
好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。用户给的文章是关于Windows的一个漏洞BlueHammer,已经被公开了利用代码,但微软还没有修补。首先,我要理解文章的主要内容。 文章提到,一个安全研究人员对微软的漏洞披露处理不满,公开了BlueHammer的漏洞细节和利用代码。这个漏洞允许攻击者提升权限到SYSTEM或高级管理员权限。微软还没有发布补丁,所以这是一个零日漏洞。 接下来,我需要提取关键信息:漏洞名称、影响、原因、现状和风险。然后用简洁的语言把这些点整合起来,确保不超过100字。 可能的结构是:研究人员因不满微软处理而公开未修补的Windows漏洞BlueHammer,允许攻击者提升权限至SYSTEM或高级管理员。该漏洞尚未有补丁,被视为零日漏洞。 检查一下字数是否符合要求,并确保信息准确无误。 </think> 一位安全研究人员因不满微软对漏洞披露的处理方式,公开了未修补的Windows特权提升漏洞BlueHammer的细节及利用代码。该漏洞允许攻击者获取SYSTEM或高级管理员权限,并被视为零日漏洞。 2026-4-6 19:30:23 Author: www.bleepingcomputer.com(查看原文) 阅读量:20 收藏
Exploit code has been released for an unpatched Windows privilege escalation flaw reported privately to Microsoft, allowing attackers to gain SYSTEM or elevated administrator permissions.
Dubbed BlueHammer, the vulnerability was published by a security researcher discontent with how Microsoft’s Security Response Center (MSRC) handled the disclosure process.
Since, the security issue has no official patch and there is no update to address it, the flaw is considered a zero-day by Microsoft's definition.
It is unclear what triggered the public release of the exploit code. In a short post under the alias Chaotic Eclipse, the researcher says "I was not bluffing Microsoft, and I'm doing it again."
“Unlike previous times, I'm not explaining how this works; y'all geniuses can figure it out. Also, huge thanks to MSRC leadership for making this possible,” the researcher added.
On April 3rd, Chaotic Eclipse published a GitHub repository for the BlueHammer vulnerability exploit under the alias Nightmare-Eclipse, expressing disbelief and frustration at how Microsoft decided to address the security issue.
"I'm just really wondering what was the math behind their decision, like you knew this was going to happen and you still did whatever you did ? Are they serious ?"
The researcher also noted that the proof-of-concept (PoC) code contains bugs that may prevent it from working reliably.
Will Dormann, principal vulnerability analyst at Tharros (formerly Analygence), confirmed to BleepingComputer that the BlueHammer exploit works, saying that the flaw is a local privilege escalation (LPE) that combines a TOCTOU (time-of-check to time-of-use) and a path confusion.
He explained that the issue is not easy to exploit and that it gives a local attacker access to the Security Account Manager (SAM) database, which contains password hashes for local accounts.
Given this access, attackers can escalate to SYSTEM privileges and potentially achieve complete machine compromise.
“At that point, [the attackers] basically own the system, and can do things like spawn a SYSTEM-privileged shell,” Dormann told BleepingComputer.
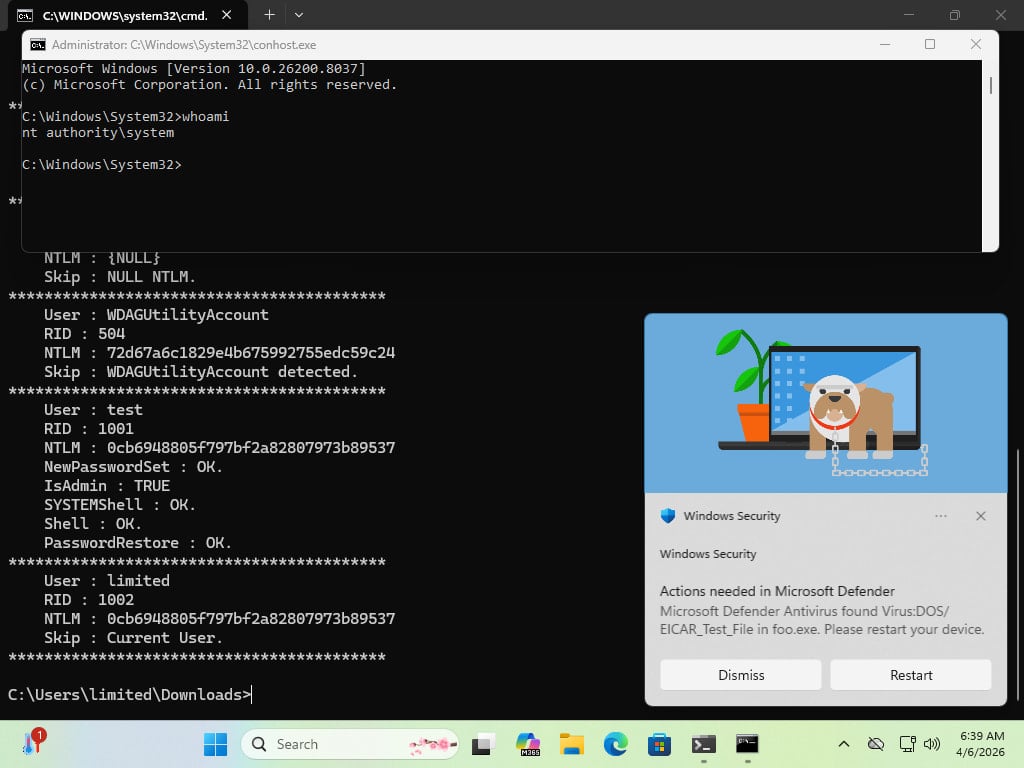
Source: Will Dormann
Some researchers testing the exploit confirmed that the code was not successful on Windows Server, confirming Chaotic Eclipse's statement that there are bugs that may prevent it from working properly.
Will Dormann added that on the Server platform, the BlueHammer exploit increases permissions from non-admin to elevated administrator, a protection that requires the user to temporarily authorize an operation that needs full access to the system.
While the reason behind Chaotic Eclipse/Nightmare-Eclipse's disclosure remains uncertain, Dormann notes that one requirement from MSRC when submitting a vulnerability is to provide a video of the exploit.
Although this may help Microsoft sift through reported vulnerabilities more easily, it adds to the effort of submitting a valid report.
Despite BlueHammer requiring a local attacker to exploit it, the risk it poses is still significant, as hackers can gain local access through a variety of vectors, including social engineering, leveraging other software vulnerabilities, or through credential-based attacks.
BleepingComputer has contacted Microsoft for a comment on the BlueHammer flaw, but we did not receive a response by publication time.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

