嗯,用户让我帮忙总结一篇文章,控制在一百个字以内,而且不需要用“文章内容总结”之类的开头。首先,我需要仔细阅读这篇文章,理解它的主要内容和重点。 这篇文章主要讲的是Mend.io的新集成功能,结合Docker的加固镜像(DHI),提升容器安全。作者提到传统容器扫描有很多噪音,比如扫描出成千上万的CVE漏洞,但很多都是应用从未接触过的基础镜像漏洞,导致团队浪费时间处理这些无关紧要的问题。 Mend.io的新集成通过引入Docker的VEX情报和自身的可达性分析,帮助团队聚焦于真正重要的漏洞。Docker加固镜像提供最小化、持续更新的基础镜像,并带有VEX声明,说明哪些CVE不可被利用。Mend.io的扫描能自动识别这些加固镜像,并在界面上标记出来,让团队一目了然。 此外,Mend.io结合VEX数据和可达性引擎,过滤掉不可达或不可利用的漏洞,只显示真正有风险的漏洞。这不仅节省了时间,还提升了开发效率和合规性。 所以,在总结的时候,我需要涵盖以下几个关键点:Mend.io的新集成、Docker加固镜像、减少噪音、提升安全效率、自动化处理以及合规性支持。同时要控制在100字以内,并且直接描述内容。 可能会这样组织语言:“Mend.io与Docker合作推出加固镜像集成,解决容器扫描中的噪音问题。通过整合VEX情报和可达性分析,自动识别并过滤无关漏洞,提升开发效率和安全性。” 这样既涵盖了主要功能和技术点,又简洁明了。 </think> Mend.io与Docker合作推出加固镜像集成,解决容器扫描中的噪音问题。通过整合VEX情报和可达性分析,自动识别并过滤无关漏洞,提升开发效率和安全性。 2026-4-7 13:34:5 Author: securityboulevard.com(查看原文) 阅读量:8 收藏
Mend.io’s new Docker Hardened Images integration brings DHI intelligence directly into the AppSec workflow, giving a smarter, faster path to container security.
Container scanning has a noise problem.
Run a standard scan against any production image, and you’ll surface thousands of CVEs. Your team triages them, prioritizes them, assigns them—and then discovers that the vast majority are base image vulnerabilities tied to packages your application never touches and can’t directly fix.
Hours spent. Risk posture unchanged.
Mend.io’s new Docker Hardened Images (DHI) integration is built to solve exactly this. Pulling Docker’s VEX intelligence directly into the Mend platform and combining it with Mend.io’s reachability analysis gives teams the clarity to focus on vulnerabilities that actually matter.
What Docker Hardened Images bring to the table
Docker Hardened Images are minimal, continuously patched base images built with software supply chain security as a foundational requirement. Each base image ships with VEX (Vulnerability Exploitability eXchange) statements, machine-readable declarations identifying which CVEs present in the image are not exploitable given how the software is actually used.
Without VEX, your scanner can’t distinguish between a CVE in a package that your application never touches and one that poses a true risk. Neither can your team.
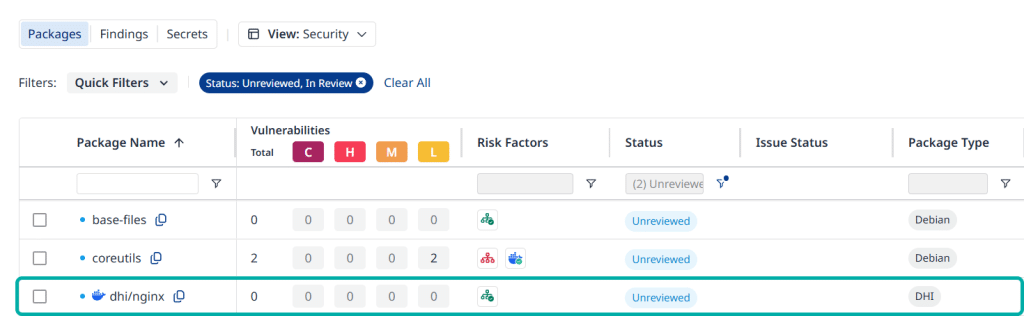
When Mend.io scans a container built on a Docker Hardened Image, it automatically detects the DHI base no manual tagging, no configuration changes required. Within the Mend UI, DHI protected packages are marked with a dedicated Docker icon so anyone on the team immediately sees which components belong to Docker’s hardened foundation versus your application layer.
Two intelligence layers, one focused risk view
Mend.io ingests DHI’s VEX data as a primary Risk Factor source. Any CVE marked as not_affected is immediately deprioritized. On top of that, Mend’s reachability engine evaluates whether vulnerable code paths in your application dependencies are ever actually called at runtime.
The result: your team sees only vulnerabilities that are present, reachable, and exploitable. Everything else can be suppressed in bulk, potentially clearing thousands of non-exploitable CVEs in a single action—so you focus on the fraction of findings that represent genuine risk in your custom code.
Pipeline gating that reflects actual risk
Mend.io’s workflow engine lets you configure build gates to trigger only when high-risk, reachable vulnerabilities are introduced in your custom application code—not because of a base image CVE Docker has already declared non-exploitable. Your pipeline keeps moving. Your developers get failure signals they can actually act on.
Compliance as a byproduct
For organizations under SSDF, FedRAMP, or similar frameworks, Mend.io lets you export a full SBOM with a single click, backed by an auditable trail of VEX statements and reachability logs. Compliance evidence becomes a natural output of your standard development workflow—not a manual effort assembled before every audit.
The 1% that matters
Stop spending developer hours on the 99% of container vulnerabilities that don’t represent real risk. With zero-configuration detection, combined VEX and reachability filtering, automated base image patching, and one-click SBOM export, Mend.io and Docker Hardened Images give your team the signal-to-noise ratio container security has always needed.
*** This is a Security Bloggers Network syndicated blog from Mend authored by Shannon Davis. Read the original post at: https://www.mend.io/blog/docker-hardened-images-container-security/
如有侵权请联系:admin#unsafe.sh