
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是一个名为GPUBreach的新攻击,它利用GPU GDDR6内存的Rowhammer漏洞来提升权限,最终导致整个系统的被攻陷。这个攻击是由多伦多大学的研究团队开发的,他们将在IEEE安全与隐私会议上展示细节。 攻击步骤包括通过Rowhammer诱导位翻转,破坏GPU页表,从而让无特权的CUDA内核获得任意GPU内存读写权限。然后利用NVIDIA驱动中的内存安全漏洞进一步提升权限到CPU侧,最终完全控制整个系统,而不需要禁用IOMMU保护。 此外,文章提到研究人员已经向NVIDIA等公司报告了这一漏洞,并获得了奖励。目前没有有效的缓解措施,尤其是针对没有ECC的消费级GPU。 总结时需要涵盖攻击名称、机制、影响、研究团队和缓解情况。要确保在100字以内简洁明了地表达这些要点。 </think> GPUBreach是一种新型攻击技术,通过利用GPU GDDR6内存中的Rowhammer漏洞,在不关闭IOMMU的情况下实现权限提升和系统完全控制。该攻击由多伦多大学研究团队开发,通过破坏GPU页表并结合NVIDIA驱动中的内存安全漏洞,在消费级GPU上实现系统级妥协。 2026-4-6 21:45:13 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏

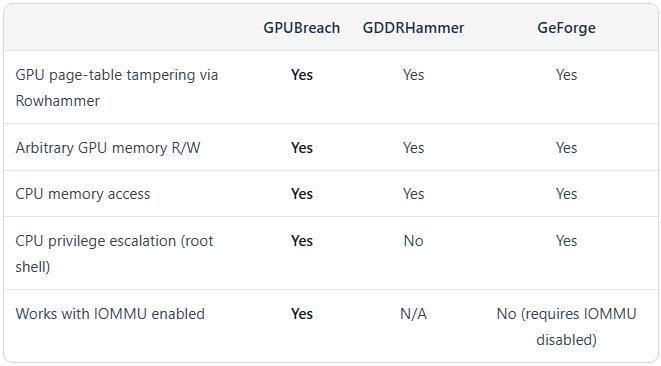
A new attack, dubbed GPUBreach, can induce Rowhammer bit-flips on GPU GDDR6 memories to escalate privileges and lead to a full system compromise.
GPUBreach was developed by a team of researchers at the University of Toronto, and full details will be presented at the upcoming IEEE Symposium on Security & Privacy on April 13 in Oakland.
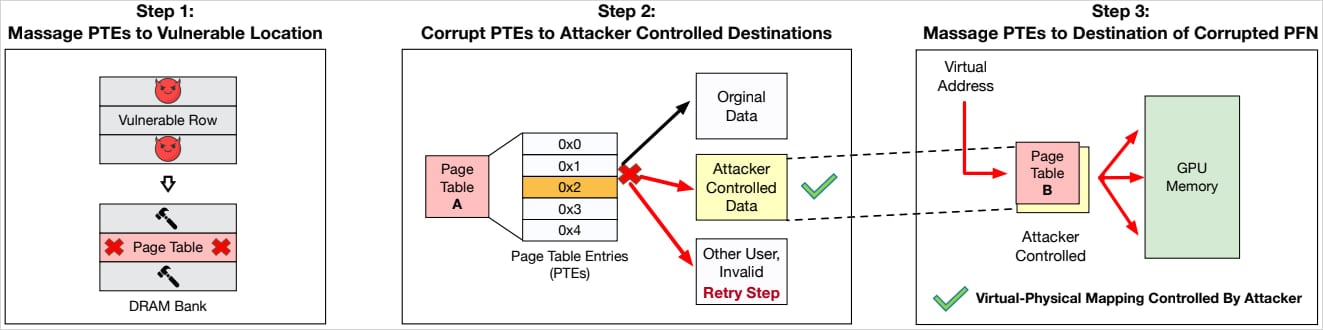
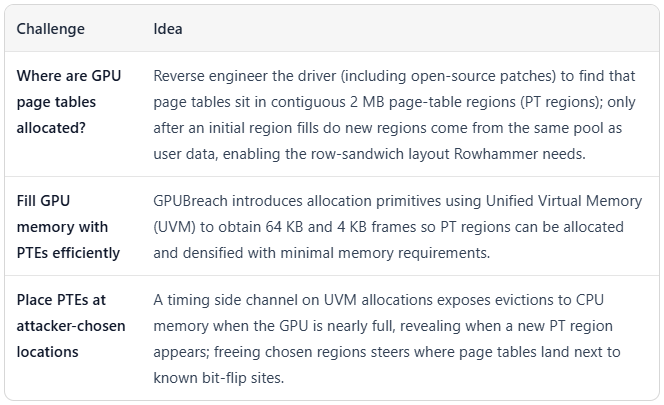
The researchers demonstrated that Rowhammer-induced bit flips in GDDR6 can corrupt GPU page tables (PTEs) and grant arbitrary GPU memory read/write access to an unprivileged CUDA kernel.
An attacker may then chain this into a CPU-side escalation by exploiting memory-safety bugs in the NVIDIA driver, potentially leading to complete system compromise without the need to disable Input-Output Memory Management Unit (IOMMU) protection.
Source: University of Toronto
IOMMU is a hardware unit that protects against direct memory attacks. It controls and restricts how devices access memory by managing which memory regions are accessible to each device.
Despite being an effective measure against most direct memory access (DMA) attacks, IOMMU does not stop GPUBreach.
“GPUBreach shows that GPU Rowhammer attacks can move beyond data corruption to real privilege escalation,” the researchers explain.
“By corrupting GPU page tables, an unprivileged CUDA kernel can gain arbitrary GPU memory read/write, and then chain that capability into CPU-side escalation by exploiting newly discovered memory-safety bugs in the NVIDIA driver.”
“The result is system-wide compromise up to a root shell, without disabling IOMMU, unlike contemporary works, making GPUBreach a more potent threat.”
Source: University of Toronto
The same researchers previously demonstrated GPUHammer, the first attack showing that Rowhammer attacks on GPUs are practical, prompting NVIDIA to issue a warning to users and suggesting the activation of the System Level Error-Correcting Code mitigation to block such attempts on GDDR6 memory.
However, GPUBreach is taking the threat to the next level, showing that it is possible not only to corrupt data but also to gain root privileges with IOMMU enabled.
The researchers exemplified the results with an NVIDIA RTX A6000 GPU with GDDR6. This model is widely used in AI development and training workloads.
Source: University of Toronto
Disclosure and mitigations
The University of Toronto researchers reported their findings to NVIDIA, Google, AWS, and Microsoft on November 11, 2025.
Google acknowledged the report and awarded the researchers a $600 bug bounty.
NVIDIA stated that it may update its existing security notice from July 2025 to include the newly discovered attack possibilities.
As demonstrated by the researchers, IOMMU alone is insufficient if GPU-controlled memory can corrupt trusted driver state, so users at risk should rely solely on that security measure.
Error Correcting Code (ECC) memory helps correct single-bit flips and detect double-bit flips, but it is not reliable against multi-bit flips.
Ultimately, the researchers underlined that GPUBreach is completely unmitigated for consumer GPUs without ECC.
The researchers will publish the full details of their work, including a technical paper and a GitHub repository with the reproduction package and scripts, on April 13.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

