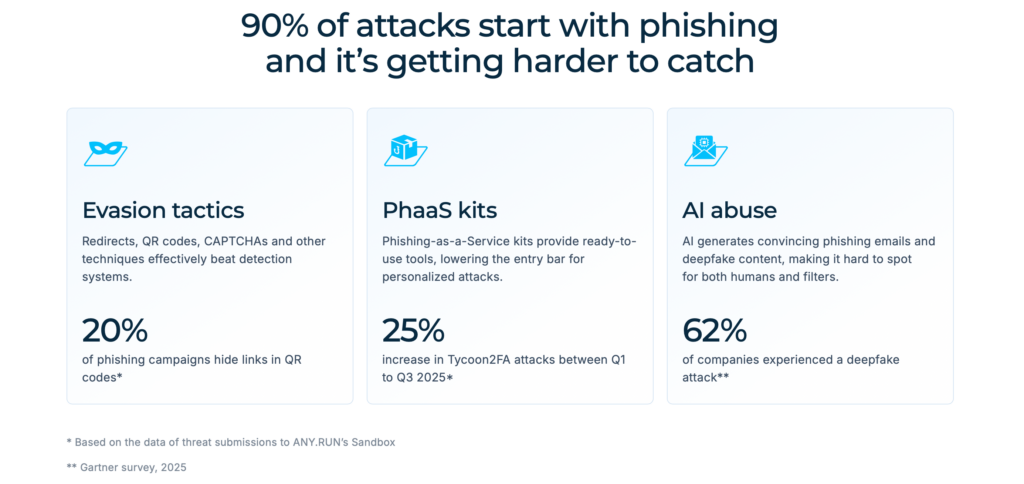
90% of attacks start with phishing. For CISOs, the real pain begins when the SOC cannot quickly tell whether a suspicious alert is just noise or the start of credential theft, account compromise, malware delivery, or wider business disruption.
Modern phishing campaigns are designed to create exactly that uncertainty. QR codes, redirect chains, CAPTCHAs, phishing kits, and AI-generated lures can all hide the real objective until late in the attack flow.
So what does phishing detection that actually works look like for a modern SOC or MSSP? Let’s find out.
Why Modern Phishing Still Breaks SOC Workflows
Phishing is still one of the most common ways attackers get into organizations, but the threat no longer follows a simple pattern. Modern phishing campaigns are built to hide their real intent, delay validation, and make investigation harder for already overloaded security teams.
What makes today’s phishing especially disruptive is the mix of techniques now used in a single campaign. Security teams are no longer dealing with one suspicious email and one malicious link. They are dealing with layered attack flows that may include:
- redirect chains that hide the real destination
- QR codes that bypass traditional inspection
- CAPTCHAs that slow or block analysis
- Phishing-as-a-Service kits that make advanced attacks easier to launch
- AI-generated lures and deepfake content that make phishing more convincing
This combination puts much more pressure on SOC workflows. The challenge is understanding what actually happens next and doing it fast enough to reduce business risk.
The numbers reflect this shift. 20% of phishing campaigns hide links in QR codes, while Tycoon2FA attacks increased by 25% between Q1 and Q3 2025. Gartner also found that 62% of companies experienced a deepfake attack in 2025. Together, these trends show that phishing is more adaptive, more evasive, and more difficult to investigate quickly.
For SOC teams, this creates a dangerous workflow gap. An alert may show that something looks suspicious, but it often does not reveal whether credentials are being harvested, whether MFA is being bypassed, whether malware is delivered after the phishing stage, or how far the attack could spread if it succeeds. That lack of visibility is where delays begin.
When visibility breaks down, the workflow usually breaks down with it:
- triage takes longer
- confidence in decisions drops
- more cases are escalated
- response slows at the exact moment speed matters most
To make phishing detection work, CISOs need an approach that helps the SOC spot threats sooner, understand their impact earlier, and contain them before they escalate.
Step 1: Strengthen Monitoring with Fresh Phishing Intelligence
The first step is making sure the SOC can see phishing activity early enough to act on it. If malicious domains, URLs, or campaign indicators surface too late, the team starts every investigation from behind.
Strong monitoring is not just about collecting more alerts. It is about improving what the SOC sees first and giving teams a better chance to catch phishing before it spreads further. The more current and relevant the intelligence is, the easier it becomes to recognize real threats early and prioritize them correctly.
This is where the quality and scale of threat data make a real difference. ANY.RUN’s phishing intelligence is built on first-hand investigations of active campaigns observed across 15,000 organizations and used by more than 600,000 security professionals worldwide. That gives teams access to fresh phishing indicators grounded in real attack activity, not just static or generic reputation data.
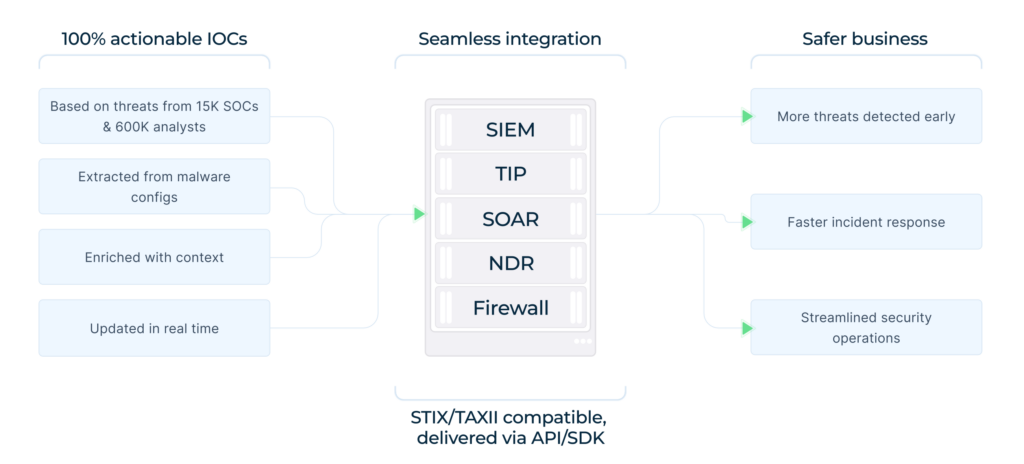
With this kind of monitoring in place, SOC teams can:
- spot malicious URLs, domains, and payloads earlier
- improve coverage across emerging phishing campaigns
- enrich detections with context tied to real investigations
- prioritize alerts faster and with more confidence
A stronger monitoring layer gives the SOC a much better starting point. And when phishing is detected earlier, every step that follows becomes more effective.
Step 2: Improve Triage with Full Attack-Chain Visibility
Early detection is only the starting point. Once a phishing alert reaches the SOC, the next challenge is figuring out what the attack is actually doing and whether it creates real business risk.
This is where triage often slows down. A suspicious URL or attachment may trigger an alert, but that alone does not show whether the campaign leads to credential theft, MFA bypass, malware delivery, or a broader account takeover attempt. Without that visibility, teams spend more time validating the threat, confidence in verdicts drops, and more cases are escalated than necessary.
Strong phishing triage should help teams quickly answer a few critical questions:
- Where does the attack flow actually lead?
- Is the user being pushed to a fake login page?
- Are credentials or session tokens being stolen?
- Does the phishing stage end in malware delivery?
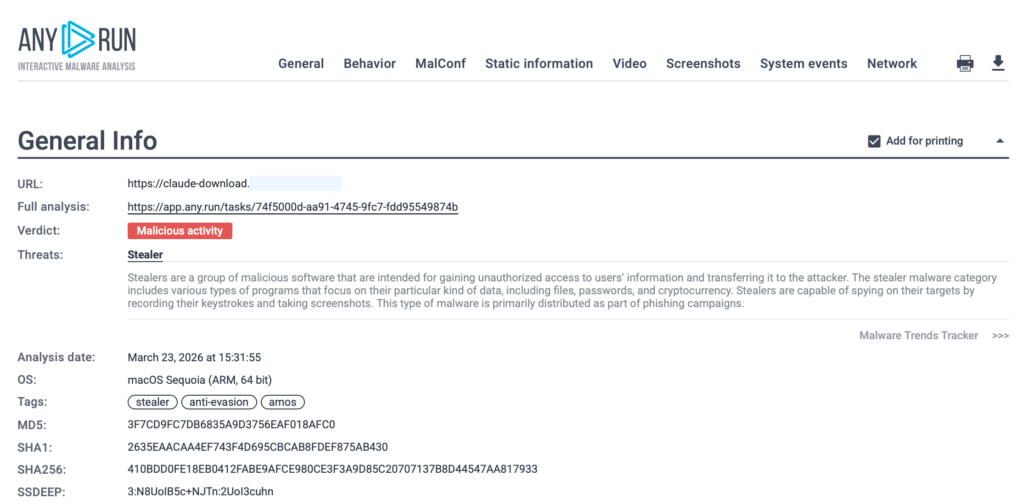
ANY.RUN helps close this gap with Interactive Sandbox analysis that exposes the full phishing chain in a safe environment. Teams can detonate suspicious URLs and files, follow redirects, open attachments, scan QR codes, and inspect CAPTCHA-protected flows to see how the attack behaves in practice.
Instead of relying on assumptions, they can validate the threat based on what actually happens. Analysts can also interact with the environment at any time, which makes it easier to investigate suspicious behavior manually when a deeper look is needed.
See how a real quishing attack can be analyzed inside ANY.RUN’s Interactive Sandbox in seconds:
This process becomes even faster with Automated Interactivity. By imitating analyst behavior inside the sandbox, it can interact with phishing pages automatically, uncover hidden links behind QR codes, solve CAPTCHAs, and continue the analysis flow without waiting for manual input. That helps teams move through evasive phishing stages faster and reach the real malicious behavior sooner.
Check sandbox analysis with Automated Interactivity
Stronger triage reduces uncertainty, cuts wasted effort and helps teams reach conclusions faster. That means fewer unnecessary escalations, quicker containment, and less chance for phishing incidents to grow into broader operational or financial impact.
Step 3: Speed Up Response with Clear Verdicts and Actionable Evidence
Phishing detection does not end when the SOC confirms that something looks suspicious. The next challenge is turning that analysis into fast, confident response.
This is where many workflows still slow down. Even after a phishing attack has been investigated, teams often need to manually collect indicators, document what happened, map behavior to known techniques, and prepare findings for escalation or response. That extra effort creates delays at exactly the moment when speed matters most.
A strong response workflow should give teams what they need to act without friction:
- a clear verdict on the threat
- extracted IOCs for blocking and investigation
- mapped TTPs for faster understanding
- structured reports for escalation and handoff
- evidence that helps response teams move with confidence
ANY.RUN helps speed up this stage by turning phishing analysis into decision-ready outputs. Teams can see how the attack unfolds across redirects, phishing pages, credential theft attempts, and payload delivery, often reaching a verdict within the first 60 seconds. Clear verdicts, extracted IOCs, mapped TTPs, visual behavior details, and auto-generated reports make incidents easier to understand and faster to contain.
For CISOs, the real benefit is a faster path from investigation to containment. It helps teams contain phishing incidents sooner, make more consistent decisions under pressure, and reduce the time attackers have to turn a phishing attempt into credential theft, fraud, or wider business disruption.
What SOC Teams Gain from Stronger Phishing Detection
When SOC teams improve monitoring, sharpen triage, and speed up response, phishing becomes much harder to turn into a larger incident. Stronger phishing detection helps teams identify suspicious activity sooner, understand it more quickly, and act with greater confidence when time matters most.
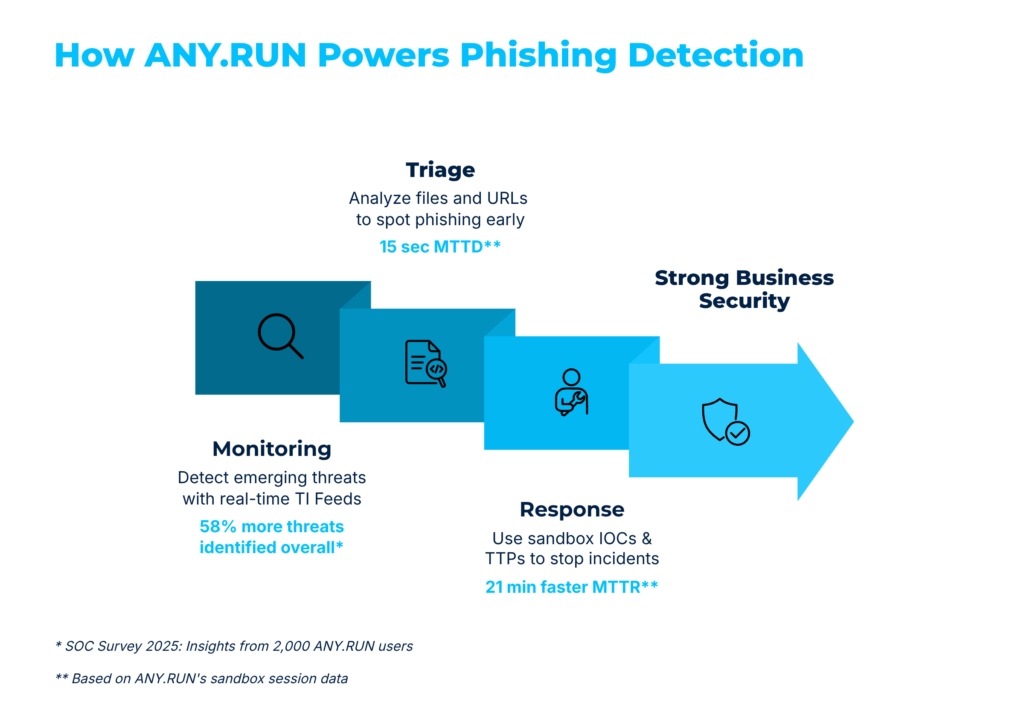
This approach drives measurable improvements across day-to-day SOC operations:
- 36% higher detection rate
- up to 58% more threats detected
- 21 minutes faster MTTR per incident
- up to 20% lower Tier 1 workload
- 30% fewer Tier 1 to Tier 2 escalations
The value goes beyond the numbers. Better phishing detection helps reduce alert fatigue by making suspicious activity easier to assess. It also helps Tier 1 handle more cases with confidence instead of pushing unclear investigations further down the workflow.
- Lower breach risk through earlier detection and more informed response
- Reduce the cost of phishing incidents by containing threats faster
- Ease alert fatigue with faster clarity on suspicious activity
- Improve SOC efficiency with quicker, better-informed decisions
- Reduce Tier 1 workload by helping front-line teams close more cases sooner
- Improve consistency in phishing investigations and response workflow
- Avoid hardware costs by using cloud-based analysis
- Scale operations more easily as phishing volume grows
- Get more value from existing teams without adding the same operational burden
- Reduce the likelihood of wider business disruption by stopping phishing earlier
Phishing is often the first step in account compromise, fraud, malware delivery, and wider business disruption. When SOC teams can detect it earlier and respond faster, the organization is in a much stronger position to stop the attack before the damage spreads.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps organizations detect, investigate, and respond to modern phishing attacks with greater speed and clarity.
By combining Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds, ANY.RUN gives SOC and MSSP teams the tools to spot phishing activity sooner, investigate threats more effectively, and respond with structured findings. Its approach helps security teams expose full attack chains, investigate evasive phishing techniques, and make more confident decisions under pressure.
Trusted by more than 15,000 organizations and 600,000 security professionals worldwide, including 74% of Fortune 100 companies, ANY.RUN is built to support modern security operations with faster threat visibility, stronger investigation workflows, and more informed response. The company is SOC 2 Type II certified, reflecting its focus on strong security controls and customer data protection.
Integrate ANY.RUN’s solution for Tier 1/2/3 in your organization →