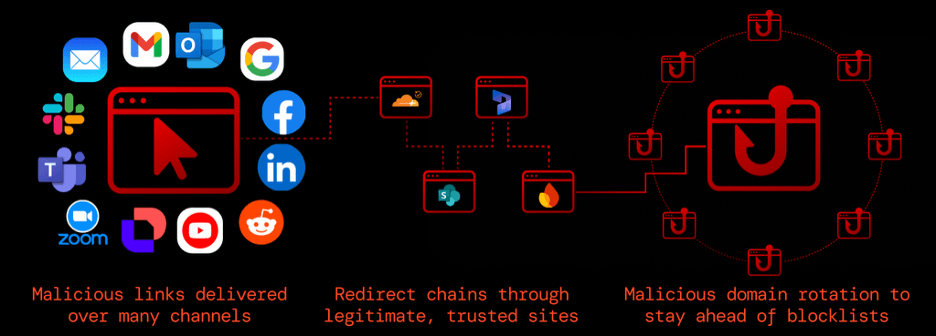
What makes these techniques collectively so effective is how they evade established controls. Around a third of payloads now arrive outside email. Attacker infrastructure sits on trusted services like SharePoint, Google Sites, and Cloudflare to blend in with legitimate sites and traffic. Rapid domain rotation, complex redirect chains, and bot protection services (used in an estimated 95% of in-browser attacks) mean security scanners can’t keep up.
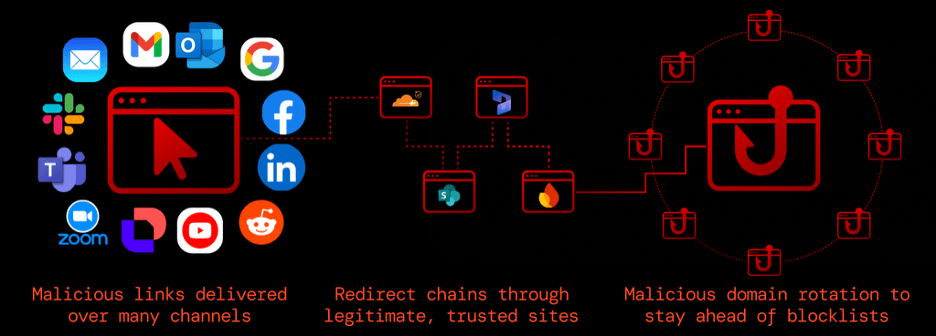
Modern attacks are designed to evade detection controls, with varied delivery channels, trusted sites abuse, and rapid domain rotation to stay ahead of known-bad detections.
So, when you compare browser-based techniques to the typical security stack, the gaps are clear. Email security misses non-email delivery. Secure web gateways are bypassed by domain rotation and HTML smuggling. Remote browser isolation was designed for browser exploits, not in-browser account takeover. EDR doesn’t see inside browser sessions. Identity controls are undermined by AITM phishing, ghost logins, and post-auth attacks. And cloud security logging is inconsistent from app to app.
None of this means these controls are useless. But security teams should re-evaluate whether their stack provides the protection they assume against this class of attack.
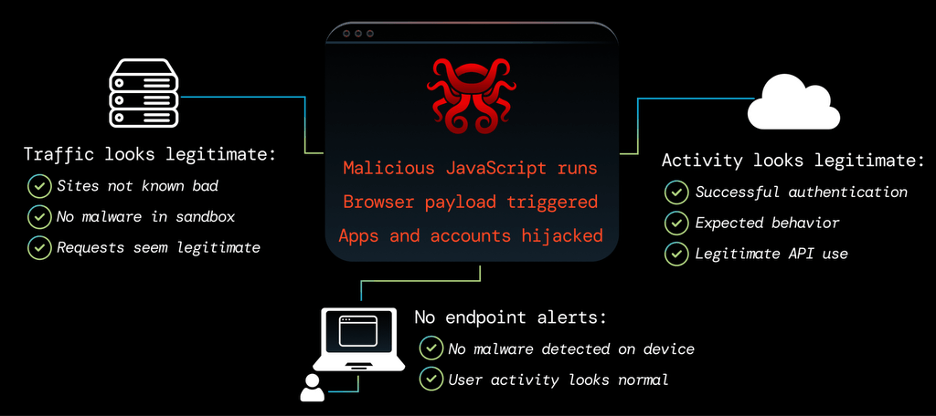
The browser is a blind-spot for most security teams.
Accessible to All Attackers
Browser-based attacks also have a low barrier to entry compared to traditional attacks. A phishing kit rental runs about $1,000 per year, an IAB (Initial Access Broker)-provided admin account costs around $3,000, and bulk stolen credentials go for $15. And because these attacks abuse legitimate authentication flows rather than exploiting software vulnerabilities, they don’t get “patched” in the traditional sense — the underlying mechanisms they target (OAuth, session tokens, password logins) are features, not bugs.
In contrast, a browser RCE (Remote Code Execution) exploit costs around $250,000 with an increasingly short shelf life. EDR has gotten significantly better at blocking endpoint malware, driving up the cost of custom tooling and obfuscation. The result is a rational economic shift — and because of their effectiveness, highly skilled threat actors use these techniques as readily as lower-sophistication operators.
Where to Go from Here
The average e-crime breakout time was 29 minutes in 2025 according to CrowdStrike. For browser-based attacks that go straight from account takeover to data exfiltration, that window can be even shorter. Intercepting these attacks before damage is done necessitates moving security into the browser — where traditional tools have least coverage, and where browser-based detection and response can restore the advantage for defenders.
This post draws on Push Security’s 2026 Browser Attack Techniques report, which covers each of these TTPs in greater detail with additional case studies and data. Worth a read if you’re working in detection and response, identity security, or SaaS security posture.
如有侵权请联系:admin#unsafe.sh